由于小程序要求必须访问wss的接口,因此需要将测试环境也切换到https,看了下官方的文档
RabbitMQ Web STOMP Plugin | RabbitMQ里面有这个信息

然后敲打GPT一阵子,把要求输入几个来回,得到这样一个脚本:
generate_cert.sh
#!/bin/bash# 检查是否提供了IP地址
if [ "$#" -ne 1 ]; thenecho "Usage: $0 <IP_ADDRESS>"exit 1
fiIP_ADDRESS=$1
PASSWORD="changeme"# 创建必要的目录
mkdir -p certs# 生成 CA 密钥
openssl genrsa -des3 -passout pass:$PASSWORD -out certs/ca.key 2048# 生成 CA 证书
openssl req -x509 -new -nodes -key certs/ca.key -sha256 -days 1024 -passin pass:$PASSWORD -out certs/ca_certificate.pem -subj "/CN=${IP_ADDRESS}"# 生成服务器密钥
openssl genrsa -des3 -passout pass:$PASSWORD -out certs/server.key 2048# 生成服务器证书签名请求(CSR)
openssl req -new -key certs/server.key -passin pass:$PASSWORD -out certs/server.csr -subj "/CN=${IP_ADDRESS}"# 创建一个配置文件用于扩展
cat <<EOF > certs/openssl.cnf
[ v3_ca ]
basicConstraints = CA:TRUE[ v3_req ]
basicConstraints = CA:FALSE
subjectAltName = @alt_names[ alt_names ]
IP.1 = ${IP_ADDRESS}
EOF# 使用 CA 证书签署服务器证书
openssl x509 -req -in certs/server.csr -CA certs/ca_certificate.pem -CAkey certs/ca.key -CAcreateserial -out certs/server_certificate.pem -days 500 -sha256 -passin pass:$PASSWORD -extfile certs/openssl.cnf -extensions v3_req# 转换服务器密钥为 PEM 格式
openssl rsa -in certs/server.key -out certs/server_key.pem -passin pass:$PASSWORD -passout pass:$PASSWORD# 打印完成信息
echo "Certificates and keys generated successfully in the 'certs' directory."
echo "CA Certificate: certs/ca_certificate.pem"
echo "Server Certificate: certs/server_certificate.pem"
echo "Server Key: certs/server_key.pem"
在WSL的ubuntu里使用
generate_cert.sh <测试IP> 来生成
然后在RabbitMQ服务器的log/db同级目录下建立rabbitmq.conf
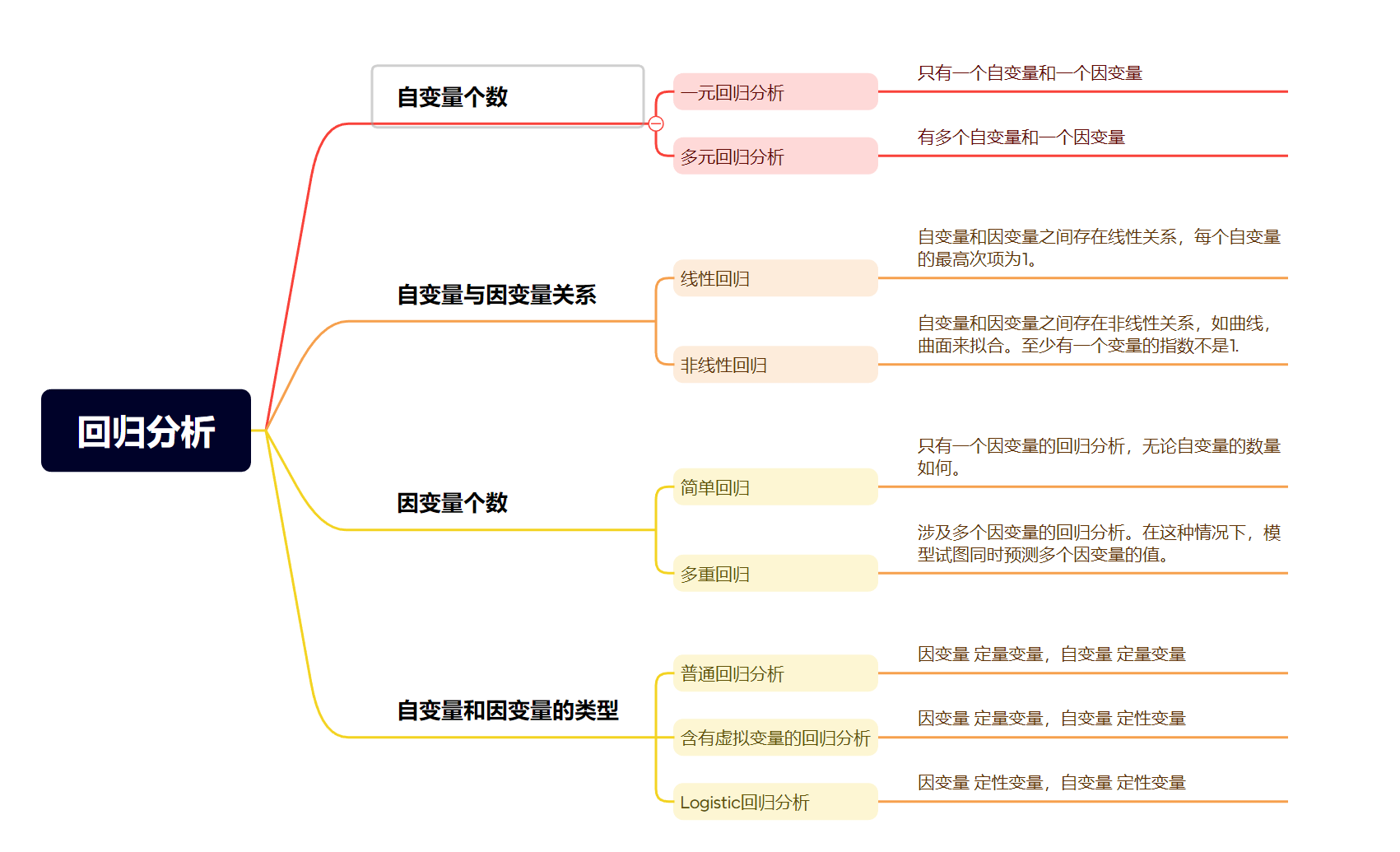
第一个张图片内容贴进去,然后重启rabbitMQ服务,再看管理界面,https的端口15673成功起来了









![[Java IO] 文件的概念与相关操作](https://i-blog.csdnimg.cn/direct/7986feeada6a4cf19d339b0312ea1647.png)