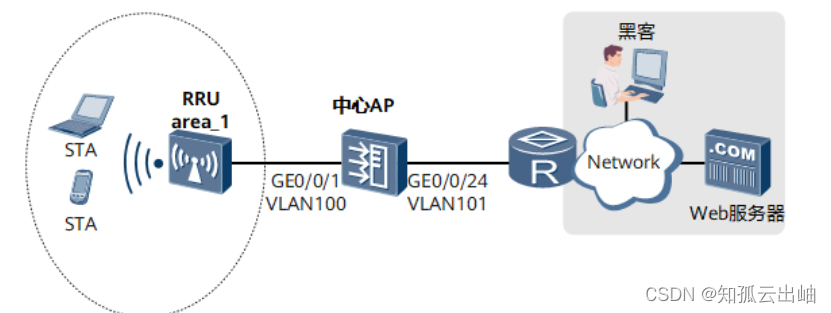
配置入侵防御示例
操作步骤
- 配置WLAN基本业务,具体配置步骤请参照配置敏捷分布式WLAN组网示例。
- 使能安全引擎。
<span style="background-color:#dddddd">[AP] <strong>defence engine enable</strong> </span> - 创建入侵防御模板“profile_ips_pc”,保护内网用户。
<span style="background-color:#dddddd">[AP] <strong>profile type ips name profile_ips_pc</strong> [AP-profile-ips-profile_ips_pc] <strong>description profile for intranet users</strong> [AP-profile-ips-profile_ips_pc] <strong>collect-attack-evidence enable</strong> Warning: Succeeded in configuring attack evidence collection for the IPS functio n. The function is used for fault locating. This function may deteriorate systemperformance. Exercise caution before using the function. Attack evidences can be collected only when a log storage device with sufficientstorage space is available. After all required attack evidences are collected, disable the function. Our company alone is unable to transfer or process the communication contents orpersonal data. You are advised to enable the related functions based on the ap plicable laws and regulations in terms of purpose and scope of usage. When the c ommunication contents or personal data are being transferred or processed, you are obliged to take considerable measures to ensure that these contents are full y protected. Continue? [Y/N]: <strong>y</strong> [AP-profile-ips-profile_ips_pc] <strong>signature-set name filter1</strong> [AP-profile-ips-profile_ips_pc-sigset-filter1] <strong>target client</strong> [AP-profile-ips-profile_ips_pc-sigset-filter1] <strong>severity high</strong> [AP-profile-ips-profile_ips_pc-sigset-filter1] <strong>protocol HTTP</strong> [AP-profile-ips-profile_ips_pc-sigset-filter1] <strong>quit</strong> [AP-profile-ips-profile_ips_pc] <strong>quit</strong> </span> - 提交配置。
<span style="background-color:#dddddd">[AP] <strong>engine configuration commit</strong> </span> - 创建攻击防御模板“defence_1”,引用入侵防御模板“profile_ips_pc”。
<span style="background-color:#dddddd">[AP] <strong>defence-profile name defence_1</strong> [AP-defence-profile-defence_1] <strong>profile type ips profile_ips_pc</strong> [AP-defence-profile-defence_1] <strong>quit</strong> </span> - 在VAP模板上引用攻击防御模板“defence_1”。
<span style="background-color:#dddddd">[AP] <strong>wlan</strong> [AP-wlan-view] <strong>vap-profile name wlan-vap</strong> [AP-wlan-vap-prof-wlan-vap] <strong>defence-profile defence_1</strong> [AP-wlan-vap-prof-wlan-vap] <strong>quit</strong> </span> - 验证配置结果。
在中心AP上执行命令display profile type ips name profile_ips_pc,查看入侵防御配置文件的配置信息。
<span style="background-color:#dddddd">[AP-wlan-view] <strong>display profile type ips name profile_ips_pc</strong>IPS Profile Configurations: ---------------------------------------------------------------------- Name : profile_ips_pc Description : profile for intranet users Referenced : 1 State : committed AttackEvidenceCollection : enable SignatureSet : filter1 Target : client Severity : high OS : N/A Protocol : HTTP Category : N/A Action : default Application : N/A Exception: ID Action Name ---------------------------------------------------------------------- DNS Protocol Check: HTTP Protocol Check: ---------------------------------------------------------------------- </span>
中心AP的配置文件
<span style="background-color:#dddddd">#defence engine enablesysname AP
#
profile type ips name profile_ips_pc description profile for intranet users collect-attack-evidence enable signature-set name filter1 target client severity high protocol HTTP
#
vlan batch 100 to 101
#
dhcp enable
#
defence-profile name defence_1 profile type ips profile_ips_pc
#
interface Vlanif100ip address 10.23.100.1 255.255.255.0dhcp select interface
#
interface Vlanif101ip address 10.23.101.1 255.255.255.0dhcp select interface
#
interface GigabitEthernet0/0/1port link-type trunkport trunk pvid vlan 100port trunk allow-pass vlan 100 to 101
#
interface GigabitEthernet0/0/24port link-type trunkport trunk allow-pass vlan 101
#
management-vlan 100
#
wlansecurity-profile name wlan-securitysecurity wpa2 psk pass-phrase %^%#m"tz0f>~7.[`^6RWdzwCy16hJj/Mc!,}s`X*B]}A%^%# aesssid-profile name wlan-ssidssid wlan-netvap-profile name wlan-vapservice-vlan vlan-id 101ssid-profile wlan-ssidsecurity-profile wlan-securitydefence-profile defence_1regulatory-domain-profile name domain1ap-group name ap-group1regulatory-domain-profile domain1radio 0vap-profile wlan-vap wlan 1radio 1vap-profile wlan-vap wlan 1ap-id 1 type-id 19 ap-mac 60de-4476-e360 ap-sn 210235554710CB000042ap-name area_1ap-group ap-group1radio 0channel 20mhz 6eirp 127radio 1channel 20mhz 149eirp 127
#
return</span> 父主题: 配置举例
版权所有 © 华为技术有限公司

![数据库被.[Goodmorningfriends@onionmail.org].faust勒索病毒加密,能恢复吗?](https://img-blog.csdnimg.cn/direct/6547328ef6bc4864be7c5a7d89505198.jpeg)
![【PyTorch][chapter 22][李宏毅深度学习][ WGAN]【实战三】](https://img-blog.csdnimg.cn/direct/54522e6650df424e97d377af0e02ee69.png)