Ubuntu系统下配置ssh免密访问
- 一、基本信息
- 二、ssh安装
- 2.1 查看是否已经安装ssh
- 2.2 安装ssh
- 2.3 查看ssh安装状态
- 三、启动、停止,及开机自启动
- 3.1 启动ssh
- 3.2 关闭ssh
- 3.3 使用systemctl设置ssh服务自启动
- 3.4 使用systemctl关闭ssh开机启动
- 四、配置通过密钥进行免密访问
- 4.1 生成密钥
- 4.2 通过ssh-agent管理私钥
- 4.3 管理公钥
- 4.4 通过scp将公钥拷贝到服务器
- 4.5 将公钥添加到公钥管理文件中
- 4.6 享受ssh免密链接服务器
一、基本信息
Ubuntu是linux系统,虽然他是支持界面化操作的,一般用来做服务器用,所以配置ssh可以比较安全的进行访问,也方便在其他地方访问服务器,轻松省事。
Ubuntu系统版本:
使用uname -a指令获取系统版本信息
zero@ubuntu:~$ uname -a
Linux ubuntu 5.15.0-79-generic #86-Ubuntu SMP Mon Jul 10 16:07:21 UTC 2023 x86_64 x86_64 x86_64 GNU/Linux
具体信息如下:
- 系统类型: Linux
- 主机名:ubuntu
- 内核版本:5.15.0-79-generic
- 编译时间:#86-Ubuntu SMP Mon Jul 10 16:07:21 UTC 2023
- 硬件架构:x86_64 x86_64 x86_64(处理器架构,操作系统类型,软件环境)
- 操作系统名称:GNU/Linux
二、ssh安装
2.1 查看是否已经安装ssh
直接输入ssh查看
zero@ubuntu:~$ ssh
usage: ssh [-46AaCfGgKkMNnqsTtVvXxYy] [-B bind_interface][-b bind_address] [-c cipher_spec] [-D [bind_address:]port][-E log_file] [-e escape_char] [-F configfile] [-I pkcs11][-i identity_file] [-J [user@]host[:port]] [-L address][-l login_name] [-m mac_spec] [-O ctl_cmd] [-o option] [-p port][-Q query_option] [-R address] [-S ctl_path] [-W host:port][-w local_tun[:remote_tun]] destination [command [argument ...]]
有具体的信息就是已经安装了。
2.2 安装ssh
可以使用如下指令安装ssh
sudo apt-get install openssh-server
一般服务器是被访问的,所以只要安装openssh-server即可,如果要安装客户端,将安装的内容改成openssh-client即可。
2.3 查看ssh安装状态
安装完成后重新查看ssh安装状态
使用netstat查看状态
zero@ubuntu:~$ sudo netstat -tlnp | grep sshd
[sudo] password for zero:
tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN 2714/sshd: /usr/sbi
tcp6 0 0 :::22 :::* LISTEN 2714/sshd: /usr/sbi
使用systemctl查看状态
zero@ubuntu:~$ sudo systemctl status ssh
● ssh.service - OpenBSD Secure Shell serverLoaded: loaded (/lib/systemd/system/ssh.service; enabled; vendor preset: enabled)Active: active (running) since Sat 2023-08-26 15:01:13 UTC; 13min agoDocs: man:sshd(8)man:sshd_config(5)Main PID: 2714 (sshd)Tasks: 1 (limit: 4514)Memory: 4.0MCPU: 33msCGroup: /system.slice/ssh.service└─2714 "sshd: /usr/sbin/sshd -D [listener] 0 of 10-100 startups"Aug 26 15:01:13 ubuntu systemd[1]: Starting OpenBSD Secure Shell server...
Aug 26 15:01:13 ubuntu sshd[2714]: Server listening on 0.0.0.0 port 22.
Aug 26 15:01:13 ubuntu sshd[2714]: Server listening on :: port 22.
Aug 26 15:01:13 ubuntu systemd[1]: Started OpenBSD Secure Shell server.
Aug 26 15:11:26 ubuntu sshd[2899]: Accepted password for zero from 192.168.159.1 port 51604 ssh2
Aug 26 15:11:26 ubuntu sshd[2899]: pam_unix(sshd:session): session opened for user zero(uid=1000) by (uid=0)
三、启动、停止,及开机自启动
3.1 启动ssh
zero@ubuntu:~$ sudo systemctl start ssh #启动ssh服务
zero@ubuntu:~$ sudo systemctl status sshd #查询状态
Unit sshd.service could not be found.
zero@ubuntu:~$ sudo systemctl status ssh
● ssh.service - OpenBSD Secure Shell serverLoaded: loaded (/lib/systemd/system/ssh.service; disabled; vendor preset: enabled)Active: active (running) since Sat 2023-08-26 15:01:13 UTC; 27min agoDocs: man:sshd(8)man:sshd_config(5)Main PID: 2714 (sshd)Tasks: 1 (limit: 4514)Memory: 4.0MCPU: 33msCGroup: /system.slice/ssh.service└─2714 "sshd: /usr/sbin/sshd -D [listener] 0 of 10-100 startups"Aug 26 15:01:13 ubuntu systemd[1]: Starting OpenBSD Secure Shell server...
Aug 26 15:01:13 ubuntu sshd[2714]: Server listening on 0.0.0.0 port 22.
Aug 26 15:01:13 ubuntu sshd[2714]: Server listening on :: port 22.
Aug 26 15:01:13 ubuntu systemd[1]: Started OpenBSD Secure Shell server.
Aug 26 15:11:26 ubuntu sshd[2899]: Accepted password for zero from 192.168.159.1 port 51604 ssh2
Aug 26 15:11:26 ubuntu sshd[2899]: pam_unix(sshd:session): session opened for user zero(uid=1000) by (uid=0)
zero@ubuntu:~$ sudo netstat -tlnp | grep sshd #查询状态
tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN 2714/sshd: /usr/sbi
tcp6 0 0 :::22 :::* LISTEN 2714/sshd: /usr/sbi
3.2 关闭ssh
zero@ubuntu:~$ sudo systemctl stop ssh #关闭ssh服务
zero@ubuntu:~$ sudo netstat -tlnp | grep sshd #关闭后查询不到网络状态
zero@ubuntu:~$ sudo systemctl status ssh #ssh状态已关闭
○ ssh.service - OpenBSD Secure Shell serverLoaded: loaded (/lib/systemd/system/ssh.service; disabled; vendor preset: enabled)Active: inactive (dead) since Sat 2023-08-26 15:34:05 UTC; 11s agoDocs: man:sshd(8)man:sshd_config(5)Process: 2714 ExecStart=/usr/sbin/sshd -D $SSHD_OPTS (code=exited, status=0/SUCCESS)Main PID: 2714 (code=exited, status=0/SUCCESS)CPU: 35msAug 26 15:01:13 ubuntu systemd[1]: Starting OpenBSD Secure Shell server...
Aug 26 15:01:13 ubuntu sshd[2714]: Server listening on 0.0.0.0 port 22.
Aug 26 15:01:13 ubuntu sshd[2714]: Server listening on :: port 22.
Aug 26 15:01:13 ubuntu systemd[1]: Started OpenBSD Secure Shell server.
Aug 26 15:11:26 ubuntu sshd[2899]: Accepted password for zero from 192.168.159.1 port 51604 ssh2
Aug 26 15:11:26 ubuntu sshd[2899]: pam_unix(sshd:session): session opened for user zero(uid=1000) by (uid=0)
Aug 26 15:34:05 ubuntu systemd[1]: Stopping OpenBSD Secure Shell server...
Aug 26 15:34:05 ubuntu systemd[1]: ssh.service: Deactivated successfully.
Aug 26 15:34:05 ubuntu systemd[1]: Stopped OpenBSD Secure Shell server.
3.3 使用systemctl设置ssh服务自启动
zero@ubuntu:~$ sudo systemctl enable ssh
Synchronizing state of ssh.service with SysV service script with /lib/systemd/systemd-sysv-install.
Executing: /lib/systemd/systemd-sysv-install enable ssh

设置完成之后重启即可
3.4 使用systemctl关闭ssh开机启动
zero@ubuntu:~$ sudo systemctl disable ssh
Synchronizing state of ssh.service with SysV service script with /lib/systemd/systemd-sysv-install.
Executing: /lib/systemd/systemd-sysv-install disable ssh
Removed /etc/systemd/system/multi-user.target.wants/ssh.service.
Removed /etc/systemd/system/sshd.service.

四、配置通过密钥进行免密访问
部分操作说明可参考Windows下配置SSH实现免密访问和远程端口转发,本文直接进行操作。
4.1 生成密钥
zero@ubuntu:~$ sudo ssh-keygen #此处直接使用默认设置生成rsa的密钥
Generating public/private rsa key pair.
Enter file in which to save the key (/root/.ssh/id_rsa): //不修改路径
Enter passphrase (empty for no passphrase): #不设置密码,实际使用根据自己需要设置密码会比较安全
Enter same passphrase again:
Your identification has been saved in /root/.ssh/id_rsa
Your public key has been saved in /root/.ssh/id_rsa.pub
The key fingerprint is:
SHA256:elLfv9r5e4RLOSKnee6oJPBGmS6YGm3WcAuvXVAxBtg root@ubuntu
The key's randomart image is:
+---[RSA 3072]----+
| o..+ |
| . E. o |
| . |
| . o |
| o + + S o |
| . O B o ...o = .|
|. * = O o .=.o + |
| = o + = o..o...|
|. . . ...++.=++|
+----[SHA256]-----+
注: 若要配置git访问服务器,此处密钥对可使用rsa格式的,git for windows默认识别rsa密钥。
4.2 通过ssh-agent管理私钥
zero@ubuntu:~$ ssh-agent #启动服务
SSH_AUTH_SOCK=/tmp/ssh-XXXXXXjkoDta/agent.3455; export SSH_AUTH_SOCK;
SSH_AGENT_PID=3456; export SSH_AGENT_PID;
echo Agent pid 3456;zero@ubuntu:~$ ssh-add /root/.ssh/id_rsa # 没有使用agent启动bash直接调用ssh-add添加私钥会报错
Could not open a connection to your authentication agent. zero@ubuntu:~$ sudo ssh-agent bash --login -i # 使用ssh-agent启动bash,注意需要添加sudo,添加root的密钥需要使用root权限。root@ubuntu:/home/zero# ssh-add /root/.ssh/id_rsa #将密钥添加到agent中
Identity added: /root/.ssh/id_rsa (root@ubuntu)
root@ubuntu:/home/zero# exit # 退出当前bash
logout
zero@ubuntu:~$
4.3 管理公钥
服务器管理公钥,可以直接添加公钥文件中
zero@ubuntu:~$ cat /root/.ssh/id_ras.pub >> authorized_keys # 直接拷贝汇报错,当我们要操作的公钥在root文件夹下时就需要root权限
cat: /root/.ssh/id_ras.pub: Permission deniedzero@ubuntu:~$ sudo cat /root/.ssh/id_rsa.pub >> authorized_keys # 添加sudo使用root权限操作
zero@ubuntu:~$ # 操作成功没有错误提示
4.4 通过scp将公钥拷贝到服务器
需要将公钥拷贝到要访问的服务器中。
PS C:\WINDOWS\system32> scp C:\Users\LJM\.ssh\id_rsa.pub zero@192.168.159.129:.ssh/id_rsa_git.pub
zero@192.168.159.129's password:
id_rsa.pub 100% 567 558.8KB/s 00:00
PS C:\WINDOWS\system32>
4.5 将公钥添加到公钥管理文件中
切换到.ssh文件夹中,然后将公钥添加到公钥管理文件中。
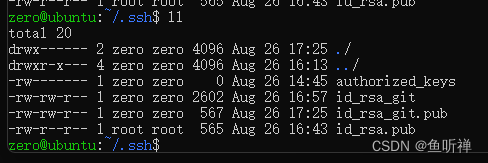
zero@ubuntu:~/.ssh$ ll
total 24
drwx------ 2 zero zero 4096 Aug 26 17:25 ./
drwxr-x--- 4 zero zero 4096 Aug 26 16:13 ../
-rw------- 1 zero zero 567 Aug 26 17:28 authorized_keys
-rw-rw-r-- 1 zero zero 2602 Aug 26 16:57 id_rsa_git
-rw-rw-r-- 1 zero zero 567 Aug 26 17:25 id_rsa_git.pub
-rw-r--r-- 1 root root 565 Aug 26 16:43 id_rsa.pub
zero@ubuntu:~/.ssh$ cat id_rsa_git.pub >> authorized_keys
4.6 享受ssh免密链接服务器
公钥和私钥添加管理后,对应的文件即可删除了。然后客户端就可以通过ssh免密访问服务器。
通常一般要访问的客户端保存私钥,服务端保存公钥。

![java八股文面试[多线程]——合适的线程数是多少](https://img-blog.csdnimg.cn/e277391b24534bb3aecd0d61f380dc3b.png)