一、前言
在集群外部prometheus想要调用k8s集群的apiserver获取监控数据需要通过token和ca验证,在集群内部部署的prometheus就不会有这个情况,因为集群内部部署prometheus pod的时候就已经注入了访问集群的token和ca文件,所以以下就针对k8s集群外部署的prometheus创建token和ca文件使得prometheus能够访问k8s集群的apiserver获取监控数据
二、k8s集群创建RBAC对象
vi prometheus-rabc.yaml
apiVersion: v1
kind: ServiceAccount
metadata:name: prometheusnamespace: prometheus
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:name: prometheus
rules:
- apiGroups:- ""resources:- nodes- services- endpoints- pods- nodes/proxyverbs:- get- list- watch
- apiGroups:- "extensions"resources:- ingressesverbs:- get- list- watch
- apiGroups:- ""resources:- configmaps- nodes/metricsverbs:- get
- nonResourceURLs:- /metricsverbs:- get
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:name: prometheus
roleRef:apiGroup: rbac.authorization.k8s.iokind: ClusterRolename: prometheus
subjects:
- kind: ServiceAccountname: prometheusnamespace: prometheus创建命名空间
kubectl create namespace prometheus
创建rbac
kubectl create -f prometheus-rabc.yaml
在新版本的k8s中创建ServiceAccount不会默认创建secret,需要自己手动创建
vi prometheus-secret.yaml
apiVersion: v1
kind: Secret
metadata:name: prometheusnamespace: prometheusannotations:kubernetes.io/service-account.name: prometheus #这里需要填写创建的ServiceAccount的名称
type: kubernetes.io/service-account-token查看token
kubectl describe secret prometheus -n prometheus

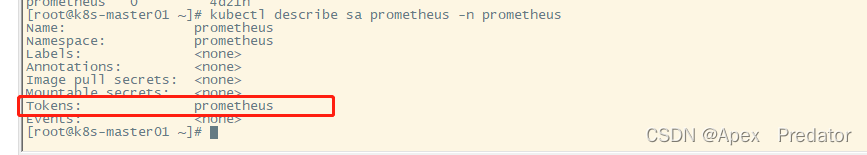
查看一下ServiceAccount
kubectl describe sa prometheus -n prometheus
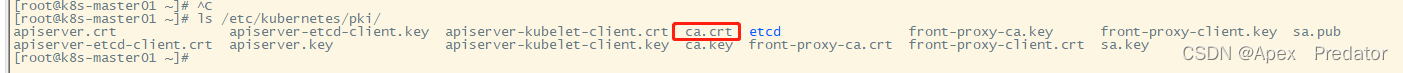
prometheus调用k8s集群接口获取监控数据,使用以上的token和集群ca证书即可
k8s集群的ca证书在以下目录中
ls /etc/kubenetes/pki
![[正式学习java③]——字符串在内存中的存储方式、为什么字符串不可变、字符串的拼接原理,键盘录入的小细节。](https://img-blog.csdnimg.cn/85365aa00f6642c78ee6aa4a696e3280.png)